3 Configuring Session Monitor
This chapter describes how to configure Oracle Communications Session Monitor.
About the Platform Setup Application
The Platform Setup Application (PSA) guides you through the configuration steps to get the Session Monitor system running, including configuring the machine type, network settings, DNS settings, and SMTP settings.
The menu on the right shows your progress in the overall configuration.
The Machine Type page lets you choose the applications you want to install. In the License page you can upload a license file that also configures the applications.
The subsequent sections help you in configuring the machine for your network and time zone. These steps are optional and can be skipped by clicking on Continue.
You can review and change these settings at any time by visiting the Platform Setup Application at the https://ip-address/setup/ URL. This URL is valid for any Session Monitor server.
In the final step, the applications that are selected are installed. After the successful installation, you are taken to the applications.
Platform Setup Application Initial Log In
All Session Monitor interfaces can only be accessed through encrypted HTTPS connections. At initial login, your Web browser may not recognize the server and display the "This Connection is Untrusted" a warning message. Confirm the security exception to proceed.
Figure 3-1 shows the security exception confirmation screen.
Figure 3-1 Security Exception Confirmation
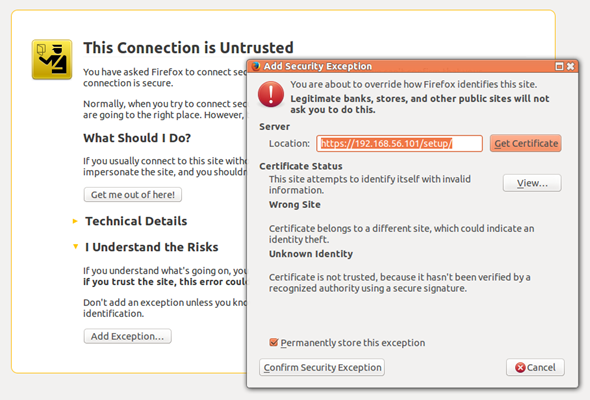
Description of ''Figure 3-1 Security Exception Confirmation''
See "Secure Configuration" for information about how to protect connections to the system and avoid the untrusted certificate warning in the future.
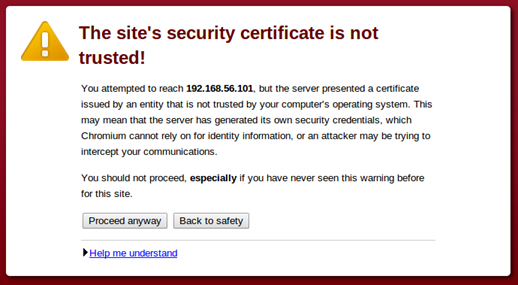
The login page allows you to access the Platform Setup Application. Enter your user name and password into the indicated fields then click Sign in.
Figure 3-2 shows the Platform Setup Application Login page.
Figure 3-2 Platform Setup Application Login Page
Description of ''Figure 3-2 Platform Setup Application Login Page''
If the user name or password entered are incorrect, a warning message appears below the login button and you'll have the opportunity to retry.
You can log into the Platform Setup Application using the default user name sysadmin and password oracle.
After you log in, you are prompted to review and accept the license of the software. You must agree to the license terms to continue.
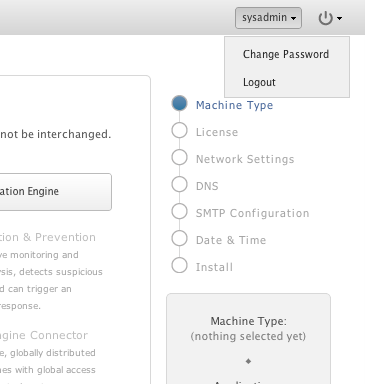
Changing Your Password
To change your password, click your user name in the top right-hand corner of the screen and select Change Password from the drop-down menu.
Figure 3-3 shows the drop-down menu when you click your user name.
In the Change Password dialog box, enter the old and the new passwords in the indicated fields and click Change to complete the action.
