ORIGINATION WEB SERVICE USERNAME TOKEN CONFIGURATION GUIDE
Anonymous user configuration
- Insert/ Update security policy to be used in the field in Anonymous Security Policy at Day1 (defaulted to “oracle/wss_username_token_client_policy”)
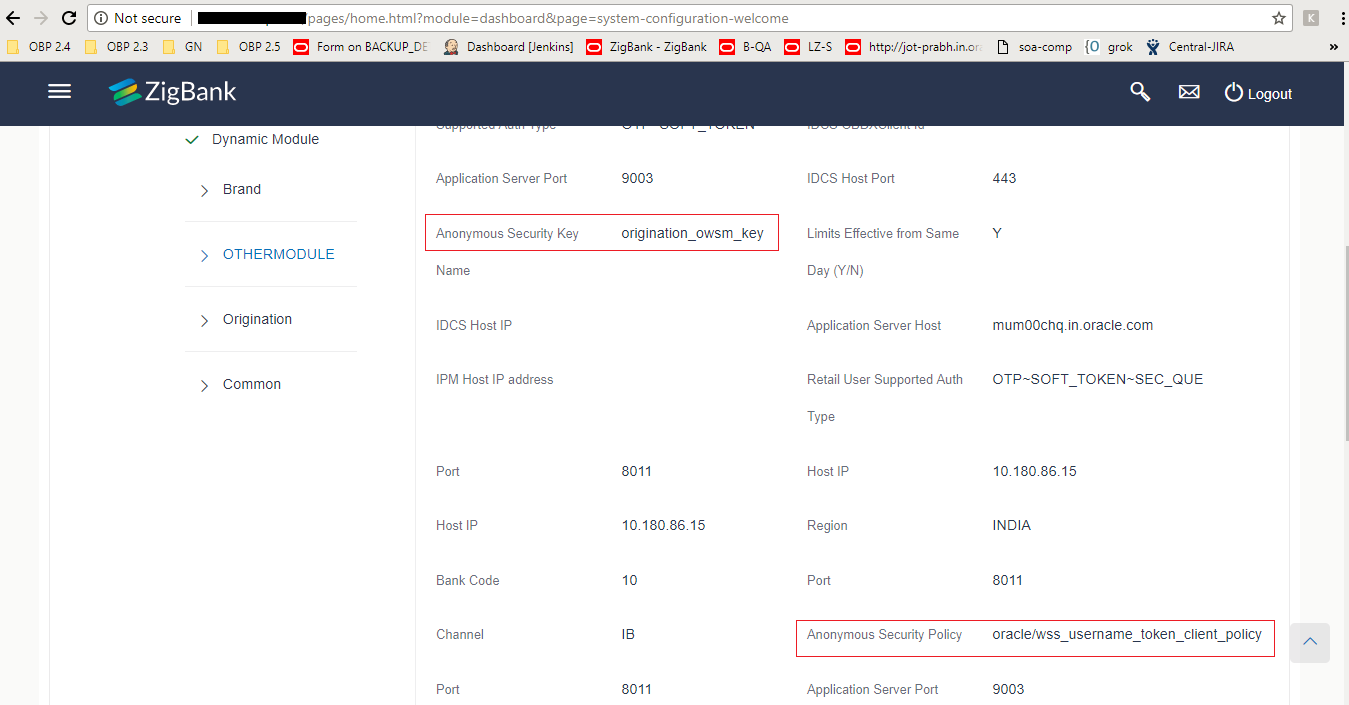
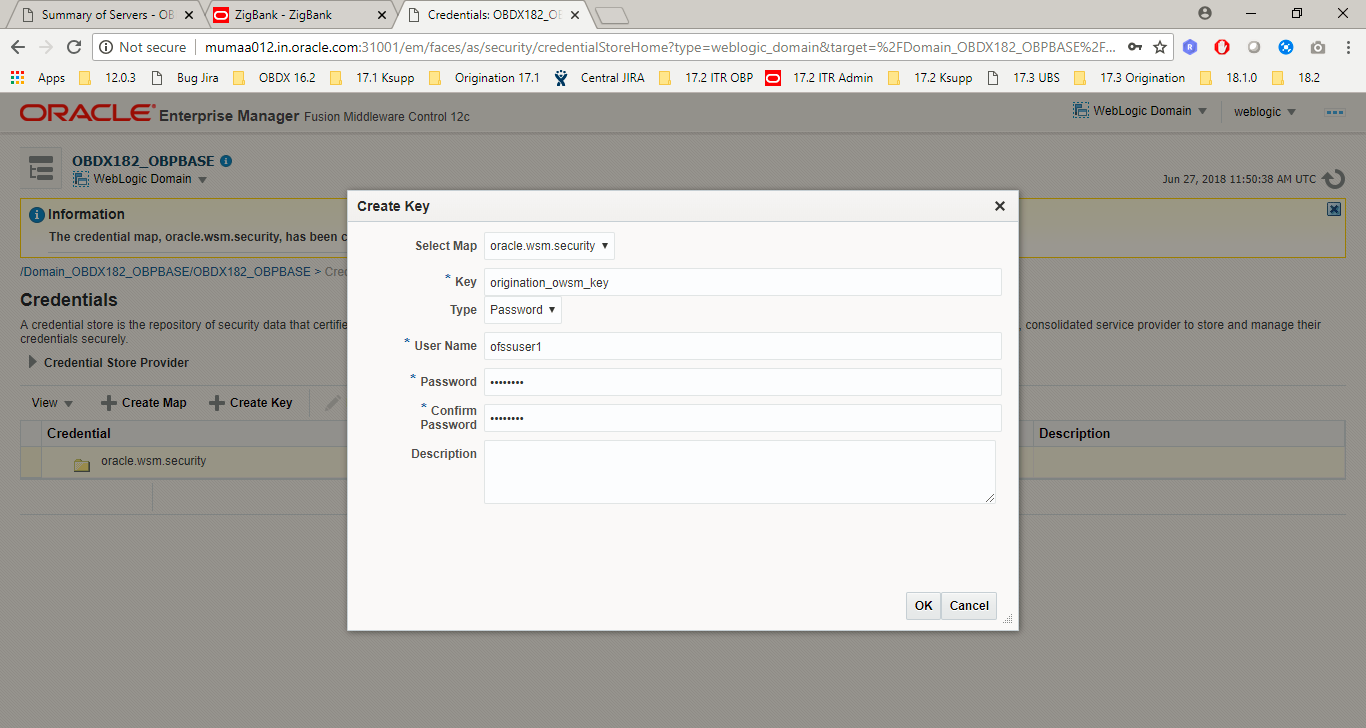
- Insert/ Update security policy key to be used in the field in Anonymous Security Key at Day1 (defaulted to “origination_owsm_key”)
