CONFIGURING OBDX APPLICATION AND MOBILE BANKING USING OAM AND WEBLOGIC
Following topics in this chapter provides detailed information on configuring OBDX Application and Mobile Banking:
- Creating WebGate Agent on OAM Console
- Creating Custom Login Scheme
- Manage Application Domain and Resources
- Creating the Attributes, Object Class, Users, Groups and Adding Optional Attributes on LDAP Server
REST API configurations for Mobile Banking (2-Legged OAuth Flows) Creating WebGate Agent on OAM Console
Before you can use the new Oracle HTTP Server 12c WebGate agent for Oracle Access Manager, you must register the new WebGate agent with Oracle Access Manager by using the Oracle Access Manager Administration Console. Following are the steps to register a WebGate Agent:
Login to OAM Console.
For example: http://<hostname>:<oam_admin_port>/oamconsole
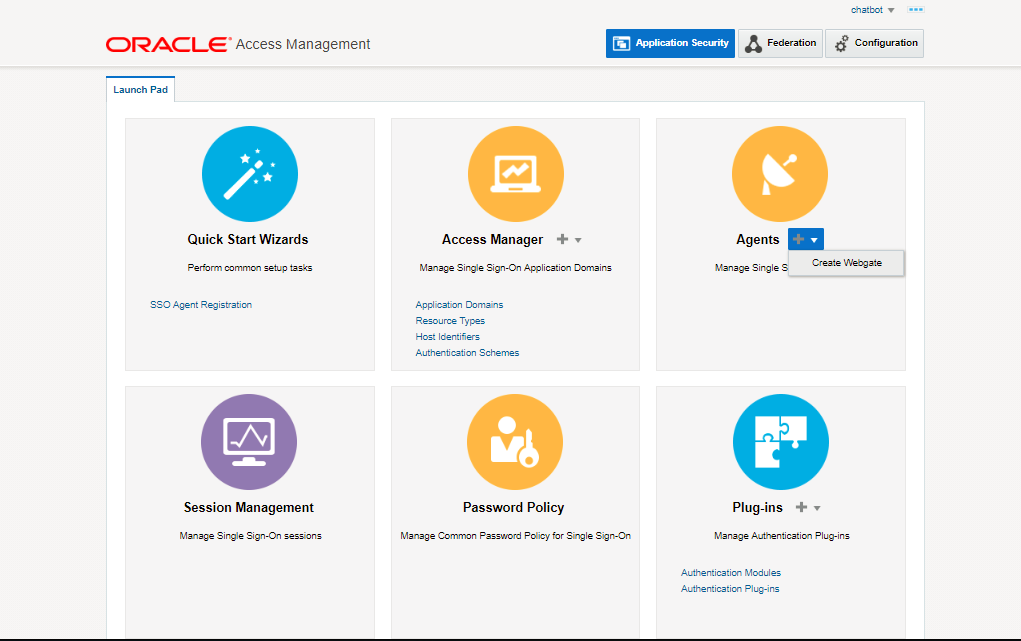
In the Agents block, Create Webgate.
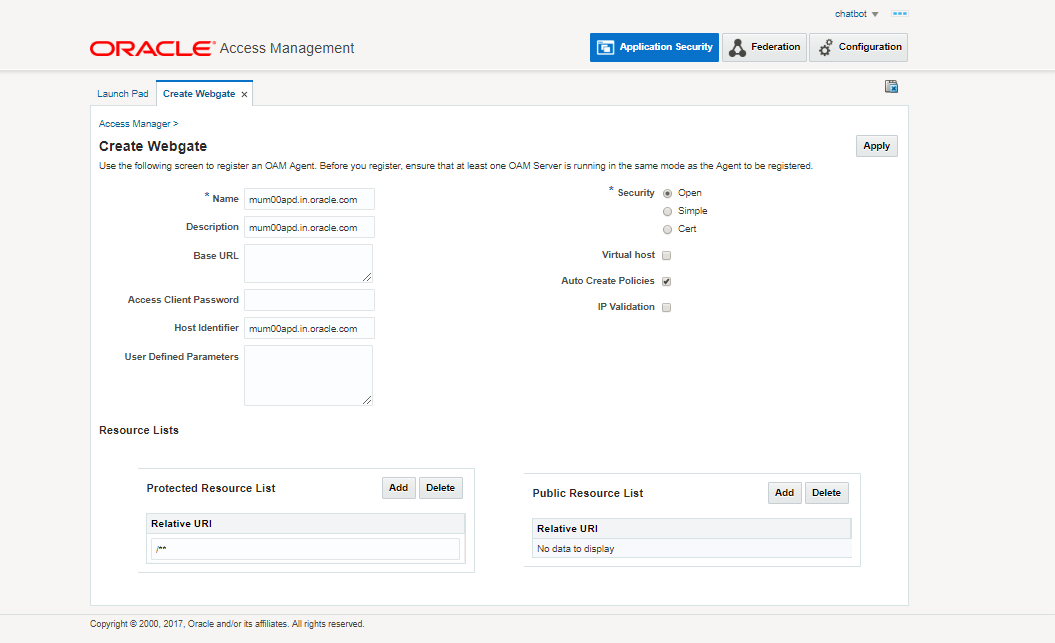
Enter the hostname in Name field
Click on Apply.
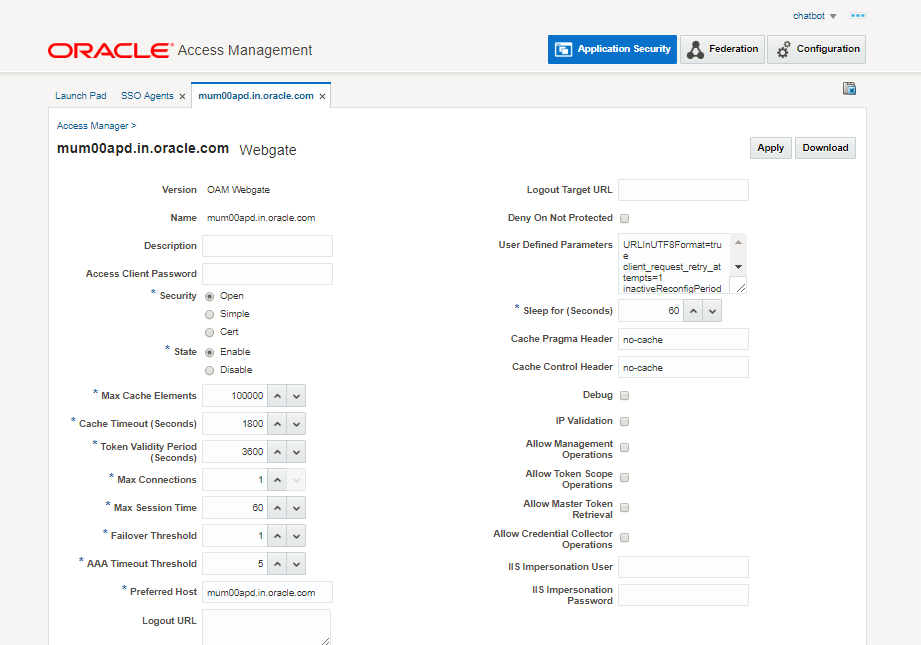
This creates the Webgate Agent for OAM. Download files for webgate by clicking the “Download” button. Extract below files from zip.
