1 Introduction
This chapter explains integration concepts for the Oracle Identity Management suite.
The chapter contains these topics:
Before proceeding with the topics in this chapter, refer to the following documents for background information about Oracle Identity Management:
-
Oracle Fusion Middleware Installation Guide for Oracle Identity Management
-
Oracle Fusion Middleware Administrator's Guide
1.1 Prerequisites to Integration
Before using the procedures in this document to integrate Oracle Identity Management components, you must install and deploy the components.
For details about installing Oracle Identity Management components, see:
-
Oracle Fusion Middleware Installation Guide for Oracle Identity and Access Management
-
Oracle Fusion Middleware Quick Installation Guide for Oracle Identity and Access Management
The Introduction chapter in the Oracle Fusion Middleware Installation Guide for Oracle Identity and Access Management contains background on the IdM deployment procedure such as the installation roadmap, prerequisites, and the installation and configuration workflow.
You must also understand the identity management topology and the environment in which the components will function.
To learn more about the range of topologies supported in this document, see Section 1.2.
Enabling LDAP Synchronization in Oracle Identity Manager
You must enable LDAP synchronization in Oracle Identity Manager before starting this integration.
If you did not enable LDAP synchronization by using the OIM Configuration Wizard during installation, then refer to Appendix E, "Enabling LDAP Synchronization in Oracle Identity Manager" for instructions.
Oracle Virtual Directory Integration
Using Oracle Virtual Directory with Oracle Access Management Access Manager (Access Manager) is optional. However, if you plan to use Oracle Virtual Directory with Access Manager, then you must configure Oracle Virtual Directory for integration with Access Manager before starting the core integration procedures described in this publication.
Refer to Appendix F, "Configuring Oracle Virtual Directory for Integration with Oracle Access Management Access Manager" for instructions.
1.2 Integration Topologies
Oracle Identity Management consists of a number of products, which can be used either individually or collectively. Two basic types of topology are available in Oracle Identity Management:
-
Basic integration topologies
This topology supports integration between suite components, in an environment where each component runs on at most one node.
-
Enterprise integration topologies
This topology is meant for configuring integration between suite components in an enterprise environment. Each component may run on one or more nodes.
Topologies Described in this Document
This book is dedicated to single-node integration topologies. Use the procedures described in this book when deploying Oracle Identity Management in an environment where each component runs on a single node. You can also use the procedures to understand integration tools and techniques, and to understand the effects and benefits of integrating specific identity management components.
1.2.1 Basic Integration Topologies
This section describes the component topologies that form the basis of this document. It also explains the tiers that make up each topology.
See Also:
Table 1-1 for definitions of acronyms used in this section.
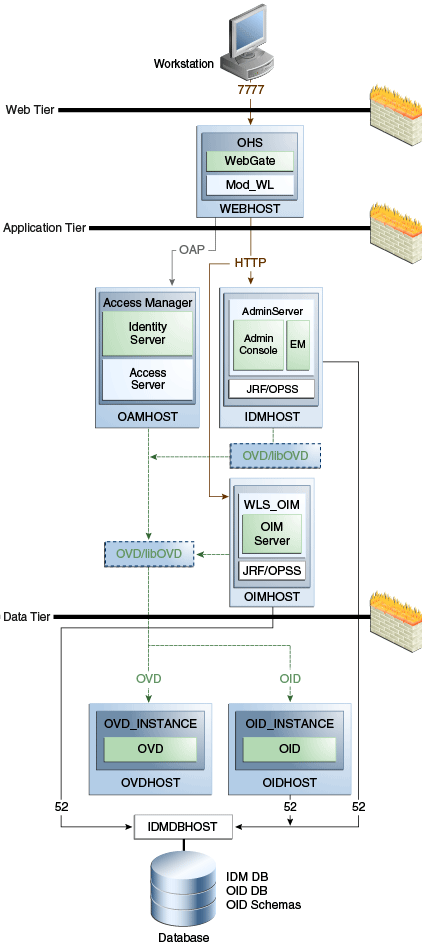
1.2.1.1 Single Domain Architecture
In the single-domain architecture, the Oracle Access Management Access Manager and Oracle Identity Manager servers are configured on the same Oracle WebLogic Server.
Figure 1-1 shows the basic single-domain integration topology:
In this topology all the IdM components are configured in the same WebLogic domain, so they are administered by one WebLogic administration server.
Note:
The figure shows some representative ports. For a complete list, see About Firewalls and Ports in the Oracle Fusion Middleware Enterprise Deployment Guide for Oracle Identity Management.