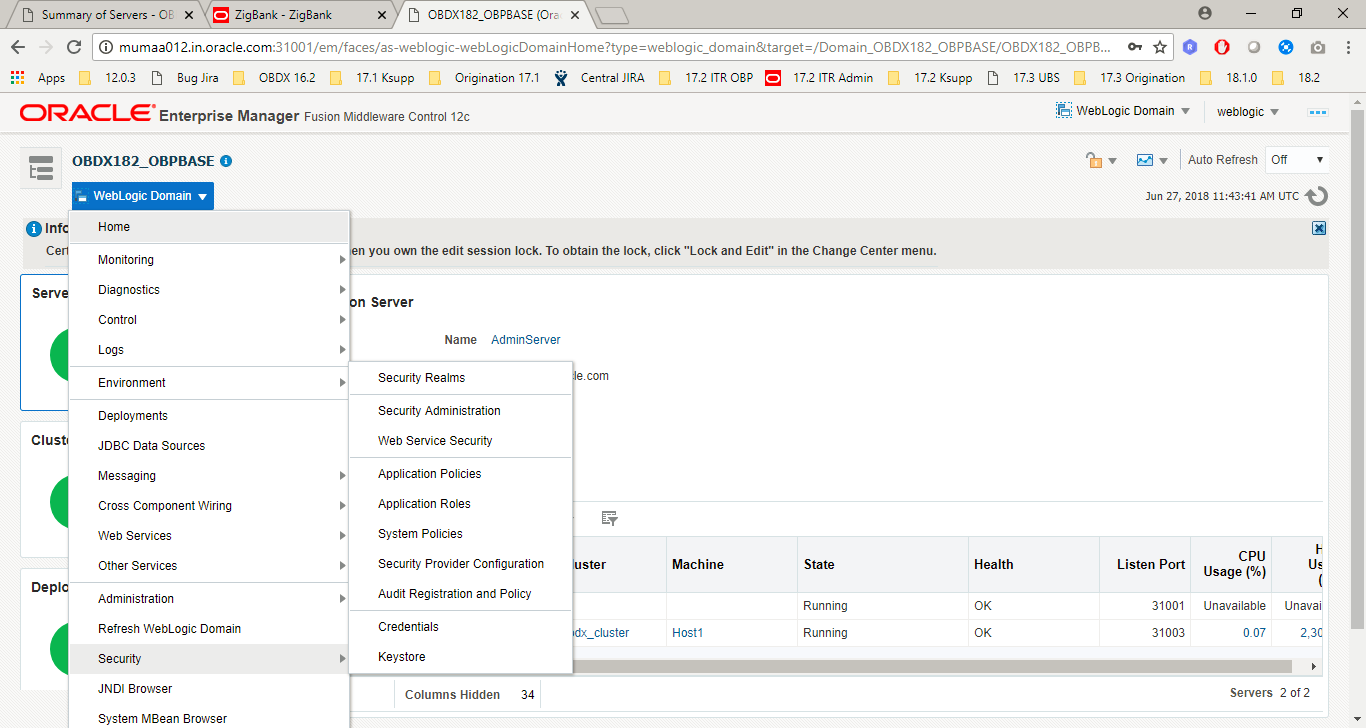
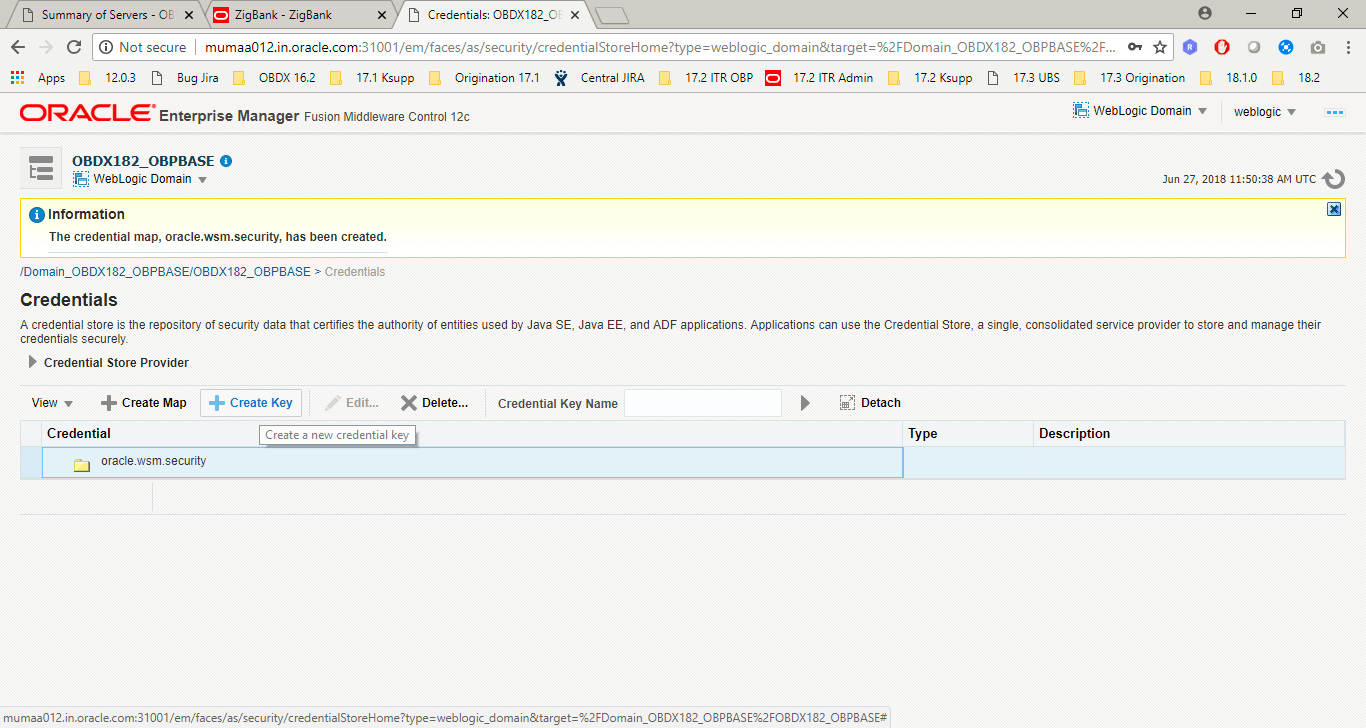
Name should match with credential key stored inside the credential store repository. - Create a map named “oracle.wsm.security” in credential store provider.