Note:
The password can only contain digits, letters and white spaces.Restarting or Powering Off Session Monitor
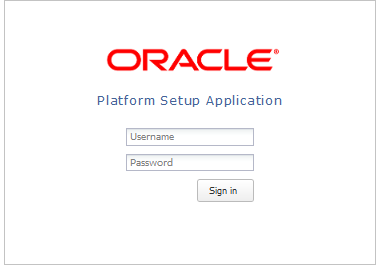
The restart and power off buttons are accessible through the power button on the top right-hand corner of the screen.
Figure 3-4 shows the drop-down menu when you click the power button.
Figure 3-4 Restarting or Powering Off Session Monitor
Description of ''Figure 3-4 Restarting or Powering Off Session Monitor''
After selecting an option, you are prompted a final time to confirm that you wish to proceed.
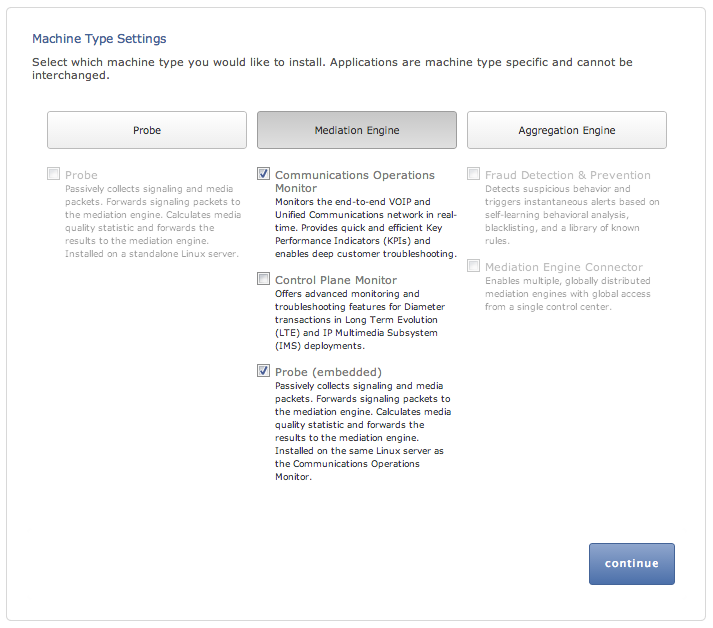
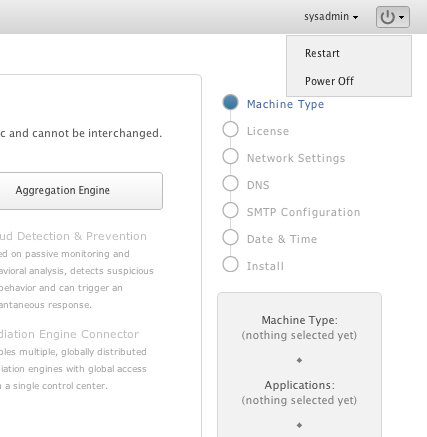
Selecting the Machine Type
Figure 3-5 shows the Machine Type Settings page.
The Machine Type Settings page allows you to select which products you want to install. This page only appears the first time you configure Session Monitor prior to the products installation.
Select your machine type by clicking Probe or Mediation Engine or Aggregation Engine button. This will enable the corresponding product selection.
Note:
-
You can select only one machine type per installation.
-
If you plan to use Packet Inspector for capturing network traffic, you need to install Operations Monitor and Probe on separate machines and then enable Packet Inspector extension on both machines. Packet Inspector is not supported on the machine where Operations Monitor and Probe are collocated.
Next, select the check boxes next to the products that you want to install. Only checked items are included in the installation.
Note:
The products are machine type specific and cannot be interchanged between machine types.For example, the Probe machine type requires a probe product, and the Mediation Engine machine type requires the Operations Monitor product.
After selecting the products, click continue to proceed with the installation. Your machine type and product selections should appear in the status panel located on the right under the navigation menu.
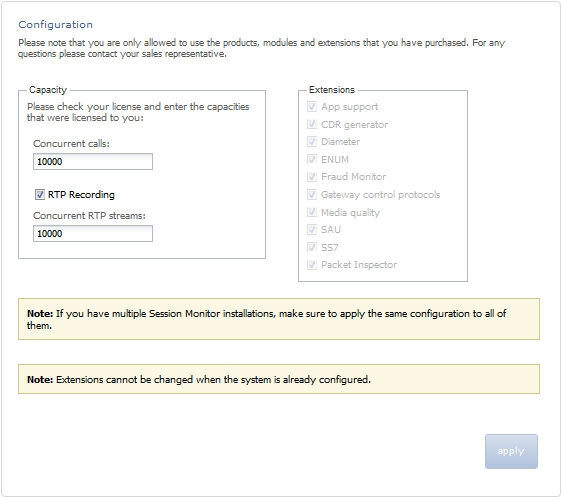
Configuring Session Monitor
This step in the configuration process allows you to configure Session Monitor settings for this machine in accordance with the terms of your license.