cwallet.sso
ObAccessClient.xml
The user should copy the files from the above mentioned location to the <WebTier_Instance_Home>/config/OHS/ohs1/webgate/config directory and restart OHS server instance.
Note: The hostname here will be the fully qualified hostname of the server where Webgate is installed.
Creating Custom Login Scheme
To add a Custom Login Page, go to Launch Pad on oamconsole.
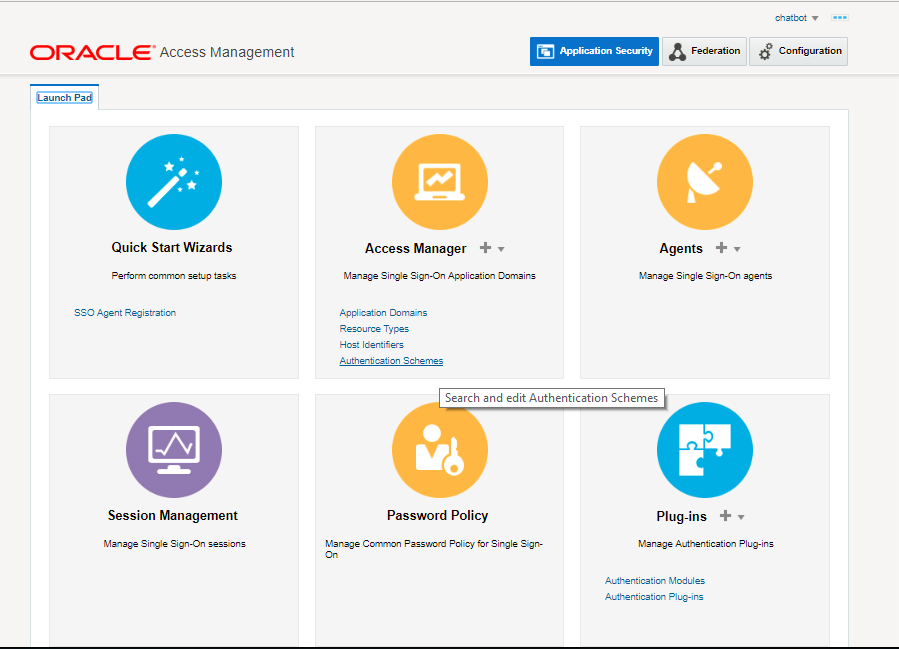
Click on Authentication Schemes from the Access Manager block.
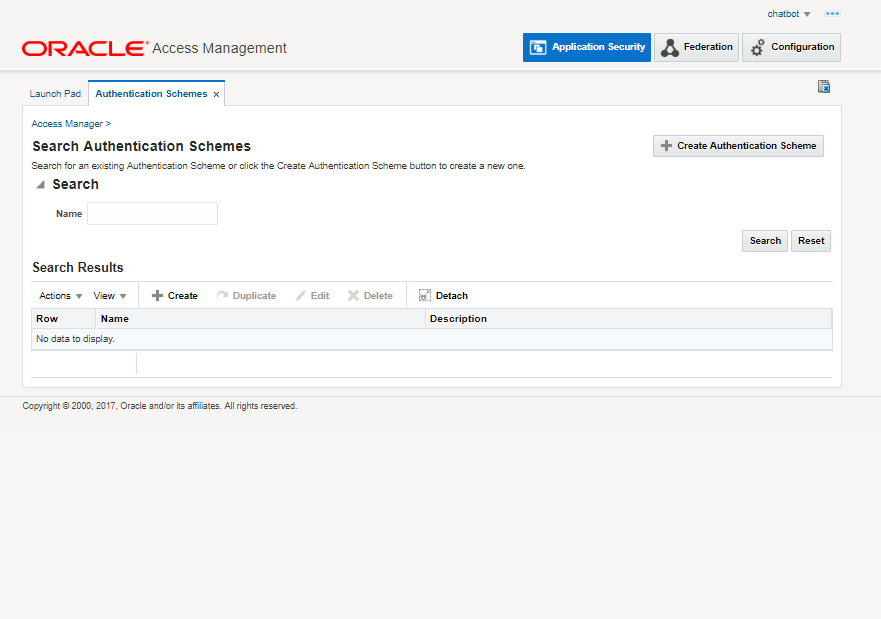
Click on Create Authentication Scheme.
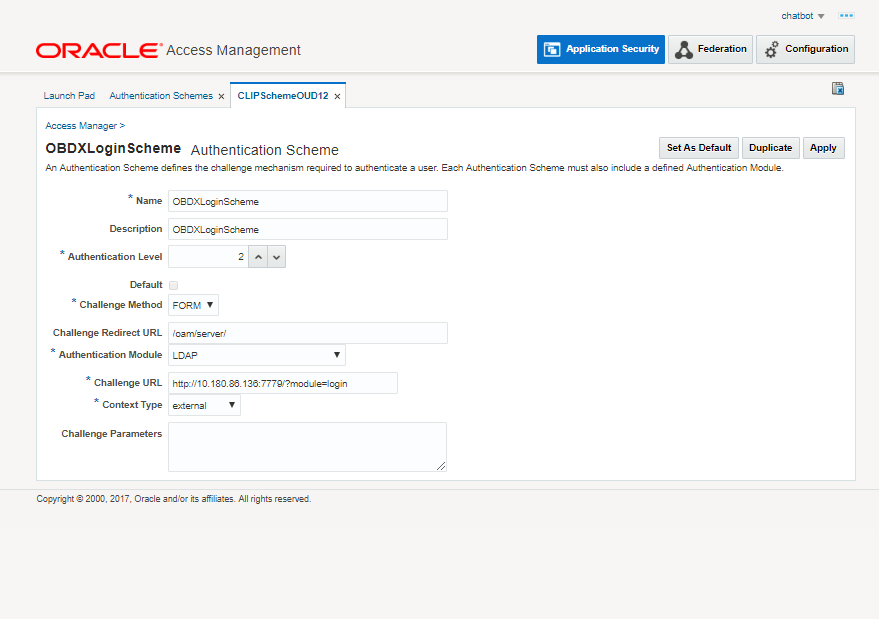
Specify the following details:
- Provide a name for the Scheme. E.g. OBDXLoginScheme
- Select the authentication level as 2.