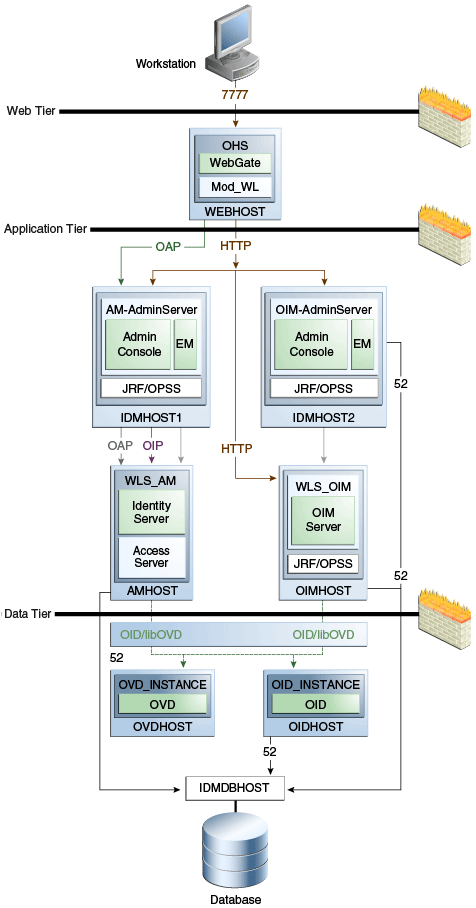
1.2.1.2 Double (Split) Domain Architecture
Figure 1-2 shows a variation of the previous integration topology. Here, the Access Manager and Oracle Identity Manager servers are configured on separate WebLogic domains:
In this topology the Access Manager server (AMHOST) and the Oracle Identity Manager server (OIMHOST) are configured in separate WebLogic domains, so each is administered by its own administration server.
Note:
The figure shows some representative ports. For a complete list, see About Firewalls and Ports in the Oracle Fusion Middleware Enterprise Deployment Guide for Oracle Identity Management.
1.2.1.3 The Three Tier Architecture
This architecture can be viewed as consisting of three layers or zones:
-
The Web Tier consists of the HTTP server and handles incoming Web traffic.
-
The Application Tier contains identity management applications for managing identities and access, including Oracle Identity Manager and Oracle Access Manager.
-
The Data Tier, here considered to include the directory servers, hosts LDAPs and database.
1.2.1.4 Understanding the Web Tier
The web tier is in the DMZ Public Zone. The HTTP servers are deployed in the web tier.Most Identity Management components can function without the web tier. However, the web tier is required to support enterprise level single sign-on using products such as Access Manager.
The web tier is structured as follows in the single-node topology:
-
WEBHOST has Oracle HTTP Server, WebGate (an Access Manager component), and the mod_wl_ohs plug-in module installed. The mod_wl_ohs plug-in module enables requests to be proxied from Oracle HTTP Server to a WebLogic Server running in the application tier.WebGate, an Access Manager component in Oracle HTTP Server, uses Oracle Access Protocol (OAP) to communicate with Access Manager running on OAMHOST. WebGate and Access Manager are used to perform operations such as user authentication.
1.2.1.5 Understanding the Application Tier
The application tier is the tier where Java EE applications are deployed. Products such as Oracle Identity Manager, Oracle Access Management Identity Federation, and Oracle Enterprise Manager Fusion Middleware Control are among key Java EE components deployed in this tier.
The Identity Management applications in the application tier interact with the directory tier as follows:
-
They leverage the directory tier for enterprise identity information.
-
They leverage the directory tier (and sometimes the database in the data tier) for application metadata.
-
Fusion Middleware Control Console provides administrative functions to the components in the application and directory tiers.
-
Oracle WebLogic Server has built-in web server support. If enabled, the HTTP listener exists in the application tier as well.
1.2.1.6 Understanding the Data Tier
The data tier is the deployment layer where all the LDAP services reside. This tier includes products such as Oracle Internet Directory (OIDHOST), Oracle Virtual Directory (OVDHOST), and Oracle Database (IDMDBHOST).
The data tier stores two types of information:
-
Identity Information: Information about users and groups resides in the identity store.
-
Oracle Platform Security Services (OPSS): Information about security policies and about configuration resides in the policy store.
Policy information resides in a centralized policy store that is located within a database. You may store identity information in Oracle Internet Directory or in another directory.
If you store the identity details in a directory other than Oracle Internet Directory you can use Oracle Virtual Directory to present all the identity data in a single consolidated view that Oracle Identity Management components can interpret. For details, see Chapter 6.
Note:
Oracle Identity Manager uses Oracle Virtual Directory server or libOVD to access third-party directories.
1.2.2 The Enterprise Integration Topology
Unlike the single-node topologies described in this document, an enterprise integration topology takes into account such features as high availability, failover, and firewalls, and is beyond the scope of this document.
See the Oracle Fusion Middleware Enterprise Deployment Guide for Oracle Identity Management, which explains the concepts of the enterprise integration topology and provides implementation procedures.
1.2.3 Using Multiple Directories for an Identity Store
Although the integration scenarios in this document focus on a simple identity store topology consisting of an Oracle Internet Directory LDAP server, your site may have some user data in a third-party directory, such as Microsoft Active Directory, and other user data in Oracle Internet Directory.
To account for this topology, you can use Oracle Virtual Directory to present all the identity data in a single consolidated view that Oracle Identity Management components can interpret.
For configuration details, see Chapter 6.
