4 Extending the Functionality of the Connector
The following section describes procedures that you can perform to extend the functionality of the connector for addressing your specific business requirements:
-
Section 4.1, "Guidelines on Extending the Functionality of the Connector"
-
Section 4.2, "Adding or Removing Attributes for Reconciliation"
-
Section 4.3, "Adding or Removing Attribute Mappings for Provisioning"
-
Section 4.5, "Configuring the Connector for Multiple Installations of the Target System"
-
Section 4.6, "Configuring the Connector for Multiple Trusted Source Reconciliation"
-
Section 4.8, "Configuring Validation of Data During Reconciliation and Provisioning"
-
Section 4.9, "Configuring Transformation of Data During Reconciliation"
-
Section 4.10, "Configuring the Connector for Reconciling and Provisioning Object-Level Privileges"
4.1 Guidelines on Extending the Functionality of the Connector
Note:
In Oracle Identity Manager release 11.1.1, a scheduled job is an instance of a scheduled task. In this guide, the term scheduled task used in the context of Oracle Identity Manager release 9.1.0.x is the same as the term scheduled job in the context of Oracle Identity Manager release 11.1.1.
See Oracle Fusion Middleware System Administrator's Guide for Oracle Identity Manager for more information about scheduled tasks and scheduled jobs.
As mentioned earlier in this guide, predefined queries are provided to reconcile target system user records and synchronize lookup field values with Oracle Identity Manager. These predefined queries are in the DBUMReconQuery.properties and DBUMLookUpQuery.properties files, respectively.
You can modify the predefined queries. In addition, you can add your own queries in the same file or in a different properties file. The query whose name you specify in the scheduled task (for reconciliation) is applied during reconciliation. Similarly, the lookup definition name that you specify in the scheduled task (for lookup field synchronization) is synchronized during lookup field synchronization.
The following sections discuss guidelines that you must apply while modifying the predefined queries or creating new queries:
-
Section 4.1.1, "Guidelines for Configuring Queries Used in Lookup Field Synchronization"
-
Section 4.1.2, "Guidelines for Configuring Queries Used in Reconciliation"
-
Section 4.1.3, "Guidelines Common to Configuring Both Types of Queries"
The following section discusses guidelines that you must apply while modifying the predefined attribute mappings for provisioning:
4.1.1 Guidelines for Configuring Queries Used in Lookup Field Synchronization
The following are guidelines that you must apply while modifying or creating queries for lookup field synchronization:
-
You must not change the SELECT clause of the predefined query. In other words, the set of target system attributes from which values are fetched for synchronization cannot be modified.
-
If you create a query, then you must mention the name of the query, which is the lookup definition name, as the value of the Lookup Definition Name attribute in the scheduled task.
-
If you want to use a new properties file instead of the predefined DBUMLookUpQuery.properties file, then specify the full path and name of that file as the value of the Query Properties File Path attribute in the reconciliation scheduled task. See Section 3.3, "Scheduled Task for Lookup Field Synchronization" for information about this scheduled task.
4.1.2 Guidelines for Configuring Queries Used in Reconciliation
The following are examples of scenarios in which you might want to modify a reconciliation query:
-
You want to add a column in the SELECT clause of the reconciliation query.
-
You want to remove a column from the SELECT clause of the reconciliation query. For example, if you are using Oracle Database as the target system, then you might want to remove the PROFILE column.
-
You want to add conditions to the WHERE clause of the reconciliation query so that only a specified subset of the target system records are considered for reconciliation.
The following are guidelines that you must apply while modifying or creating queries for reconciliation:
-
By adding or removing a column from the SELECT clause of a reconciliation query, you add or remove an attribute from the list of target system attributes for reconciliation. To enable the connector to process a change (addition or removal) in the list of reconciled attributes, you must make corresponding changes in the provisioning part of the connector. The procedures are described later in this guide.
-
In the query properties file, you must not change the names of the following predefined queries because these names have been included in the connector code:
SYBASE_DATABASE
SYBASE_LOGIN_DETAILS
SYBASE_USER_DETAILS
SQL_SERVER_DATABASE
SQL_SERVER_LOGIN_DETAILS
SQL_SERVER_USER_DETAILS
SQL_SERVER_STATUS_AUTH_TYPE:
-
Some of the predefined queries use inner queries. If you add or remove a column from the outer query, you must make corresponding changes in the inner queries.
-
You cannot remove columns corresponding to the following resource object attributes that are marked as mandatory attributes:
-
For IBM DB2 UDB: User Name
-
For Microsoft SQL Server login entity: Login Name
-
For Microsoft SQL Server user entity: Login Name, User Name
-
For MySQL: User Name
-
For Oracle Database: User Name
-
For Sybase login entity: Login Name
-
For Sybase user entity: Login Name, User Name
-
-
If you are using Oracle Database as the target system, then you must ensure that the following condition included in the WHERE clause of the inner query is not removed:
WHERE ((CREATED - TO_DATE('01011970','ddmmyyyy')) *24*60*60*1000) > :lastExecutionTimeThis condition is used to determine if a target system record was added or updated after the time stamp stored in the Last Execution Time scheduled task attribute.
-
For Oracle Database, in the WHERE clause, you must ensure that formats for date literals are specified by the use of the TO_DATE function. For example, instead of specifying a date value as
'31-Dec-4712'useTO_DATE('31-Dec-4712','DD-Mon-YYYY'). -
When you add or remove columns from the SELECT clause of the child queries in the properties file, then you must update the attribute mapping lookup definition that holds mappings between child attributes and the target system column names. In addition, you must update other OIM objects. The procedure is described later in this guide.
-
Before you modify or add a query in the properties file, you must run the query by using any standard database client to ensure that the query produces the required results when it is run against the target system database.
-
If you want to use a new properties file instead of the predefined DBUMReconQuery.properties file, then specify the name of the file as the value of the Query Properties File attribute in the Configuration lookup definition for your target system database. See Appendix A, "Preconfigured Lookup Definitions" for information about Configuration lookup definition.
4.1.3 Guidelines Common to Configuring Both Types of Queries
The following are guidelines that you must apply while modifying or creating queries for either reconciliation or lookup field synchronization:
-
The name of the query must not be the same as the name of any other query in the properties file.
-
The name of the query must not contain spaces.
-
Before you modify or add a query in the properties file, you must run the query by using any standard database client to ensure that it produces the required results.
-
Use the number sign (#) to begin each comment line in the properties file.
Add comments to describe changes that you make in existing queries and also to describe new queries that you add in the file.
See existing comments in the properties file for an example.
-
If you want to introduce line breaks in the query (to improve readability), then add a backslash (\) at the end of each line.
-
You must not change existing conditions in the WHERE clause of the predefined query.
-
You can add conditions to the WHERE clause of the predefined query.
4.1.4 Guidelines on Modifying Predefined Attribute Mappings for Provisioning
You must not remove attributes that are marked as mandatory in Section 1.7.2, "Attributes for Provisioning."
4.2 Adding or Removing Attributes for Reconciliation
This section is divided into the following topics:
-
Section 4.2.1, "Adding New Standard and Custom Attributes for Reconciliation"
-
Section 4.2.3, "Removing Attributes Used for Reconciliation"
4.2.1 Adding New Standard and Custom Attributes for Reconciliation
Note:
The procedure described in this section applies to both standard target system attributes and custom attributes that you create on the target system.
If you want to add a multivalued field for reconciliation, then see Section 4.2.2, "Adding New Standard and Custom Multivalued Attributes for Target Resource Reconciliation."
By default, the attributes listed in Section 1.6.2, "Target System Columns Used in Reconciliation" are mapped for reconciliation between Oracle Identity Manager and the target system. If required, you can add new attributes for target resource reconciliation or trusted source reconciliation.
To add a new standard or custom attribute for reconciliation:
See Also:
Oracle Identity Manager Design Console Guide for detailed information about these steps
-
Open the reconciliation properties file in a text editor. In the section corresponding to the target system database that you are using, add to the query, the target system column name that you want to include for reconciliation.
-
Save the changes to the file.
-
Log in to the Design Console.
-
In the resource object definition, add the reconciliation field corresponding to the attribute as follows:
-
Expand the Resource Management folder, and then double-click Resource Objects.
-
If you have configured the target system as a trusted source, then search for and open the DBUM Trusted Source resource object.
-
If you have configured the target system as a target resource, then search for and open one of the following resource objects:
-
For IBM DB2 UDB: DB2 DB User
-
For Microsoft SQL Server login entity: MSSQL User Login
-
For Microsoft SQL Server user entity: MSSQL User
-
For MySQL: MySQL DB User
-
For Oracle Database: Oracle DB User
-
For Sybase login entity: Sybase DB User Login
-
For Sybase user entity: Sybase DB User
-
-
On the Object Reconciliation tab, click Add Field to open the Add Reconciliation Field dialog box.
-
Specify a value for the field name.
-
From the Field Type list, select a data type for the field. In addition, if you want to designate the attribute as a mandatory attribute, then select the check box.
-
Click the Save icon, and then close the dialog box.
-
If you are using Oracle Identity Manager release 11.1.1, then click Create Reconciliation Profile. This copies changes made to the resource object into the MDS.
-
Click the Save icon.
-
-
Add an entry for the attribute in the lookup definition for reconciliation attribute mapping as follows:
-
Expand the Administration folder, and then double-click Lookup Definition.
-
If you have configured the target system as a trusted source, then search for and open one of the following lookup definitions:
-
For IBM DB2 UDB: Lookup.DBUM.DB2.TrustedRecon.Mapping
-
For Microsoft SQL Server: Lookup.DBUM.MSSQL.TrustedRecon.Mapping
-
For MySQL: Lookup.DBUM.MySQL.TrustedRecon.Mapping
-
For Oracle Database: Lookup.DBUM.Oracle.TrustedRecon.Mapping
-
For Sybase: Lookup.DBUM.Sybase.TrustedRecon.Mapping
-
-
If you have configured the target system as a target source, then search for and open one of the following lookup definitions:
-
For IBM DB2 UDB: Lookup.DBUM.DB2.TargetRecon.Mapping
-
For Microsoft SQL Server login entity: Lookup.DBUM. MSSQL.TargetRecon.Login.Mapping
-
For Microsoft SQL Server user entity: Lookup.DBUM. MSSQL.TargetRecon.User.Mapping
-
For MySQL Database: Lookup.DBUM.MySQL.TargetRecon.Mapping
-
For Oracle Database: Lookup.DBUM.Oracle.TargetRecon.Mapping
-
For Sybase login entity: Lookup.DBUM.Sybase.TargetRecon.Login.Mapping
-
For Sybase user entity: Lookup.DBUM.Sybase.TargetRecon.User.Mapping
-
-
To add a row, click Add.
-
In the Code Key column, enter the name that you have set for the attribute in the resource object.
-
In the Decode column, enter one of the following values:
-
If your target system contains a column corresponding to the resource object attribute that you added, then enter the target system column name in the reconciliation query of the properties file as the Decode value. If you have set an alias for the column in the query, then enter the alias in the Decode column.
-
If you want to set a constant value, then enter the value in the
CONSTANT~CONSTANT_VALUEformat.In this format,
CONSTANTspecifies that the data in this column is a constant or literal. CONSTANT_VALUE is value to be displayed in the corresponding field of the OIM User form. -
If you want to specify values fetched from the target system in a format that is accepted by Oracle Identity Manager, then enter the value in the COLUMN_NAME~LOOKUP_NAME format.
In this format, COLUMN_NAME is the target system column name from which the value is fetched. LOOKUP_NAME is the name of the lookup definition that maps values fetched from the target system with values that must be displayed in the OIM User form field.
-
If the process form field corresponding to the Code Key value is a lookup type field, then enter the value in the
LOOKUP~COL_NAMEformat.In this format, LOOKUP specifies that the data retrieved from the target system is lookup data. COL_NAME is the corresponding column name or column name alias used in the reconciliation query
-
-
Click the Save icon.
-
-
Add the attribute as a field on the process form as follows:
-
Expand the Development Tools folder, and then double-click Form Designer.
-
Search for and open the process form for the connector that you are using:
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process forms for each connector.
-
Click Create New Version to create a version of the process form. Then, enter a version name and click the Save icon.
-
Click Add.
-
Specify the properties of the attribute according to your requirement.
-
Click the Save icon.
-
Click Make Version Active to activate the new version of the process form.
-
-
Create a reconciliation field mapping in the process definition as follows:
-
Expand the Process Management folder, and then double-click Process Definition.
-
If you have configured the target system as a trusted source, then search for and open the DBUM Trusted User process definition.
-
If you have configured the target system as a target resource, then search for and open one of the following process definitions:
-
For IBM DB2 UDB: DB2 DB User
-
For Microsoft SQL Server login entity: MSSQL DB User Login
-
For Microsoft SQL Server user entity: MSSQL DB User
-
For MySQL Database: MySQL DB User
-
For Oracle Database: Oracle DB User
-
For Sybase login entity: Sybase DB User Login
-
For Sybase user entity: Sybase DB User
-
-
On the Reconciliation Field Mapping tab, click Add Field Map.