- Choose the Challenge Method as FORM
- Enter the Challenge Re-direct URL. E.g. /oam/server
- Select the Authentication Module as LDAP
- Enter the Challenge URL which is the actual URL of the login page.
- Select the Context Type as External
Click on Apply to save the Scheme.
Manage Application Domain Resources
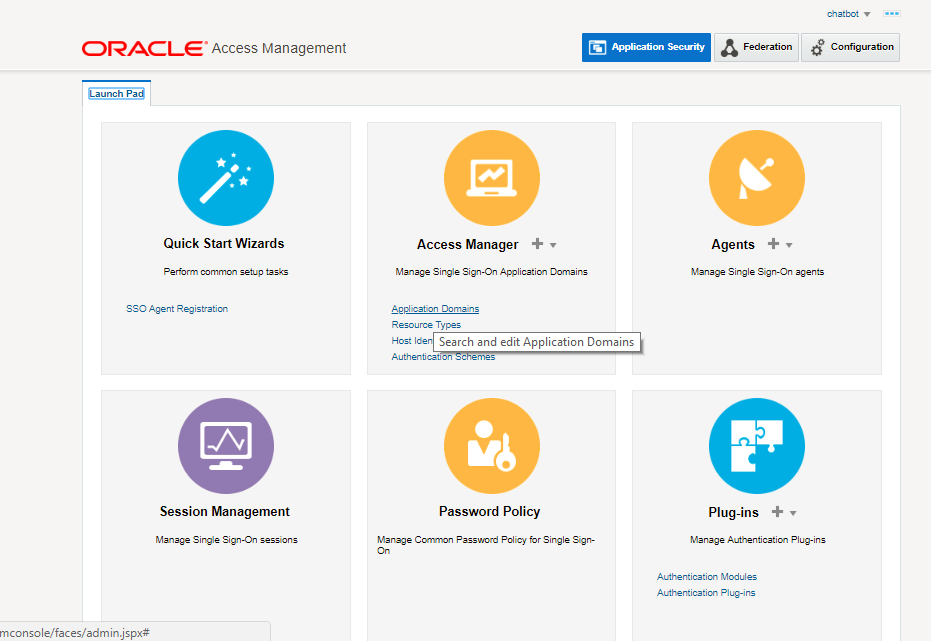
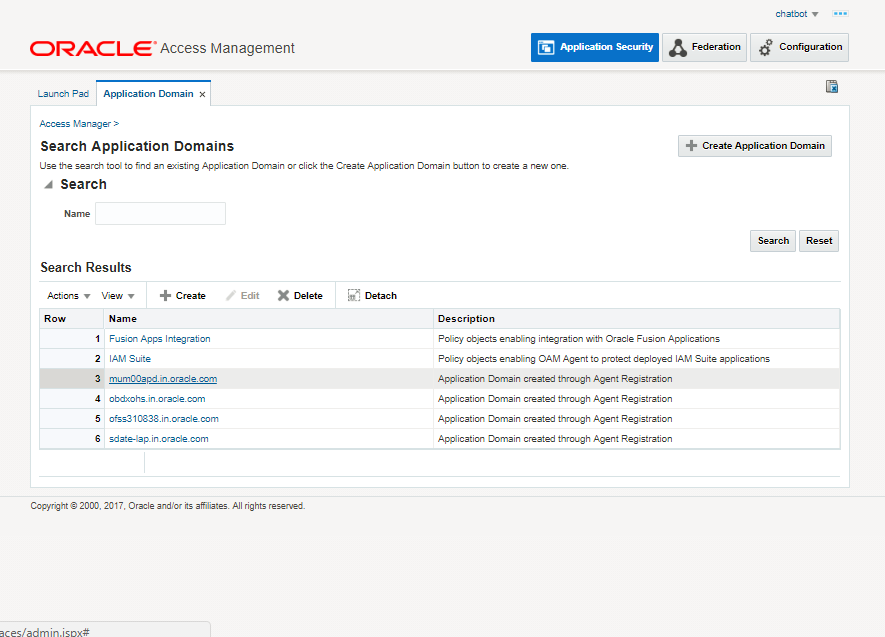
Go to Launch Pad and search for an application domain.
Click on Applications Domain in the Access Manager tab.