1.2.4 Integration Terminology
Table 1-1 shows key terms and acronyms that are used to describe the architecture and topology of an Oracle Fusion Middleware environment:
Table 1-1 Oracle Fusion Middleware Integration Terminology
| Term | Definition |
|---|---|
|
IdM Configuration Tool |
A command-line tool to verify the status of identity management components and to perform certain integration tasks. |
|
Oracle Access Protocol (OAP) |
A secure channel for communication between Webgates and Access Manager servers during authorization. |
|
A Middleware home consists of the Oracle WebLogic Server home, and, optionally, one or more Oracle homes. A Middleware home can reside on a local file system or on a remote shared disk that is accessible through NFS. |
|
|
Oracle HTTP Server (OHS) |
Web server component for Oracle Fusion Middleware that provides a listener for Oracle WebLogic Server. |
|
A WebLogic Server home contains installed files necessary to host a WebLogic Server. The WebLogic Server home directory is a peer of other Oracle home directories underneath the Middleware home directory. |
|
|
An Oracle home contains installed files necessary to host a specific product. For example, the Oracle Identity Management Oracle home contains a directory that contains binary and library files for Oracle Identity Management. An Oracle home resides within the directory structure of the Middleware home. Each Oracle home can be associated with multiple Oracle instances or Oracle WebLogic Server domains. |
|
|
An Oracle instance contains one or more system components, such as Oracle Web Cache, Oracle HTTP Server, or Oracle Internet Directory. The system components in an Oracle instance must reside on the same machine. An Oracle instance directory contains files that can be updated, such as configuration files, log files, and temporary files. An Oracle instance is a peer of an Oracle WebLogic Server domain. Both contain specific configurations outside of their Oracle homes. The directory structure of an Oracle instance is separate from the directory structure of the Oracle home. It can reside anywhere; it need not be within the Middleware home directory. |
|
|
A WebLogic Server domain is a logically related group of Java components. A WebLogic Server domain includes a special WebLogic Server instance called the Administration Server, which is the central point from which you configure and manage all resources in the domain. Usually, you configure a domain to include additional WebLogic Server instances called Managed Servers. You deploy Java components, such as Web applications, EJBs, and Web services, and other resources to the Managed Servers and use the Administration Server for configuration and management purposes only. Managed Servers in a WebLogic Server domain can be grouped together into a cluster. An Oracle WebLogic Server domain is a peer of an Oracle instance. Both contain specific configurations outside of their Oracle homes. The directory structure of an WebLogic Server domain is separate from the directory structure of the WebLogic Server home. It can reside anywhere; it need not be within the Middleware home directory. |
|
|
A system component is a manageable process that is not WebLogic Server. For example: Oracle HTTP Server, WebCache, and Oracle Internet Directory. Includes the JSE component. |
|
|
A Java component is a peer of a system component, but is managed by the application server container. Generally refers to a collection of applications and resources, with generally a 1:1 relationship with a domain extension template. For example: SOA and WebCenter Spaces. |
|
|
Oracle Enterprise Manager Fusion Middleware Control is a Web browser-based, graphical user interface that you can use to monitor and administer an Oracle Fusion Middleware farm. An Oracle Fusion Middleware farm is a collection of components managed by Fusion Middleware Control. It can contain WebLogic Server domains, one or more Managed Servers and the Oracle Fusion Middleware system components that are installed, configured, and running in the domain. |
|
|
Oracle Identity Management |
The suite of identity and access management components in Oracle Fusion Middleware. See Section 1.3 for details. |
|
The Administration Server is the central point from which you configure and manage all resources in the WebLogic domain. |
|
|
The Managed Server is an additional WebLogic Server instance to host business applications, application components, Web services, and their associated resources. Multiple managed servers can operate within the domain. Certain Managed Servers in the domain are created specifically to host Oracle Fusion Middleware components. |
1.3 About Oracle Identity Management Components
This section provides a brief overview of IdM components whose integrations are described in this book, and the benefits of integration. Topics include:
1.3.1 Oracle Internet Directory
Oracle Internet Directory is a general purpose directory service that enables fast retrieval and centralized management of information about dispersed users and network resources. It combines Lightweight Directory Access Protocol (LDAP) Version 3 with the high performance, scalability, robustness, and availability of an Oracle Database.
Oracle Internet Directory can serve as the repository for the identity store, which contains user identities leveraged by identity management components and other applications.
For details about integration with Oracle Internet Directory, see:
1.3.2 Oracle Virtual Directory
Oracle Virtual Directory, an LDAP version 3 enabled service that provides virtualized abstraction of one or more enterprise data sources into a single directory view. Oracle Virtual Directory makes many directories appear to be one local repository, hiding the complexity of data location, format, and protocol from client applications.
For details about integration with Oracle Virtual Directory, see:
1.3.3 Oracle Access Management Access Manager
Oracle Access Management Access Manager provides a full range of Web perimeter security functions that include Web single sign-on; authentication and authorization; policy administration; auditing, and more. All existing access technologies in the Oracle Identity Management stack converge in Access Manager.
For details about integration with Access Manager, see:
1.3.4 Oracle Identity Manager
Oracle Identity Manager is a powerful and flexible enterprise identity management system that automatically manages users' access privileges within enterprise IT resources. Oracle Identity Manager is designed from the ground up to manage user access privileges across all of a firm's resources, throughout the entire identity management lifecycle—from initial creation of access privileges to dynamically adapting to changes in business requirements.
