| Oracle® Retail Integration Bus Implementation Guide Release 19.0 F22947-01 |
|
 Previous |
 Next |
WebLogic ships with a default internal Light-weight Directory Access Protocol (LDAP) authentication provider. In an environment where a couple of domains exist, an administrator can set up users and groups in an internal LDAP provider and use these parameters during login and authentication. Alternatively, in an environment that contains multiple domains, managing/maintaining users and groups can be a difficult task. Oracle recommends that you use a centralized LDAP server to manage/maintain the users and groups. This chapter describes the steps you should take to configure the Oracle Internet Directory (OID) and the Active Directory (AD) LDAP based authentication provider in WebLogic.
An online directory is a specialized database that stores and retrieves collections of information about objects. The information can represent any resources that require management, for example:
Employee names, titles, and security credentials
Information about partners
Information about shared resources such as conference rooms and printers
The information in the directory is available to different clients, such as single sign-on solutions, e-mail clients, and database applications. Clients communicate with a directory server by means of the LDAP. The Oracle Internet Directory is an LDAP directory that uses an Oracle database for storage.
An Active Directory (AD) is a directory service implemented by Microsoft for Windows domain networks. It is included in most Windows Server operating systems. Active Directory is a special-purpose database — it is not a registry replacement. The directory is designed to handle a large number of read and search operations and a significantly smaller number of changes and updates. Active Directory data is hierarchical, replicated, and extensible. Because it is replicated, you do not want to store dynamic data, such as corporate stock prices or CPU performance.In Windows 2000, Active Directory has three partitions. These are also known as naming contexts: do-main, schema, and configuration. The domain partition contains users, groups, contacts, computers, organizational units, and many other object types. Because Active Directory is extensible, you can also add your own classes and/or attributes. The schema partition contains classes and attributes definitions. The configuration partition includes configuration data for services, partitions, and sites.
The architecture diagram describes the configuration of an OID and AD LDAP-based authentication provider used by applications deployed in an WebLogic server environment. 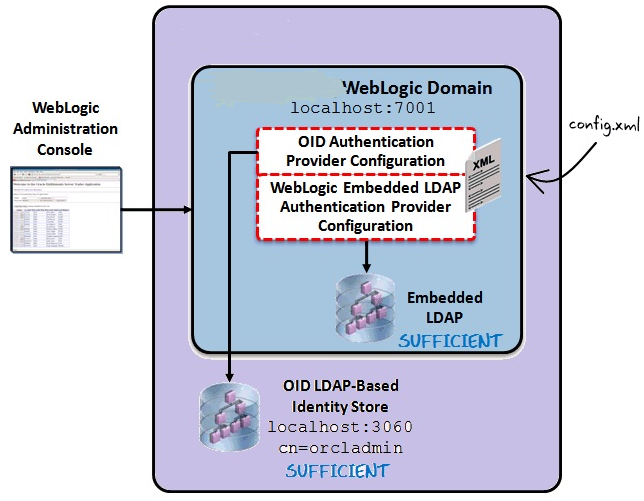
The diagram displays a sample environment and consists of the following:
The WebLogic Server running on port 7001
The WebLogic Administration Console used to configure authentication providers
The WebLogic Embedded LDAP server with a control flag setting of SUFFICIENT
An OID LDAP-based identity store running on port 3060 with a control flag setting of SUFFI-CIENT
The WebLogic config.xml that stores the authentication provider configuration
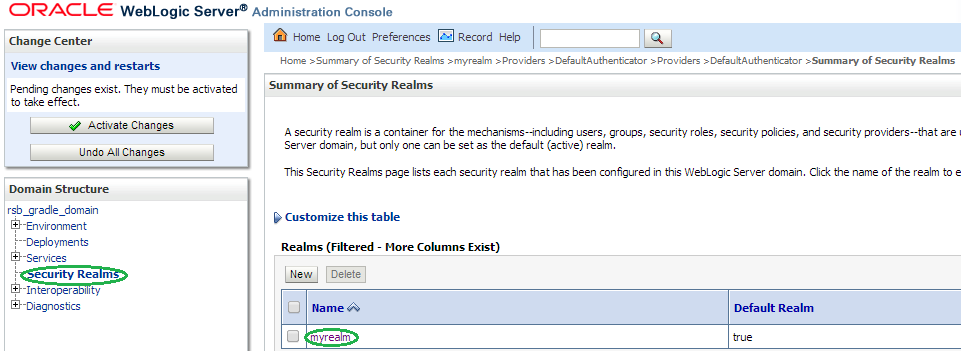
By default, the WebLogic server uses a security realm with the name ”myrealm” that uses an embedded LDAP server (two default users WebLogic & OracleSystemUser) that acts as data store for Authentication, Authorization, Credential Mapping and Role Mapping Provider.