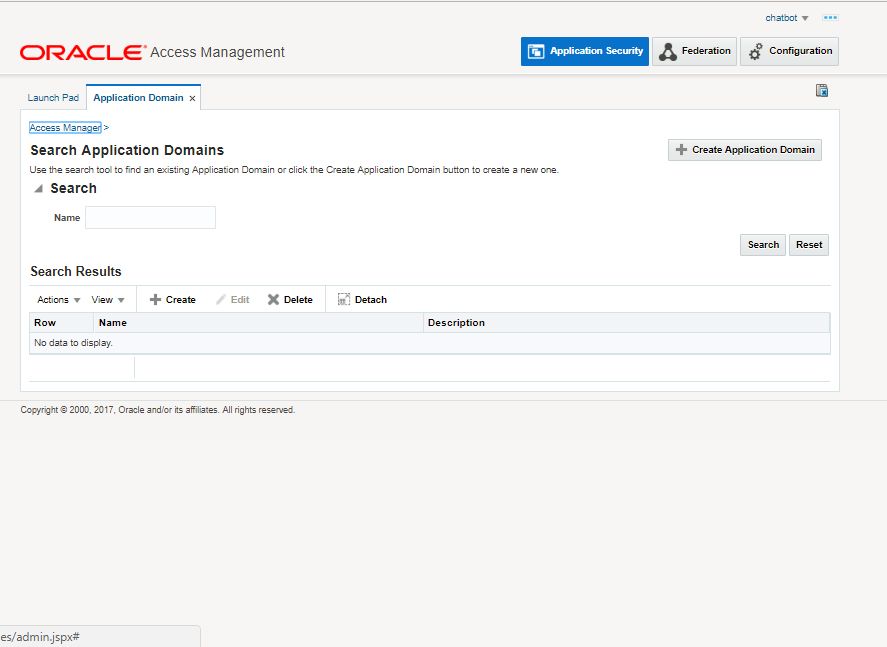
Click on Search
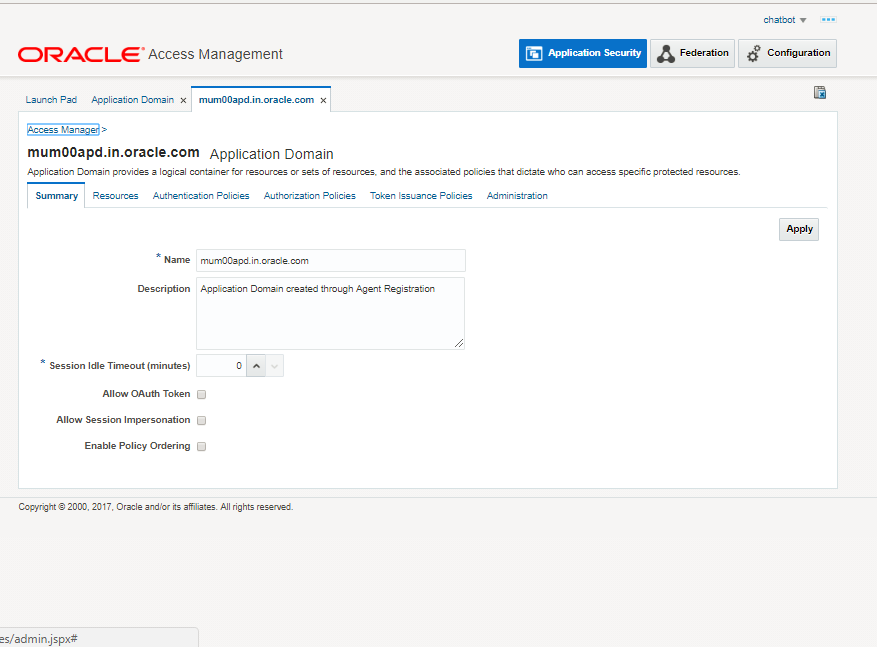
Click on the Domain Name you want to configure.
Click on the Resources Tab.
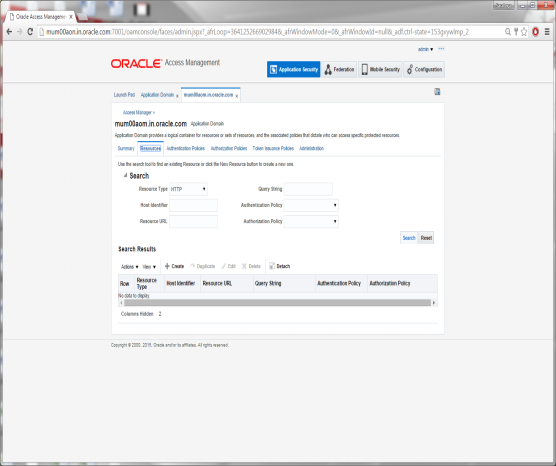
Click on Search.
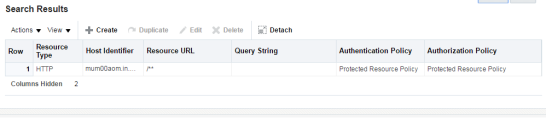
Search Results will show an entry for Resource URL as /** which is Protected.
Select the Resource entry and Click the Edit option.
Modify the values of Protection Level, Authentication & Authorization Policy as shown.
Click on Apply to save the changes.
Click on the Create Icon.
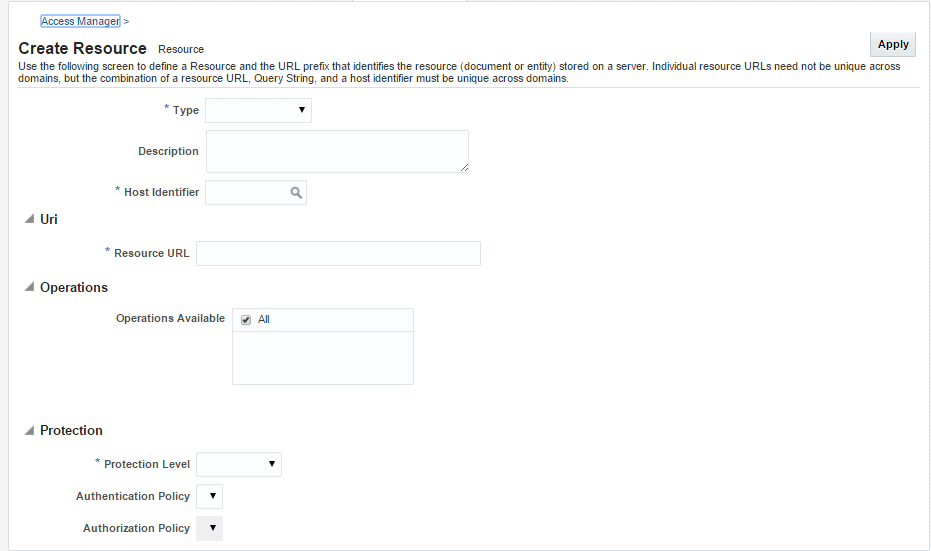
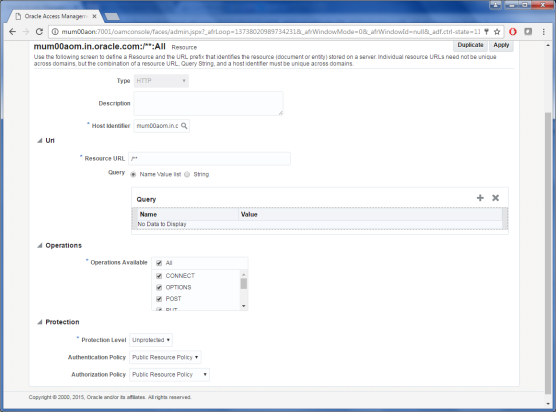
Specify the following values for each of the fields respectively:
- Type: The HTTP type is the default; it covers resources that are accessed using either the HTTP or HTTPS protocol. Policies that govern a particular resource apply to all operations.