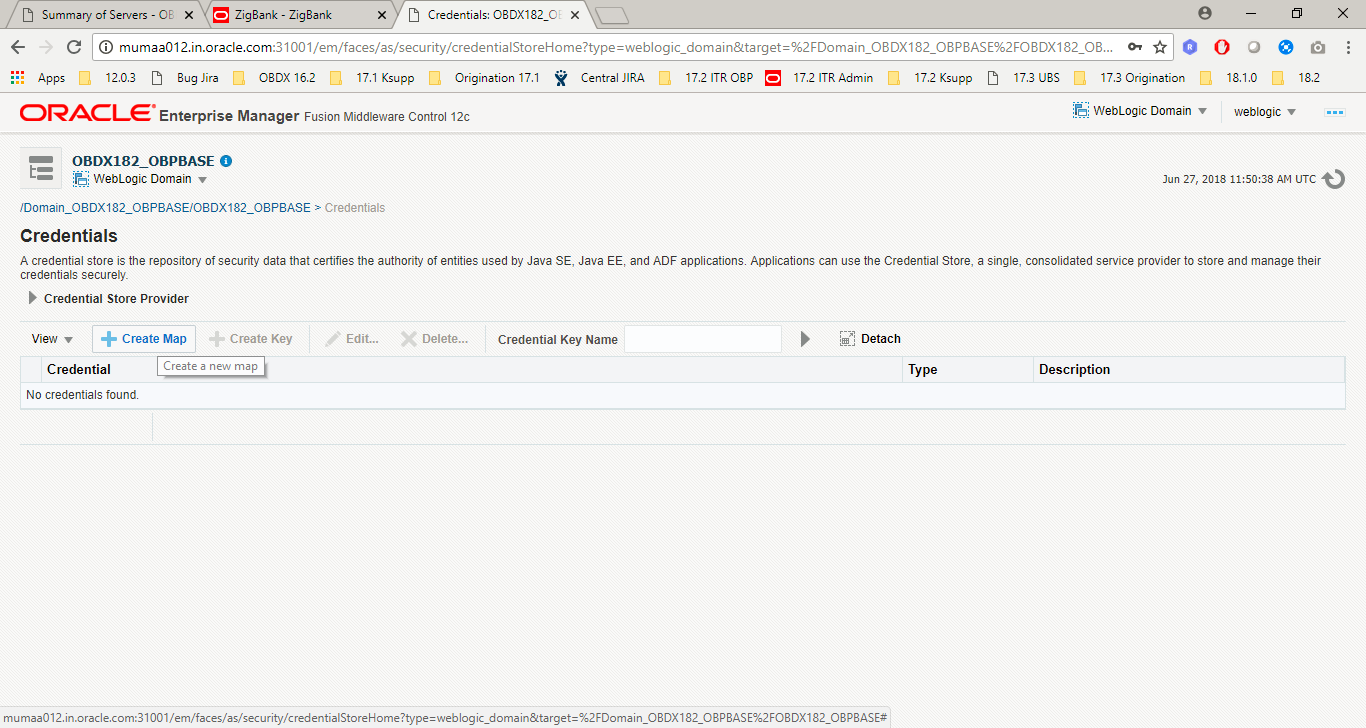
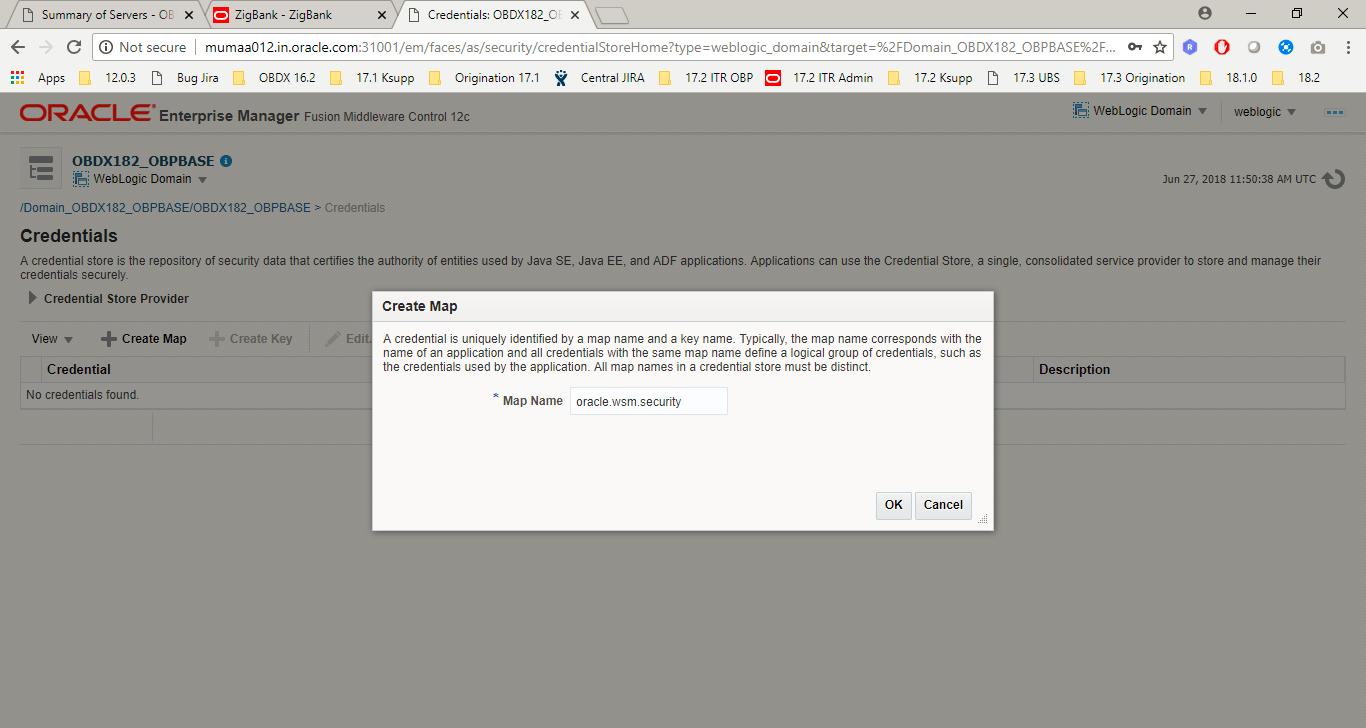
- Create credential key and provide username & password which will be used for authentication and authorization at OBP.