Note:
If you do not have a valid Session Monitor license, contact Oracle.Figure 3-6 shows the Configuration page.
On the left side of the page you must enter the number of concurrent calls printed on your license. On the right side you must check the product extensions you have a license to use. All enterprise customers should automatically check Media quality.
Note:
The number of Concurrent RTP streams can cause performance and stability issues if it is set higher than the hardware and the network permits. Values above 20 are not recommended. Changes to the RTP recording setting take effect only after a restart of the system.Click the continue button to navigate to the Network Settings page.
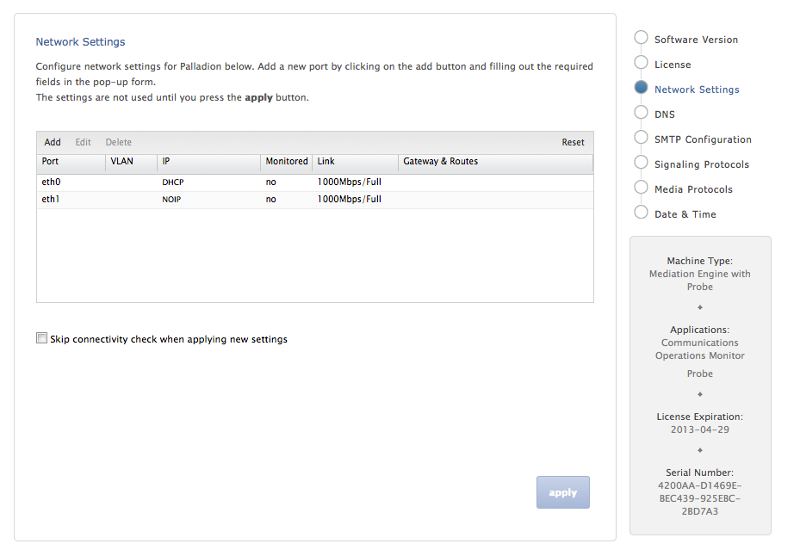
Configuring the Network Settings
The Network Settings page contains a list of configured network interfaces, with a toolbar for adding, deleting, and editing interfaces, as well as a restore button to reset the last applied settings (usually, you want to add interfaces you didn't add during the installation procedure).
There's also a check box below the network list that can be checked if you wish to apply network settings that won't allow you to reconnect to the Platform Setup Application again.
Figure 3-7 shows the Network Settings page.
Editing a Network Interface
To edit the settings of a network interface, select the entry in the list and click Edit in the toolbar (or double-click the entry).
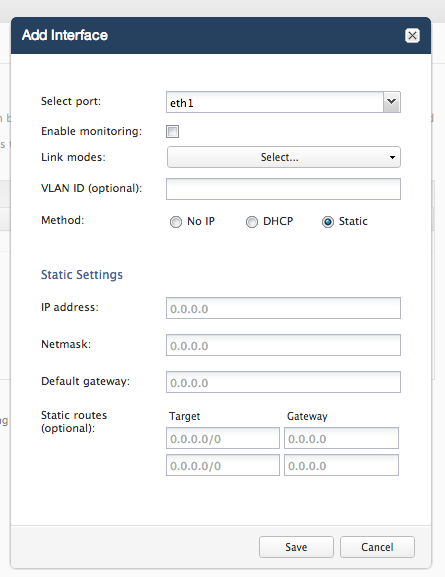
Figure 3-8 shows the dialog box to edit the network interface.
To change the IP method, select the radio button. If you select Static IP configuration, you will get additional options.
The following fields are compulsory for static IP configuration:
-
IP Address
-
Netmask
-
Default Gateway
Static routes are optional; the left column contains the target IP/netmask in CIDR format and the right one the target IP.