Select Type HTTP
- Description: An optional unique description for this resource.
- Host Identifier: A list of host identifiers is available, which contains all identifiers that were defined as a shared component. You must search and choose a host identifier to assign this resource.
- Resource URL: The URL value must be expressed as a single relative URL string that represents a path component of a full URL. For example, /pages/*
- Operations: Select the required Operation from the table.
- Protection Level: Select the Protection Level from the drop-down as per the table.
- Authentication Policy: Select the required value from the drop-down.
- Authorization Policy: Select the required value from the drop-down.
Click on Apply to add the resource.
Perform the above steps to add the URLs listed in the table below:
|
Resource URLs |
Operations |
Protection Level |
Authentication Authorization Policy |
|---|---|---|---|
|
/** |
ALL |
Unprotected |
Public Resource Policy |
|
/pages/* |
ALL |
Protected |
Protected Resource Policy |
|
/oam/pages/consent.jsp |
ALL |
Protected |
Protected Resource Policy |
|
/digx/v1/locations/branches/* |
GET |
Excluded |
- |
|
/digx/v1/locations/atms/* |
GET |
Excluded |
- |
|
/digx/v1/locations* |
GET |
Excluded |
- |
|
/digx/v1/mobileClient/verify |
ALL |
Excluded |
- |
|
/.../*.js |
ALL |
Excluded |
- |
|
/oauth2/rest/approval |
ALL |
Protected |
Protected Resource Policy |
|
/oauth2/rest/** |
ALL |
Excluded |
- |
|
/oam/** |
ALL |
Excluded |
- |
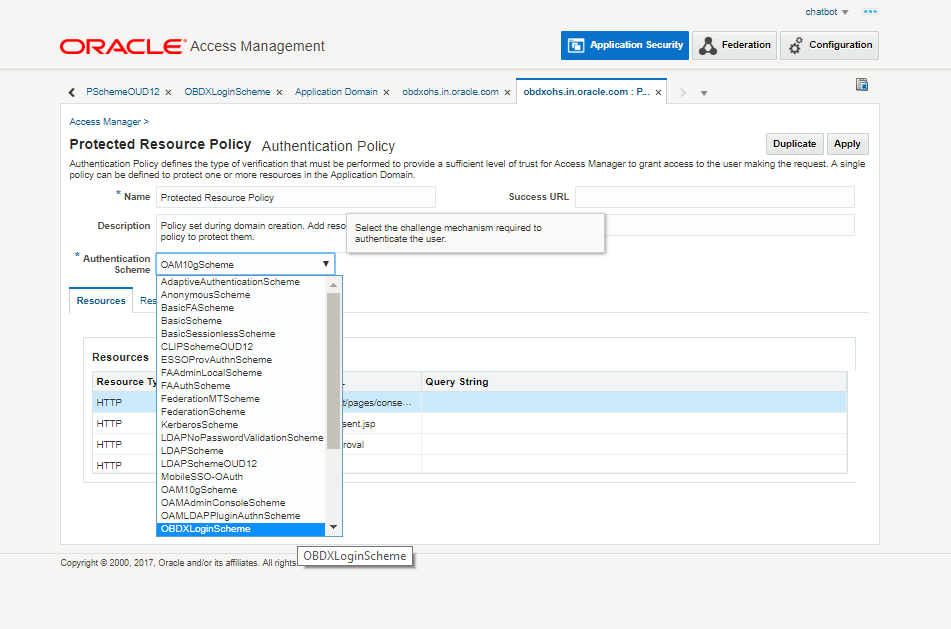
Mapping Login Scheme to Application Domain
Navigate to Authentication Policy Tab > Protected Resource Policy > Select the scheme > Apply
Select the entry UserIdentityStore1, under OAM ID Stores and Click the Edit option.
REST API configurations for Mobile Banking (2-Legged OAuth Flows)
OBDX Mobile application user OAuth for API Based login. Clients are defined in OAM and the same are mapped to access points in OBDX.
To define OAuth Clients in OAM, invoke below REST APIs as OAM does not provide a screen to define the OAuth client. OAM Admin console credentials are required to invoke these APIs.
Domain Creation –
http://mum00aon.in.oracle.com:8001/oam/services/rest/ssa/api/v1/oauthpolicyadmin/oauthidentitydomain
Headers –
Authorization: Basic <Base64 of uid:pwd>
Content-Type: application/json
Mobile App
{"name": " OBDXMobileAppDomain ",
"tokenSettings": [{"tokenType": "ACCESS_TOKEN",
"tokenExpiry": 300,
"lifeCycleEnabled": true,
"refreshTokenEnabled": true,
"refreshTokenExpiry": 864000,
"refreshTokenLifeCycleEnabled": true
}]
}
Siri
{"name": " OBDXSiriDomain ",
"tokenSettings": [{"tokenType": "ACCESS_TOKEN",
"tokenExpiry": 300,
"lifeCycleEnabled": true,
"refreshTokenEnabled": true,
"refreshTokenExpiry": 864000,
"refreshTokenLifeCycleEnabled": true
}]
}
Wearable
{"name": " OBDXWearDomain",
"tokenSettings": [{"tokenType": "ACCESS_TOKEN",
"tokenExpiry": 300,
"lifeCycleEnabled": true,
"refreshTokenEnabled": true,
"refreshTokenExpiry": 864000,
"refreshTokenLifeCycleEnabled": true
}]
}
Snapshot
{"name": "OBDXSnapshotDomain",
"tokenSettings": [{"tokenType": "ACCESS_TOKEN",
"tokenExpiry": 300,
"lifeCycleEnabled": true,
"refreshTokenEnabled": true,
"refreshTokenExpiry": 2592000,
"refreshTokenLifeCycleEnabled": true
}]
}
Resource Server:
http://mum00aon.in.oracle.com:8001/oam/services/rest/ssa/api/v1/oauthpolicyadmin/application
Headers –
Authorization: Basic <Base64 of uid:pwd>
Content-Type: application/json
Mobile App
{"name": "OBDXMobileAppResServer",
"description": "Resource Server for Mobile",
"scopes": [{"scopeName": "OBDXLoginScope",
"description": "OBDXLoginScope"
},
{"scopeName": "ValidateDeviceScope",