For details about integration with Oracle Identity Manager, see Chapter 3, "Integrating Access Manager, OAAM, and OIM".
1.3.5 Oracle Adaptive Access Manager
Oracle Adaptive Access Manager is Oracle Identity Management's solution for web access real-time fraud detection and multifactor online authentication security for the enterprise.
For details about integration with Oracle Adaptive Access Manager, see:
Note:
Oracle Adaptive Access Manager customizations are beyond the scope of this document. For details on customizations, such as single login page mode, see Oracle Fusion Middleware Developer's Guide for Oracle Adaptive Access Manager.
1.3.6 Oracle Access Management Identity Federation
To enhance support for federated authentication in cloud, web services, and B2B transactions, a SAML-based federation service is being introduced in a single access management server in 11g Release 2 (11.1.2). Oracle Access Management Identity Federation is an enterprise-level, carrier-grade service for secure identity information exchange between partners. Identity Federation protects existing IT investments by integrating with a wide variety of data stores, user directories, authentication providers and applications.
In this initial release Identity Federation is limited to Service Provider mode. Identity Provider mode still requires an Oracle Identity Federation 11gR1 installation.
For details about using the Identity Federation service with Access Manager, see Chapter 4, "Integrating with Identity Federation".
1.3.7 Oracle Identity Navigator
Oracle Identity Navigator is a web-based application that you access through a browser. You can use it to access consoles for Access Manager, Oracle Adaptive Access Manager, Oracle Identity Manager, Directory Services (ODSM), and other Oracle Identity Management components.
For details about integration with Access Manager, see Chapter 5, "Integrating with Oracle Identity Navigator".
1.4 Integration Quick Links
Table 1-2 provides links to the integration procedures described in this document.
Table 1-2 Links to Integration Procedures
| Components to Integrate | Link |
|---|---|
|
Post-install LDAP Synchronization with Oracle Identity Manager |
|
|
Oracle Virtual Directory and Oracle Identity Manager |
|
|
Oracle Virtual Directory and Access Manager |
|
|
Access Manager and Oracle Identity Manager |
|
|
Access Manager, Oracle Identity Manager, and Oracle Adaptive Access Manager |
|
|
Access Manager and Identity Federation |
|
|
Access Manager and Oracle Identity Navigator |
|
|
Multi-Directory identity store |
|
|
Access Manager and Oracle Adaptive Access Manager |
1.5 Common Integration Scenarios
This section describes common scenarios to integrate Access Manager, Oracle Adaptive Access Manager, and Oracle Identity Manager and the resource protection and collection and password management benefits.
1.5.1 Resource Protection and Credential Collection Scenarios (Advanced Integration)
This section describes the process flow when a user tries to access a protected resource in an Access Manager and OAAM "Advanced" integration. The Advanced integration option provides advanced features such as OTP Anywhere and challenge processor and shared library frameworks, but requires a full OAAM deployment. Figure 1-3 illustrates the following scenarios:
Figure 1-3 Resource Protection and Credential Collection Flow
Description of "Figure 1-3 Resource Protection and Credential Collection Flow"
Initial steps that pertain to all three cases are listed as follows:
-
A user tries to access a resource protected by Access Manager via TAPscheme configured with Oracle Adaptive Access Manager.
-
The Oracle Access Management Agent intercepts the (unauthenticated) request and redirects the user to the OAAM Server with encrypted TAP token.
-
The OAAM Server checks for the current authentication status of the user from the TAP token. The TAP token contains current authentication level. Depending on the value of the current authentication level, Oracle Adaptive Access Manager can determine whether the user is authenticated or not. Accordingly, the user will be taken through one of the following flows.
For information on authentication flows, see "Authentication Flow" in Oracle Fusion Middleware Administrator's Guide for Oracle Adaptive Access Manager.
1.5.1.1 Case 1: The User is Authenticated by Access Manager with Oracle Adaptive Access Manager Performing Step Up Authentication
In this scenario, the user is already authenticated when he recently accessed another resource with a lower authentication level using Access Manager. When the user tries to access a resource protected by TAPscheme, Oracle Adaptive Access Manager does not show the user name and password pages since the user is already authenticated. However the following flows are executed in Oracle Adaptive Access Manager depending on whether the user has already registered with Oracle Adaptive Access Manager or not.
User has registered with Oracle Adaptive Access Manager
If the user has registered with Oracle Adaptive Access Manager, the process flow is as follows:
-
Oracle Adaptive Access Manager fingerprints the user device (device fingerprinting)
-
Oracle Adaptive Access Manager runs the post-authentication rules. It determines the user's risk score and executes any actions (for example, KBA or OTP) or alerts that are specified in the policy.
-
The user might also be taken to the challenge flow depending on the risk score.
-
If the challenge flow is successful and the user has the appropriate profile registered, Oracle Adaptive Access Manager constructs the TAP token with the user name and sends it back to Access Manager. Access Manager asserts the token sent back. After asserting the token, Access Manager creates its cookie and continues the normal single-sign on flow in which it redirects the user to the protected resource.