-
From the Field name list in the Add Reconciliation Field Mapping dialog box, select the name that you have assigned to the attribute created in the resource object.
-
Double-click the Process Data Field. The entries in the dialog box that is displayed correspond to the process form fields.
-
Select the corresponding newly added field from the dialog box.
-
If the field mapping is a key field for matching the process data, check the key Field for Reconciliation matching check box.
-
Click the Save icon.
-
-
Add the attribute for provisioning. Section 4.3.1, "Adding New Standard and Custom Attributes for Provisioning" for detailed information about the procedure.
4.2.2 Adding New Standard and Custom Multivalued Attributes for Target Resource Reconciliation
By default, the attributes listed in Section 1.6.2, "Target System Columns Used in Reconciliation" are mapped for reconciliation between Oracle Identity Manager and the target system. If required, you can add new multivalued attributes for target resource reconciliation.
To add a new standard or custom multivalued attribute for reconciliation:
See Also:
Oracle Identity Manager Design Console Guide for detailed information about these steps
-
Open the reconciliation properties file in a text editor. In the section corresponding to the target system database that you are using, add to the query, the target system column name that you want to include for reconciliation.
-
Save the changes to the file.
-
Log in to the Design Console.
-
In the resource object definition, add the reconciliation field corresponding to the attribute as follows:
-
Expand the Resource Management folder, and then double-click Resource Objects.
-
Search for and open one of the following resource objects:
-
For IBM DB2 UDB: DB2 DB User
-
For Microsoft SQL Server login entity: MSSQL User Login
-
For Microsoft SQL Server user entity: MSSQL User
-
For MySQL: MySQL DB User
-
For Oracle Database: Oracle DB User
-
For Sybase login entity: Sybase DB User Login
-
For Sybase user entity: Sybase DB User
-
-
On the Object Reconciliation tab, click Add Field to open the Add Reconciliation Field dialog box. The following screenshot shows this page:
-
Specify a value for the field name.
-
From the Field Type list, select Multi-Valued. In addition, if you want to designate the attribute as a mandatory attribute, then select the check box.
-
Click the Save icon, and then close the dialog box.
-
Right-click the field that you added as a multivalued attribute in Step 4.c, and then select Define Property Fields to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter the name of the field that you want to add to the multivalued attribute.
-
From the Field Type list, select String.
-
Repeat Steps 4.g through 4.j for every field that you want to add to the multivalued attribute.
-
If you are using Oracle Identity Manager release 11.1.1, then click Create Reconciliation Profile. This copies changes made to the resource object into the MDS.
-
Click the Save icon.
-
-
Create a lookup definition with the entries listed in Table 4-1. This lookup definition contains configurable entries for a multivalued attribute.
Table 4-1 Entries in the Configuration Lookup Definition for a Multivalued Attribute
Code Key Decode Child Attribute Mapping Lookup
Enter the name of the lookup definition that maps the fields of the multivalued attribute with the column name used in the reconciliation query.
Sample value:
Lookup.DBUM.DB2.TargetRecon.Schema.ConfigurationSee Appendix A, "Preconfigured Lookup Definitions" for more information about this lookup definition.
Child Query Name
Enter the name of the query in the reconciliation query file that you want to run for reconciling data about the child attribute.
Sample value:
DB2_TARGET_USER_SCHEMAChild Reconciliation Query Filter Lookup
Enter the name of the lookup definition that contains information about reconciliation filter parameters for the child attribute.
Sample value:
Lookup.DBUM.DB2.TargetRecon.Schema.QueryFilterSee Appendix A, "Preconfigured Lookup Definitions" for more information about this lookup definition.
Parent Attribute
This entry holds the primary key column of the query used for running target resource user reconciliation.
-
Add an entry for the attribute in the lookup definition for reconciliation attribute mapping as follows:
-
Expand the Administration folder, and then double-click Lookup Definition.
-
Search for and open one of the following lookup definitions:
-
For IBM DB2 UDB: Lookup.DBUM.DB2.TargetRecon.Mapping
-
For Microsoft SQL Server login entity: Lookup.DBUM. MSSQL.TargetRecon.Login.Mapping
-
For Microsoft SQL Server user entity: Lookup.DBUM. MSSQL.TargetRecon.User.Mapping
-
For MySQL: Lookup.DBUM.MySQL.TargetRecon.Mapping
-
For Oracle Database: Lookup.DBUM.Oracle.TargetRecon.Mapping
-
For Sybase login entity: Lookup.DBUM.Sybase.TargetRecon.Login.Mapping
-
For Sybase user entity: Lookup.DBUM.Sybase.TargetRecon.User.Mapping
-
-
To add a row, click Add.
-
In the Code Key column, enter the name that you have set for the attribute in the resource object.
-
In the Decode column, enter a value in the following format:
CHILD~CONFIG_LOOKUP_NAMEIn this format:
-
Child specifies that the data in this column is the child attribute data
-
CONFIG_LOOKUP_NAME is name of the lookup definition that holds configurable entries for the multivalued attribute. This is the lookup definition that you created in Step 5.
-
-
Click the Save icon.
-
-
Create a child form. See Section 5.4, "Creating a Process Form" for information about creating a child form.
-
Add the child attribute as a field on the child form.
See Section 4.3, "Adding or Removing Attribute Mappings for Provisioning" for information about adding child attributes to the child form.
-
Assign to the parent form the child table, which is represented by the child form as follows:
-
Expand Development Tools, and then double-click Form Designer.
-
Search for and open the parent process form for the target system that you are using:
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process definitions for each connector.
-
Click Create New Version to create a version of the form. Then, enter a version name and click the Save icon.
-
On the Child Tables tab, click Assign.
The Assignment window is displayed.
-
From this window, select the child table, and assign it to the form.
-
Click OK.
The selected child table is assigned to the form.
-
-
Create a reconciliation field mapping in the process definition as follows:
-
Expand the Process Management folder, and then double-click Process Definition.
-
Search for and open one of the following process definitions:
-
For IBM DB2 UDB: DB2 DB User
-
For Microsoft SQL Server login entity: MSSQL DB User Login
-
For Microsoft SQL Server user entity: MSSQL DB User
-
For MySQL: MySQL DB User
-
For Oracle Database: Oracle DB User
-
For Sybase login entity: Sybase DB User Login
-
For Sybase user entity: Sybase DB User
-
-
On the Reconciliation Field Mapping tab, click Add Field Map.
-
From the Field Name list in the Add Reconciliation Field Mapping dialog box, select the name that you have assigned to the multivalued attribute created in the resource object.
-
Double-click the Process Data Field, a new pop-up will appear. The entries in the pop-up correspond to the process form fields.
-
Select the corresponding newly added field from the pop-up.
-
If the field mapping is a key field for matching the process data, check the Key Field for Reconciliation matching check box.
-
Click the Save icon.
-
-
Add the attribute for provisioning. Section 4.3.2, "Adding New Standard and Custom Multivalued Attributes for Provisioning" for detailed information about the procedure.
4.2.3 Removing Attributes Used for Reconciliation
By default, the attributes listed in Section 1.6.2, "Target System Columns Used in Reconciliation" are mapped for reconciliation between Oracle Identity Manager and the target system. From that list of attributes, you must ensure that mappings for the following attributes and the corresponding columns in the SQL query are not modified or removed:
-
For IBM DB2 UDB: User Name
-
For Microsoft SQL Server login entity: Login Name
-
For Microsoft SQL Server user entity: Login Name, User Name
-
For MySQL: User Name
-
For Oracle Database: User Name
-
For Sybase login entity: Login Name
-
For Sybase user entity: Login Name, User Name
To remove an attribute from the list of attributes for reconciliation:
See Also:
Oracle Identity Manager Design Console Guide for detailed information about these steps
-
Open the properties file in a text editor, and remove the column from the query corresponding to the target system that you are using. Then, save and close the file.
-
Log in to the Design Console.
-
Remove the reconciliation field mapping in the process definition as follows:
-
Expand the Process Management folder, and then double-click Process Definition.
-
Search for and open the process definition for the connector that you are using:
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process definitions for each connector.
-
On the Reconciliation Field Mapping tab, select the mapping that you want to remove and then click Delete Map. The following screenshot shows this page:
-
Click the Save icon.
-
-
In the resource object definition, remove the reconciliation field corresponding to the attribute as follows:
-
Expand the Resource Management folder, and then double-click Resource Objects.
-
If you have configured the target system as a trusted source, then search for and open the DBUM Trusted Source resource object.
-
If you have configured the target system as a target resource, then search for and open one of the following resource objects:
-
For IBM DB2 UDB: DB2 DB User
-
For Microsoft SQL Server login entity: MSSQL User Login
-
For Microsoft SQL Server user entity: MSSQL User
-
For MySQL: MySQL DB User
-
For Oracle Database: Oracle DB User
-
For Sybase login entity: Sybase DB User Login
-
For Sybase user entity: Sybase DB User
-
-
On the Object Reconciliation tab, select the attribute that you want to remove and then click Delete Field. The following screenshot shows this page:
-
Click the Save icon, and then close the dialog box.
-
If you are using Oracle Identity Manager release 11.1.1, then click Create Reconciliation Profile. This copies changes made to the resource object into the MDS.
-
Click the Save icon.
-
-
Remove the entry for the attribute in the lookup definition for reconciliation attribute mapping as follows:
-
Expand the Administration folder, and then double-click Lookup Definition.
-
If you have configured the target system as a trusted source, then search for and open one of the following lookup definitions:
-
For IBM DB2 UDB: Lookup.DBUM.DB2.TrustedRecon.Mapping
-
For Microsoft SQL Server: Lookup.DBUM.DB2.TrustedRecon.Mapping
-
For MySQL: Lookup.DBUM.MySQL.TrustedRecon.Mapping
-
For Oracle Database: Lookup.DBUM.Oracle.TrustedRecon.Mapping
-
For Sybase: Lookup.DBUM.Sybase.TrustedRecon.Mapping
-
-
If you have configured the target system as a target resource, then search for and open one of the following lookup definitions:
-
For IBM DB2 UDB: Lookup.DBUM.DB2.TargetRecon.Mapping
-
For Microsoft SQL Server login entity: Lookup.DBUM. MSSQL.TargetRecon.Login.Mapping
-
For Microsoft SQL Server user entity: Lookup.DBUM. MSSQL.TargetRecon.User.Mapping
-
For MySQL: Lookup.DBUM.MySQL.TargetRecon.Mapping
-
For Oracle Database: Lookup.DBUM.Oracle.TargetRecon.Mapping
-
For Sybase login entity: Lookup.DBUM.Sybase.TargetRecon.Login.Mapping
-
For Sybase user entity: Lookup.DBUM.Sybase.TargetRecon.User.Mapping
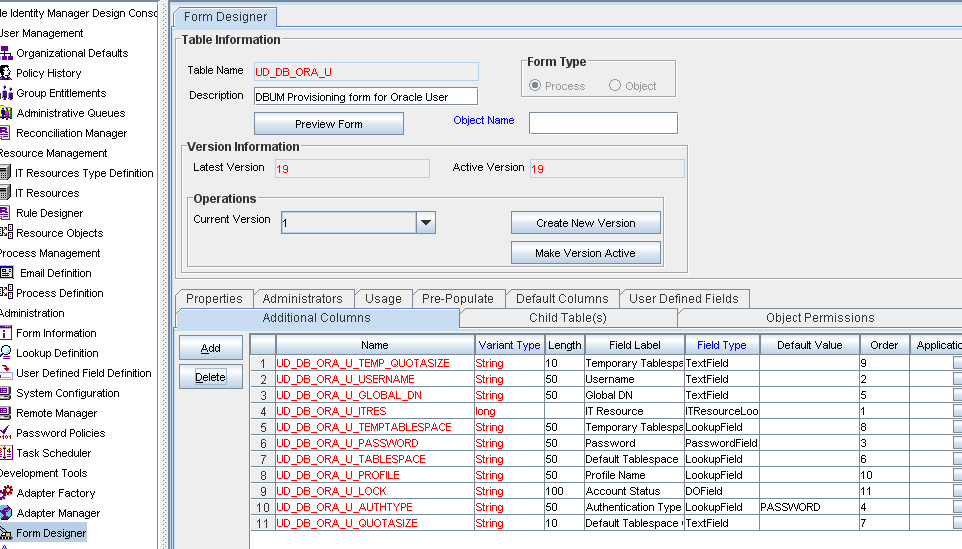
The following screenshot shows this page for Oracle Database:
-
-
Select the row for the attribute that you want to remove, and then click Delete.
-
Click the Save icon.
-
-
Remove the attribute from the process form as follows:
-
Expand the Development Tools folder, and then double-click Form Designer.
-
Search for and open the process form for the connector that you are using:
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process definitions for each connector.
-
Click Create New Version to create a version of the process form. Then, enter a version name and click the Save icon.
-
Select the field that you want to remove, and then click Delete.
-
Click the Save icon.