To configure the OID as an authentication provider in WebLogic, take the following steps:
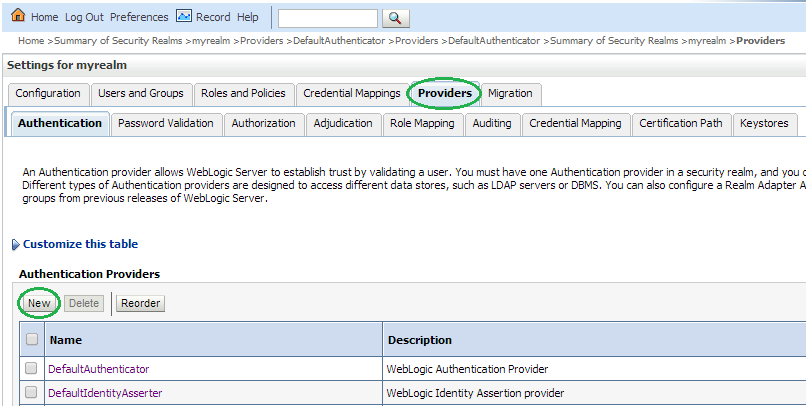
Login to WebLogic Console -> Security Realm -> myrealm.
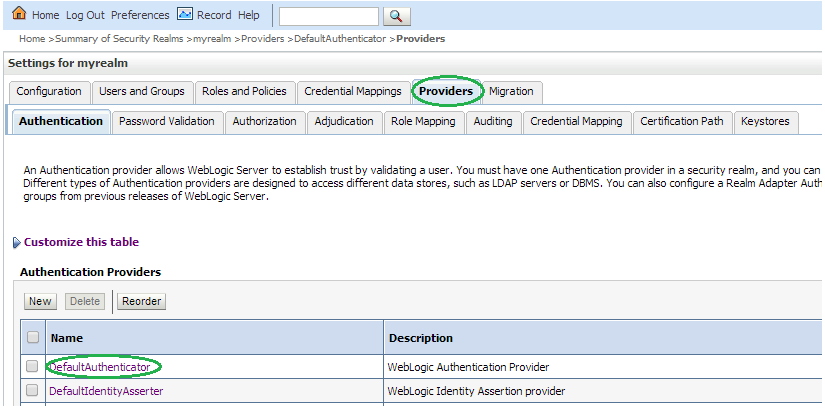
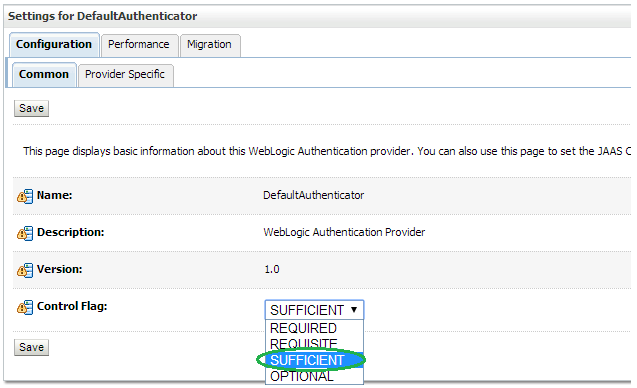
Select tab Providers -> Authentication -> Default Provider (DefaultAuthenticator).
Change the Control Flag (JAAS Flag) parameter from REQUIRED to SUFFICIENT and click Save.
Click New to add a new Authentication Provider.
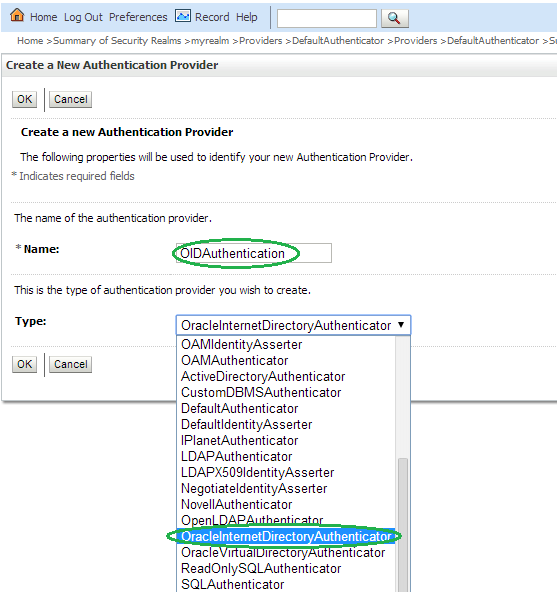
Enter OIDAuthentication as the Name of the new provider. Select OracleInternetDirectoryAuthenticator as Type and then click OK.
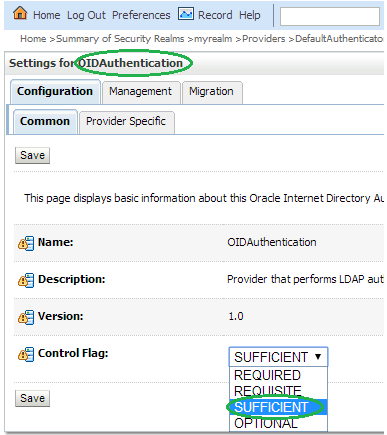
Change the Control Flag to SUFFICIENT for the OIDAuthentication Provider added and click Save.