User has not registered with Oracle Adaptive Access Manager
If the user has not registered with Oracle Adaptive Access Manager, the process flow is as follows:
-
If the user is not registered, he may be asked to register, for example, KBA or OTP. Registration is required depending on security requirements, which specify whether the registration is mandatory or optional.
-
Oracle Adaptive Access Manager fingerprints the user device (device fingerprinting).
-
Oracle Adaptive Access Manager runs the post-authentication rules. It determines the user's risk score and executes any actions (for example, KBA or OTP) or alerts that are specified in the policy.
-
If the risk score is sufficiently high, then the user might be blocked because it is not possible to take him to the challenge flow because of incomplete registration.
-
However, if there is no risk, the user is taken through profile registration and after that, Oracle Adaptive Access Manager constructs the TAP token with the user name and sends it back to Access Manager. Access Manager asserts the token sent back. After asserting the token, Access Manager creates its cookie and continues the normal single-sign on flow in which it redirects the user to the protected resource.
1.5.1.2 Case 2: User is Not Authenticated by Access Manager
If the user is not authenticated, the process flow is as follows.
-
The OAAM Server presents the user with the OAAM user name page.
-
The user submits his user name on the OAAM user name page.
-
Oracle Adaptive Access Manager fingerprints the user device and runs pre-authentication rules to determine if the user should be allowed to proceed to the OAAM password page.
-
If the user is allowed to proceed, the virtual authentication device rules are run during the Authentication Pad checkpoint. These rules determine which virtual authenticator to display in the OAAM password page.
-
If the user has registered with Oracle Adaptive Access Manager, the OAAM Server displays the OAAM password page with either the personalized TextPad or KeyPad.
-
If the user has not registered, Oracle Adaptive Access Manager displays the OAAM password page with the Generic TextPad.
-
The user submits his password on the OAAM password page.
-
The credentials collected from Oracle Adaptive Access Manager is verified against the identity store using the Oracle Access Management OAP API. After validation on the Access Manager side, Oracle Adaptive Access Manager runs the post-authentication rules.
-
Oracle Adaptive Access Manager interacts with the user to establish identity to perform the desired action. Oracle Adaptive Access Manager determines the user's risk score and executes any actions (for example, KBA or OTP) or alerts that are specified in the policy.
-
If the user is not registered, he may be asked to go through registration, for example, KBA or OTP.
-
Registration is required depending on security requirements, which specify whether the registration is mandatory or optional.
-
If authentication is successful and the user has the appropriate profile registered, Oracle Adaptive Access Manager constructs the TAP token with the user name and sends it back to Access Manager. Access Manager asserts the token sent back. After asserting the token, Access Manager creates its cookie and continues the normal single-sign on flow in which it redirects the user to the protected resource.
1.5.1.3 Case 3: User is Authenticated by Access Manager and Oracle Adaptive Access Manager Does Not Perform Step Up Authentication
If the user is already authenticated at a higher level than the level required to access the resource protected by TAPscheme, then the flow is not interrupted by Oracle Adaptive Access Manager and the user can directly access the protected resource.
1.5.2 Resource Protection and Credential Collection Scenario (Basic Integration)
This section describes the process flow when a user tries to access a protected resource in an Access Manager and OAAM "Basic" integration. This deployment provides login security and Knowledge Based Authentication (KBA) without requiring a separate OAAM Server.
-
A user tries to access a resource protected by Access Manager.
-
Oracle Access Management WebGate intercepts the request and redirects the user to the OAAM Server.
-
Access Manager calls the OAAM APIs to run pre-authentication rules to determine if the user should be allowed to proceed.
-
Based on the rule result such as ALLOW, BLOCK, or DENY, Access Manager displays the appropriate pages.
-
If the user is allowed to proceed, Access Manager displays the password page.
-
The user submits his password on the password page.
-
The credentials collected from Access Manager is verified against the identity store.
-
After validation, Access Manager calls the OAAM APIs again to run the post-authentication rules.
-
Access Manager displays the appropriate set of pages based on the rule result, which are REGISTER USER, REGISTER QUESTIONS, REGISTER USER [optional], CHALLENGE, ALLOW, or BLOCK.
For example, if the result is REGISTER USER, as part of the user registration process (for first time login), the user is asked to select and answer three challenge questions.
For example, if the result is CHALLENGE, Access Manager displays a challenge question page with the security question displayed.
1.5.3 Password Management Scenarios
Common management scenarios supported by these deployment modes include:
1.5.3.1 Access Manager Integrated with Oracle Identity Manager
Figure 1-4 shows how password management is achieved when Access Manager and Oracle Identity Manager are integrated.
The flow of interactions between the components is as follows:
-
A user tries to access a resource protected by Access Manager.
-
The Oracle Access Management WebGate intercepts the (unauthenticated) request.
-
WebGate redirects the user to the Access Manager login service, which performs validation checks.
-
If Access Manager finds any password management trigger conditions, such as password expiry, it redirects users to Oracle Identity Manager.
-
Oracle Identity Manager interacts with the user to establish the user's identity and carry out the appropriate action, such as resetting the password.