-
Click Make Version Active to activate the new version of the process form.
-
-
Remove the attribute from the list used for provisioning. Section 4.3.3, "Removing Attributes for Provisioning" for detailed information about the procedure.
4.3 Adding or Removing Attribute Mappings for Provisioning
By default, the attributes listed in Section 1.7.2, "Attributes for Provisioning" are mapped for provisioning between Oracle Identity Manager and the target system. If required, you can add new attributes for provisioning.
Note:
Attributes marked as mandatory in Section 1.7.2, "Attributes for Provisioning" cannot be modified or removed.
As mentioned earlier in this guide, SQL statements are used for performing provisioning operations. These SQL statements are stored in the Query Configuration lookup definition. The input parameters required to run the SQL statements are retrieved from the Parameter Configuration lookup definition. The Parameter Configuration lookup definition maps identifiers used in the SQL statements and the attributes for provisioning, defined on the process form. Therefore, if you add an add an attribute for provisioning, then this attribute must be mapped to an identifier, which becomes the actual input parameter required to run the SQL statements. This guideline forms the basis of two of the steps that you perform while adding or removing attributes for provisioning.
The section describes the following procedures:
-
Section 4.3.1, "Adding New Standard and Custom Attributes for Provisioning"
-
Section 4.3.2, "Adding New Standard and Custom Multivalued Attributes for Provisioning"
4.3.1 Adding New Standard and Custom Attributes for Provisioning
Note:
Perform the procedure described in this section only if you want to map standard or custom target system attributes for provisioning. If you want to add a standard or custom multivalued attribute for provisioning, then see Section 4.3.2, "Adding New Standard and Custom Multivalued Attributes for Provisioning."
To add a new standard or custom attribute for provisioning:
-
Add the attribute as a field on the process form as follows:
Note:
Directly proceed to the next step if you have already added the field to the process form while performing the procedure described in Section 4.2.1, "Adding New Standard and Custom Attributes for Reconciliation."
-
Expand Development Tools, and then double-click Form Designer.
-
Search for and open the process form for the target system that you are using:
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process form for each target system.
-
Click Create New Version to create a version of the form. Then, enter a version name and click the Save icon.
-
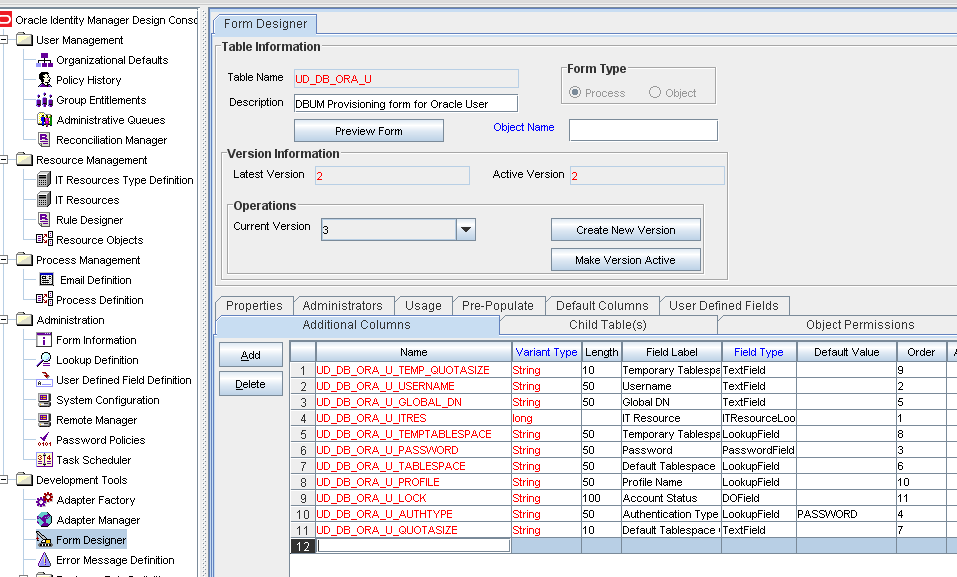
Click Add. The following screenshot shows this page:
-
Specify the properties of the attribute according to your requirement.
-
Click the Save icon.
-
Click Make Version Active to activate the new version of the process form.
-
-
Modify the Query Configuration lookup definition a follows:
-
On the Design Console, expand Administration and then double-click Lookup Definition.
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Query.Configuration
-
Lookup.DBUM.MSSQL.Query.Configuration
-
Lookup.DBUM.MySQL.Query.Configuration
-
Lookup.DBUM.Oracle.Query.Configuration
-
Lookup.DBUM.Sybase.Query.Configuration
-
-
If you want to modify a SQL statement or stored procedure, then:
i. Search for the entry containing the SQL statement or stored procedure that you want to modify.
ii. In the Decode column, enter the SQL statement or stored procedure.
Note:
Each identifier in the SQL statement of the Decode column must be prefixed with a colon (:). For example, REVOKE :role_name FROM :user_id.
iii. Click the Save icon.
-
If you want to add a SQL statement, then:
i. Click Add, to add a new row. The following screenshot shows this page:
ii. In the Code Key column, enter the name of the SQL statement that you want to add.
iii. In the Decode column, enter the SQL statement.
Note:
Each identifier in the SQL statement of the Decode column must be prefixed with a colon (:). For example, REVOKE :role_name FROM :user_id.
iv. Click the Save icon.
-
-
In the Parameter Configuration lookup definition, add an entry for the attribute that you added on the process form in Step 1 as follows:
-
On the Design Console, expand Administration and then double-click Lookup Definition.
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Parameter.Configuration
-
Lookup.DBUM.MSSQL.Parameter.Configuration
-
Lookup.DBUM.MySQL.Parameter.Configuration
-
Lookup.DBUM.Oracle.Parameter.Configuration
-
Lookup.DBUM.Sybase.Parameter.Configuration
-
-
Click Add, to add a new row.
-
In the Code Key column, enter the identifier (prefixed with a colon (:)) of the SQL statement that was entered in the Decode column of the Query Configuration lookup definition in Step 2.
-
In the Decode column, enter the decode value. See Appendix A, "Preconfigured Lookup Definitions" for information about the Parameter Configuration lookup definition and the format of values to be entered in the Decode column.
-
Click the Save icon.
-
-
Add the attribute for reconciliation.
When you add an attribute on the process form, you must also enable reconciliation of values for that attribute from the target system. See Section 4.2.1, "Adding New Standard and Custom Attributes for Reconciliation" for more information.
Note:
Perform steps 5 through 7 only if you want to perform request-based provisioning.
-
Update the request dataset.
When you add an attribute on the process form, you also update the XML file containing the request dataset definitions. To update a request dataset:
-
In a text editor, open the XML file located in the OIM_HOME/DataSet/file directory for editing.
-
Add the AttributeReference element and specify values for the mandatory attributes of this element.
See Also:
The "Configuring Requests" chapter of the Oracle Fusion Middleware Developer's Guide for Oracle Identity Manager guide for more information about creating and updating request datasets
For example, while performing Step 1 of this procedure, if you added City as an attribute on the process form, then enter the following line:
<AttributeReference name = "City" attr-ref = "City" type = "String" widget = "text" length = "50" available-in-bulk = "false"/>
In this AttributeReference element:
-
For the name attribute, enter the value in the Name column of the process form without the tablename prefix.
For example, if UD_DB_ORA_U_CITY is the value in the Name column of the process form, then you must specify
Cityas the value of the name attribute in the AttributeReference element. -
For the attr-ref attribute, enter the value that you entered in the Field Label column of the process form while performing Step 1.
-
For the type attribute, enter the value that you entered in the Variant Type column of the process form while performing Step 1.
-
For the widget attribute, enter the value that you entered in the Field Type column of the process form, while performing Step 1.
-
For the length attribute, enter the value that you entered in the Length column of the process form while performing Step 1.
-
For the available-in-bulk attribute, specify
trueif the attribute must be available during bulk request creation or modification. Otherwise, specifyfalse.
While performing Step 1, if you added more than one attribute on the process form, then repeat this step for each attribute added.
-
-
Save and close the XML file.
-
-
Run the PurgeCache utility to clear content related to request datasets from the server cache.
See Oracle Fusion Middleware System Administrator's Guide for Oracle Identity Manager for more information about the PurgeCache utility.
-
Import into MDS, the request dataset definitions in XML format.
See Section 2.3.1.8.2, "Importing Request Datasets into MDS" for detailed information about the procedure.
4.3.2 Adding New Standard and Custom Multivalued Attributes for Provisioning
Note:
This section describes the procedure to add standard or custom multivalued attributes of the target system for provisioning.
By default, the multivalued attributes listed in Section 1.7.2, "Attributes for Provisioning" are mapped for provisioning between Oracle Identity Manager and the target system. If required, you can add new multivalued fields for provisioning.
To add a new standard or custom multivalued attribute for provisioning:
Note:
See Oracle Identity Manager Design Console Guide for detailed information about the steps of this procedure.
If you have already added a multivalued attribute for reconciliation, then you need not repeat steps performed as part of that procedure.
See Also:
Section 4.10, "Configuring the Connector for Reconciling and Provisioning Object-Level Privileges"
-
Log in to the Oracle Identity Manager Design Console.
-
Create a child form for the new multivalued attribute as follows:
-
Expand Development Tools, and then double-click Form Designer.
-
In the Table Name field, enter a name for the child table.
-
In the Description field, enter a description for the child form.
-
In the Form Type region, select Process.
-
Click the Save icon.
-
On the Additional Columns tab, click Add.
-
In the Name column, enter a name for the attribute.
-
Enter values in the remaining columns, and then click the Save icon.
-
If you want to add more fields, then click Add and enter values for each field.
-
-
Associate the child form with the process form as follows:
Note:
Only the most basic instructions to create a child form are given in this section. See Oracle Identity Manager Design Console Guide for detailed instructions.
-
Search for and open the parent process form for the target system that you are using. See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process forms for each target system.
-
Click Create New Version.
-
Enter a version name, and then click the Save icon.
-
From the Current Version list, select the version that you created.
-
On the Child Tables tab, click Assign.
-
From the list on the left, select the child table and then move it to the list on the right. Then, click OK.
-
Click Make Version Active.
-
-
Create an entry for the attribute in the Query Configuration lookup definition for multivalued attribute provisioning as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Query.Configuration
-
Lookup.DBUM.MSSQL.Query.Configuration
-
Lookup.DBUM.MySQL.Query.Configuration
-
Lookup.DBUM.Oracle.Query.Configuration
-
Lookup.DBUM.Sybase.Query.Configuration
-
-
If you want to modify a SQL statement or a stored procedure, then:
i. Search for the entry containing the SQL statement or stored procedure that you want to modify.
ii. In the Decode column, enter the SQL statement. or stored procedure
Note:
Each identifier in the SQL statement of the Decode column must be prefixed with a colon (:). For example, REVOKE :role_name FROM :user_id.
iii. Click the Save icon.
-
If you want to add a SQL statement, then:
i. Click Add, to add a new row.
ii. In the Code Key column, enter the name of the SQL statement that you want to add.
iii. In the Decode column, enter the SQL statement.
Note:
Each identifier in the SQL statement of the Decode column must be prefixed with a colon (:). For example, REVOKE :role_name FROM :user_id.
iv. Click the Save icon.
-
-
Create an entry for the attribute in the Parameter Configuration lookup definition for multivalued attribute provisioning as follows:
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Parameter.Configuration
-
Lookup.DBUM.MSSQL.Parameter.Configuration
-
Lookup.DBUM.MySQL.Parameter.Configuration
-
Lookup.DBUM.Oracle.Parameter.Configuration
-
Lookup.DBUM.Sybase.Parameter.Configuration
-
-
Click Add, to add a new row.
-
In the Code Key column, enter the identifier (prefixed with a colon (:)) of the SQL statement that was entered in the Decode column of the Query Configuration lookup definition in Step 2.
-
In the Decode column, enter the decode value. See Appendix A, "Preconfigured Lookup Definitions" for information about the Parameter Configuration lookup definition and the format of values to be entered in the Decode column.
-
Click the Save icon.
-
-
Expand Process Management, and double-click Process Definition.
-
Search for and open the process definition. See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process definitions for each target system.
-
In the process definition, create a process task for adding values in the attribute:
-
Click Add.
-
On the General tab of the Creating New Task dialog box, enter a name and description for the task and then select the following:
Conditional
Required for Completion
Allow Cancellation while Pending
Allow Multiple Instances
-
From the Child Table list, select the child table name.
-
From the Trigger Type list, select Insert.
-
Click the Save icon.
-
On the Integration tab of the Creating New Task dialog box, click Add.
-
In the Handler Selection dialog box, select Adapter, click the adapter, and then click the Save icon. See Table 5-1 for information about adapters that you can use.
The list of adapter variables is displayed on the Integration tab.
-
To create the mapping for the adapter variables:
Double-click the number of the first row.
In the Edit Data Mapping for Variable dialog box, enter values for the Variable Name, Data Type, and Map To fields, and then click the Save icon.
