| Skip Navigation Links | |
| Exit Print View | |

|
Oracle Solaris Trusted Extensions Configuration and Administration Oracle Solaris 11 Express 11/10 |
| Skip Navigation Links | |
| Exit Print View | |

|
Oracle Solaris Trusted Extensions Configuration and Administration Oracle Solaris 11 Express 11/10 |
Part I Initial Configuration of Trusted Extensions
1. Security Planning for Trusted Extensions
2. Configuration Roadmap for Trusted Extensions
3. Adding Trusted Extensions Software to the Oracle Solaris OS (Tasks)
4. Configuring Trusted Extensions (Tasks)
5. Configuring LDAP for Trusted Extensions (Tasks)
6. Configuring a Headless System With Trusted Extensions (Tasks)
Part II Administration of Trusted Extensions
7. Trusted Extensions Administration Concepts
8. Trusted Extensions Administration Tools
9. Getting Started as a Trusted Extensions Administrator (Tasks)
10. Security Requirements on a Trusted Extensions System (Overview)
11. Administering Security Requirements in Trusted Extensions (Tasks)
Common Tasks in Trusted Extensions (Task Map)
How to Change the Password for root
How to Regain Control of the Desktop's Current Focus
How to Obtain the Hexadecimal Equivalent for a Label
How to Obtain a Readable Label From Its Hexadecimal Form
How to Prevent Password Prompting at a Change in Workspace Label
12. Users, Rights, and Roles in Trusted Extensions (Overview)
13. Managing Users, Rights, and Roles in Trusted Extensions (Tasks)
14. Remote Administration in Trusted Extensions (Tasks)
15. Trusted Extensions and LDAP (Overview)
16. Managing Zones in Trusted Extensions (Tasks)
17. Managing and Mounting Files in Trusted Extensions (Tasks)
18. Trusted Networking (Overview)
19. Managing Networks in Trusted Extensions (Tasks)
20. Multilevel Mail in Trusted Extensions (Overview)
21. Managing Labeled Printing (Tasks)
22. Devices in Trusted Extensions (Overview)
23. Managing Devices for Trusted Extensions (Tasks)
24. Trusted Extensions Auditing (Overview)
25. Software Management in Trusted Extensions (Reference)
Creating and Managing a Security Policy
Site Security Policy and Trusted Extensions
Computer Security Recommendations
Physical Security Recommendations
Personnel Security Recommendations
Additional Security References
B. Configuration Checklist for Trusted Extensions
Checklist for Configuring Trusted Extensions
C. Quick Reference to Trusted Extensions Administration
Administrative Interfaces in Trusted Extensions
Oracle Solaris Interfaces Extended by Trusted Extensions
Tighter Security Defaults in Trusted Extensions
Limited Options in Trusted Extensions
D. List of Trusted Extensions Man Pages
Trusted Extensions Man Pages in Alphabetical Order
Oracle Solaris Man Pages That Are Modified by Trusted Extensions
The following task map describes procedures that set up a working environment for administrators of Trusted Extensions.
|
The Security Administrator role is authorized to change any account's password at any time. However, the System Administrator cannot change the password of a system account. A system account is an account whose UID is below 100. root is a system account because its UID is 0.
If your site has made superuser into the root role, assume the root role.
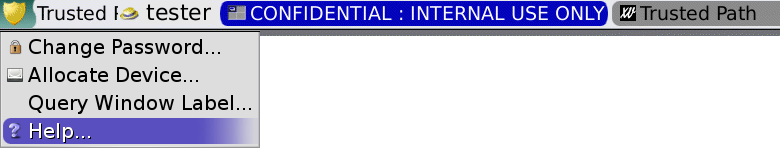
From the trusted path menu, choose Change Password.
The “Secure Attention” key combination can be used to break a pointer grab or a keyboard grab by an untrusted application. The key combination can also be used to verify if a pointer or a keyboard has been grabbed by a trusted application. On a multiheaded system that has been spoofed to display more than one trusted stripe, this key combination warps the pointer to the authorized trusted stripe.
