| Exit Print View | |
Sun Dual 10GbE SPF+ PCIe 2.0 Low Profile Adapter User’s Guide |

|
Documentation, Support, and Training
Understanding the Low Profile Adapter
Front Panel Connectors and LEDs
Power and Environmental Requirements
Hardware and Software Requirements
Solaris Platform Installation Overview
Linux Platform Installation Overview
Microsoft Windows Platform Installation Overview
Verify the Driver Version on a Solaris Platform
Remove the Driver From a Solaris Platform
Download and Install the Driver on a Linux Platform
Remove the Driver From a Linux Platform
Download and Install the Driver on a Microsoft Windows Platform
Remove the Driver From a Microsoft Windows Platform
Installing the Low Profile Adapter
Install the Adapter in a System
Verify the Installation in a Solaris SPARC System
Verify the Installation in a Solaris x86 System
Verify the Installation in a Linux System
Verify the Installation in a Microsoft Windows System
Create /etc/hostname.ixgbe# Files
Configure the Network Host Files With the ifconfig Command
Boot Over the Network Using PXE
Boot Solaris x86 and Linux Systems Over a 10GbE Network
Install the Solaris OS Over a 10GbE Network on SPARC Systems
Configuring the Driver Parameters
Driver Parameters for the Solaris OS
Set ixgbe Driver Parameters in the Solaris OS
Solaris OS Performance Variables
Improve Performance in the Solaris OS
Set Driver Parameters in Linux
Configure Jumbo Frames in Solaris OS
Configure Jumbo Frames in Linux
Configuring Link Aggregation in a Solaris Environment
Display Information About Link Aggregations
Configure Static VLANs in a Solaris Environment
Configure VLANs in a Linux Environment
Configure VLANs in a Microsoft Windows Environment
With multiple VLANs on a card, a server with a single card can have a logical presence on multiple IP subnets. By default, you can define 128 VLANs for each VLAN-aware card on your server. However, you can increase this number by changing the system parameters.
If your network does not require multiple VLANs, you can use the default configuration, in which case no further configuration is necessary.
VLANs enable you to split your physical LAN into logical subparts, providing an essential tool for increasing the efficiency and flexibility of your network.
VLANs are commonly used to separate groups of network users into manageable broadcast domains, to create logical segmentation of workgroups, and to enforce security policies among each logical segment. Each defined VLAN behaves as its own separate network, with its traffic and broadcasts isolated from the others, increasing the bandwidth efficiency within each logical group.
Although VLANs are commonly used to create individual broadcast domains or separate IP subnets, it can be useful for a server to have a presence on more than one VLAN simultaneously. Several Sun products support multiple VLANs on a per-port or per-interface basis, allowing very flexible network configurations.
The following figure shows an example network that uses VLANs.
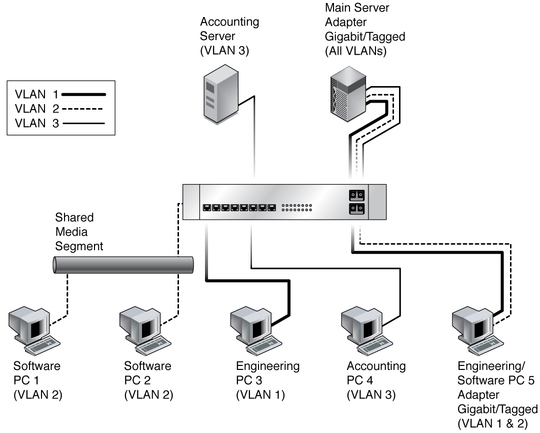
The example network has the following features:
The physical LAN network consists of a switch, two servers, and five clients. The LAN is logically organized into three different VLANs, each representing a different IP subnet.
VLAN 1 is an IP subnet consisting of the Main Server, Client 3, and Client 5. This VLAN represents an engineering group.
VLAN 2 includes the Main Server, Clients 1 and 2 by means of a shared media segment, and Client 5. This VLAN is a software development group.
VLAN 3 includes the Main Server, the Accounting Server, and Client 4. This VLAN is an accounting group.
The Main Server is a high-use server that must be accessed from all VLANs and IP subnets. The server has a Sun Dual 10GbE SFP+ PCIe 2.0 Low Profile Adapter installed. All three IP subnets are accessed by means of the single physical Ethernet adapter interface. The server is attached to one of the switch’s Gigabit Ethernet ports, which is configured for VLANs 1, 2, and 3. Both the Ethernet adapter and the connected switch port have tagging turned on. Because of the tagging VLAN capabilities of both devices, the server is able to communicate on all three IP subnets in this network, but continues to maintain broadcast separation between all of those subnets. The following list describes the components of this network:
The Accounting Server is available to only VLAN 3. The Accounting Server is isolated from all traffic on VLANs 1 and 2. The switch port connected to the server has tagging turned off.
Clients 1 and 2 are attached to a shared media hub that is then connected to the switch. Clients 1 and 2 belong only to VLAN 2. Those clients are logically in the same IP subnet as the Main Server and Client 5. The switch port connected to this segment has tagging turned off.
Client 3 is a member of VLAN 1. This client can communicate only with the Main Server and Client 5. Tagging is not enabled on Client 3’s switch port.
Client 4 is a member of VLAN 3. This client can communicate only with the servers. Tagging is not enabled on Client 4’s switch port.
Client 5 is a member of both VLANs 1 and 2. This client has a Sun Dual 10GbE SFP+ PCIe 2.0 Low Profile Adapter installed. Client 5 is connected to switch port 10. Both the Ethernet adapter and the switch port are configured for VLANs 1 and 2, and both have tagging enabled.
VLAN tagging is only required to be enabled on switch ports that create trunk links to other VLAN-aware Ethernet switches, or on ports connected to tag-capable end-stations, such as servers or workstations with VLAN-aware Ethernet adapters.