Repeat this step for each adapter variable that you must map. See Table 5-2 for information about the adapter variables that you can map.
-
Click the Save icon in the Editing Task dialog box, and then close the dialog box.
-
Click the Save icon to save changes to the process definition.
-
-
To enable updates of the multivalued attribute during provisioning operations, create a process task in the process definition as follows:
-
On the General tab of the Creating New Task dialog box, enter a name and description for the task and then select the following:
Conditional
Required for Completion
Allow Cancellation while Pending
Allow Multiple Instances
-
From the Child Table list, select the child table name.
-
From the Trigger Type list, select Update.
-
On the Integration tab of the Creating New Task dialog box, click Add.
-
In the Handler Selection dialog box, select Adapter, click the adapter that is used to delete the child data, and then click the Save icon. See Table 5-1 for information about adapters that you can use.
The list of adapter variables is displayed on the Integration tab.
-
To create the mapping for the first adapter variable:
Double-click the number of the first row.
In the Edit Data Mapping for Variable dialog box, enter values for the Variable Name, Data Type, and Map To fields, and then click the Save icon.
Repeat this step for each adapter variable that you must map. See Table 5-2 for information about the adapter variables that you can map.
-
Click the Save icon in the Editing Task dialog box, and then close the dialog box.
-
Click the Save icon to save changes to the process definition.
-
To add the tasks to be generated when the SUCCESS response is received:
-
In the Responses region, select the row with the SUCCESS response.
-
In the Tasks To Generate region, click Assign.
-
In the dialog box that appears, from the left pane, select the task name created in Step 8.
-
-
In the process definition, create a process task to delete values in the attribute:
-
Click Add.
-
On the General tab of the Creating New Task dialog box, enter a name and description for the task and then select the following:
Conditional
Required for Completion
Allow Cancellation while Pending
Allow Multiple Instances
-
From the Child Table list, select the child table name.
-
From the Trigger Type list, select Delete.
-
Click the Save icon.
-
On the Integration tab of the Creating New Task dialog box, click Add.
-
In the Handler Selection dialog box, select Adapter, click the adapter that is used to delete the child data, and then click the Save icon. See Table 5-1 for information about adapters that you can use.
The list of adapter variables is displayed on the Integration tab.
-
To create the mapping for the first adapter variable:
Double-click the number of the first row.
In the Edit Data Mapping for Variable dialog box, enter values for the Variable Name, Data Type, and Map To fields, and then click the Save icon.
Repeat this step for each adapter variable that you must map. See Table 5-2 for information about the adapter variables that you can map.
-
Click the Save icon in the Editing Task dialog box, and then close the dialog box.
-
Click the Save icon to save changes to the process definition.
-
-
Save the changes to the process definition.
-
Add the attribute for reconciliation.
When you add an attribute on the process form, you must also enable reconciliation of values for that attribute from the target system. See Section 4.2.2, "Adding New Standard and Custom Multivalued Attributes for Target Resource Reconciliation" for more information.
Note:
Perform steps 13 through 15 only if you want to perform request-based provisioning.
-
Update the request dataset.
When you add an attribute on the process form, you also update the XML file containing the request dataset definitions. To update a request dataset:
-
In a text editor, open the XML file located in the OIM_HOME/DataSet/file directory for editing.
-
Add the AttributeReference element and specify values for the mandatory attributes of this element.
See Also:
The "Configuring Requests" chapter of the Oracle Fusion Middleware Developer's Guide for Oracle Identity Manager guide for more information about creating and updating request datasets
For example, while performing Step 2 of this procedure, if you added City as an attribute on the process form, then enter the following line:
<AttributeReference name = "City" attr-ref = "City" type = "String" widget = "text" length = "50" available-in-bulk = "false"/>
In this AttributeReference element:
-
For the name attribute, enter the value in the Name column of the process form without the tablename prefix.
For example, if UD_DB_ORA_U_CITY is the value in the Name column of the process form, then you must specify
Cityas the value of the name attribute in the AttributeReference element. -
For the attr-ref attribute, enter the value that you entered in the Field Label column of the process form while performing Step 2.
-
For the type attribute, enter the value that you entered in the Variant Type column of the process form while performing Step 2.
-
For the widget attribute, enter the value that you entered in the Field Type column of the process form, while performing Step 2.
-
For the length attribute, enter the value that you entered in the Length column of the process form while performing Step 2.
-
For the available-in-bulk attribute, specify
trueif the attribute must be available during bulk request creation or modification. Otherwise, specifyfalse.
While performing Step 2, if you added more than one attribute on the process form, then repeat this step for each attribute added.
-
-
Save and close the XML file.
-
-
Run the PurgeCache utility to clear content related to request datasets from the server cache.
See Oracle Fusion Middleware System Administrator's Guide for Oracle Identity Manager for more information about the PurgeCache utility.
-
Import into MDS, the request dataset definitions in XML format.
See Section 2.3.1.8.2, "Importing Request Datasets into MDS" for detailed information about the procedure.
4.3.3 Removing Attributes for Provisioning
By default, the attributes listed in Section 1.7.2, "Attributes for Provisioning" are mapped for provisioning between Oracle Identity Manager and the target system. From that list of attributes, you must ensure that mappings for the following attributes are not modified or removed:
For IBM DB2 UDB
-
IT Resource
-
Username
-
User Type
For Microsoft SQL Server
Attributes of the login entity:
-
IT Resource
-
Login Name
-
Password (If creating a login based on SQL server authentication)
-
Authentication Type
-
Default Database (If creating a login based on Windows authentication)
-
Default Language (If creating a login based on Windows authentication)
Attributes of the user entity:
-
IT Resource
-
Login Name
-
Username
-
Authentication Type
-
Database Name
For MySQL Database
-
IT Resource
-
User Name
-
User Password
For Oracle Database
-
IT Resource
-
Username
-
Password (If creating a local user by using the
BYpasswordclause) -
Authentication Type
-
Global DN (If creating a global user by using the
GLOBALLYclause) -
Account Status (Read-only field)
For Sybase
Attributes of the login entity:
-
IT Resource
-
Login Name
-
Password
Attributes of the user entity:
-
IT Resource
-
Login Name
-
Username
-
Database Name (Read-only field)
To remove the attribute (field) from the process form:
Note:
When you remove an attribute from the process form, you must also remove any pre-populate adapter that is associated with the attribute.
To remove an attribute for provisioning:
-
Remove the attribute as a field on the process form as follows:
Note:
Directly proceed to the next step if you have already removed the field from the process form while performing the procedure described in Section 4.2.3, "Removing Attributes Used for Reconciliation."
-
Expand Development Tools, and then double-click Form Designer.
-
Search for and open the process form for the connector that you are using:
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process forms for each target system.
-
Click Create New Version to create a version of the form. Then, enter a version name and click the Save icon.
-
Select the attribute to be deleted, and then click Delete.
-
Click the Save icon.
-
Click Make Version Active to activate the new version of the process form.
-
-
In the Parameter Configuration lookup definition, remove the entry for the attribute that you removed from the process form in Step 1 as follows:
-
On the Design Console, expand Administration and then double-click Lookup Definition.
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Parameter.Configuration
-
Lookup.DBUM.MSSQL.Parameter.Configuration
-
Lookup.DBUM.MySQL.Parameter.Configuration
-
Lookup.DBUM.Oracle.Parameter.Configuration
-
Lookup.DBUM.Sybase.Parameter.Configuration
-
-
Select the row containing the process form field name that you removed (in Step 1), and then click Delete.
-
Click the Save icon.
-
-
To remove from the Query Configuration lookup definition, the SQL clauses that contain identifiers corresponding to the entry that you removed from the Parameter Configuration lookup definition (in Step 2):
Note:
After you modify the entries in the Query Configuration lookup definition, you must run the statement by using any standard database client to ensure that the statement produces the required results when it is run against the target system database.
-
On the Design Console, expand Administration and then double-click Lookup Definition.
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Query.Configuration
-
Lookup.DBUM.MSSQL.Query.Configuration
-
Lookup.DBUM.MySQL.Query.Configuration
-
Lookup.DBUM.Oracle.Query.Configuration
-
Lookup.DBUM.Sybase.Query.Configuration
-
-
Search for the entry that contains the SQL fragment that you want to remove.
-
In the Decode column, remove the SQL fragment and its corresponding identifier along with its colon (:) prefix.
-
Click the Save icon.
-
-
From the appropriate provisioning process definition, delete the process task corresponding to the attribute that you deleted (in Step 1) as follows:
-
On the Design Console, expand Process Management, and then double-click Process Definition.
-
Search for and open the process definition corresponding to the process form that you used in Step 1. See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process definitions for each target system.
-
On the Tasks tab, select the process task to be deleted and then click Delete.
-
Click the Save icon.
-
-
Remove the attribute for reconciliation. See Section 4.2.3, "Removing Attributes Used for Reconciliation" for more information.
Note:
Perform steps 6 through 8 only if you want to perform request-based provisioning.
-
Update the request dataset.
When you remove an attribute from the process form, you also update the XML file containing the request dataset definitions. To update a request dataset:
-
In a text editor, open the XML file located in the OIM_HOME/DataSet/file directory for editing.
-
Remove the AttributeReference element corresponding to the attribute removed from the process form while performing Step 1. If you remove more than one attribute from the process form, then repeat this step for each attribute that you remove.
For example, while performing Step 1 of this procedure, if you remove the City attribute from the process form, then remove the following line:
<AttributeReference name = "City" attr-ref = "City" type = "String" widget = "text" length = "50" available-in-bulk = "false"/>
See Also:
The "Configuring Requests" chapter of the Oracle Fusion Middleware Developer's Guide for Oracle Identity Manager guide for more information about creating and updating request datasets
-
Save and close the XML file.
-
-
Run the PurgeCache utility to clear content related to request datasets from the server cache.
See Oracle Fusion Middleware System Administrator's Guide for Oracle Identity Manager for more information about the PurgeCache utility.
-
Import into MDS, the request dataset definitions in XML format.
See Section 2.3.1.8.2, "Importing Request Datasets into MDS" for detailed information about the procedure.
4.4 Modifying Field Lengths on the Process Form
You might want to modify the lengths of fields (attributes) on the process form. For example, if you use the Japanese locale, then you might want to increase the lengths of process form fields to accommodate multibyte data from the target system.
If you want to modify the length of field on the process form, then:
-
Log in to the Design Console.
-
Expand Development Tools, and double-click Form Designer.
-
Search for and open the process form.
See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of process forms for each connector.
-
Click Create New Version.
-
Modify the length of the required field.
-
Save the form and make the version active
-
Click the Save icon.
4.5 Configuring the Connector for Multiple Installations of the Target System
You might want to configure the connector for multiple installations of the target system. The following example illustrates this requirement:
The London and New York offices of Example Multinational Inc. have their own installations of the target system. The company has recently installed Oracle Identity Manager, and they want to configure Oracle Identity Manager to link all the installations of the target system.
To meet the requirement posed by such a scenario, you can create copies of connector objects, such as the IT resource and resource object.
The decision to create a copy of a connector object might be based on a requirement. For example, an IT resource can hold connection information for one target system installation. Therefore, it is mandatory to create a copy of the IT resource for each target system installation.
With some other connector objects, you do not need to create copies at all. For example, a single attribute-mapping lookup definition can be used for all installations of the target system.
All connector objects are linked. For example, a scheduled task holds the name of the IT resource. Similarly, the IT resource for a target system such as Oracle Database holds the name of the configuration lookup definition, Lookup.DBUM.Oracle.Configuration. If you create a copy of an object, then you must specify the name of the copy in associated connector objects.
Table 4-2 lists associations between connector objects whose copies can be created and the other objects that reference these objects. When you create a copy of a connector object, use this information to change the associations of that object with other objects.
Note:
On a particular Oracle Identity Manager installation, if you create a copy of a connector object, then you must set a unique name for it.
Table 4-2 Connector Objects and Their Associations
When you configure reconciliation:
To reconcile data from a particular target system installation, specify the name of the IT resource for that target system installation as the value of the scheduled task attribute that holds the IT resource name. For example, if you are using Oracle Database as the target system, then you enter the name of the IT resource as the value of the IT resource attribute of the scheduled task that you run.
When you perform provisioning operations:
When you use the Administrative and User Console to perform provisioning, you can specify the IT resource corresponding to the target system installation to which you want to provision the user.
4.5.1 Enabling the Dependent Lookup Fields Feature
When you perform a provisioning operation, lookup fields on the Administrative and User Console allow you to select values from lists. Some of these lookup fields are populated with values copied from the target system.
For release 9.1.0 of the connector, the Dependent Lookup Fields feature is disabled by default. If you have multiple installations of the target system, then you can enable this feature after you deploy the Oracle Identity Manager release 9.1.0.2 bundle patch that addresses Bug 9181280.
If you enable the Dependent Lookup Fields feature, then entries in the lookup field are linked with the target system installation from which the entries are copied. This allows you to select lookup field values that are specific to the target system installation on which the provisioning operation is to be performed.