Logged-In User Configuration
- Insert a credentials entry for the connector.
- Update the connector name for the logged-in user.
- Update security policy of logged-in user from saml token to user token policy
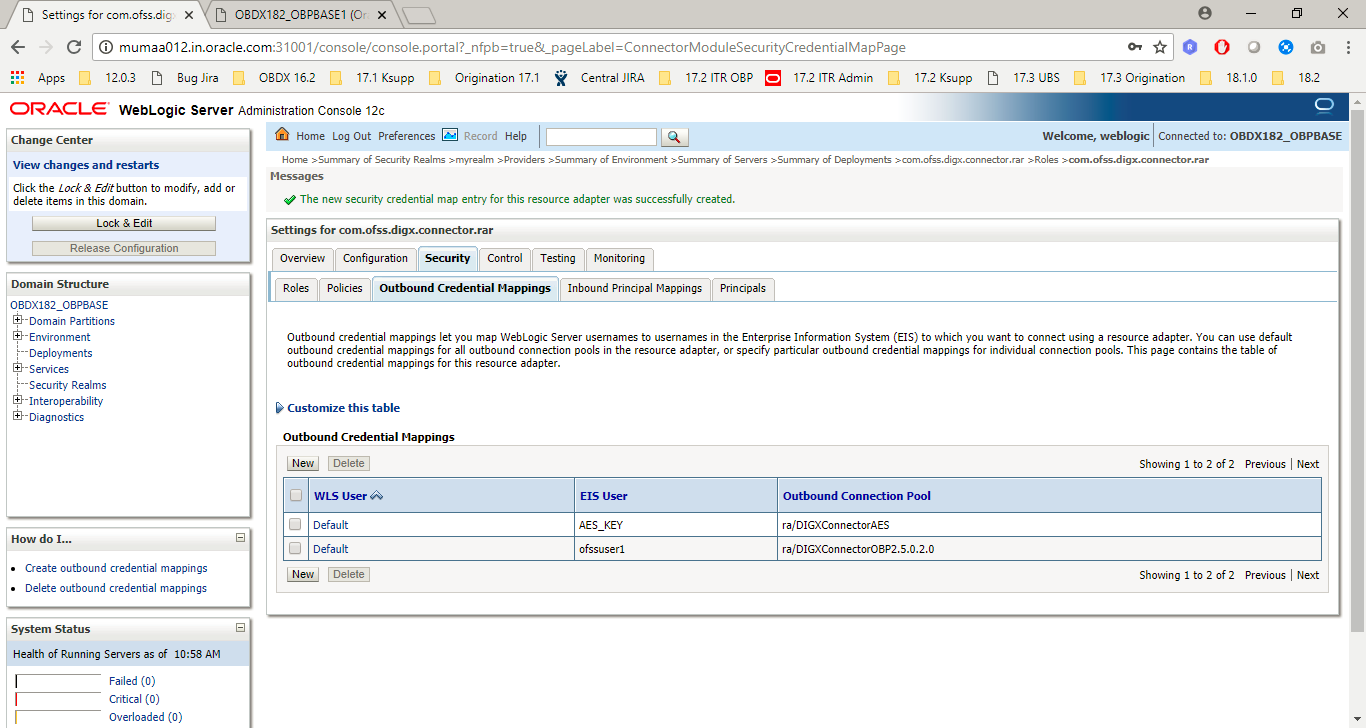
- Create a new “Outbound Credentials Mapping” in the connector (com.ofss.digx.app.connector.ear) ear and create a default user (use user id and credentials as provided by OBP team) for the mapping in the security tab. Managed server restart is required after these changes.
- Login into Weblogic console.
- Click on Deployments.
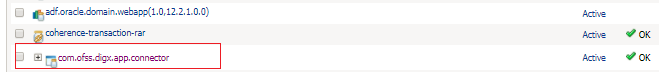
- Expand by clicking ‘+’ icon present in front of com.ofss.digx.app.connector application as shown below.
