| Skip Navigation Links | |
| Exit Print View | |
|
Oracle VM Server for SPARC 2.1 Administration Guide Oracle VM Server for SPARC |
| Skip Navigation Links | |
| Exit Print View | |
|
Oracle VM Server for SPARC 2.1 Administration Guide Oracle VM Server for SPARC |
Part I Oracle VM Server for SPARC 2.1 Software
1. Overview of the Oracle VM Server for SPARC Software
2. Installing and Enabling Software
4. Setting Up Services and the Control Domain
Introduction to a Virtual Network
Virtual Device Identifier and Network Interface Name
Find Oracle Solaris OS Network Interface Name
Assigning MAC Addresses Automatically or Manually
Range of MAC Addresses Assigned to Logical Domains
Automatic Assignment Algorithm
Duplicate MAC Address Detection
Using Network Adapters With Logical Domains
Determine If a Network Adapter Is GLDv3-Compliant
Configuring Virtual Switch and Service Domain for NAT and Routing
Set Up the Virtual Switch to Provide External Connectivity to Domains
Configuring IPMP in a Logical Domains Environment
Configuring Virtual Network Devices Into an IPMP Group in a Domain
Configuring and Using IPMP in the Service Domain
Using Link-Based IPMP in Logical Domains Virtual Networking
Configure Physical Link Status Updates
Configuring and Using IPMP in Releases Prior to Logical Domains 1.3
Configuring IPMP in the Guest Domain
Configuring IPMP in the Service Domain
Assign VLANs to a Virtual Switch and Virtual Network Device
Install a Guest Domain When the Install Server Is in a VLAN
Configure a Virtual Switch With an NIU Network Device
Using Link Aggregation With a Virtual Switch
Configure Virtual Network and Virtual Switch Devices to Use Jumbo Frames
Compatibility With Older (Jumbo-Unaware) Versions of the vnet and vsw Drivers
12. Performing Other Administration Tasks
Part II Optional Oracle VM Server for SPARC Software
13. Oracle VM Server for SPARC Physical-to-Virtual Conversion Tool
14. Oracle VM Server for SPARC Configuration Assistant
15. Using the Oracle VM Server for SPARC Management Information Base Software
16. Logical Domains Manager Discovery
17. Using the XML Interface With the Logical Domains Manager
A virtual network (vnet) device is a virtual device that is defined in a domain connected to a virtual switch. A virtual network device is managed by the virtual network driver, and it is connected to a virtual network through the hypervisor using logical domain channels (LDCs).
A virtual network device can be used as a network interface with the name vnetn, which can be used like any regular network interface and configured with the ifconfig command .
You can add a virtual network device to a domain, set options for an existing virtual network device, and remove a virtual network device by using the ldm add-vnet, ldm set-vnet, and ldm rm-vnet commands, respectively. For more information, see the ldm(1M) man page.
Figure 8-1 Setting Up a Virtual Network
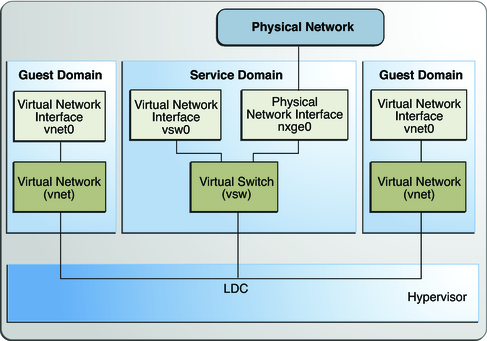
Following is an explanation for the example in Figure 8-1.
The virtual switch in the service domain is connected to the guest domains. This allows guest domains to communicate with each other.
The virtual switch is also connected to the physical network interface nxge0. This allows guest domains to communicate with the physical network.
The virtual switch network interface vsw0 is created in the service domain, so this allows the two guest domains to communicate with the service domain.
The virtual switch network interface vsw0 in the service domain can be configured using the ifconfig command.
The virtual network interfaces vnet0 in the guest domains can be configured using the ifconfig command.
Basically the virtual switch behaves like a regular physical network switch and switches network packets between the different systems, such as guest domains, service domain, and physical network, to which it is connected.
Until the Oracle VM Server for SPARC 2.1 release, the Logical Domains Manager would assign LDC channels in the following manner:
An LDC channel would be assigned between the virtual network devices and the virtual switch device.
An LDC channel would be assigned between each pair of virtual network devices that are connected to the same virtual switch device (inter-vnet).
The inter-vnet LDC channels are configured so that virtual network devices can communicate directly to achieve high guest-to-guest communications performance. However, as the number of virtual network devices in a virtual switch device increases, the number of required LDC channels for inter-vnet communications increases exponentially.
Starting with the Oracle VM Server for SPARC 2.1 release, you can choose to enable or disable inter-vnet LDC channel allocation for all virtual network devices attached to a given virtual switch device. By disabling this allocation, you can reduce the consumption of LDC channels, which are limited in number.
Disabling this allocation is useful in the following situations:
When guest-to-guest communications performance is not of primary importance
When a large number of virtual network devices are required in a virtual switch device
By not assigning inter-vnet channels, more LDC channels are available for use to add more virtual I/O devices to a guest domain.
Note - If guest-to-guest performance is of higher importance than increasing the number of virtual network devices in the system, do not disable inter-vnet LDC channel allocation.
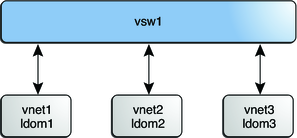
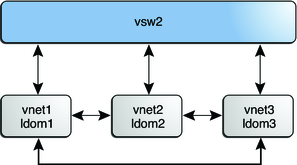
The following figure shows a typical virtual switch that has three virtual network devices. The inter-vnet-link property is set to on, which means that inter-vnet LDC channels are allocated. The guest-to-guest communications between vnet1 and vnet2 is performed directly without going through the virtual switch.
Figure 8-2 Virtual Switch Configuration That Uses Inter-Vnet Channels
The following figure shows the same virtual switch configuration with the inter-vnet-link property set to off. That means that inter-vnet LDC channels are not allocated. You can see that fewer LDC channels are used than when the inter-vnet-link property is set to on. In this configuration, guest-to-guest communications between vnet1 and vnet2 must go through vsw1.
Note - Disabling the assignment of inter-vnet LDC channels does not prevent guest-to-guest communications. Instead, all guest-to-guest communications traffic goes through the virtual switch rather than directly from one guest domain to another guest domain.
Figure 8-3 Virtual Switch Configuration That Does Not Use Inter-Vnet Channels