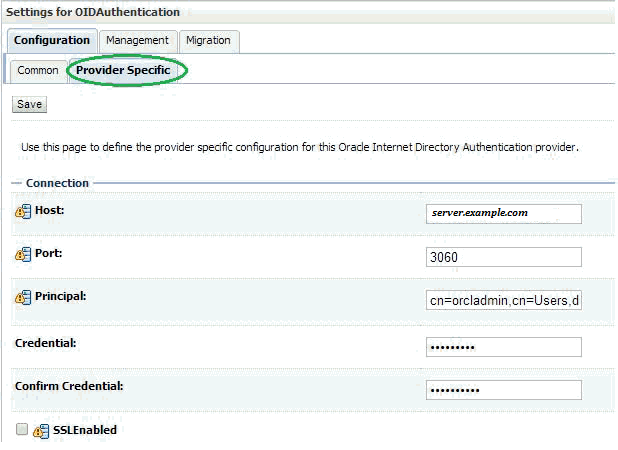
Select the Provider Specific tab and enter your OID server details.
The first section contains the Connection settings for the OID server. Use the appropriate values based on where the OID is hosted and the credentials:
| Name | Value | Purpose |
|---|---|---|
| Host: | server.example.com | The OID host name |
| Port: | 3060 | The standard OID listening port |
| Principal: | cn=orcladmin,cn=Users,dc=idc,dc=oracle,dc=com | The LDAP user that logs into OID on behalf of your authentication provider |
| Credentials: | Password for the principal user | |
| Confirm Credentials: | Confirmation of the password | |
| SSL Enabled: | Unchecked | Enables or disables SSL connectivity |
The second section contains the Users settings for the OID provider. Use appropriate values:
| Name | Value | Purpose |
|---|---|---|
| User Base DN: | cn=Users,dc=idc,dc=oracle,dc=com | The root (base DN) of the LDAP tree where searches are performed for user data |
| All Users Filter: | (&(cn=*)(objectclass=person)) -- Leave as default | The LDAP search filter that is used to show all the users below the User Base DN |
| User From Name Filter: | (&(cn=%u)(objectclass=person)) -- Leave as default | The LDAP search filter used to find the LDAP user by name |
| User Search Scope: | Leave as default | Specifies how deep in the LDAP tree to search for users |
| User Name Attribute: | Leave as default | The attribute of the LDAP user that specifies the user name |
| User Object Class: | Leave as default | The LDAP object class that stores users |
| Use Retrieved User Name as Principal: | Checked | Specifies if the user name retrieved from the LDAP directory will be used as the Principal in the Subject |
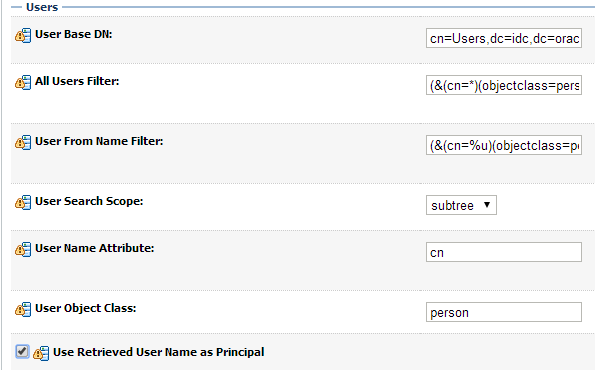
The third section contains the Groups settings for the OID provider. Use appropriate values:
| Name | Value | Purpose |
|---|---|---|
| Group Base DN: | cn=Groups,dc=idc,dc=oracle,dc=com | The root (base DN) of the LDAP tree where searches are per-formed for group data |
| All Groups Filter: | (&(cn=*)(|(objectclass=groupofUniqueNames)(objectclass=orcldynamicgroup))) -- Leave as default | The LDAP search filter that is used to show all the groups below the Group Base DN |
| Group From Name Filter: | (|(&(cn=%g)(objectclass=groupofUniqueNames))(&(cn=%g)(objectclass=orcldynamicgroup))) -- Leave as default | The LDAP search filter used to find the LDAP group by name |
| Group Search Scope: | Leave as default | Specifies how deep in the LDAP tree to search for groups |
| Group Member-ship Searching: | Leave as default | Specifies whether group searches into nested groups are limited or unlimited |
| Max Group Member-ship Search Level: | Leave as default | Specifies how many levels of group membership can be searched. This setting is only valid if GroupMembershipSearching is set to limited |
| Ignore Duplicate Membership: | Unchecked | Determines whether duplicates members are ignored when adding groups. |
Click Save.