"description": "ValidateDeviceScope"
}],
"tokenAttributes": [],
"idDomain": "OBDXMobileAppDomain",
"audienceClaim": {}}
Siri
{"name": "OBDXSiriResServer",
"description": "Resource Servcer for Siri",
"scopes": [{"scopeName": "ValidateDeviceScope",
"description": "ValidateDeviceScope"
}],
"tokenAttributes": [],
"idDomain": "OBDXSiriDomain",
"audienceClaim": {}}
Wearables
{"name": "OBDXWearResServer",
"description": "Resource Servcer for Wearables",
"scopes": [{"scopeName": "ValidateDeviceScope",
"description": "ValidateDeviceScope"
}],
"tokenAttributes": [],
"idDomain": "OBDXWearDomain",
"audienceClaim": {}}
Snapshot
{"name": "OBDXSnapshotResServer",
"description": "Resource Servcer for Snapshot",
"scopes": [{"scopeName": "ValidateDeviceScope",
"description": "ValidateDeviceScope"
}],
"tokenAttributes": [],
"idDomain": "OBDXSnapshotDomain",
"audienceClaim": {}}
Clients:
http://mum00aon.in.oracle.com:8001/ /oam/services/rest/ssa/api/v1/oauthpolicyadmin/client
Headers –
Authorization: Basic <Base64 of uid:pwd>
Content-Type: application/json
Mobile App
{"attributes": [],
"secret": "welcome1",
"id": "2d79e939e0424mobapp8e5fab436fb5581",
"scopes": ["OBDXMobileAppResServer.ValidateDeviceScope", "OBDXMobileAppResServer.OBDXLoginScope"],
"clientType": "CONFIDENTIAL_CLIENT",
"idDomain": "OBDXMobileAppDomain",
"description": "OBDXMobileAppDomain",
"name": "OBDXMobileAppClient",
"grantTypes": ["PASSWORD", "REFRESH_TOKEN"],
"defaultScope": "OBDXMobileAppResServer.ValidateDeviceScope",
"redirectURIs": [{"url": "http://localhost:8080/Sample.jsp",
"isHttps": false
}]
}
Siri
{"attributes": [],
"secret": "welcome1",
"id": "2d79e939e0424sirichat8e5ab43fb5591",
"scopes": ["OBDXSiriResServer.ValidateDeviceScope"],
"clientType": "CONFIDENTIAL_CLIENT",
"idDomain": "OBDXSiriDomain",
"description": "OBDXSiriDomain",
"name": "OBDXSiriClient",
"grantTypes": ["PASSWORD", "REFRESH_TOKEN"],
"defaultScope": "OBDXSiriResServer.ValidateDeviceScope",
"redirectURIs": [{"url": "http://localhost:8080/Sample.jsp",
"isHttps": false
}]
}
Wearables
{"attributes": [],
"secret": "welcome1",
"id": "2d79e939e0424wearable8e5ab43fb5591",
"scopes": ["OBDXWearResServer.ValidateDeviceScope"],
"clientType": "CONFIDENTIAL_CLIENT",
"idDomain": "OBDXWearDomain",
"description": "OBDXWearDomain",
"name": "OBDXWearClient",
"grantTypes": ["PASSWORD", "REFRESH_TOKEN"],
"defaultScope": "OBDXWearResServer.ValidateDeviceScope",
"redirectURIs": [{"url": "http://localhost:8080/Sample.jsp",
"isHttps": false
}]
}
Snapshot
{"attributes": [],
"secret": "welcome1",
"id": "2d79e939e0424snapshot8e5ab43fb5591",
"scopes": ["OBDXSnapshotResServer.ValidateDeviceScope"],
"clientType": "CONFIDENTIAL_CLIENT",
"idDomain": "OBDXSnapshotDomain",
"description": "OBDXSnapshotDomain",
"name": "OBDXSnapshotClient",
"grantTypes": ["PASSWORD", "REFRESH_TOKEN"],
"defaultScope": "OBDXSnapshotResServer.ValidateDeviceScope",
"redirectURIs": [{"url": "http://localhost:8080/Sample.jsp",
"isHttps": false
}]}
Creating the Attributes, Object Class, Users, Groups and Adding Optional Attributes on LDAP Server
To create Groups
- Copy the “groups.ldif” file from <OBDX BASE Installer zip>installables/oud directory to a location on the server where OUD is installed and switch to the following directory:
cd <Oracle_Home>/Oracle_OUD1/bin
- Now, execute the below command:
./ldapmodify -h localhost -p <ldap_port> -D "ldap_user" -w <ldap_password> -a -f <file_location>/usergroup.ldif
OR (using SSL)
./ldapmodify -h localhost -p <ldap_port> -D "ldap_user" -w <ldap_password> -a -f <file_location>/usergroup.ldif --useSSL
- Login to OUDSM Console. E.g. http://<hostname>:<port>/oudsm and under the Data Browser tab check if the groups are created.
