A Adding a Security Override for Package Build
This appendix contains the following topics:
-
Section A.1, "Understanding Security Overrides for Package Build"
-
Section A.3, "Adding a Security Override for the User Building Packages"
A.1 Understanding Security Overrides for Package Build
Before you build a package, you must have a security administrator add a security override if your system meets both of these conditions:
-
The database that you are using is Oracle, SQL, or IBM DB2 for LUW (Linux, UNIX, Windows).
-
The security server is enabled.
A security override is required so that the package build process can create the metadata repository tables in central objects. To add a security override, a security administrator must first add a system user for the owner of the central objects data source, and then add a security override to the user who will be building packages.
A.2 Adding a System User for Each Data Source
To add a system user for each data source:
Log into a web development client workstation or into the *DEP environment on the deployment server.
-
Enter P98OWSEC in the Fast Path to access System User Revisions.
-
On Work with User Security, from the Form menu, select Add System User.
-
On Work with System Users, in the System User field, enter the appropriate data source owner, for example DV910.
-
Click the Find button.
-
If no values are returned, add the data source owner as a system user:
-
Click the Add button.
-
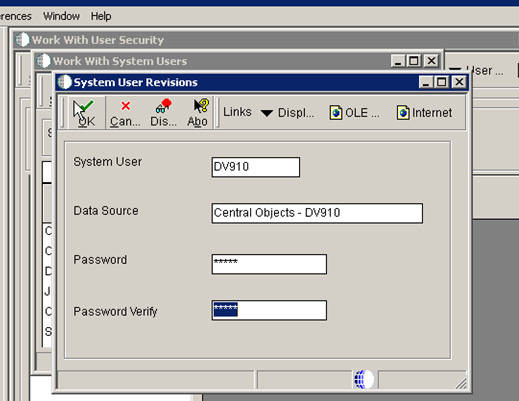
On System User Revisions, complete these fields: System User (for example, DV910), Data Source (for example, Central Objects - xxx), Password (for example, DV910 or whatever the database user's password is), and Password Verify.
-
Click OK.
-
-
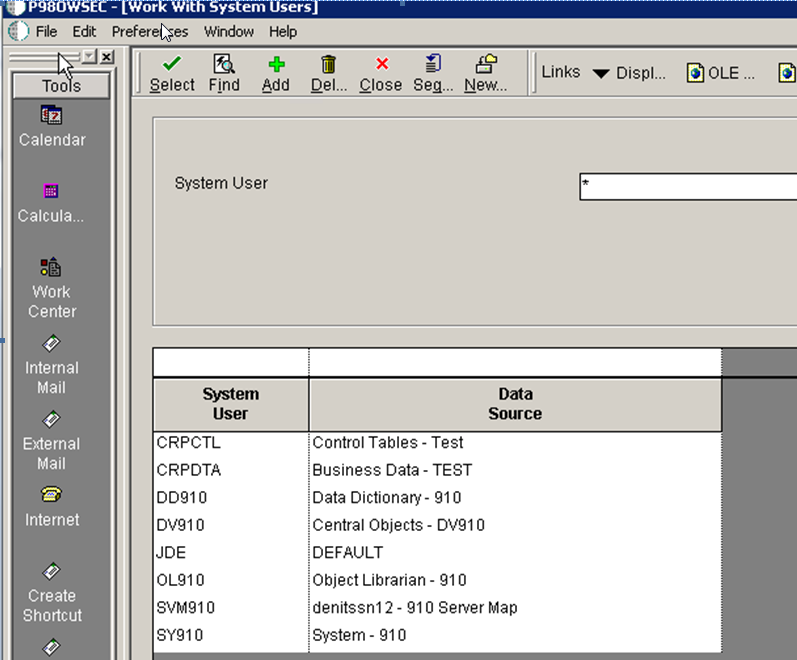
Repeat these steps for each of your defined data sources, such as Central Objects, Data Dictionary, Object Librarian, and System.
-
When you are done, the Work with System Users form should look similar to this:
-
When you are finished adding records, click the Cancel button and the Close button to return to the Work with User Security form.
A.3 Adding a Security Override for the User Building Packages
To add a security override for the user who will be building packages:
-
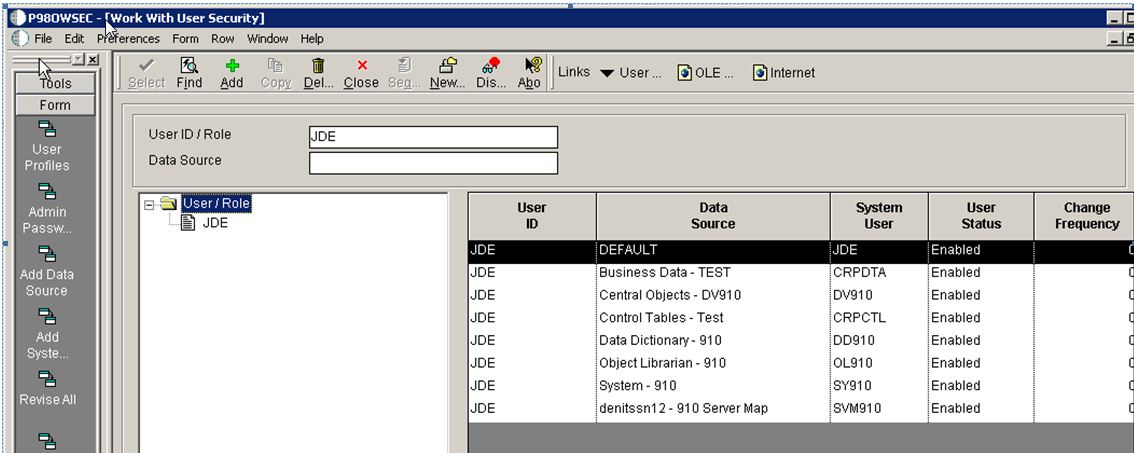
On Work with User Security, enter the User ID for the previously defined data source, such as JDE, and then click the Find button.
-
From the Form menu, select Add Data Source.
-
On Add Data Source, complete these fields:
-
User ID
-
Data Source
-
System User
-
-
Follow the above steps to add security overrides for each data source, such as Central Objects - xxx, System - xxx, and Data Dictionary - xxx.
-
Here is an example of how it should look when you are finished:
-
When you are finished, sign out of JD Edwards EnterpriseOne and restart the JD Edwards EnterpriseOne server so these necessary changes will take effect.