Note:
You can save yourself filling out the netmask by typing in CIDR format in the IP address field, for example 192.168.0.1/24, and the netmask field will get 255.255.255.0 filled in automatically.Link modes can be changed by clicking Link modes and the text Select.... This will open a pane with check boxes. There's usually no reason to touch this setting.
Monitoring can be enabled by checking the corresponding check box. This option is only available if your machine is a probe.
To save the network interface setting, click Save. The settings are not used until you click Apply/Continue.
To use and keep any changes you made in the Edit Interface dialog box, you have to click Apply/Continue in the lower-right corner. The settings are applied and the browser will try to connect to the machine. If the browser fails to connect to the machine within a given amount of time, the settings are reverted. This is to prevent locking yourself out. If you want to change the interface settings so that you won't be able to connect (for example, to deploy the server on another network), check the check box Skip connectivity check when applying new settings before clicking Apply/Continue.
If you are configuring Session Monitor for the first time you are guided to "Configuring the SMTP Settings".
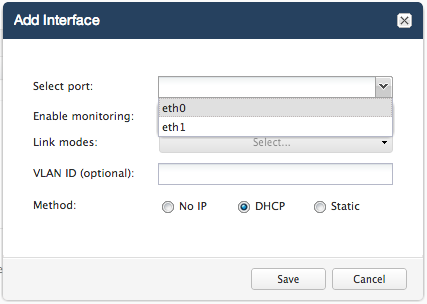
Adding a Network Interface
To add a new network interface, its physical port has to be already configured on the machine. Press Add on the toolbar. Then select an interface from the drop-down menu. You can also create a VLAN interface by entering a VLAN ID in the VLAN port.
Figure 3-9 shows the dialog box to add an interface.
Deleting a Network Interface
To delete a network interface, select the interface in the list and click Delete on the toolbar.
Resetting the Network Interface Settings
To reset your network settings to the last state before you clicked Apply/Continue, click Reset in the toolbar.
Note:
Monitoring is only enabled for machines that are configured as probes. On other machines, the monitoring check box is grayed out.Important:
Do not configure dummy interfaces with DHCP if there is no DHCP server to give an IP.When applying settings with a dummy interface using the DHCP method wait for the DHCP client to time out (usually one minute).
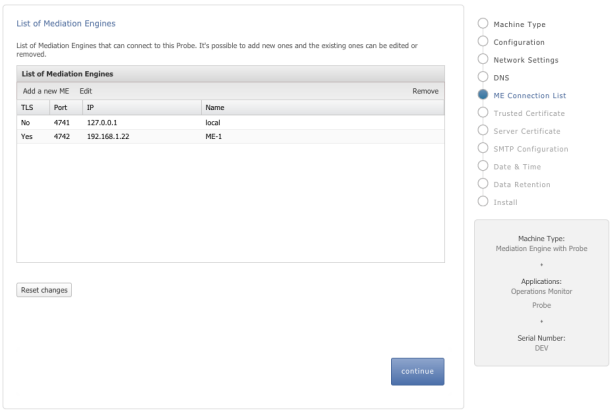
Mediation Engine Connection List
For a Probe machine type, the Mediation Engine Connection List page allows you to configure which Mediation Engines the Operations Monitor Probe connects to.
Figure 3-10 shows the ME Connection List page.
The Operations Monitor Probe can connect to one or more Mediation Engines, using TLS encryption, or with some configurations, also cleartext. Likewise, a Mediation Engine can connect to more than one Operations Monitor Probe (as well as Session Border Controller Probes).
On the Mediation Engine, cleartext connections are usually on port 4741 and encrypted connections on port 4742. For encrypted connections, the Operations Monitor Probe and the Mediation Engine need to be able to verify the certificate of the other party. See "Secure Configuration" for more information.
The Mediation Engine machines by default only accept encrypted connections (unless the Mediation Engine and Probe are on the same machine); for unencrypted connections the check box Accept insecure connections from remote probes on the Trusted Certificate page must be checked.
Figure 3-11 shows the Trusted Certificate page.
Typical Connection Scenarios
Mediation Engine and Operations Monitor Probe Are on the Same Machine
For setups with a Mediation Engine machine with an embedded Probe, a cleartext connection is automatically added to the ME connection list. For cleartext connections, no certificates are exchanged.