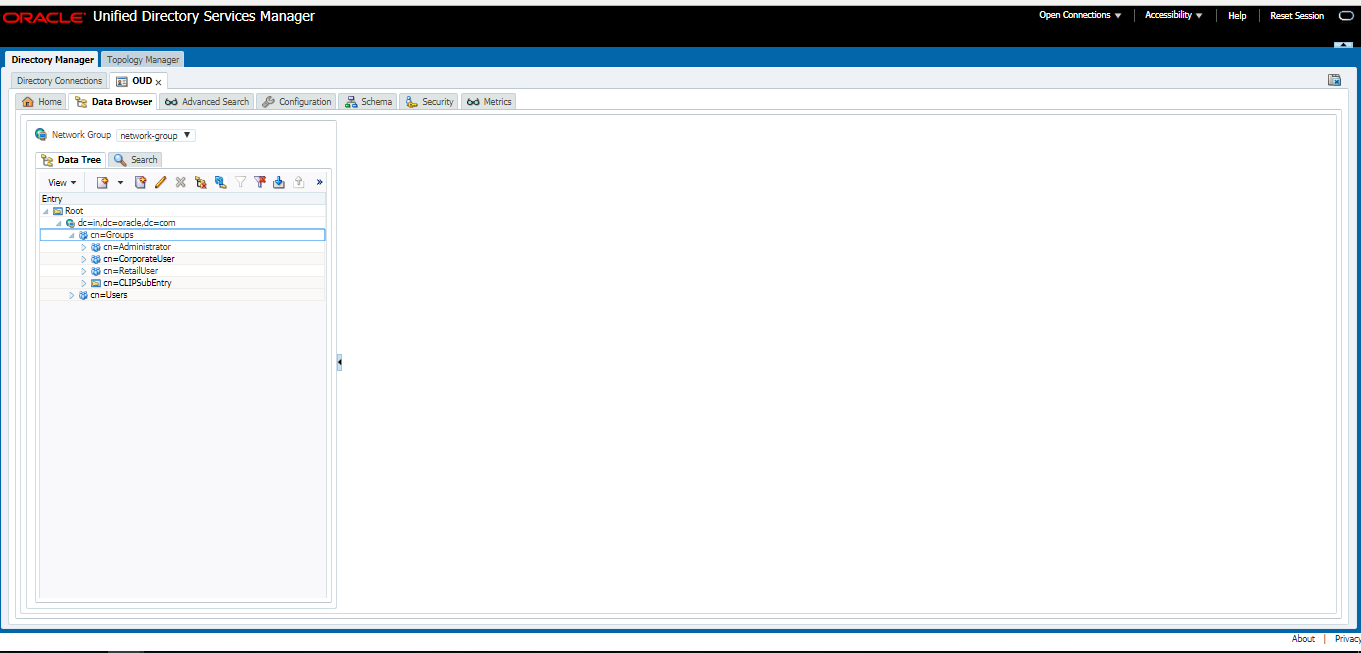
To create User and mapping it to the Group
- Login to ODSM Console using required credentials. Post login you should see below screen.
E.g. http://<hostname>:<port>/oudsm.
- Under the Data Browser tab, click on the Add icon
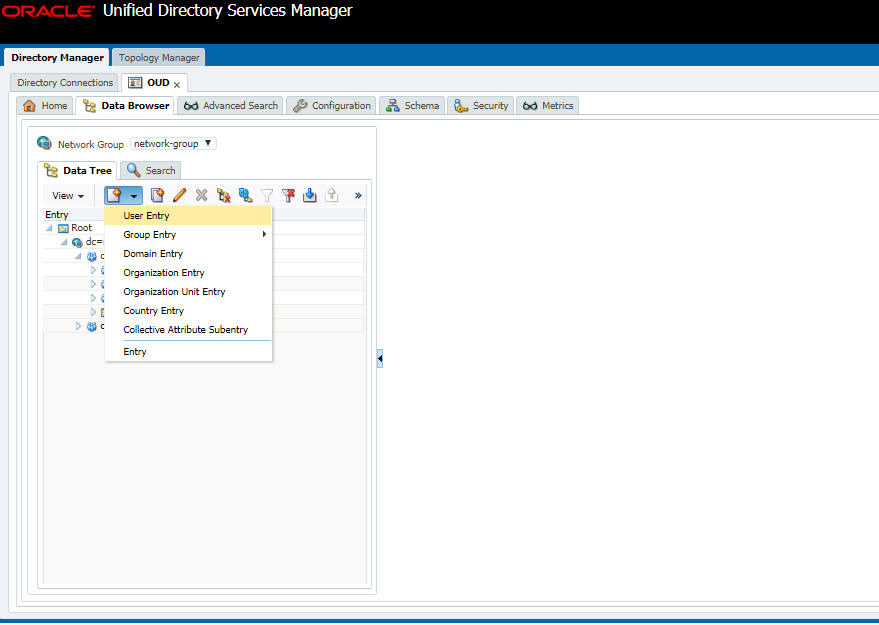
- Select User Entry from the list.
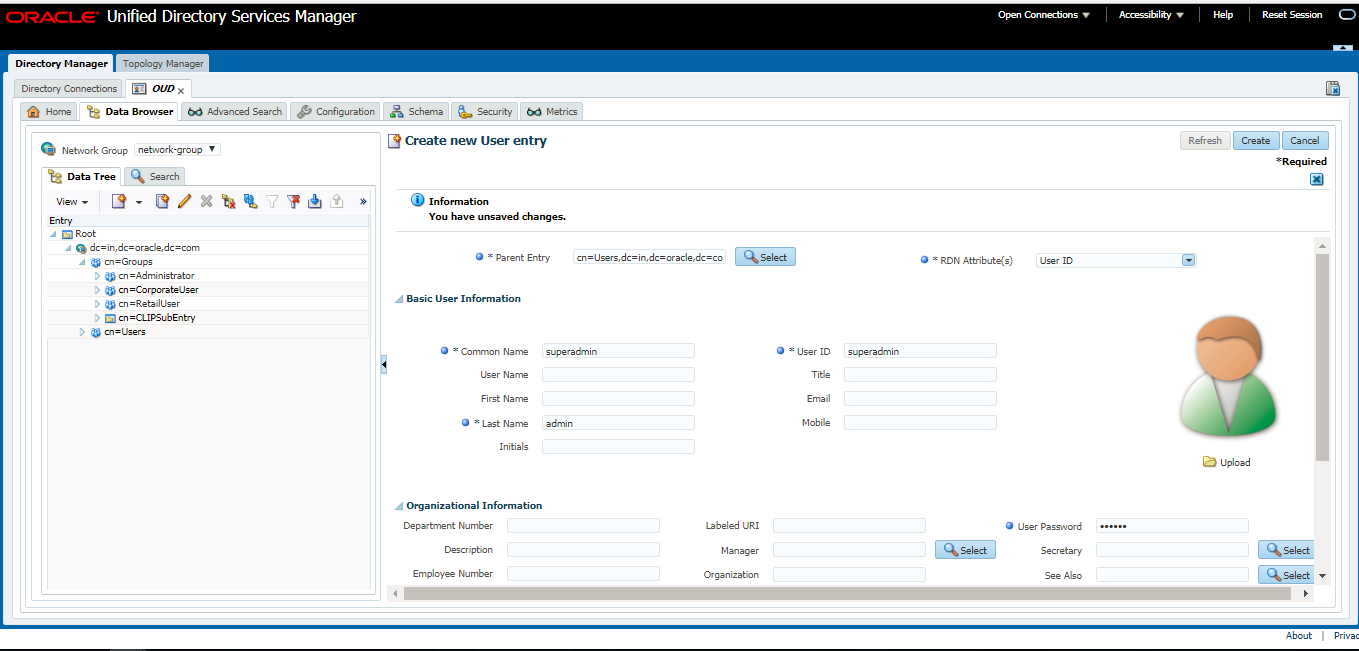
- Now, uncheck Common Name from the RDN Attributes drop-down list.