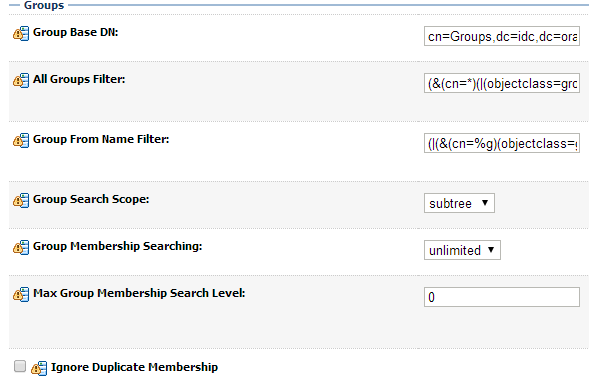
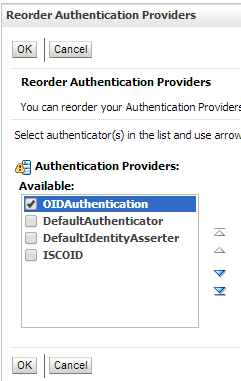
Click Reorder to change the order of your configured authentication providers. In order to ensure that the new OID authenticator is recognized as authentication provider, you must reorder your list of authentication providers so that the OID authentication provider is first in the list.
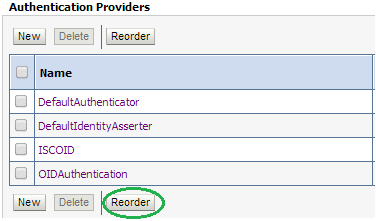
Select the OIDAuthentication and use the arrows on the right to move it into the first position. Click OK.
To verify the OID configuration, take the following steps:
Restart the WebLogic Server for your changes to take effect.
Using the WebLogic Administration Console, select Security Realms > myrealm > Users and Groups tab. The Users sub-tab should be selected by default. The circled users are created in OID and can verify the Provider – OIDAuthentication provider. 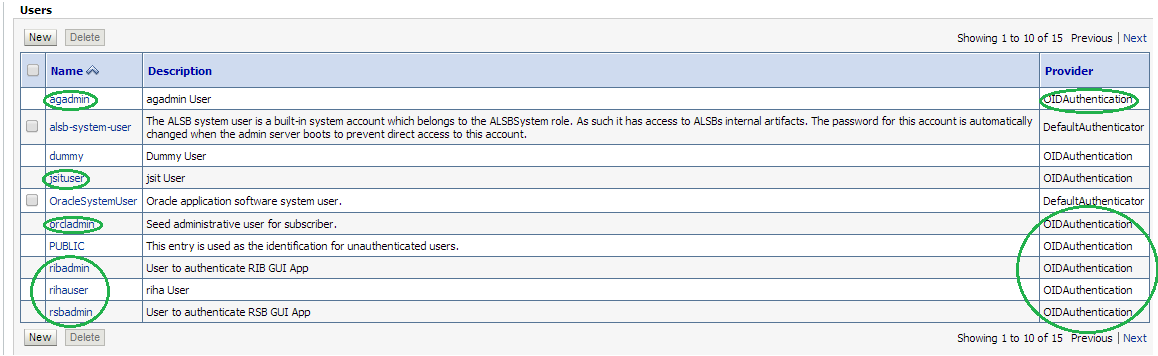
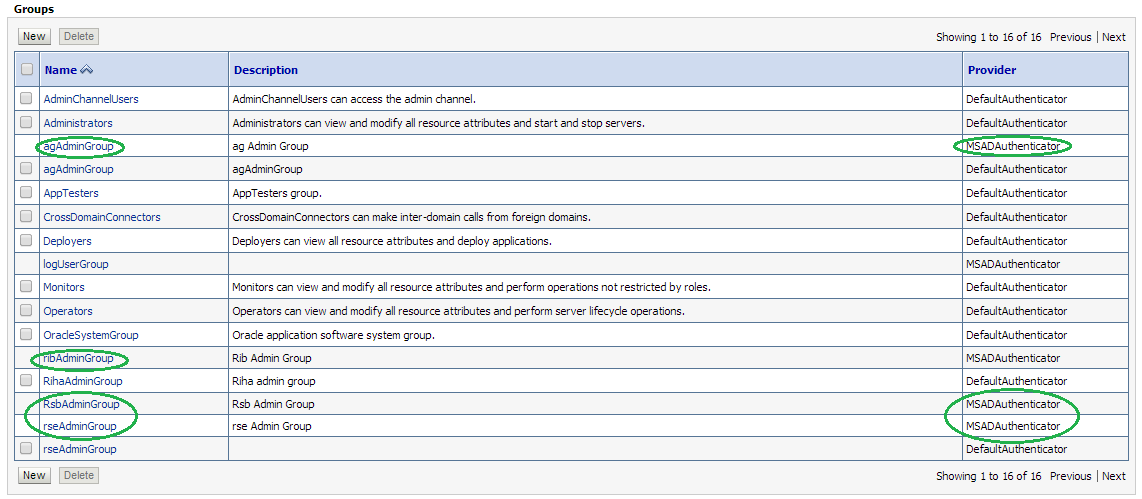
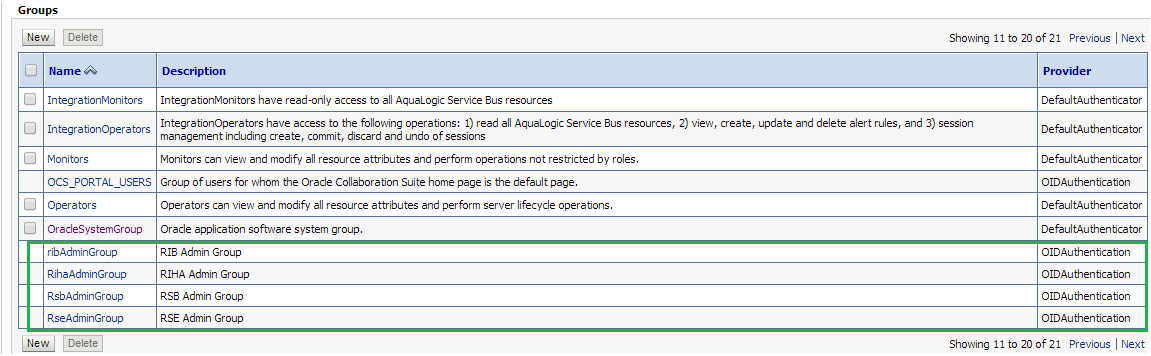
Click the Groups tab to see the list of groups the server can see. The highlighted groups are created in OID and can verify the Provider – OIDAuthentication provider.
