| Skip Navigation Links | |
| Exit Print View | |
|
System Administration Guide: IP Services Oracle Solaris 10 8/11 Information Library |
| Skip Navigation Links | |
| Exit Print View | |
|
System Administration Guide: IP Services Oracle Solaris 10 8/11 Information Library |
Part I Introducing System Administration: IP Services
1. Oracle Solaris TCP/IP Protocol Suite (Overview)
2. Planning Your TCP/IP Network (Tasks)
3. Introducing IPv6 (Overview)
4. Planning an IPv6 Network (Tasks)
Preparing the Existing Network to Support IPv6
Preparing the Network Topology for IPv6 Support
Preparing Network Services for IPv6 Support
Preparing Servers for IPv6 Support
How to Prepare Network Services for IPv6 Support
How to Prepare DNS for IPv6 Support
Planning for Tunnels in the Network Topology
Security Considerations for the IPv6 Implementation
Preparing an IPv6 Addressing Plan
Creating the IPv6 Numbering Scheme
Creating a Numbering Scheme for Subnets
Creating an IPv6 Addressing Plan for Nodes
5. Configuring TCP/IP Network Services and IPv4 Addressing (Tasks)
6. Administering Network Interfaces (Tasks)
7. Configuring an IPv6 Network (Tasks)
8. Administering a TCP/IP Network (Tasks)
9. Troubleshooting Network Problems (Tasks)
10. TCP/IP and IPv4 in Depth (Reference)
13. Planning for DHCP Service (Tasks)
14. Configuring the DHCP Service (Tasks)
15. Administering DHCP (Tasks)
16. Configuring and Administering the DHCP Client
17. Troubleshooting DHCP (Reference)
18. DHCP Commands and Files (Reference)
19. IP Security Architecture (Overview)
21. IP Security Architecture (Reference)
22. Internet Key Exchange (Overview)
24. Internet Key Exchange (Reference)
25. IP Filter in Oracle Solaris (Overview)
28. Administering Mobile IP (Tasks)
29. Mobile IP Files and Commands (Reference)
30. Introducing IPMP (Overview)
31. Administering IPMP (Tasks)
Part VII IP Quality of Service (IPQoS)
32. Introducing IPQoS (Overview)
33. Planning for an IPQoS-Enabled Network (Tasks)
34. Creating the IPQoS Configuration File (Tasks)
35. Starting and Maintaining IPQoS (Tasks)
36. Using Flow Accounting and Statistics Gathering (Tasks)
The tasks throughout this chapter explain how to plan for IPv6 services on a typical enterprise network. The following figure shows the network that is referred to throughout the chapter. Your proposed IPv6 network might include some or all of the network links that are illustrated in this figure.
Figure 4-1 IPv6 Network Topology Scenario
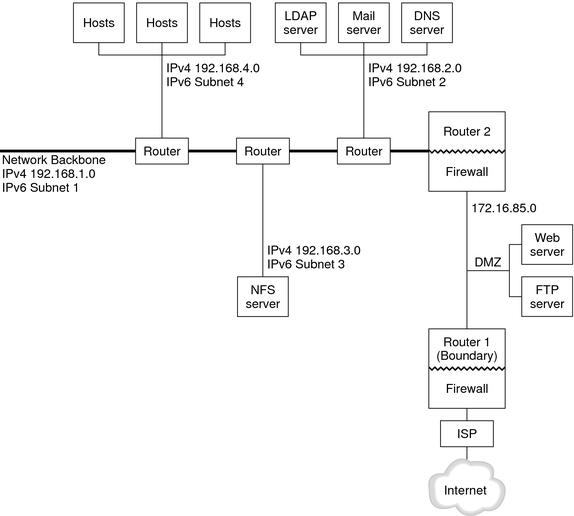
The enterprise network scenario consists of five subnets with existing IPv4 addresses. The links of the network correspond directly to the administrative subnets. The four internal networks are shown with RFC 1918-style private IPv4 addresses, which is a common solution for the lack of IPv4 addresses. The addressing scheme of these internal networks follows:
Subnet 1 is the internal network backbone 192.168.1.
Subnet 2 is the internal network 192.168.2, with LDAP, sendmail, and DNS servers.
Subnet 3 is the internal network 192.168.3, with the enterprise's NFS servers.
Subnet 4 is the internal network 192.168.4, which contains hosts for the enterprise's employees.
The external, public network 172.16.85 functions as the corporation's DMZ. This network contains web servers, anonymous FTP servers, and other resources that the enterprise offers to the outside world. Router 2 runs a firewall and separates public network 172.16.85 from the internal backbone. On the other end of the DMZ, Router 1 runs a firewall and serves as the enterprise's boundary server.
In Figure 4-1, the public DMZ has the RFC 1918 private address 172.16.85. In the real world, the public DMZ must have a registered IPv4 address. Most IPv4 sites use a combination of public addresses and RFC 1918 private addresses. However, when you introduce IPv6, the concept of public addresses and private addresses changes. Because IPv6 has a much larger address space, you use public IPv6 addresses on both private networks and public networks.