Insert into DIGX_FW_CONFIG_ALL_B ( PROP_ID, CATEGORY_ID, PROP_VALUE, FACTORY_SHIPPED_FLAG, PROP_COMMENTS,SUMMARY_TEXT, CREATED_BY, CREATION_DATE, LAST_UPDATED_BY, LAST_UPDATED_DATE, OBJECT_STATUS, OBJECT_VERSION_NUMBER, EDITABLE,CATEGORY_DESCRIPTION ) values ( 'OBP![]() Oracle Banking Platform_RA_JNDIKEY', 'CredentialConnector', 'ra/DIGXConnectorOBP', 'N', 'RA Connector for OBP', 'RA Connector for OBP', 'ofssuser', sysdate, 'ofssuser', sysdate, 'Y', 1, 'N', '1');
Oracle Banking Platform_RA_JNDIKEY', 'CredentialConnector', 'ra/DIGXConnectorOBP', 'N', 'RA Connector for OBP', 'RA Connector for OBP', 'ofssuser', sysdate, 'ofssuser', sysdate, 'Y', 1, 'N', '1');
update DIGX_FW_CONFIG_OUT_WS_CFG_B set HTTP_BASIC_AUTH_CONNECTOR='OBP' where SECURITY_POLICY='oracle/wss10_saml_token_client_policy';
update DIGX_FW_CONFIG_OUT_WS_CFG_B set SECURITY_POLICY='oracle/wss_username_token_client_policy' where SECURITY_POLICY='oracle/wss10_saml_token_client_policy';
update DIGX_FW_CONFIG_OUT_WS_CFG_B set SECURITY_POLICY='oracle/wss_username_token_client_policy' where SECURITY_POLICY='oracle/wss10_saml_token_client_policy';