LDIF scripts can be used to import users and groups into OID. Two sample scripts are supplied below. The scripts contain users and groups for multiple Oracle Retail integration products. You must review and edit the scripts to match your deployment topology and in-scope applications.
dn: cn=agAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: agAdminGroup
description: ArtifactGenerator Administrator is a group of individuals who can generate artifacts used in the integration products like OracleObject, JavaBeans.
displayname: ArtifactGenerator Administrator
#businessCategory: TBD
uniquemember: cn=agadmin,cn=users,dc=us,dc=oracle,dc=comdn: cn=JmsConsoleAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: JmsConsoleAdminGroup
description: JMS Console Administrator is a group of individuals who can perform various administrator task on jmsconsole like publishing message on topic, browsing messages on topic.
displayname: JMS Console Administrator
#businessCategory: TBD
uniquemember: cn=jmsconsoleadmin,cn=users,dc=us,dc=oracle,dc=com
dn: cn=ribAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: ribAdminGroup
description: RIB Administrator is a group of individuals who can administrator rib-admin-gui. View the adapters state, start/stop adapters, view logs,set the log levels for adapters.
displayname: RIB Administrator
#businessCategory: TBD
uniquemember: cn=ribrmsadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribsimadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribrwmsadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribaipadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=riblgfadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribocdadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribrobadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribtafradmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribrfmadmin,cn=users,dc=us,dc=oracle,dc=com
uniquemember: cn=ribrpmadmin,cn=users,dc=us,dc=oracle,dc=com
dn: cn=IntegrationGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: IntegrationGroup
description: IntegrationGroup is a group of individuals who can invoke rib interface api inject and publish.
displayname: Integration Group
#businessCategory: TBD
uniquemember: cn=integrationuser,cn=users,dc=us,dc=oracle,dc=com
dn: cn=RihaAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: RihaAdminGroup
description: Riha Admin Group is a group of individuals who can administer rib hospital. Can flush the messages stuck in rib error hospital, can retry the messages,view the messages in error hospital and can edit.
displayname: Riha Administrator
#businessCategory: TBD
uniquemember: cn=rihaadmin,cn=users,dc=us,dc=oracle,dc=comdn: cn=RicAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: RicAdminGroup
description: Ric Admin Group is a group of individuals who can administer rib runtime statistics , rsb runtime statistics.
displayname: Ric Administrator
#businessCategory: TBD
uniquemember: cn=ricadmin,cn=users,dc=us,dc=oracle,dc=com
dn: cn=rseAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: rseAdminGroup
description: Rse Admin Group is a group of individuals who can generate webservice provider , consumer.