- And, Check the User ID Attribute check box.
- Add the values in the mandatory fields Common Name, Last Name, User ID and User Password.
- Click on Create and the user entry will be created.
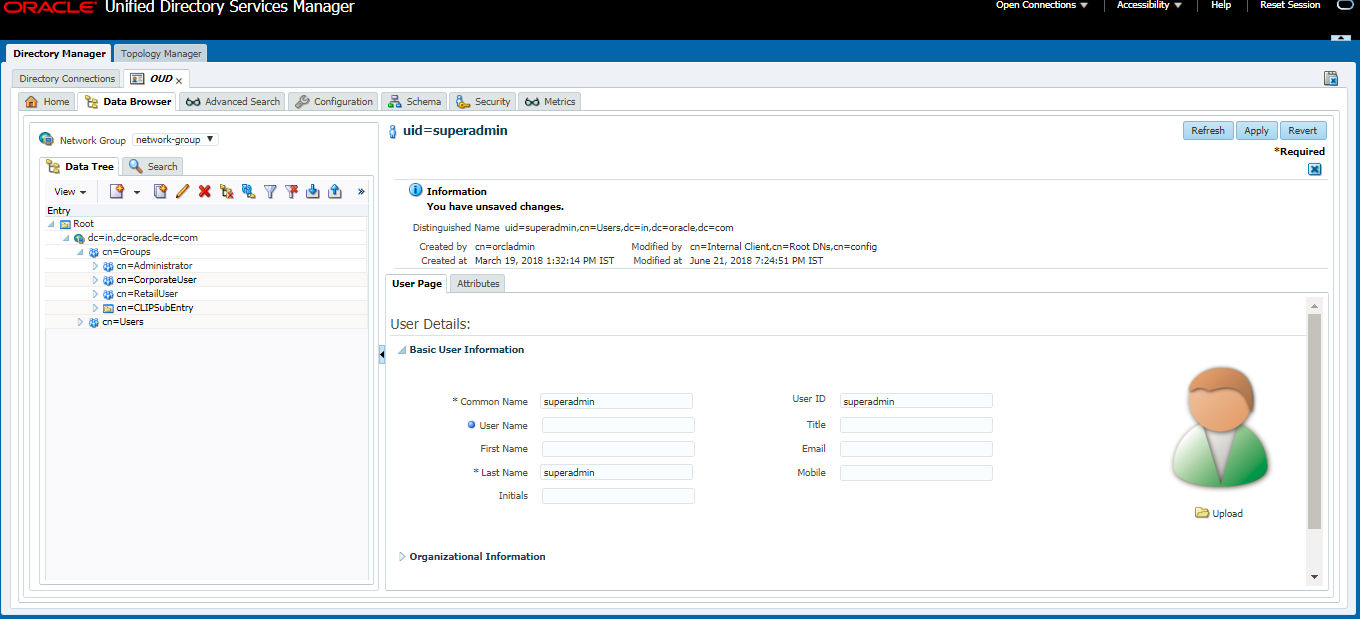
- Now, expand the Groups tab.
- Select Administrator Group.
- Expand Member Information and click on Add button.
- Enter the entry of the user created in the previous steps.
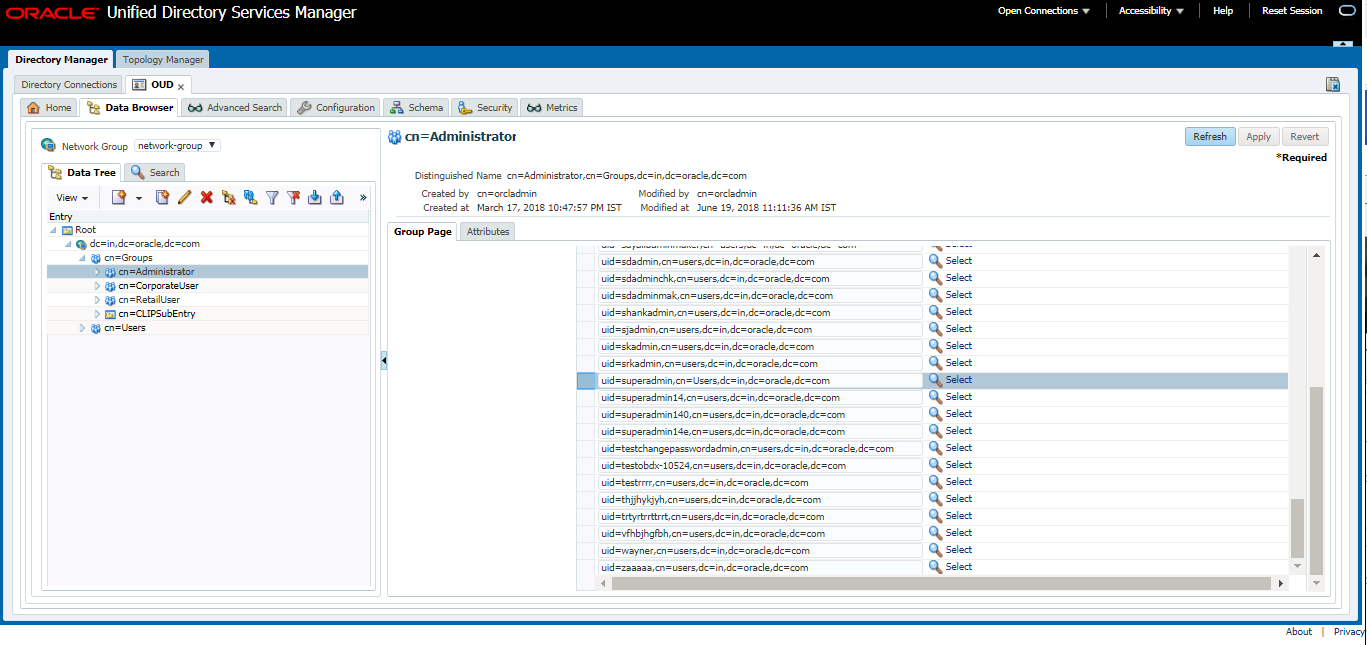
- Click on Apply to save the changes.
Oracle Business Intelligence Publisher Installation
To install Oracle Business Intelligence Installation click here.