Note:
The bundle patch that addressed Bug 9181280 had not been released at the time of release of this connector.
To enable the Dependent Lookup Fields feature after you deploy the bundle patch that addresses Bug 9181280, you must make changes in the forms listed in Table 4-3. This table lists the forms, the lookup fields on the forms, and the lookup query that you must use for each lookup field. The procedure is described after the table.
Table 4-3 Queries for Lookup Field Synchronization
| Process Form | Lookup Field | Oracle Database Version of the Query | Microsoft SQL Server Version of the Query |
|---|---|---|---|
|
For IBM DB2 UDB |
|||
|
UD_DB_DB2_T Note: This is a child form. |
Tablespace |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.DB2.Tablespaces' AND lkv_encoded like CONCAT('$Form data. UD_DB_DB2_U_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.DB2.Tablespaces' AND lkv_encoded like'$Form data. UD_DB_DB2_U_ITRES$' + '~%' |
|
UD_DB_DB2_S Note: This is a child form. |
Schema |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.DB2.Schema' AND lkv_encoded like CONCAT('$Form data. UD_DB_DB2_U_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.DB2.Schema' AND lkv_encoded like'$Form data. UD_DB_DB2_U_ITRES$' + '~%' |
|
For Microsoft SQL Server |
|||
|
UD_DB_SQL_R Note: This is a child form. |
Role |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.MSSQL.DBRoles' AND lkv_encoded like CONCAT('$Form data. UD_DB_SQL_U_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.MSSQL.DBRoles' AND lkv_encoded like'$Form data. UD_DB_SQL_U_ITRES$' + '~%' |
|
UD_DB_SQL_L |
Default DataBase |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.MSSQL.DBNames' AND lkv_encoded like CONCAT('$Form data. UD_DB_SQL_L_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.MSSQL.DBNames' AND lkv_encoded like'$Form data. UD_DB_SQL_L_ITRES$' + '~%' |
|
UD_DB_SQL_L |
Default Language |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.MSSQL.DefaultLang' AND lkv_encoded like CONCAT('$Form data. UD_DB_SQL_L_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.MSSQL.DefaultLang' AND lkv_encoded like'$Form data. UD_DB_SQL_L_ITRES$' + '~%' |
|
For MySQL |
|||
|
UD_DB_MYS_P Note: This is a child form. |
Schema Privileges |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.MySQL.SchemaPrivileges' AND lkv_encoded like CONCAT('$Form data. UD_DB_MYS_U_IT_RESOURCE$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key =lku.lku_key ANDlku_type_string_key=' Lookup.DBUM.MySQL.SchemaPrivileges ' AND lkv_encoded like'$Form data. UD_DB_MYS_U_IT_RESOURCE$' + '~%' |
|
UD_DB_MYS_P |
Schemata |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = ' Lookup.DBUM.MySQL.Schemata ' AND lkv_encoded like CONCAT('$Form data. UD_DB_MYS_U_IT_RESOURCE $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key =lku.lku_key ANDlku_type_string_key=' Lookup.DBUM.MySQL.Schemata ' AND lkv_encoded like'$Formdata UD_DB_MYS_U_IT_RESOURCE $' + '~%' |
|
For Oracle Database |
|||
|
UD_DB_ORA_P Note: This is a child form. |
Privilege |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Oracle.Privileges' AND lkv_encoded like CONCAT('$Form data. UD_DB_ORA_U_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Oracle.Privileges' AND lkv_encoded like'$Form data. UD_DB_ORA_U_ITRES$' + '~%' |
|
UD_DB_ORA_U |
Default Tablespace |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Oracle.Tablespaces' AND lkv_encoded like CONCAT('$Form data. UD_DB_ORA_U_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Oracle.Tablespaces' AND lkv_encoded like'$Form data. UD_DB_ORA_U_ITRES$' + '~%' |
|
UD_DB_ORA_U |
Temporary Tablespace |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Oracle.Temp.Tablespace' AND lkv_encoded like CONCAT('$Form data. UD_DB_ORA_U_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Oracle.Temp.Tablespace' AND lkv_encoded like'$Form data. UD_DB_ORA_U_ITRES$' + '~%' |
|
UD_DB_ORA_U |
Profile Name |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Oracle.Profiles' AND lkv_encoded like CONCAT('$Form data. UD_DB_ORA_U_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Oracle.Profiles' AND lkv_encoded like'$Form data. UD_DB_ORA_U_ITRES$' + '~%' |
|
UD_DB_ORA_R Note: This is a child form. |
Role |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Oracle.Roles' AND lkv_encoded like CONCAT('$Form data. UD_DB_ORA_U_ITRES$','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key=lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Oracle.Roles' AND lkv_encoded like'$Form data. UD_DB_ORA_U_ITRES$' + '~%' |
|
For Sybase |
|||
|
UD_DB_SYB_R Note: This is a child form. |
Role |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Sybase.Roles' AND lkv_encoded like CONCAT('$Form data. UD_DB_SYB_L_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key =lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Sybase.Roles' AND lkv_encoded like'$Form data. UD_DB_SYB_L_ITRES$' + '~%' |
|
UD_DB_SYB_U |
Database Group |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Sybase.DBGroups' AND lkv_encoded like CONCAT('$Form data. UD_DB_SYB_U_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key =lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Sybase.DBGroups' AND lkv_encoded like'$Form data. UD_DB_SYB_U_ITRES$' + '~%' |
|
UD_DB_SYB_L |
Default Database |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Sybase.Databases' AND lkv_encoded like CONCAT('$Form data. UD_DB_SYB_L_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key =lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Sybase.Databases' AND lkv_encoded like'$Form data. UD_DB_SYB_L_ITRES$' + '~%' |
|
UD_DB_SYB_L |
Default Language |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key = lku.lku_key AND lku_type_string_key = 'Lookup.DBUM.Sybase.DefaultLang' AND lkv_encoded like CONCAT('$Form data. UD_DB_SYB_L_ITRES $','~%') |
SELECT lkv_encoded,lkv_decoded FROM lkv lkv,lku lku WHERE lkv.lku_key =lku.lku_key ANDlku_type_string_key='Lookup.DBUM.Sybase.DefaultLang' AND lkv_encoded like'$Form data. UD_DB_SYB_L_ITRES$' + '~%' |
To enable lookup fields on each form:
Note:
You must enable lookup fields in the order given in Table 5–3.
-
On the Design Console, expand Development Tools and double-click Form Designer.
-
Search for and open the form for the target system that you are using. See Section 4.5, "Configuring the Connector for Multiple Installations of the Target System" for a listing of the process forms for each target system.
-
Click Create New Version, enter a new version number, and then save the version.
-
From the Current Version list, select the version that you created.
-
Open the Properties tab, and expand Components.
-
Add properties for each lookup field on the form as follows:
-
Select the Lookup Code property, and then click Delete Property.
-
Select the first lookup field on the form, and then click Add Property. For example, if you are using Oracle Database as the target system, then select Privilege on the UD_DB_ORA_P form.
-
In the Add Property dialog box:
From the Property Name list, select Lookup Column Name.
In the Property Value field, enter
lkv_encoded.Click the Save icon, and then close the dialog box.
-
Select the lookup field, and then click Add Property.
-
In the Add Property dialog box:
From the Property Name list, select Column Names.
In the Property Value field, enter
lkv_encoded.Click the Save icon, and then close the dialog box.
-
Select the lookup field, and then click Add Property.
-
In the Add Property dialog box:
From the Property Name list, select Column Widths.
In the Property Value field, enter
234. -
Select the lookup field, and then click Add Property.
-
In the Add Property dialog box:
From the Property Name list, select Column Captions.
In the Property Value field, enter
lkv_encoded.Click the Save icon, and then close the dialog box.
-
Select the lookup field, and then click Add Property.
-
In the Add Property dialog box:
From the Property Name list, select Lookup Query.
In the Property Value field, enter the query given in Table 4-3.
Click the Save icon, and then close the dialog box.
-
-
Repeat Step 6 for each lookup field on the form.
-
Click the Save icon to save the changes to the form.
-
If you have performed Steps 2 through 9 on a child form, then:
-
Expand Development Tools and double-click Form Designer.
-
Search for and open the parent form with which the child form is associated. form.
-
Click Create New Version, enter a new version number, and then save the version.
-
Click Make Version Active.
-
4.6 Configuring the Connector for Multiple Trusted Source Reconciliation
Note:
This connector supports multiple trusted source reconciliation.
This section describes an optional procedure. Perform this procedure only if you want to configure the connector for multiple trusted source reconciliation.
The following are examples of scenarios in which there is more than one trusted source for user data in an organization:
-
One of the target systems is a trusted source for data about users. The second target system is a trusted source for data about contractors. The third target system is a trusted source for data about interns.
-
One target system holds the data of some of the identity fields that constitute an OIM User. Two other systems hold data for the remaining identity fields. In other words, to create an OIM User, data from all three systems would need to be reconciled.
If the operating environment of your organization is similar to that described in either one of these scenarios, then this connector enables you to use the target system as one of the trusted sources of person data in your organization.
See Oracle Identity Manager Design Console Guide for detailed information about multiple trusted source reconciliation.
4.7 Configuring Reconciliation Queries
Note:
This section describes an optional procedure. Perform this procedure only if you want to modify one of the predefined reconciliation queries or create your own query.
You can modify existing queries in the properties file. In addition, you can add your own queries in the file. The query whose name you specify as the value of the Query Name scheduled task attribute is applied during reconciliation.
To modify an existing query or to add a query in the properties file:
Caution:
You must not modify the Delete Users query in the reconciliation properties file. If you add a WHERE clause to this query, then only a subset of the actual set of users is brought to Oracle Identity Manager for comparison. OIM Users whose user IDs do not match any of these users are deleted from Oracle Identity Manager.
-
Open the properties file in a text editor. If you are creating your own properties file, then ensure that the extension is .properties. You can place this properties file in any directory on the target system host computer.
-
Apply the following guidelines while modifying or adding a query:
Note:
Before you modify or add a query in the properties file, you must run the query by using any standard database client to ensure that the query produces the required results when it is run against the target system database.
-
Query Name
Do not include spaces in the query name.
Ensure that the query name is not the same as the name of any other query in the properties file.
-
SELECT clause
Add or modify the column list in the SELECT clause. Note that changes that you make in the SELECT clause must be duplicated in the lookup definition that holds mappings between resource object fields and target system column names and, if required, on the process form. See Section 4.2, "Adding or Removing Attributes for Reconciliation" for more information.
-
Comments
Use the number sign to begin each comment line in the properties file.
Add comments to describe changes that you make in existing queries and also to describe new queries that you add in the file.
See existing comments in the file for an example.
-
Line breaks
If you want to introduce line breaks in the query (to improve readability), then add a backslash (\) at the end of each line.
-
SQL keywords
You must ensure that the query does not contain any clause or keyword that modifies or can be used to modify data in the database.
-
-
Save and close the properties file.
4.8 Configuring Validation of Data During Reconciliation and Provisioning
You can configure validation of reconciled and provisioned single-valued data according to your requirements. For example, you can validate data fetched from the First Name attribute to ensure that it does not contain the number sign (#). In addition, you can validate data entered in the First Name field on the process form so that the number sign (#) is not sent to the target system during provisioning operations.
For data that fails the validation check, the following message is displayed or recorded in the log file:
Value returned for field FIELD_NAME is false.
Note:
This feature cannot be applied to the Locked/Unlocked status attribute of the target system.
To configure validation of data:
-
Write code that implements the required validation logic in a Java class.
This validation class must implement the oracle.iam.connectors.common.validate.Validator interface and the validate method.
See Also:
The Javadocs shipped with the connector for more information about this interface
The following sample validation class checks if the value in the First Name attribute contains the number sign (#):
public boolean validate(HashMap hmUserDetails, HashMap hmEntitlementDetails, String field) { /* * You must write code to validate attributes. Parent * data values can be fetched by using hmUserDetails.get(field) * For child data values, loop through the * ArrayList/Vector fetched by hmEntitlementDetails.get("Child Table") * Depending on the outcome of the validation operation, * the code must return true or false. */ /* * In this sample code, the value "false" is returned if the field * contains the number sign (#). Otherwise, the value "true" is * returned. */ boolean valid=true; String sFirstName=(String) hmUserDetails.get(field); for(int i=0;i<sFirstName.length();i++){ if (sFirstName.charAt(i) == '#'){ valid=false; break; } } return valid; } -
Create a JAR file to hold the Java class.
-
If you are using Oracle Identity Manager release 9.1.0.x, then copy the JAR file into one of the following directories:
-
If you create the Java class for validating a process form field for reconciliation, then copy the JAR file into the OIM_HOME/xellerate/ScheduleTask directory.
-
If you create the Java class for validating a process form field for provisioning, the copy the JAR file into the OIM_HOME/xellerate/JavaTasks directory.
-
-
If you are using Oracle Identity Manager release 11.1.1, then run the Upload JARs utility to post the JAR file to the Oracle Identity Manager database. This utility is copied to the following location when you install Oracle Identity Manager:
Note:
Verify that the WL_HOME environment variable is set to the directory in which Oracle WebLogic Server is installed.