displayname: RSE Administrator
#businessCategory: TBD
uniquemember: cn=rseadmin,cn=users,dc=us,dc=oracle,dc=com
dn: cn=RfiAdminGroup,cn=groups,dc=us,dc=oracle,dc=com
objectclass: groupOfUniqueNames
objectclass: orclGroup
objectclass: top
cn: RfiAdminGroup
description: RFI Admin
displayname: RFI Administrator
#businessCategory: TBD
uniquemember: cn=rfiadmin,cn=users,dc=us,dc=oracle,dc=com
dn: cn=agadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'AG Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: agadmin
orclsamaccountname: agadmin
sn: agadmin
uid: agadmin
givenname: agadmin
displayname: agadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: agadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=jmsconsoleadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'JMS Console Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: jmsconsoleadmin
orclsamaccountname: jmsconsoleadmin
sn: jmsconsoleadmin
uid: jmsconsoleadmin
givenname: jmsconsoleadmin
displayname: jmsconsoleadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: jmsconsoleadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribrmsadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribrmsadmin
orclsamaccountname: ribrmsadmin
sn: ribrmsadmin
uid: ribrmsadmin
givenname: ribrmsadmin
displayname: ribrmsadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribrmsadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribrpmadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribrpmadmin
orclsamaccountname: ribrpmadmin
sn: ribrpmadmin
uid: ribrpmadmin
givenname: ribrpmadmin
displayname: ribrpmadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribrpmadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribrwmsadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribrwmsadmin
orclsamaccountname: ribrwmsadmin
sn: ribrwmsadmin
uid: ribrwmsadmin
givenname: ribrwmsadmin
displayname: ribrwmsadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribrwmsadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=riblgfadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: riblgfadmin
orclsamaccountname: riblgfadmin
sn: riblgfadmin
uid: riblgfadmin
givenname: riblgfadmin
displayname: riblgfadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: riblgfadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribrobadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribrobadmin
orclsamaccountname: ribrobadmin
sn: ribrobadmin
uid: ribrobadmin
givenname: ribrobadmin
displayname: ribrobadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribrobadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribocdsadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribocdsadmin
orclsamaccountname: ribocdsadmin
sn: ribocdsadmin
uid: ribocdsadmin
givenname: ribocdsadmin
displayname: ribocdsadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribocdsadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribtafradmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribtafradmin
orclsamaccountname: ribtafradmin
sn: ribtafradmin
uid: ribtafradmin
givenname: ribtafradmin
displayname: ribtafradmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribtafradmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribaipadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribaipadmin
orclsamaccountname: ribaipadmin
sn: ribaipadmin
uid: ribaipadmin
givenname: ribaipadmin
displayname: ribaipadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribaipadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribsimadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribsimadmin
orclsamaccountname: ribsimadmin
sn: ribsimadmin
uid: ribsimadmin
givenname: ribsimadmin
displayname: ribsimadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribsimadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ribrfmadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIB Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ribrfmadmin
orclsamaccountname: ribrfmadmin
sn: ribrfmadmin
uid: ribrfmadmin
givenname: ribrfmadmin
displayname: ribrfmadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ribrfmadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=integrationuser, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'Integration' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: integrationuser
orclsamaccountname: integrationuser
sn: integrationuser
uid: integrationuser
givenname: integrationuser
displayname: integrationuser
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: integrationuser@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=rihaadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIHA Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: rihaadmin
orclsamaccountname: rihaadmin
sn: rihaadmin
uid: rihaadmin
givenname: rihaadmin
displayname: rihaadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: rihaadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=ricadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RIC Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: ricadmin
orclsamaccountname: ricadmin
sn: ricadmin
uid: ricadmin
givenname: ricadmin
displayname: ricadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: ricadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=rseadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RSE Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: rseadmin
orclsamaccountname: rseadmin
sn: rseadmin
uid: rseadmin
givenname: rseadmin
displayname: rseadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: rseadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
dn: cn=rfiadmin, cn=Users,dc=us,dc=oracle,dc=com
description: A user for the 'RFI Admin' role.
objectclass: inetOrgPerson
objectclass: organizationalPerson
objectclass: person
objectclass: top
objectclass: orcluser
objectclass: orcluserV2
objectclass: orclIDXPerson
cn: rfiadmin
orclsamaccountname: rfiadmin
sn: rfiadmin
uid: rfiadmin
givenname: rfiadmin
displayname: rfiadmin
userpassword: <update your password here>
employeeNumber:
middleName:
orclHireDate:
telephoneNumber:
facsimileTelephoneNumber:
mail: rfiadmin@example.com
postalAddress:
street:
postalCode:
title:
employeeType:
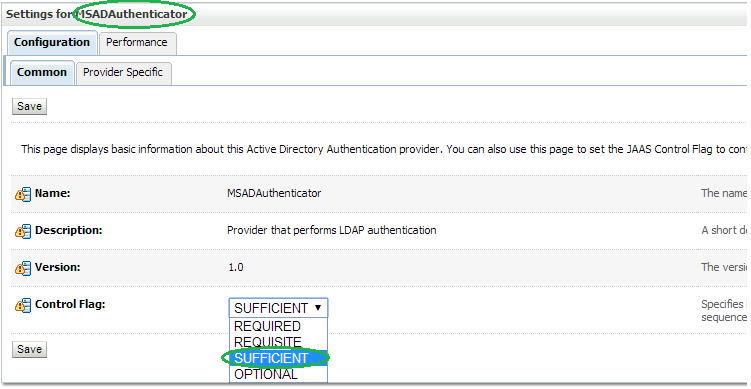
To configure the AD as an authentication provider in WebLogic, take the following steps:
Login to WebLogic Console -> Security Realm -> myrealm.
Select tab Providers -> Authentication -> Default Provider (DefaultAuthenticator).Change the Control Flag (JAAS Flag) from REQUIRED to SUFFICIENT and click Save.