One Mediation Engine and Two Operations Monitor Probes
For setups with one Mediation Engine and two Operations Monitor Probes, the self-signed server certificates of both Operations Monitor Probes are uploaded as trusted certificates on the Mediation Engine, and the self-signed server certificate of the Mediation Engine is uploaded on both Operations Monitor Probes as a trusted certificate. On each Operations Monitor Probe, the IP of the Mediation Engine is added to the ME connection list with TLS check box selected.
Table 3-1 describes the actions to configure the connections between one Mediation Engine and two Operations Monitor Probes.
Table 3-1 One Mediation Engine and Two Operations Monitor Probes
| Machine | Action |
|---|---|
|
Mediation Engine |
|
|
Operations Monitor Probe 1 |
|
|
Operations Monitor Probe 2 |
|
Two Mediation Engines and One Operations Monitor Probe
For setups with two Mediation Engines and one Operations Monitor Probe, the self-signed server certificate of the Operations Monitor Probe is uploaded as trusted certificate on both Mediation Engines, and the self-signed server certificates of the Mediation Engine are uploaded on the Operations Monitor Probe as a trusted certificate. On the Operations Monitor Probe, the IPs of the Mediation Engines are both added to the ME connection list with TLS check box selected.
Table 3-2 describes the actions to configure the connections between two Mediation Engines and one Operations Monitor Probe.
Table 3-2 Two Mediation Engine and One Operations Monitor Probe
| Machine | Action |
|---|---|
|
Mediation Engine 1 |
|
|
Mediation Engine 2 |
|
|
Operations Monitor Probe |
|
For setups with more than two Operations Monitor Probes or Mediation Engines, Oracle recommends that you use PKI (Public Key Infrastructure) with root certificates as described in Session Monitor Security Guide.
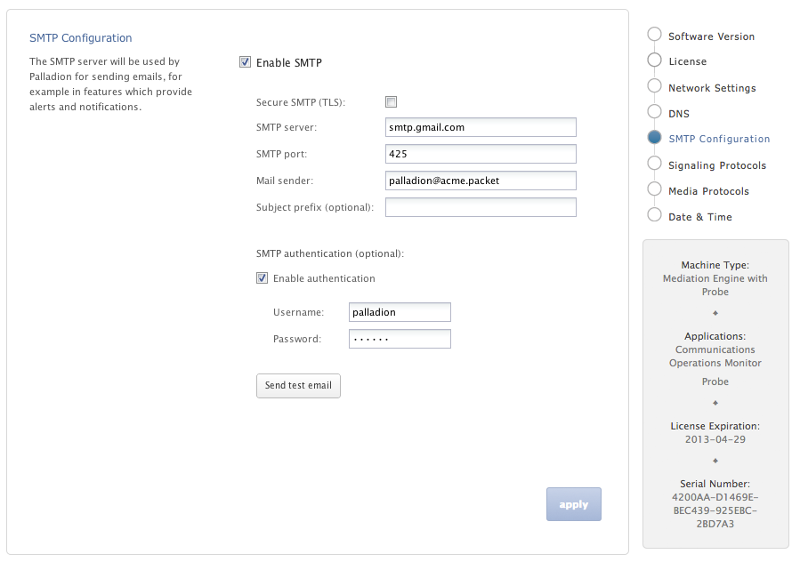
Configuring the SMTP Settings
Figure 3-12 shows the SMTP Configuration page.
Session Monitor can send notifications and alerts directly to users' email addresses. Which notification to send to which address is configured in the relevant products. However, you first need to configure the SMTP settings properly for this feature to be available.
Setting Up the Mail Server
To use the email notification feature, select Enable SMTP check box. The system will need an SMTP server to send emails. Contact your network administrator to find out the address of the server your organization uses. The default port is the standard port 25.
If the server requires a valid email account, you will need to create one for Session Monitor. Then, select Enable authentication check box and enter the credentials.
Setting Up the Email Notifications
You can choose how the emails from Session Monitor will look like in the users' mailboxes.The field Mail sender is the email address Session Monitor will use; users will see this address in the Sender: or From: field of the emails. You can optionally specify a Subject prefix; this will appear at the beginning of the subject of the emails and make it easy to identify Session Monitor's emails in users' inbox.