For Microsoft Windows:
OIM_HOME/server/bin/UploadJars.bat
For UNIX:
OIM_HOME/server/bin/UploadJars.sh
When you run the utility, you are prompted to enter the login credentials of the Oracle Identity Manager administrator, URL of the Oracle Identity Manager host computer, context factory value, type of JAR file being uploaded, and the location from which the JAR file is to be uploaded.
If you created the Java class for validating a process form field for reconciliation, then specify
2as the value of the JAR type.If you created the Java class for validating a process form field for provisioning, then specify
1as the value of the JAR type.See Also:
The "Upload JAR and Resource Bundle Utilities" chapter of Oracle Fusion Middleware Developer's Guide for Oracle Identity Manager for detailed information about the Upload JARs utility
-
If you created the Java class for validating a process form field for reconciliation, then:
-
Log in to the Design Console.
-
If you have configured your target system as a target resource, then search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.TargetRecon.Validation
-
Lookup.DBUM.MSSQL.TargetRecon.Validation
-
Lookup.DBUM.MySQL.TargetRecon.Validation
-
Lookup.DBUM.Oracle.TargetRecon.Validation
-
Lookup.DBUM.Sybase.TargetRecon.Validation
-
-
If you have configured your target system as a trusted source, then search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.TrustedRecon.Validation
-
Lookup.DBUM.MSSQL.TrustedRecon.Validation
-
Lookup.DBUM.MySQL.TrustedRecon.Validation
-
Lookup.DBUM.Oracle.TrustedRecon.Validation
-
Lookup.DBUM.Sybase.TrustedRecon.Validation
-
-
In the Code Key, enter the resource object attribute name. In the Decode, enter the class name that is implementing the validation logic.
For example, if you want to perform validation of the First Name attribute, then you must enter the following values in the Code Key and Decode columns:
Code Key: First Name
Decode: oracle.iam.connectors.recon.validation
Here, the Code Key specifies the name of the resource object attribute that you want to validate and Decode is the complete package name of the Implementation class.
-
Save the changes to the lookup definition.
-
To enable validation, in the scheduled task for your database, set the value of the Use Validation For Reconciliation entry to
yes, and then save your changes.
-
-
If you created the Java class for validating a process form field for provisioning, then:
-
Log in to the Design Console.
-
Search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.Provisioning.Validation
-
Lookup.DBUM.MSSQL.Provisioning.Validation
-
Lookup.DBUM.MySQL.Provisioning.Validation
-
Lookup.DBUM.Oracle.Provisioning.Validation
-
Lookup.DBUM.Sybase.Provisioning.Validation
-
-
In the Code Key, enter the process form field name. In the Decode, enter the class name that is implementing the validation logic.
For example, if you want to perform validation of the User Name process form field, then you must enter the following values in the Code Key and Decode columns:
Code Key: UD_DB_DB2_U_USERNAME
Decode: DataValidator.java
Here, the Code Key specifies the name of the resource object attribute that you want to validate and Decode is the name of the class that is implementing the validation logic.
-
Save the changes to the lookup definition.
-
To enable validation for provisioning:
-
Search for and open one of the following lookup definitions:
Lookup.DBUM.DB2.Configuration
Lookup.DBUM.MSSQL.Configuration
Lookup.DBUM.MySQL.Configuration
Lookup.DBUM.Oracle.Configuration
Lookup.DBUM.Sybase.Configuration
-
Provide values for the following lookup entries:
i. Use Validation For Provisioning: Enter
yesto specify that you want to enable validation.ii. Provisioning Validation Lookup: Ensure that the value of this entry is set to one of the following:
Lookup.DBUM.DB2.Provisioning.Validation
Lookup.DBUM.MSSQL.Provisioning.Validation
Lookup.DBUM.MySQL.Provisioning.Validation
Lookup.DBUM.Oracle.Provisioning.Validation
Lookup.DBUM.Sybase.Provisioning.Validation
-
-
4.9 Configuring Transformation of Data During Reconciliation
You can configure transformation of reconciled single-valued data according to your requirements. For example, you can use First Name and Last Name values to create a value for the Full Name field in Oracle Identity Manager.
Note:
This feature cannot be applied to the Locked/Unlocked status attribute of the target system.
To configure transformation of data:
-
Write code that implements the required transformation logic in a Java class.
This transformation class must implement the oracle.iam.connectors.common.transform.Transformation interface and the transform method.
See Also:
The Javadocs shipped with the connector for more information about this interface
The following sample transformation class creates a value for the Full Name attribute by using values fetched from the First Name and Last Name attributes of the target system:
package oracle.iam.connectors.common.transform; import java.util.HashMap; public class TransformAttribute implements Transformation { /* Description:Abstract method for transforming the attributes param hmUserDetails<String,Object> HashMap containing parent data details param hmEntitlementDetails <String,Object> HashMap containing child data details */ public Object transform(HashMap hmUserDetails, HashMap hmEntitlementDetails,String sField) { /* * You must write code to transform the attributes. Parent data attribute values can be fetched by using hmUserDetails.get("Field Name"). *To fetch child data values, loop through the * ArrayList/Vector fetched by hmEntitlementDetails.get("Child Table") * Return the transformed attribute. */ String sFirstName= (String)hmUserDetails.get("First Name"); String sLastName= (String)hmUserDetails.get("Last Name"); String sFullName=sFirstName+"."+sLastName; return sFullName; } } -
Create a JAR file to hold the Java class.
-
If you are using Oracle Identity Manager release 9.1.0.x, then copy the JAR file into the following directory:
OIM_HOME/xellerate/ScheduleTask
-
If you are using Oracle Identity Manager release 11.1.1, then run the Upload JARs utility to post the JAR file to the Oracle Identity Manager database. This utility is copied into the following location when you install Oracle Identity Manager:
Note:
Verify that the WL_HOME environment variable is set to the directory in which Oracle WebLogic Server is installed.
For Microsoft Windows:
OIM_HOME/server/bin/UploadJars.bat
For UNIX:
OIM_HOME/server/bin/UploadJars.sh
When you run the utility, you are prompted to enter the login credentials of the Oracle Identity Manager administrator, URL of the Oracle Identity Manager host computer, context factory value, type of JAR file being uploaded, and the location from which the JAR file is to be uploaded. Specify
2as the value of the JAR type.See Also:
The "Upload JAR and Resource Bundle Utilities" chapter of Oracle Fusion Middleware Developer's Guide for Oracle Identity Manager for detailed information about the Upload JARs utility
-
Log in to the Design Console.
-
If you have configured your target system as a target resource, then search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.TargetRecon.Transformation
-
Lookup.DBUM.MSSQL.TargetRecon.Transformation
-
Lookup.DBUM.MySQL.TargetRecon.Transformation
-
Lookup.DBUM.Oracle.TargetRecon.Transformation
-
Lookup.DBUM.Sybase.TargetRecon.Transformation
-
-
If you have configured your target system as a trusted source, then search for and open one of the following lookup definitions:
-
Lookup.DBUM.DB2.TrustedRecon.Transformation
-
Lookup.DBUM.MSSQL.TrustedRecon.Transformation
-
Lookup.DBUM.MySQL.TrustedRecon.Transformation
-
Lookup.DBUM.Oracle.TrustedRecon.Transformation
-
Lookup.DBUM.Sybase.TrustedRecon.Transformation
-
-
In the Code Key, enter the resource object attribute name. In the Decode, enter the class name that implements the validation logic.
-
Save the changes to the lookup definition.
-
In the scheduled task for your database, set the value of the Use Validation For Reconciliation entry to
yes. -
Save the changes to the scheduled task.
4.10 Configuring the Connector for Reconciling and Provisioning Object-Level Privileges
Note:
Perform the procedure described in this section only if both the conditions are true:
-
Your target system is Oracle Database and it has been configured as a target resource.
-
You want configure the connector for provisioning and reconciling object-level privileges.
This section provides information about the following topics:.
-
Section 4.10.1, "Configuring the Connector for Provisioning Object-Level Privileges"
-
Section 4.10.2, "Configuring the Connector for Reconciling Object-Level Privileges"
4.10.1 Configuring the Connector for Provisioning Object-Level Privileges
To configure the connector for provisioning object-level privileges:
Note:
A sample scenario in which you provision object-level privileges for the table database object in Oracle Database has been used to illustrate the procedure.
-
Create the Lookup.DBUM.Oracle.Tables and Lookup.DBUM.Oracle.Tables.Privileges lookup definitions for table objects and object privileges, respectively. Note that you do not add any entries to these lookup definitions. The entries in these lookup definitions will be populated after you perform lookup field synchronization.
See Section 5.6, "Creating Lookup Definitions Used During Connector Operations" for information about creating a lookup definition.
-
Update the properties file that contains queries to perform lookup field synchronization as follows:
-
Open the properties file in a text editor.
-
Add the following queries for reconciling table objects and table object privileges:
-
Lookup.DBUM.Oracle.Tables = SELECT OBJECT_NAME FROM USER_OBJECTS WHERE OBJECT_TYPE='TABLE'
-
Lookup.DBUM.Oracle.Tables.Privileges = SELECT DISTINCT PRIVILEGE from USER_TAB_PRIVS
-
-
-
Run the DBUM Lookup Reconciliation scheduled task to reconcile into the lookup definitions (created in Step 1) existing table objects and table object privileges in Oracle Database.
See Section 3.3, "Scheduled Task for Lookup Field Synchronization" for more information about the attributes of the DBUM Lookup Reconciliation scheduled task.
-
Create a child form that contains attributes for table object and object privilege as follows:
-
Expand Development Tools, and then double-click Form Designer.
-
In the Table Name field, enter
UD_DB_ORA_T. -
In the Description field, enter
DBUM Manage Object Level Privileges. -
On the Additional Columns tab, click Add.
A blank row is displayed in the Additional Columns tab.
-
Enter values for the following columns on the blank row that you added:
-
Name:
UD_DB_ORA_T_TABLE -
Variant Type:
String -
Length:
100 -
Field Label:
Table Name -
Field Type:
LookupField -
Order:
1
-
-
Click Add.
A blank row is displayed in the Additional Columns tab.
-
Enter values for the following columns on the blank row that you added:
-
Name:
UD_DB_ORA_T_PRIVILEGE -
Variant Type:
String -
Length:
100 -
Field Label:
Privilege -
Field Type:
LookupField -
Order:
2
-
-
Click the Save icon.
-
On the Properties tab expand Components.
-
Select Table Name, and then click Add Property to add properties for the Table Name lookup field.
-
In the Add Property dialog box:
-
From the Property Name list, select Lookup Code.
-
In the Property Value field, enter
Lookup.DBUM.Oracle.Tables. -
Click the Save icon, and then close the dialog box.
The following screenshot shows the Add Property dialog box:
-
-
Select Privilege, and then click Add Property to add properties for the Privilege lookup field.
-
In the Add Property dialog box:
-
From the Property Name list, select Lookup Code.
-
In the Property Value field, enter
Lookup.DBUM.Oracle.Tables.Privileges. -
Click the Save icon, and then close the dialog box.
-
-
Click Make Version Active.
-
-
Assign to the parent form the child table, which is represented by the child form created in the preceding step as follows:
-
Expand Development Tools, and then double-click Form Designer.
-
Search for and open the UD_DB_ORA_U process form, which is the parent process form.
-
Click Create New Version to create a version of the form. Then, enter a version name and click the Save icon.
-
On the Child Tables tab, click Assign.
-
In the Assign Child Tables dialog box, select the child table UD_DB_ORA_T, click the right arrow, and then click OK. The following screenshot shows the Assign Child Tables dialog box:
-
Click OK.
The selected child table is assigned to the form.
-
Click Make Version Active.
-
-
Update the Parameter configuration lookup definition by adding lookup entries corresponding to the child attributes as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.Parameter.Configuration lookup definition.
-
Click Add.
-
In the Code Key column, enter, for example,
ora_table_privilege. -
In the Decode column, enter (for example)
UD_DB_ORA_T_PRIVILEGE~varchar2~IN~EXCLUDE_VALIDATION. -
Click Add.
-
In the Code Key column, enter, for example,
ora_tablename. -
In the Decode column, enter (for example)
UD_DB_ORA_T_TABLE~varchar2~IN~EXCLUDE_VALIDATION.The following screenshot shows the Lookup.DBUM.Oracle.Parameter.Configuration lookup definition:
-
-
Update the Query configuration lookup definition by adding lookup entries corresponding to the child attributes as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.Query.Configuration lookup definition.
-
Click Add.
-
In the Code Key column, enter, for example,
ORA_ADD_TABLE_PRIVILEGE. -
In the Decode column, enter (for example)
GRANT :ora_table_privilege ON :ora_tablename TO :ora_user_id_external. -
Click Add.