-
Access Manager logs the user in by means of auto-login, and redirects the user to the Access Manager-protected resource which the user was trying to access in Step 1.
1.5.3.2 Self-Registration
In this scenario, the user does not have an account but tries to access an Access Manager-protected resource. An Oracle Access Management 11g WebGate intercepts the request, detects that the user is not authenticated, and redirects the user to the Oracle Access Management Credential Collector (or 10g authenticating WebGate), which shows the Access ManagerLogin page containing a Register New Account link.
On selecting this link, the user is securely redirected to the Oracle Identity Manager Self Registration URL. Oracle Identity Manager interacts with the user to provision his account.
The Welcome Page is an unprotected page from which the self-registration/account creation can be initiated. This page contains two links, in addition to any introductory text or branding information. The links are:
-
Register New Account - This is an unprotected URL to the corresponding application's registration wizard
-
Login - This is a protected URL which serves as the landing page to which the user is directed after successfully completing the login.
Note:
Any application protected by a single sign-on system with the self-registration requirement is expected to support a self-registration page. The options are:
-
Self-registration using the default self-registration page or a customized version of the page.
This is the most common option and is covered here.
-
Self-registration using anonymous pages in other applications.
If the application dictates that the user be automatically logged in at the end of the registration process, it can implement this by using the Oracle Platform Security Services APIs.
See Also:
Oracle Fusion Middleware Security Overview for more information about Oracle Platform Security Services.
The account creation flow is as follows:
-
The user (using his browser) accesses the application's welcome page, which contains a Register New Account link.
-
The user clicks the Register New Account link, which takes the user to a self-registration page provided by the application.
-
The user interacts with the application to self-register.
-
On completion, the application performs an auto-login for the user.
The protected application is expected to send an SPML request to Oracle Identity Manager to create the user. After this, the application could choose to do one of the following:
-
The application may choose not to auto-login the user. The application redirects the user to the protected landing page URL. Access Manager then shows the login page and takes the user through the login flow.
-
If there is no approval associated with the request, the application can make use of the Oracle Platform Security Services (OPSS) APIs to conduct an auto-login to the specific landing page URL and respond with a redirect request with that URL (along with the SSO cookie). This takes the user directly to the landing page without bringing up the login page.
-
Auto-login cannot be done if approval is needed. The application determines which profile to use at the time of SPML request. The application needs to respond with an appropriate page indicating that the request has been submitted.
1.5.3.3 Password Change
The Change Password flow enables users to change their password.
Password Change Flow with Access Manager and Oracle Identity Manager
In this situation, the user successfully logs into Access Manager but is required to immediately change the password. The user is not authorized to access protected resources until the password is changed and challenges have been set up.
On successful login, Access Manager detects if the triggering condition is in effect and redirects the user to the Oracle Identity Manager Change Password URL. Oracle Identity Manager facilitates the user password change or challenge set-up and resets the triggering condition.
On completion, Oracle Identity Manager redirects the user to the protected resource.
This situation is triggered in the following cases:
-
The
Change Password upon Loginflag is on. This occurs:-
when a new user is created
-
when the administrator resets a user's password
-
-
The password has expired.
This flow describes the situation where a user logs in to an Access Manager-protected application for the first time, and is required to change password before proceeding.
The following describes the Change Password flow:
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate (SSO Agent) intercepts the request and redirects the user to the Access Manager Login Page.
-
The user submits credentials, which are validated by Access Manager.
-
Access Manager next determines if any of the First Login trigger conditions are valid. If so, Access Manager redirects the user to the Oracle Identity Manager Change Password URL.
-
Oracle Access Management WebGate (SSO Agent) intercepts the request, determines that Oracle Identity Manager is protected by the Anonymous Authentication Policy, and allows the user request to proceed.
-
Oracle Identity Manager interacts with the user to enable the user to change his password. On completion, Oracle Identity Manager updates the attributes that triggered the First Login flow. Oracle Identity Manager then performs a user auto-login.
-
Oracle Identity Manager notifies Access Manager of the successful first login.
-
Oracle Identity Manager redirects the user to the application URL the user tried to access in step 1.
Password Change Flow - Access Manager, Oracle Adaptive Access Manager, and Oracle Identity Manager Integrated
In this scenario, the user is at the OAAM password page and clicks the Change Your Password link.
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate intercepts the (unauthenticated) request.
-
Oracle Access Management WebGate redirects the user to the OAAM Server and passes a redirect URL.
-
The OAAM Server presents the user with the OAAM user name page.
-
The user submits his user name on the OAAM user name page.
-
Oracle Adaptive Access Manager fingerprints the user device (a desktop computer, laptop computer, PDA, cell phone, kiosk, or other web enabled device) and runs pre-authentication rules to determine if the user should be allowed to proceed to the OAAM password page.
-
If the user is allowed to proceed, the OAAM Server displays the OAAM password page with the strong authenticator specified by the virtual authentication device rules.
-
The user submits his password on the OAAM password page.
-
During authentication, Oracle Adaptive Access Manager calls the Oracle Access Management Java APIs to validate the credentials.
-
If authentication is successful and the user has registered questions, but he wants to reset his password, the user clicks the Change Password link.