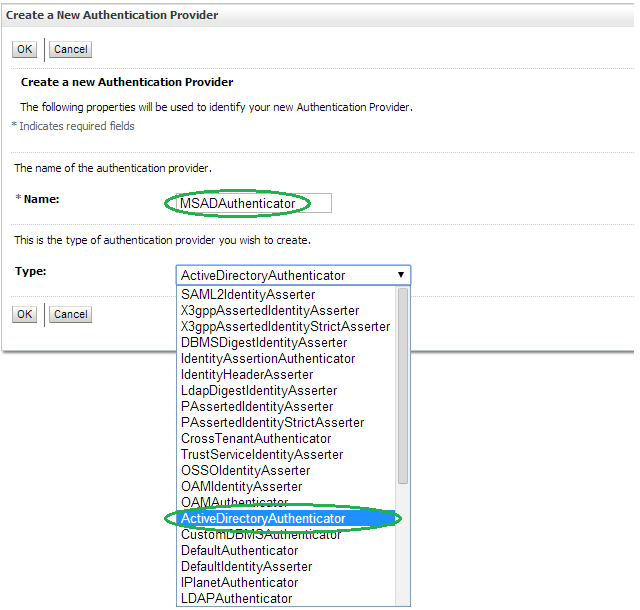
Click New to add a new Authentication Provider.
Enter MSADAuthenticator as the Name. Select ActiveDirectoryAuthenticator as the Type and click OK.
Change the Control Flag to SUFFICIENT for the MSADAuthenticator Provider added and click Save.
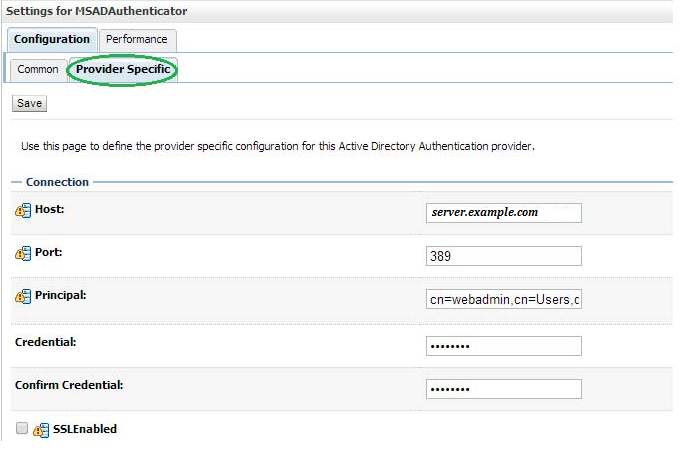
Select Provider Specific tab and enter the Active Directory (AD) server details.
The first section contains the Connection settings for the AD server. Use appropriate values based on where AD is hosted and the credentials:
| Name | Value | Purpose |
|---|---|---|
| Host: | server.example.com | The AD host name |
| Port: | 389 | The standard AD listening port |
| Principal: | cn=webadmin,cn=Users,dc=us,dc=oracle,dc=com | The LDAP user that logs into AD on behalf of your authentication provider |
| Credentials: | Password for the principal user | |
| Confirm Credentials: | Confirmation of the password | |
| SSL Enabled: | Unchecked | Enables or disables SSL connectivity |
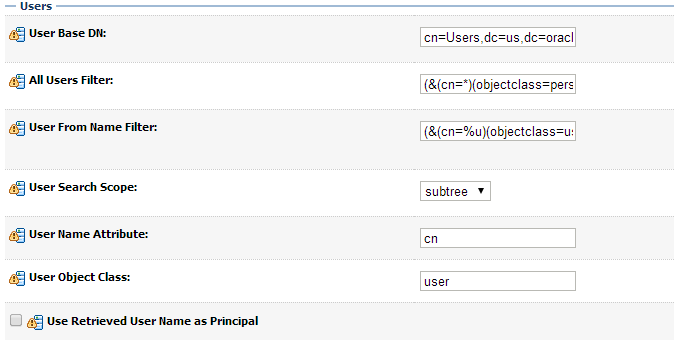
The second section contains the Users settings for the AD provider. Use appropriate values:
| Name | Value | Purpose |
|---|---|---|
| User Base DN: | cn=Users,dc=us,dc=oracle,dc=com | The root (base DN) of the LDAP tree where searches are performed for user data |
| All Users Filter: | (&(cn=*)(objectclass=person)) | The LDAP search filter that is used to show all the users below the User Base DN |
| User From Name Filter: | (&(cn=%u)(objectclass=user)) | The LDAP search filter used to find the LDAP user by name |
| User Search Scope: | Leave as default | Specifies how deep in the LDAP tree to search for users |
| User Name Attribute: | Leave as default | The attribute of the LDAP user that specifies the user name |
| User Object Class: | Leave as default | The LDAP object class that stores users |
| Use Retrieved User Name as Principal: | Unchecked | Specifies if the user name retrieved from the LDAP directory will be used as the Principal in the Subject |
The third section contains the Groups settings for the AD provider. Use appropriate values:
| Name | Value | Purpose |
|---|---|---|
| Group Base DN: | cn=Groups,dc=us,dc=oracle,dc=com | The root (base DN) of the LDAP tree where searches are performed for group data |
| All Groups Filter: | (&(cn=*)(|(objectclass=group))) | The LDAP search filter that is used to show all the groups below the Group Base DN |
| Group From Name Filter: | (&(cn=%g)(objectclass=group)) | The LDAP search filter used to find the LDAP group by name |
| Group Search Scope: | Leave as default | Specifies how deep in the LDAP tree to search for groups |
| Group Member-ship Searching: | Leave as default | Specifies whether group searches into nested groups are limited or unlimited |
| Max Group Membership Search Level: | Leave as default | Specifies how many levels of group membership can be searched. This setting is only valid if GroupMembershipSearching is set to limited |
| Ignore Duplicate Membership: | Unchecked | Determines whether duplicates members are ignored when adding groups. |
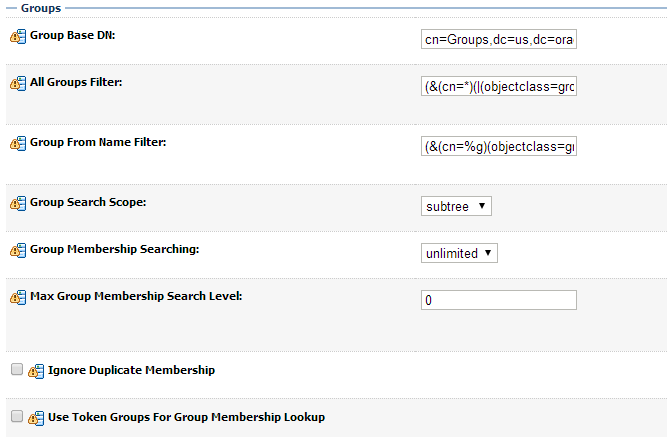
Click Save.