-
In the Code Key column, enter, for example,
ORA_REVOKE_TABLE_PRIVILEGE. -
In the Decode column, enter (for example)
REVOKE :ora_table_privilege ON :ora_tablename FROM :ora_user_id_external.The following screenshot shows the Lookup.DBUM.Oracle.Query.Configuration lookup definition:
-
-
Update the Oracle DB User process definition task by adding a process task that is used for granting object-level privileges as follows:
-
Expand Process Management, and then double-click Process Definition.
-
Search for and open the Oracle DB User process definition.
-
On the Tasks tab, click Add.
The Creating New Task dialog box is displayed.
-
In the Task Name field, enter the name of the process task, for example,
Grant object privileges. -
In the Task Properties region:
-
From the Child Table list, select UD_DB_ORA_T.
-
From the Trigger Type list, select Insert.
-
Select the following check boxes:
Conditional
Disable Manual Insert
Allow Cancellation while Pending
Allow Multiple Instances
-
-
Click the Save icon, and then close the dialog box.
-
On the Tasks tab, double-click the process task that you added.
The Editing Task window is displayed.
-
On the Integration tab, click Add.
-
In the Handler Selection dialog box, to add an adapter to the process task, select the Adapter option.
A list of adapters that you can assign to the process task is displayed in the Handler Name region.
-
From the list of adapters, select adpDBUMEXECUTEQUERY, and then click the Save icon.
A list of adapter variables is displayed.
-
To map the adapter variables listed in this table, select the adapter variable, click Map, specify the data given in the following table, and then save and close the dialog box:
Variable Name Data Type Map To Qualifier Literal Value Column Name
String
Literal
String
NA
Adapter Return Value
Object
Response Code
NA
NA
processInstanceKey
Long
Process Data
Process Instance
NA
itResourceColumnName
string
Literal
String
UD_DB_ORA_U_ITRES
lookupCodeKey
String
Literal
String
ORA_ADD_TABLE_PRIVILEGE
value
String
Literal
String
NA
setFlag
String
Literal
String
NA
-
To add responses listed in this table, on the Responses tab, click Add, and then specify the data given in the following table:
Response Description Status INVALID_SQL
Invalid SQL Statement
R
ERROR
Error occurred while performing the operation. Please check the log.
R
INCOMPLETE_LOOKUP_DEF
Incomplete or invalid lookup definition
R
INSUFFICIENT_PRIVILEGE
Insufficient Privilege to execute the query
R
SUCCESS
Object Level Privilege added successfully
C
INVALID_SYNTAX
Incorrect Query format
R
PERMISSION_DENIED
User doesn't have permission to perform this action
R
INVALID_IT_RESOURCE_NAME
Invalid IT Resource name in process task mapping
R
ERROR_UTIL_INIT
Error occurred while initializing parameters
R
-
-
Update the Oracle DB User process definition task by adding a process task that is used for updating table privileges as follows:
-
Expand Process Management, and then double-click Process Definition.
-
Search for and open the Oracle DB User process definition.
-
On the Tasks tab, click Add.
The Creating New Task dialog box is displayed.
-
In the Task Name field, enter the name of the process task, for example,
Update Table Object. -
In the Task Properties region:
-
From the Child Table list, select UD_DB_ORA_T.
-
From the Trigger Type list, select Update.
The following is a screenshot of the Creating New Task dialog box displaying the Task Properties region:
-
-
Click the Save icon, and then close the dialog box.
-
On the Tasks tab, double-click the process task that you added.
The Editing Task dialog box is displayed.
-
On the Integration tab, click Add.
-
In the Handler Selection dialog box, to add an adapter to the process task, select the Adapter option.
A list of adapters that you can assign to the process task is displayed in the Handler Name region.
-
From the list of adapters, select adpDBUMEXECUTEMULTIOLDDATAQUERY.
-
To map the adapter variables listed in this table, select the adapter, click Map, and then specify the data given in the following table:
Variable Name Data Type Map To Qualifier Literal Value Column Name
String
Literal
String
NA
Adapter Return Value
Object
Response Code
NA
NA
processInstanceKey
Long
Process Data
Process Instance
NA
itResourceColumnName
string
Literal
String
UD_DB_ORA_U_ITRES
lookupCodeKey
String
Literal
String
ORA_REVOKE_TABLE_PRIVILEGE
colName1
String
Literal
String
UD_DB_ORA_T_PRIVILEGE
colValue1
String
Process Data
From the list adjacent to the Map To list, select Manage Object Level Privileges.
Privilege
From the list adjacent to the Qualifier list, select Old Value.
NA
colName2
String
Literal
String
UD_DB_ORA_T_TABLE
colValue2
String
Process Data
From the list adjacent to the Map To list, select Manage Object Level Privileges.
Table Name
From the list adjacent to the Qualifier list, select Old Value.
NA
-
Modify the message that is displayed when the Update Table Object process task (created in Step 9.d) is completed:
On the Responses tab, in the Responses region, modify the description corresponding to the SUCCESS response. For example, change the description to
The Table privilege was updated successfully. -
To add the task to be generated on receiving the SUCCESS response:
-
In the Responses region, select the row with the SUCCESS response.
-
In the Tasks To Generate region, click Assign.
-
In the dialog box that appears, from the left pane, select
Grant object privileges, which is the task name created in Step 8.d. -
Click the right arrow and click OK.
-
Click the Save icon, and then close the form.
-
-
-
Update the Oracle DB User process definition task by adding a process task that is used for revoking table privileges by performing the procedure in Steps 9.a through 9.i.
4.10.2 Configuring the Connector for Reconciling Object-Level Privileges
To configure the connector for reconciling object-level privileges:
Note:
A sample scenario in which you reconcile object-level privileges for the table database object in Oracle Database has been used to illustrate the procedure.
-
Add the query that is used to reconcile object-level privileges to the reconciliation query properties file as follows:
-
In the resource object definition, add a multivalued reconciliation field as follows:
-
Expand the Resource Management folder, and then double-click Resource Objects.
-
Search for and open the Oracle DB User resource object.
-
On the Object Reconciliation tab, click Add Field to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter
Table Privilege Listas the name of the field. -
From the Field Type list, select Multi-Valued Attribute.
The following screenshot shows the Add Reconciliation Field dialog box:
-
Click the Save icon, and then close the dialog box.
-
Right-click the Table Privilege List reconciliation field, and then select Define Property Fields to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter
Table Name. -
From the Field Type list, select String.
-
Click the Save icon and close the dialog box.
-
Right-click the Table Privilege List reconciliation field, and then select Define Property Fields to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter
Privilege. -
From the Field Type list, select String.
-
Click the Save icon and close the dialog box.
-
If you are using Oracle Identity Manager release 11.1.1, then click Create Reconciliation Profile. This copies changes made to the resource object into the MDS.
-
-
Create a reconciliation field mapping for the multivalued attribute as follows:
-
Expand the Process Management folder, and then double-click Process Definition.
-
Search for and open the Oracle DB User form.
-
On the Reconciliation Field Mappings tab of the process definition, click Add Table Map.
-
In the Add Reconciliation Table Mapping dialog box:
-
From the Field Name list, select Table Privilege List.
-
From the Table Name list, select UD_DB_ORA_T.
The following is a screenshot of the Add Reconciliation Table Mapping dialog box:
-
Click the Save icon and close the dialog box.
-
-
Right-click the newly created attribute, Table Privilege List (for example), and then select Define Property Field Map.
-
In the Field Name field, select Table Name.
-
Double-click the Process Data Field field, and then select UD_DB_ORA_T_TABLE_NAME.
-
Click the save icon and then close the dialog box.
-
Right-click the newly created attribute, Table Privilege List (for example), and then select Define Property Field Map.
-
In the Field Name field, select Privilege.
-
Double-click the Process Data Field field, and then select UD_DB_ORA_T_PRIVILEGE.
-
Click the save icon.
-
-
Create a lookup definition that maps fields of the Table Privilege List resource object attribute with the column names used in the reconciliation query (that you added in Step 1.b) as follows:
-
Expand the Administration folder, and then double-click Lookup Definition.
-
In the Code field, enter
Lookup.DBUM.Oracle.TargetRecon.TablePrivilege.Mappingas the name of the lookup definition. -
In the Field field, enter
DBUM. -
Select the Lookup Type option.
-
In the Group field, enter
DBUM. -
Click the Save icon.
The lookup definition is created.
-
Add the following entries to this lookup definition by clicking Add and specifying values for the Code Key and Decode columns:
Code Key Decode Table Name
LOOKUP~TABLE_NAME
Privilege
LOOKUP~PRIVILEGE
-
-
Create a lookup definition, which contains configurable entries for the multivalued attribute, as follows:
Perform the procedure describes in Step 4 with the following differences:
-
While performing Step 4.b, in the Code field, enter
Lookup.DBUM.Oracle.TargetRecon.TablePrivilege.Configuration. -
While performing Step 4.g, add the following entries to the lookup definition:
Code Key Decode Child Attribute Mapping Lookup
Lookup.DBUM.Oracle.TargetRecon.TablePrivilege.Mapping
Child Query Name
ORACLE_TARGET_USER_TABLE_PRIVILEGE
Child Reconciliation Query Filter Lookup
Lookup.DBUM.Oracle.TargetRecon.TablePrivilege.QueryFilter
Parent Attribute
USERNAME
-
-
Update the Lookup.DBUM.Oracle.TargetRecon.Mapping lookup definition by adding a lookup entry corresponding to the multivalued attribute (added to the resource object in Step 2) as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.TargetRecon.Mapping lookup definition.
-
Click Add.
-
In the Code Key column, enter
Table Privilege List. -
In the Decode column, enter
CHILD~Lookup.DBUM.Oracle.TargetRecon.TablePrivilege.Configuration. -
Click the Save icon.
-
-
Create an empty lookup definition for target reconciliation table query filter as follows:
See Also:
Section A.4.18, "Lookup.DBUM.Oracle.TargetRecon.Role.QueryFilter" for an example on using the lookup definition for target reconciliation table query filter
-
Expand the Administration folder, and then double-click Lookup Definition.
-
In the Code field, enter
Lookup.DBUM.Oracle.TargetRecon.TablePrivilege.QueryFilteras the name of the lookup definition. -
In the Field field enter
DBUM. -
Select the Lookup Type option.
-
In the Group field, enter
DBUM. -
Click the Save icon.
The lookup definition is created.
-
4.11 Configuring the Connector for Reconciling and Provisioning Authorization to Oracle Database Vault Realms
Note:
Perform the procedure described in this section only if both the conditions are true:
-
Your target system is Oracle Database and it has been configured as a target resource.
-
You want configure the connector for provisioning and reconciling authorization to Oracle Database Vault realms.
This section provides information about the following topics:.
4.11.1 Configuring the Connector for Provisioning Authorization to Oracle Database Vault Realms
To configure the connector for provisioning authorization to Oracle Database Vault realms:
-
Create the Lookup.DBUM.Oracle.DBVault.Realms and Lookup.DBUM.Oracle.DBVault.AuthType lookup definitions for realm name and authorization type, respectively. Note that you do not add any entries to these lookup definitions. The entries in these lookup definitions will be populated after you perform lookup field synchronization.
See Section 5.6, "Creating Lookup Definitions Used During Connector Operations" for information about creating a lookup definition.
-
Update the properties file that contains queries to perform lookup field synchronization as follows:
-
Open the properties file in a text editor.
-
Add the following query for reconciling realm names:
Lookup.DBUM.Oracle.DBVault.Realms = SELECT REALM_NAME FROM FROM DVSYS.DBA_DV_REALM_AUTH
-
-
Run the DBUM Lookup Reconciliation scheduled task to reconcile into the lookup definitions (created in Step 1) names of existing realms in Oracle Database.
See Section 3.3, "Scheduled Task for Lookup Field Synchronization" for more information about the attributes of the DBUM Lookup Reconciliation scheduled task.
-
Update the Lookup.DBUM.Oracle.DBVault.AuthType lookup definition as follows:
-
Expand Administration, and then double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.DBVault.AuthType lookup definition.
-
Add the following entries to this lookup definition by clicking Add and then specifying values for the Code Key and Decode columns:
Code Key Decode 0
Participant
1
Other
-
-
Create a child form that contains attributes for realm names and authorization types as follows:
-
Expand Development Tools, and then double-click Form Designer.
-
In the Table Name field, enter
UD_DB_ORA_V. -
In the Description field, enter
DBUM Manage DB Vault Authorization. -
On the Additional Columns tab, click Add.
A blank row is displayed in the Additional Columns tab.
-
Enter values for the following columns on the blank row that you added:
-
Name:
UD_DB_ORA_V_REALM -
Variant Type:
String -
Length:
100 -
Field Label:
Realm Name -
Field Type:
LookupField -
Order:
1
-
-
Click Add.
A blank row is displayed in the Additional Columns tab.
-
Enter values for the following columns on the blank row that you added:
-
Name:
UD_DB_ORA_V_AUTHTYPE -
Variant Type:
String -
Length:
100 -
Field Label:
Authorization Type -
Field Type:
LookupField -
Order:
2
-
-
Click the Save icon.
-
On the Properties tab expand Components.