Press the keys simultaneously to regain control of the current desktop focus. On the Sun keyboard, the diamond is the Meta key.
<Meta> <Stop>
If the grab, such as a pointer, is not trusted, the pointer moves to the stripe. A trusted pointer does not move to the trusted stripe.
<Alt> <Break>
Press the keys simultaneously to regain control of the current desktop focus on your laptop.
Example 11-1 Testing If the Password Prompt Can Be Trusted
On an x86 system that is using a Sun keyboard, the user has been prompted for a password. The cursor has been grabbed, and is in the password dialog box. To check that the prompt is trusted, the user presses the <Meta> <Stop> keys simultaneously. When the pointer remains in the dialog box, the user knows that the password prompt is trusted.
If the pointer had moved to the trusted stripe, the user would know that the password prompt could not be trusted, and contact the administrator.
Example 11-2 Forcing the Pointer to the Trusted Stripe
In this example, a user is not running any trusted processes but cannot see the mouse pointer. To bring the pointer to the center of the trusted stripe, the user presses the <Meta> <Stop> keys simultaneously.
This procedure provides an internal hexadecimal representation of a label. This representation is safe for storing in a public directory. For more information, see the atohexlabel(1M) man page.
You must be in the Security Administrator role in the global zone. For details, see How to Enter the Global Zone in Trusted Extensions.
$ atohexlabel "CONFIDENTIAL : NEED TO KNOW" 0x0004-08-68
$ atohexlabel -c "CONFIDENTIAL NEED TO KNOW" 0x0004-08-68
Note - Human readable sensitivity labels and clearance labels are formed according to rules in the label_encodings file. Each type of label uses rules from a separate section of this file. When a sensitivity label and a clearance label both express the same underlying level of sensitivity, the labels have identical hexadecimal forms. However, the labels can have different human readable forms. System interfaces that accept human readable labels as input expect one type of label. If the text strings for the label types differ, these text strings cannot be used interchangeably.
In the default label_encodings file, the text equivalent of a clearance label does not include a colon (:).
Example 11-3 Using the atohexlabel Command
When you pass a valid label in hexadecimal format, the command returns the argument.
$ atohexlabel 0x0004-08-68 0x0004-08-68
When you pass an administrative label, the command returns the argument.
$ atohexlabel admin_high ADMIN_HIGH atohexlabel admin_low ADMIN_LOW
The error message atohexlabel parsing error found in <string> at position 0 indicates that the <string> argument that you passed to atohexlabel was not a valid label or clearance. Check your typing, and check that the label exists in your installed label_encodings file.
This procedure provides a way to repair labels that are stored in internal databases. For more information, see the hextoalabel(1M) man page.
You must be in the Security Administrator role in the global zone.
$ hextoalabel 0x0004-08-68 CONFIDENTIAL : NEED TO KNOW
$ hextoalabel -c 0x0004-08-68 CONFIDENTIAL NEED TO KNOW
Because ZFS datasets carry their own labels, users are required to be authenticated when they change to a workspace at a different label. This procedure removes the password prompt and allows users to change workspace labels without authentication.
Note - Enabling users to change to a workspace at a different label without requiring the user to provide a password is a security risk. Be sure that you want to change from the default security posture.
You must be root in the global zone, and have access to every non-global zone.
Comment out the tsoljds-userlogin entry in the /etc/pam.conf file.
## /etc/pam.conf file ... # GDM Autologin (explicit because of pam_allow). These need to be ... tsoljds-userlogin auth sufficient pam_allow.so.1 . . . # Default definitions for Authentication management ... tsoljds-userlogin auth sufficient pam_allow.so.1 ...
In Trusted Extensions, the security administrator changes or accesses default security settings on a system.
Files in the /etc/security and /etc/default directories contain security settings. On an Oracle Solaris system, superuser can edit these files. For Oracle Solaris security information, see Chapter 3, Controlling Access to Systems (Tasks), in System Administration Guide: Security Services.
 | Caution - Relax system security defaults only if site security policy allows you to. |
You must be in the Security Administrator role in the global zone.
The following table lists the security files and what security parameters to change in the files.
|