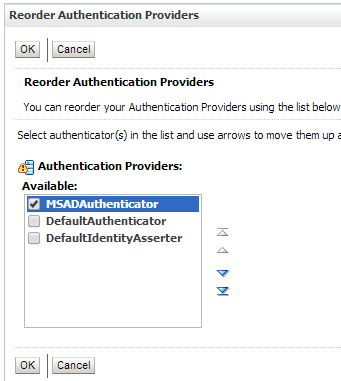
Click Reorder to change the order of your configured authentication providers. In order to ensure that MSAD authenticator is recognized as authentication provider, you must reorder your list of authentication providers so that the MSAD authentication provider is first in the list.
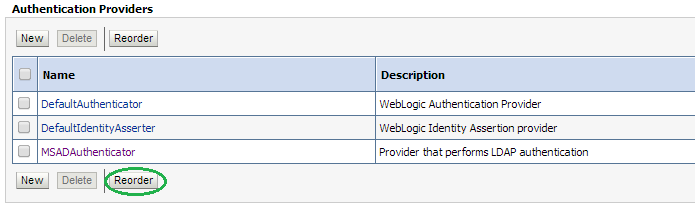
Select the MSADAuthenticator and use the arrows on the right to move it into the first position. Click OK.
To verify the AD configuration, take the following steps:
Restart the WebLogic Server for your changes to take effect.
Using the WebLogic Administration Console, select Security Realms > myrealm > Users and Groups tab. The Users sub-tab should be selected by default. The circled users are created in AD and can verify the Provider – MSADAuthenticator provider.
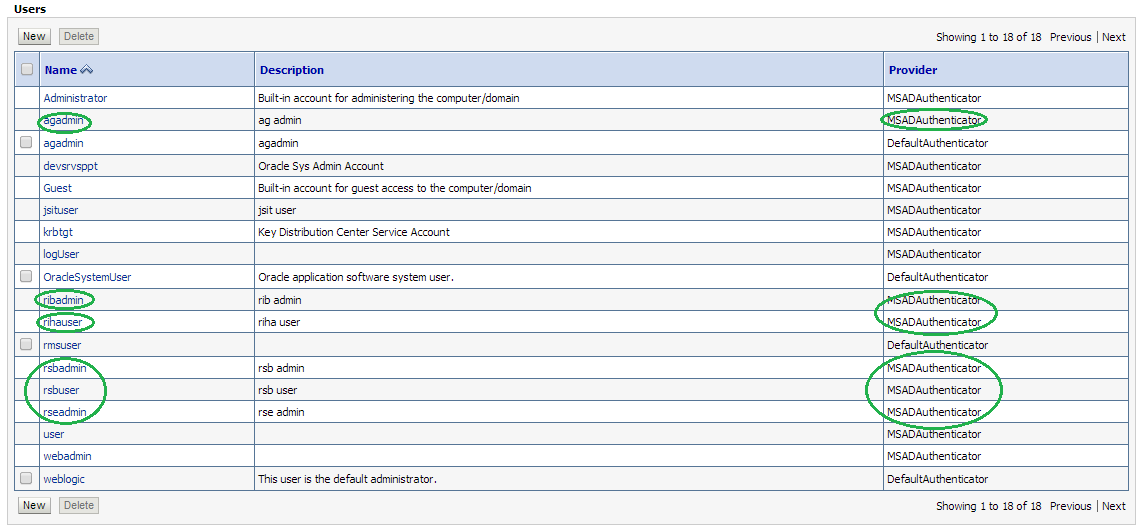
Click the Groups tab to see the list of groups the server can see. The highlighted groups are created in AD and can verify the Provider – MSADAuthenticator provider.