-
The user is redirected to the Change Password URL of Oracle Adaptive Access Manager, which allows the users to change his password.
-
Oracle Adaptive Access Manager collects the current password and the new password, and confirms the password from the user using its authenticators.
-
Password policy information, obtained from Oracle Identity Manager, is displayed to guide the user to select the appropriate password.
-
Oracle Adaptive Access Manager makes Oracle Identity Manager calls to update the password in the repository.
-
If the update is successful, Oracle Adaptive Access Manager redirects the user to the resource protected by Access Manager.
1.5.3.4 Forgot Password
The Forgot Password flow allows users to reset their password after successfully answering all challenge questions.
Forgot Password Flow for Access Manager/Oracle Identity Manager Integration
In this scenario, the user is at the Access Manager Login page and clicks the Forgot Password link. Access Manager redirects the user to the Oracle Identity Manager Forgot Password URL, and passes the destination URL to which Oracle Identity Manager must redirect upon a successful password change as a query parameter (backURL).
Oracle Identity Manager asks the user the challenge questions. Upon providing the correct responses, the user is allowed to specify a new password.
On completion, Oracle Identity Manager redirects the user to the protected resource.
The Forgot Password flow is as follows:
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
The Oracle Access Management WebGate (SSO Agent) intercepts the request and redirects the user to the Access Manager Login Page.
-
The user clicks on the Forgot Password link on the Access Manager Login page, which sends the user to the Oracle Identity Manager Forgot Password URL.
-
Oracle Identity Manager interacts with the user to enable the user to reset the password. On completion, Oracle Identity Manager performs a user auto-login.
-
Oracle Identity Manager redirects the user to the application URL to which access was attempted in step 1.
Forgot Password Flow for Access Manager/Oracle Identity Manager/Oracle Adaptive Access Manager Integration
With Oracle Adaptive Access Manager and Oracle Identity Manager integration, the forgot password feature is made available as a link from the OAAM password page. The flow starts when the user is at the OAAM password page and clicks the Forgot your password link.
The flow is as follows:
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate intercepts the (unauthenticated) request.
-
Oracle Access Management WebGate redirects the user to the OAAM Server.
-
The OAAM Server presents the user with the OAAM user name page.
-
The user submits his user name on the OAAM user name page.
-
Oracle Adaptive Access Manager fingerprints the user device (a desktop computer, laptop computer, PDA, cell phone, kiosk, or other web enabled device) and runs pre-authentication rules to determine if the user should be allowed to proceed to the OAAM password page.
-
If the user is allowed to proceed, the OAAM Server displays the OAAM password page with the strong authenticator specified by the virtual authentication device rules.
-
The user clicks the Forgot your password link on the OAAM password page.
-
Oracle Adaptive Access Manager presents the user with a pre-registered set of challenge questions.
-
The user provides the answers to the challenge questions.
-
Oracle Adaptive Access Manager uses fuzzy logic to validate the answers to challenge questions.
-
If the user provided correct responses, he is redirected to the Password Reset page.
-
Password policy text from Oracle Identity Manager is retrieved by Oracle Adaptive Access Manager by making calls to Oracle Identity Manager, and then shown in the Reset Password page.
-
The user enters the new password.
-
Oracle Adaptive Access Manager calls Oracle Identity Manager to update the repository with the new password.
-
If the update is successful, Oracle Adaptive Access Manager redirects the user to the resource protected by Access Manager.
1.5.3.5 Account Lock and Unlock
Access Manager keeps track of login attempts and locks the account when the count exceeds the established limit.
When an account is locked, Access Manager displays the Help Desk contact information.
When contacted by the end user, the Help Desk unlocks the account using the Oracle Identity Manager administrative console. Oracle Identity Manager then notifies Access Manager about the changes.
When the number of unsuccessful user login attempts exceeds the value specified in the password policy, the user account is locked. Any login attempt after the user account has been locked displays a page that provides information about the account unlocking process, which will need to be customized to reflect the process (Help Desk information or similar) that is followed by your organization.
The following describes the account locking/unlocking flow:
-
Using a browser, a user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate (SSO Agent) intercepts the request and redirects the user to the Access Manager login page.
-
The user submits credentials that fail Access Manager validation. Access Manager renders the login page and asks the user to resubmit his or her credentials.
-
The user's unsuccessful login attempts exceed the limit specified by the policy. Access Manager locks the user account and redirects the user to the Access Manager Account Lockout URL, which displays help desk contact information.
-
The user contacts the help desk over the telephone and asks an administrator to unlock the account.
-
Oracle Identity Manager notifies Access Manager of the account unlock event.
-
The user attempts to access an application URL and this event triggers the normal Oracle Access Management single sign-on flow.
1.5.3.6 Challenge Setup
The Challenge Setup enables users to register challenge questions and answers.
Challenge Setup Flow for Access Manager-Oracle Identity Manager Integration
Access Manager detects and redirects on password trigger conditions:
-
Password Policy is updated to increase the required number of challenges.
-
Password Policy is updated to require challenges .
When such redirection happens, Oracle Identity Manager checks if the challenge questions are set. If not, it asks the user to set up challenge questions in addition to resetting the password.