-
Select Realm Name, and then click Add Property to add properties for the Table Name lookup field.
-
In the Add Property dialog box:
-
From the Property Name list, select Lookup Code.
-
In the Property Value field, enter
Lookup.DBUM.Oracle.DBVault.Realms. -
Click the Save icon, and then close the dialog box.
The following screenshot shows the Add Property dialog box:
-
-
Select Authorization Type, and then click Add Property to add properties for the Privilege lookup field.
-
In the Add Property dialog box:
-
From the Property Name list, select Lookup Code.
-
In the Property Value field, enter
Lookup.DBUM.Oracle.DBVault.AuthType. -
Click the Save icon, and then close the dialog box.
-
-
-
Assign to the parent form the child table, which is represented by the child form created in the preceding step as follows:
-
Expand Development Tools, and then double-click Form Designer.
-
Search for and open the UD_DB_ORA_U process form, which is the parent process form.
-
Click Create New Version to create a version of the form. Then, enter a version name and click the Save icon.
-
On the Child Tables tab, click Assign.
-
In the Assign Child Tables dialog box, select the child table UD_DB_ORA_V, click the right arrow, and then click OK. The following screenshot shows the Assign Child Tables dialog box:
-
Click OK.
The selected child table is assigned to the form.
-
Click Make Version Active.
-
-
Update the Parameter configuration lookup definition by adding lookup entries corresponding to the child attributes as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.Parameter.Configuration lookup definition.
-
Click Add.
-
In the Code Key column, enter, for example,
realm_name. -
In the Decode column, enter (for example)
UD_DB_ORA_V_REALM~varchar2~IN~EXCLUDE_VALIDATION. -
Click Add.
-
In the Code Key column, enter, for example,
auth_options. -
In the Decode column, enter (for example)
UD_DB_ORA_V_AUTHTYPE~varchar2~IN~EXCLUDE_VALIDATION.The following screenshot shows the Lookup.DBUM.Oracle.Parameter.Configuration lookup definition:
-
-
Update the Query configuration lookup definition by adding lookup entries corresponding to the child attributes as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.Query.Configuration lookup definition.
-
Click Add.
-
In the Code Key column, enter, for example,
ORA_ADD_DBVAULT_AUTHORIZATION. -
In the Decode column, enter (for example)
{CALL DVSYS.DBMS_MACADM.ADD_AUTH_TO_REALM(:realm_name,:ora_user_id_external,:auth_options)}. -
Click Add.
-
In the Code Key column, enter, for example,
ORA_REVOKE_DBVAULT_AUTHORIZATION. -
In the Decode column, enter (for example)
{CALL DVSYS.DBMS_MACADM.DELETE_AUTH_FROM_REALM(:realm_name,:ora_user_id)}.The following screenshot shows the Lookup.DBUM.Oracle.Query.Configuration lookup definition:
-
-
Update the Oracle DB User process definition task by adding a process task that is used for granting authorization to Oracle Database Vault realms as follows:
-
Expand Process Management, and then double-click Process Definition.
-
Search for and open the Oracle DB User process definition.
-
On the Tasks tab, click Add.
The Creating New Task dialog box is displayed.
-
In the Task Name field, enter the name of the process task, for example,
Grant DBVault Authorization. -
In the Task Properties region:
-
From the Child Table list, select UD_DB_ORA_V.
-
From the Trigger Type list, select Insert.
-
-
Click the Save icon, and then close the dialog box.
-
On the Tasks tab, double-click the process task that you added.
The Editing Task window is displayed.
-
On the Integration tab, click Add.
-
In the Handler Selection dialog box, to add an adapter to the process task, select the Adapter option.
A list of adapters that you can assign to the process task is displayed in the Handler Name region.
-
From the list of adapters, select adpDBUMExecuteStoredProc.
-
To map the adapter variables listed in this table, select the adapter, click Map, and then specify the data given in the following table:
Variable Name Data Type Map To Qualifier Literal Value Column Name
String
Literal
String
NA
Adapter Return Value
Object
Response Code
NA
NA
processInstanceKey
Long
Process Data
Process Instance
NA
itResourceColumnName
string
Literal
String
UD_DB_ORA_U_ITRES
lookupCodeKey
String
Literal
String
ORA_ADD_DBVAULT_AUTHORIZATION
value
String
Literal
String
NA
setFlag
String
Literal
String
NA
-
To add responses listed in this table, on the Responses tab, click Add, and then specify the data given in the following table:
Response Description Status INVALID_SQL
Invalid SQL Statement
R
ERROR
Error occurred while performing the operation. Please check the log.
R
INCOMPLETE_LOOKUP_DEF
Incomplete or invalid lookup definition
R
INSUFFICIENT_PRIVILEGE
Insufficient Privilege to execute the query
R
SUCCESS
Vault authorization added successfully
C
INVALID_SYNTAX
Incorrect Query format
R
PERMISSION_DENIED
User doesn't have permission to perform this action
R
INVALID_IT_RESOURCE_NAME
Invalid IT Resource name in process task mapping
R
ERROR_UTIL_INIT
Error occurred while initializing parameters
R
-
-
Update the Oracle DB User process definition task by adding a process task that is used for updating authorization to Oracle Database Vault realms as follows:
-
Expand Process Management, and then double-click Process Definition.
-
Search for and open the Oracle DB User process definition.
-
On the Tasks tab, click Add.
The Creating New Task dialog box is displayed.
-
In the Task Name field, enter the name of the process task, for example,
Update DBVault Authorization. -
In the Task Properties region:
-
From the Child Table list, select UD_DB_ORA_V.
-
From the Trigger Type list, select Update.
-
-
Click the Save icon, and then close the dialog box.
-
On the Tasks tab, double-click the process task that you added.
The Editing Task window is displayed.
-
On the Integration tab, click Add.
-
In the Handler Selection dialog box, to add an adapter to the process task, select the Adapter option.
A list of adapters that you can assign to the process task is displayed in the Handler Name region.
-
From the list of adapters, select adpDBUMEXECUTEMULTIOLDDATASTOREDPROC.
-
To map the adapter variables listed in this table, select the adapter, click Map, and then specify the data given in the following table:
Variable Name Data Type Map To Qualifier Literal Value Column Name
String
Literal
String
NA
Adapter Return Value
Object
Response Code
NA
NA
processInstanceKey
Long
Process Data
Process Instance
NA
itResourceColumnName
string
Literal
String
UD_DB_ORA_U_ITRES
lookupCodeKey
String
Literal
String
ORA_REVOKE_DBVAULT_AUTHORIZATION
colName1
String
Literal
String
UD_DB_ORA_V_REALM
colValue1
String
Process Data
From the list adjacent to the Map To list, select DBUM Manage DB Vault Authorization.
Realm Name
From the list adjacent to the Qualifier list, select Check Old Value.
NA
colName2
String
Literal
String
UD_DB_ORA_V_AUTHTYPE
colValue2
String
Process Data
From the list adjacent to the Map To list, select DBUM Manage DB Vault Authorization.
Authorization Type
From the list adjacent to the Qualifier list, select Check Old Value.
NA
-
Modify the message that is displayed when the Update DBVault Authorization process task (created in Step 10.d) is completed:
On the Responses tab, in the Responses region, modify the description corresponding to the SUCCESS response. For example, change the description to
The DBVault authorization was updated successfully. -
To add the task that has to be generated when the SUCCESS response is received:
-
In the Responses region, select the row with the SUCCESS response.
-
In the Tasks To Generate region, click Assign.
-
In the dialog box that is displayed, from the left pane, select Grant DBVault Authorization.
-
Click the right arrow and click OK.
-
Click the Save icon, and then close the form.
-
-
-
Update the Oracle DB User process definition task by adding a process task that is used for revoking authorization to Oracle Database Vault realms by performing the procedure in Step 10.a through 10.i.
4.11.2 Configuring the Connector for Reconciling Authorization to Oracle Database Vault Realms
To configure the connector for reconciling authorization to Oracle Database Vault realms:
-
Add the query that is used to reconcile authorization to Oracle Database Vault realms to the reconciliation query properties file as follows:
-
Open the properties file in a text editor.
-
Add the following query for reconciling authorization to Oracle Database Vault realms for a particular user:
ORACLE_TARGET_USER_DBVAULT_AUTHORIZATION = SELECT REALM_NAME,AUTH_OPTIONS FROM DVSYS.DBA_DV_REALM_AUTH WHERE GRANTEE = :USERNAME
-
-
In the resource object definition, add a multivalued reconciliation field as follows:
-
Expand the Resource Management folder, and then double-click Resource Objects.
-
Search for and open the Oracle DB User resource object.
-
On the Object Reconciliation tab, click Add Field to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter
Realm Authorization Listas the name of the field. -
From the Field Type list, select Multi-Valued.
The following screenshot shows the Add Reconciliation Field dialog box:
-
Click the Save icon, and then close the dialog box.
-
Right-click the DBVault Authorization reconciliation field, and then select Define Property Fields to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter
Realm Name. -
From the Field Type list, select String.
-
Click the Save icon and close the dialog box.
-
Right-click the DBVault Authorization reconciliation field, and then select Define Property Fields to open the Add Reconciliation Field dialog box.
-
In the Field Name field, enter
Authorization Type. -
From the Field Type list, select String.
-
Click the Save icon and close the dialog box.
-
If you are using Oracle Identity Manager release 11.1.1, then click Create Reconciliation Profile. This copies changes made to the resource object into the MDS.
-
-
Create a reconciliation field mapping for the multivalued attribute as follows:
-
Expand the Process Management folder, and then double-click Process Definition.
-
Search for and open the Oracle DB User form.
-
On the Reconciliation Field Mappings tab of the process definition, click Add Table Map.
-
In the Add Reconciliation Table Mapping dialog box:
-
From the Field Name list, select DBVault Authorization.
-
From the Table Name list, select UD_DB_ORA_V.
-
Click the Save icon and close the dialog box.
-
-
Right-click the newly created attribute, DBVault Authorization (for example), and then select Define Property Field Map.
-
In the Field Name field, select Realm Name.
-
Double-click the Process Data Field field, and then select UD_DB_ORA_V_REALM.
-
Click the save icon and then close the dialog box.
-
Right-click the newly created attribute, DBVault Authorization (for example), and then select Define Property Field Map.
-
In the Field Name field, select Authorization Type.
-
Double-click the Process Data Field field, and then select UD_DB_ORA_V_AUTHTYPE.
-
Click the save icon.
-
-
Create a lookup definition that maps fields of the DBVault Authorization resource object attribute with the column names used in the reconciliation query (that you added in Step 1.b) as follows:
-
Expand the Administration folder, and then double-click Lookup Definition.
-
In the Code field, enter
Lookup.DBUM.Oracle.TargetRecon.DBVault.Mappingas the name of the lookup definition. -
In the Field field, enter
DBUM. -
Select the Lookup Type option.
-
In the Group field, enter
DBUM. -
Click the Save icon.
The lookup definition is created.
-
Add the following entries to this lookup definition by clicking Add and specifying values for the Code Key and Decode columns:
Code Key Decode Realm Name
LOOKUP~REALM_NAME
Authorization Type
AUTH_OPTIONS
-
-
Create a lookup definition, which contains configurable entries for the multivalued attribute, as follows:
Perform the procedure describes in Step 4 with the following differences:
-
While performing Step 4.b, in the Code field, enter
Lookup.DBUM.Oracle.TargetRecon.DBVault.Configuration. -
While performing Step 4.g, add the following entries to the lookup definition:
Code Key Decode Child Attribute Mapping Lookup
Lookup.DBUM.Oracle.TargetRecon.DBVault.Mapping
Child Query Name
ORACLE_TARGET_USER_DBVAULT_AUTHORIZATION
Child Reconciliation Query Filter Lookup
Lookup.DBUM.Oracle.TargetRecon.DBVault.QueryFilter
Parent Attribute
USERNAME
-
-
Update the Lookup.DBUM.Oracle.TargetRecon.Mapping lookup definition by adding a lookup entry corresponding to the multivalued attribute (added to the resource object in Step 2) as follows:
-
Expand Administration, and double-click Lookup Definition.
-
Search for and open the Lookup.DBUM.Oracle.TargetRecon.Mapping lookup definition.
-
Click Add.
-
In the Code Key column, enter
DBVAult Authorization. -
In the Decode column, enter
CHILD~Lookup.DBUM.Oracle.TargetRecon.DBVault.Configuration. -
Click the Save icon.
-
-
Create an empty lookup definition for target reconciliation table query filter as follows:
See Also:
Section A.4.18, "Lookup.DBUM.Oracle.TargetRecon.Role.QueryFilter" for an example on using the lookup definition for target reconciliation table query filter
-
Expand the Administration folder, and then double-click Lookup Definition.
-
In the Code field, enter
Lookup.DBUM.Oracle.TargetRecon.DBVault.QueryFilteras the name of the lookup definition. -
In the Field field enter
DBUM. -
Select the Lookup Type option.
-
In the Group field, enter
DBUM. -
Click the Save icon.
The lookup definition is created.
-