If you are configuring Session Monitor for the first time you will be guided to "Setting the System Date and Time".
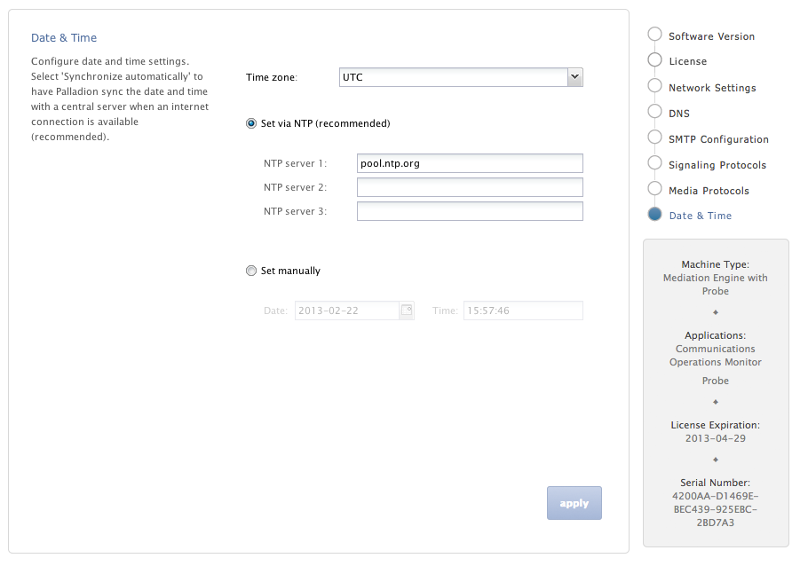
Setting the System Date and Time
Figure 3-13 shows the Date and Time Settings page.
In the Date and Time Settings page you can choose how the system will synchronize its time. Make sure that the correct method will be used, as it is important to have a correct and stable time:
-
For correctness of the data recorded by Session Monitor
-
To have automatic maintenance running during the night
-
To have correct journals to diagnose potential problems
It is recommended to use automatic time synchronization by choosing the NTP method (default). This will set the time automatically and keep it synchronized with the global internet time.
Note:
In setups with multiple Session Monitor machines, make sure to use the exact same time source for all machines. Some features might not work as expected if the machines clocks differ from each other.Setting the System Time Using the Internet Time
Session Monitor system needs a time server to synchronize with. Session Monitor is configured to use a public server pool by default (0.pool.ntp.org). This requires that the Session Monitor machine has access to the Internet. More specifically, make sure that the system is able to resolve network names with DNS (see Network Settings) and to communicate over the UDP port 123 through your internet gateway and firewall. You can specify up to three servers, in case one of them is unreachable or gives erroneous times.
Setting the System Time Using your Local Network Time
If your organization runs an NTP server (ask your network administrator about this), use that instead of a public one. To do so, select Set via NTP, and enter the network name or the IP address of this relay.
Setting the System Time Manually
If the system does not have access to any time server, you need to set the current time manually. It will then use the server's internal clock, but this will slowly drift away from the real time the rest of the world is on (for instance, 1 second more difference per day). Therefore, you should come back to the Date and Time Settings page and adjust it every week or so. To do so, get a reliable time yourself (such as a computer using network synchronization), select Set manually, and enter the correct date (YYYY-MM-DD) and time (HH:MM:SS).
Make sure to apply the settings by clicking Apply/Continue button, and wait for the synchronization to complete.
If you are configuring Session Monitor for the first time, you will be guided to "Installing the Products".