The following describes the flow:
Note:
The flow assumes First Login is not required.
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate (SSO agent) intercepts the request and redirects the user to the Access Manager Login Page.
-
The user submits credentials, which are validated by Access Manager. If a password triggering condition is detected, Access Manager redirects the user to the Oracle Identity Manager change password URL.
-
The Oracle Access Management WebGate (SSO agent) intercepts the request, determines that Oracle Identity Manager is protected by the anonymous authentication policy, and allows the user request to proceed.
-
Oracle Identity Manager interacts with the user to set up the challenges. On completion, Oracle Identity Manager updates the attributes that triggered the set challenges flow.
-
Oracle Identity Manager redirects the user to the application URL that the user attempted to access in Step 1.
Challenge Setup Flow for Access Manager-Oracle Identity Manager-Oracle Adaptive Access Manager Integration
In this scenario, the user is successfully authenticated but is required to register challenge questions. The user is not authorized to access protected resources until the challenges questions have been registered.
Note:
When adding Oracle Adaptive Access Manager to existing Oracle Identity Manager deployments, you will need to forego all the existing questions and answers that are registered in Oracle Identity Manager. Instead, users are asked to register the challenge questions again in Oracle Adaptive Access Manager on the next login.
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate intercepts the (unauthenticated) request.
-
Oracle Access Management WebGate redirects the user to the OAAM Server and passes a redirect URL.
-
Oracle Adaptive Access Manager presents the user with the OAAM user name page.
-
The user submits his user name on the OAAM user name page.
-
Oracle Adaptive Access Manager fingerprints the user device (a desktop computer, laptop computer, PDA, cell phone, kiosk, or other web enabled device) and runs pre-authentication rules to determine if the user should be allowed to proceed to the OAAM password page.
-
If the user is allowed to proceed, the OAAM Server displays the OAAM password page with the strong authenticator specified by the virtual authentication device rules.
-
The user submits his password on the OAAM password page.
-
During authentication, Oracle Adaptive Access Manager calls Access Manager to validate the credentials.
-
After authentication, Oracle Adaptive Access Manager checks if the user has registered challenge questions.
-
If the user has not registered for challenges, Oracle Adaptive Access Manager interacts with the user to set up the challenges (select challenge questions and register answers and/or set up an OTP profile).
-
If the registration is successful Oracle Adaptive Access Manager redirects the user to the Access Manager protected resource.
1.5.3.7 Challenge Reset
Challenge Reset enables users to reset their challenge registration. This feature is available when Access Manager is integrated with Oracle Adaptive Access Manager.
The flow is as follows:
-
Using a browser, the user tries to access an application URL that is protected by Access Manager.
-
Oracle Access Management WebGate intercepts the (unauthenticated) request.
-
Oracle Access Management WebGate redirects the user to the OAAM Server and passes a redirect URL.
-
The OAAM Server presents the user with the OAAM user name page.
-
The user submits his user name on the OAAM user name page.
-
Oracle Adaptive Access Manager fingerprints the user device (a desktop computer, laptop computer, PDA, cell phone, kiosk, or other web enabled device) and runs pre-authentication rules to determine if the user should be allowed to proceed to the OAAM password page.
-
If the user is allowed to proceed, the OAAM Server displays the OAAM password page with the strong authenticator specified by the virtual authentication device rules.
-
The user submits his password on the OAAM password page.
-
During authentication, Oracle Adaptive Access Manager calls Access Manager to validate the credentials.
-
If authentication is successful and the user has questions registered, but he wants to reset his challenge questions, the user clicks the Reset Challenge link.
-
The user is redirected to Oracle Adaptive Access Manager where he can reset challenge questions.
-
After resetting the challenge registration, Oracle Adaptive Access Manager prompts the user to register for challenge.
-
If the user did not complete the registration, they are prompted for registration on the next login.
1.6 System Requirements and Certification
Refer to the system compatibility, requirements and certification documentation for information about hardware and software requirements, platforms, databases, and other information.
The compatibility documentation describes compatibility and interoperability considerations that may arise when you install, patch, or upgrade Oracle Fusion Middleware 11g components. For details, see Oracle Fusion Middleware Interoperability and Compatibility Guide for Oracle Identity and Access Management.
The system requirements document covers information such as hardware and software requirements, minimum disk space and memory requirements, and required system libraries, packages, or patches.
The certification document covers supported installation types, platforms, operating systems, databases, JDKs, directory servers, and third-party products.
For the latest requirements and certification documentation refer to the table "Oracle Fusion Middleware Certification Matrices" in the Oracle Fusion Middleware Interoperability and Compatibility Guide for Oracle Identity and Access Management.
1.7 Using My Oracle Support for Additional Troubleshooting Information
You can use My Oracle Support (formerly MetaLink) to help resolve Oracle Fusion Middleware problems. My Oracle Support contains several useful troubleshooting resources, such as:
-
Knowledge base articles
-
Community forums and discussions
-
Patches and upgrades
-
Certification information
Note:
You can also use My Oracle Support to log a service request.
You can access My Oracle Support at https://support.oracle.com.