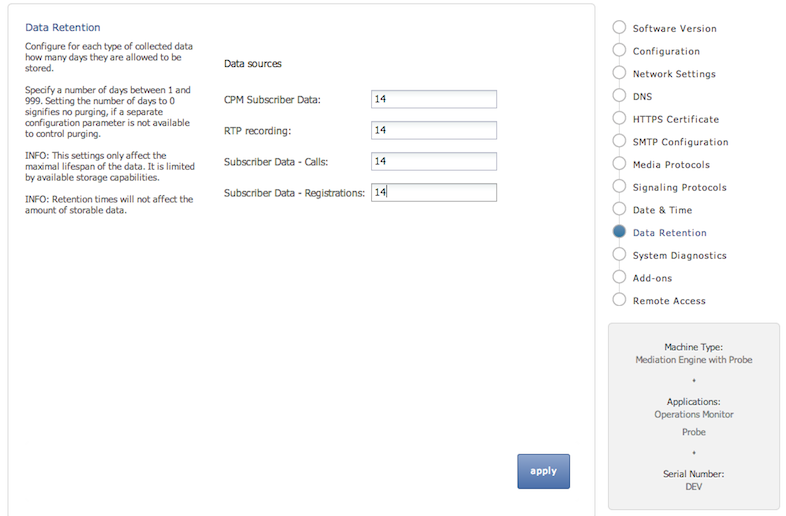
Configuring Data Retention
The Data Retention page is used for configuring data retention in database for different data sources. Some settings depend on the license settings and will be available only if the associated configuration is set.
Figure 3-14 shows the Data Retention page.
Data retention is configured in days per data type. A value of 0 disables time based data retention.
Note:
The settings only affect the maximal lifespan of the data. Data availability is limited by available storage capabilities.Note:
Retention times does not affect the amount of storable data.You can configure data retention times for the following data types:
-
CPM Subscriber Data: Delete Diameter S6 transaction data. Enabled by the CPM module.
-
RTP Recording: Delete RTP Recordings. Enabled by RTP recording configuration.
-
Subscriber Data - Calls: Delete call meta data and signaling.
Note:
Saved calls are not deleted by this option. Saved calls must be deleted by operators. (Optional) Disable user permissions for saved call functionality. -
Subscriber Data - Registration: Delete registration events.
Note:
CDR/MDRs are not supported. Data retention affects data in the database only. For deleting CDR/MDRs, use FTP to delete files after downloading.Secure Configuration
To help protect users of Session Monitor and consumers' data, see the Session Monitor Security Guide for information on the security features of Session Monitor.
During the installation of a Session Monitor server, you will encounter the server certificate and trusted certificate pages.
Server Certificate
The Server Certificate page is used to see and change the certificate used by this server. This step is recommended to protect users' data.
For more information, see the discussion about encryption and certificates in the Session Monitor Security Guide.
Trusted Certificates
The Trusted Certificates page is used to configure the authentication of session border controllers (SBCs). This step is necessary before attempting to connect SBCs to Session Monitor.
For more information, see the discussion about connection with Oracle Session Border Controller in Session Monitor Security Guide.
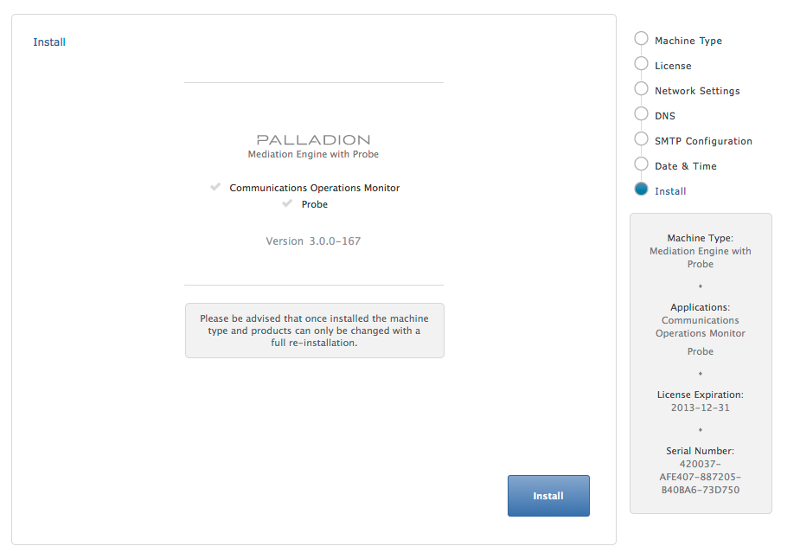
Installing the Products
The Install page summarizes the components to install. Check that you selected the correct components; after the installation is complete, the selection of the components cannot be changed.
Figure 3-15 shows the Install page.
Click Install to start with the installation. The Platform Setup Application initiates the installation process and reports back the progress. The installation process might take a few minutes to complete.
You can click on the Session Monitor button when the installation is complete. This will bring you to the installed products' interface.