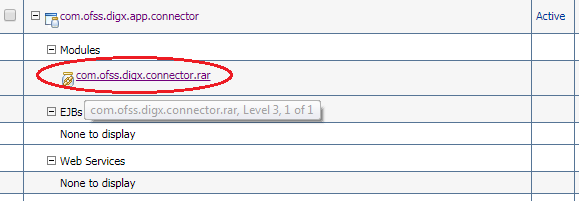
- Click com.ofss.digx.connector.rar as shown below.
- Click On “configuration” tab as shown in figure.
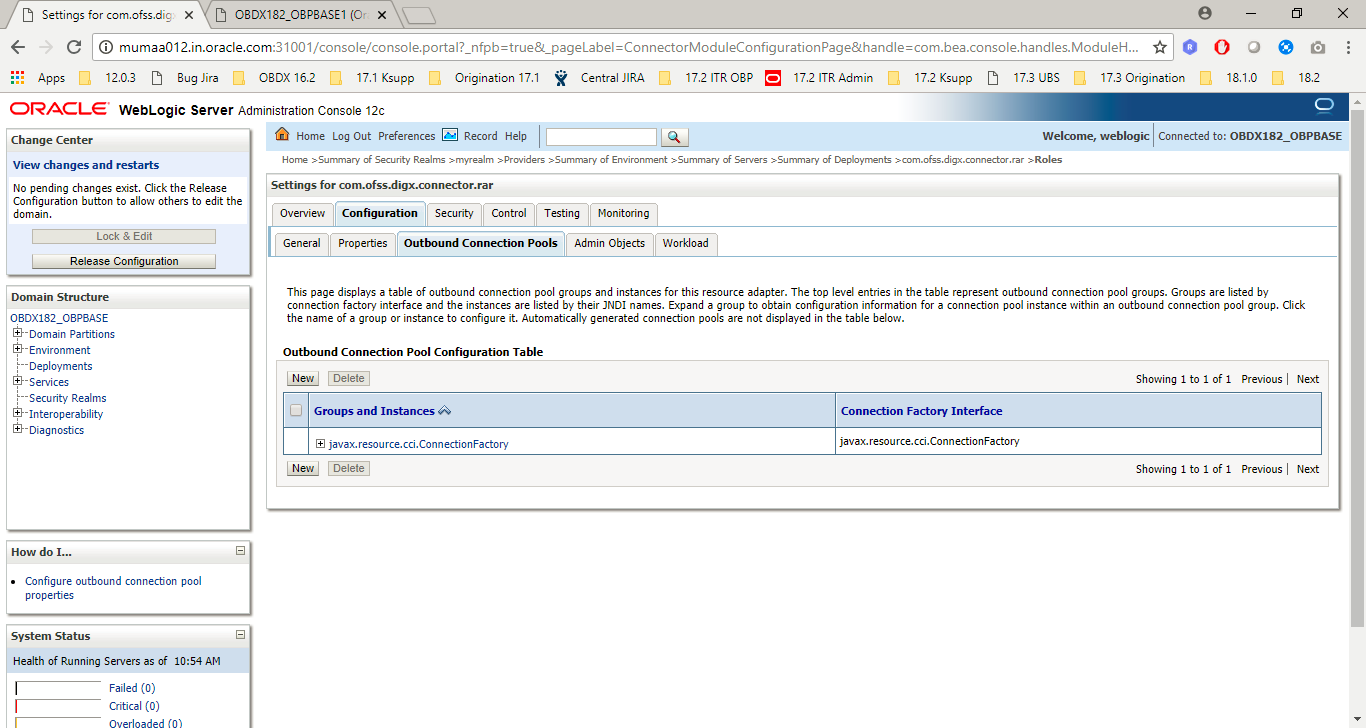
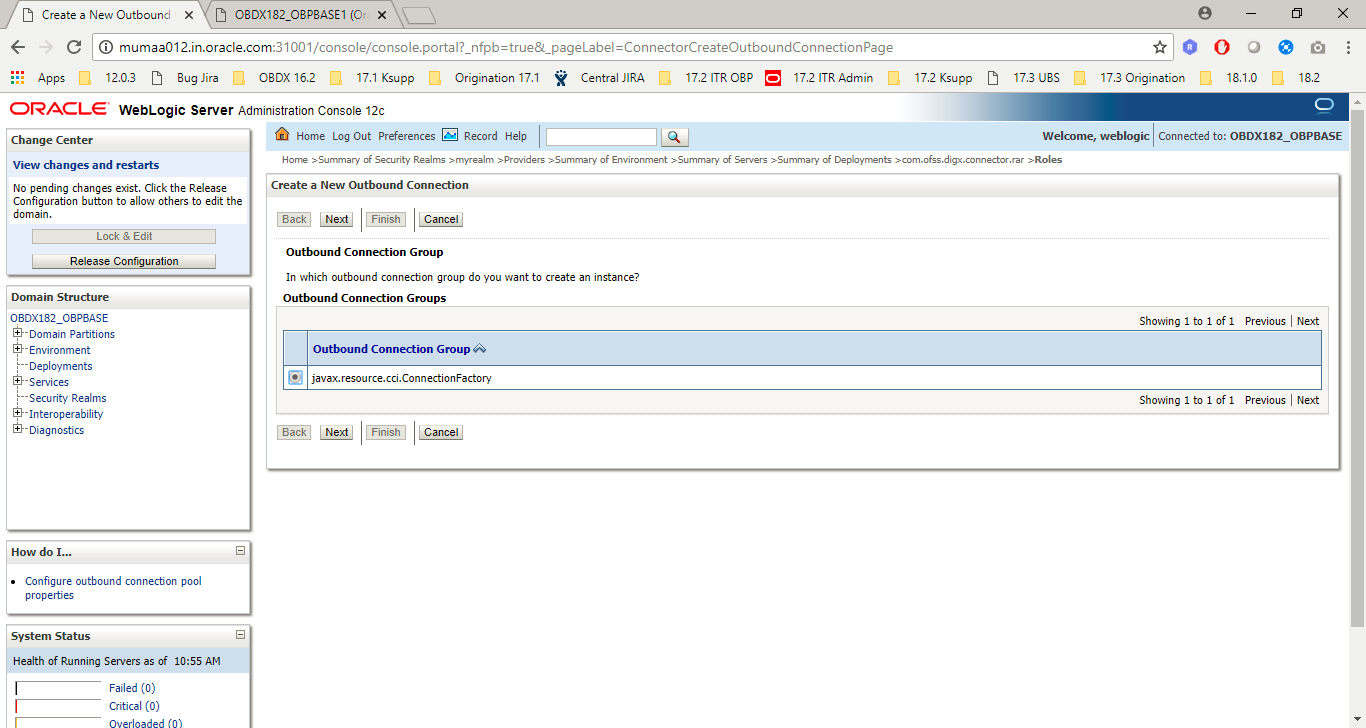
- Click on “New” button and select connection factory. Refer Screenshot.
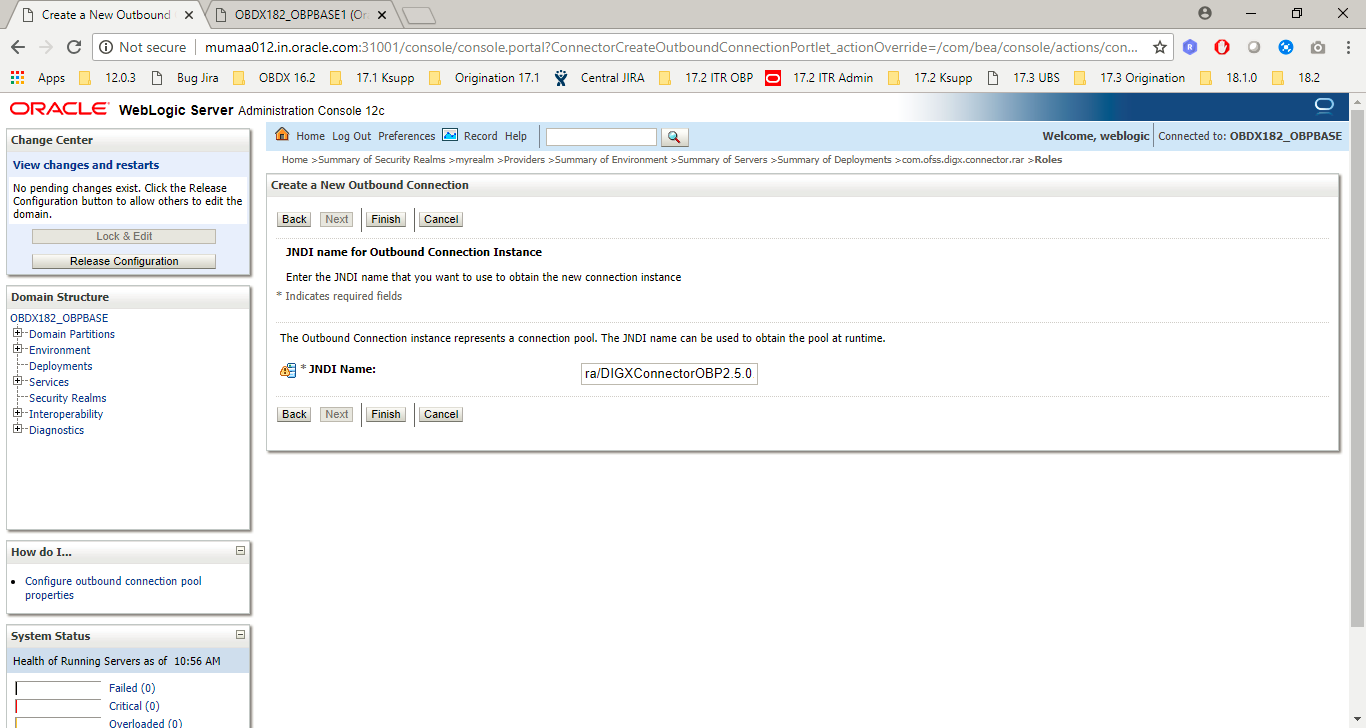
- Provide JINDI name as inserted in previous scripts. In this case name will be “ra/DIGXConnectorOBP”. After providing the name and Click on “Next”.
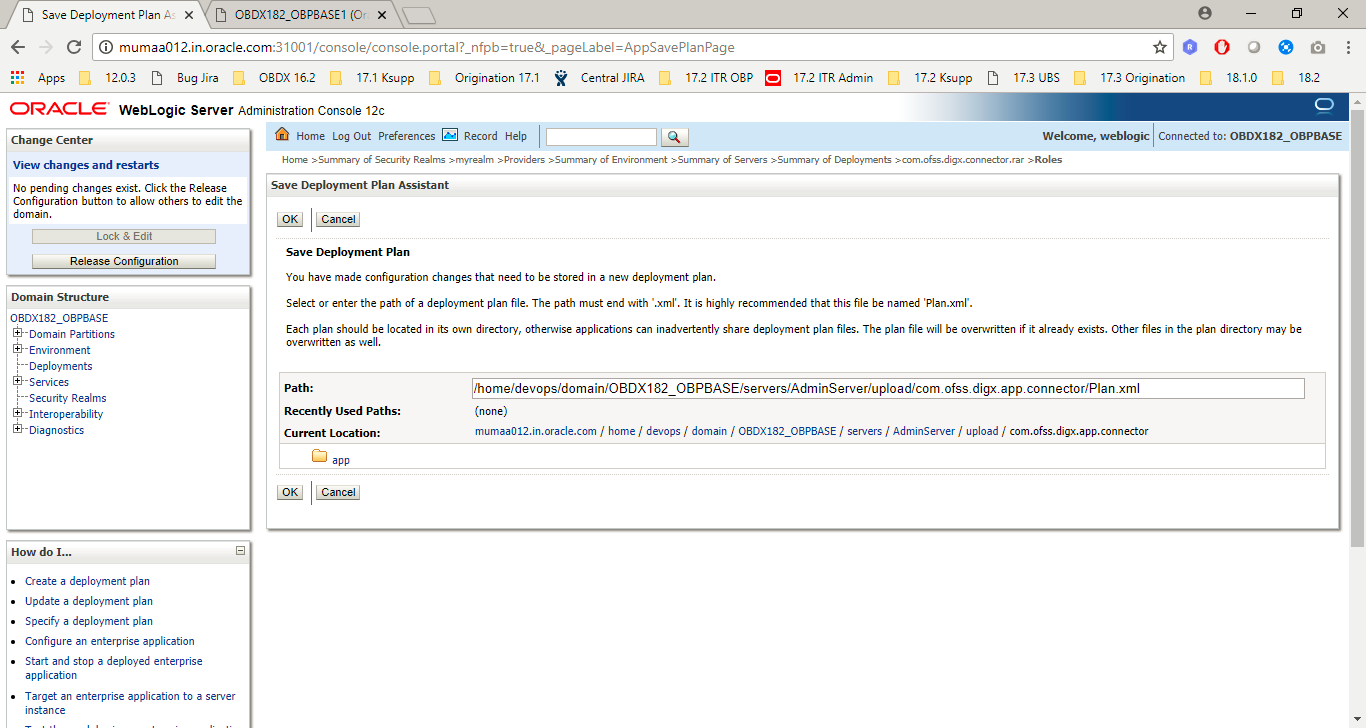
- Click on “Ok” to confirm.
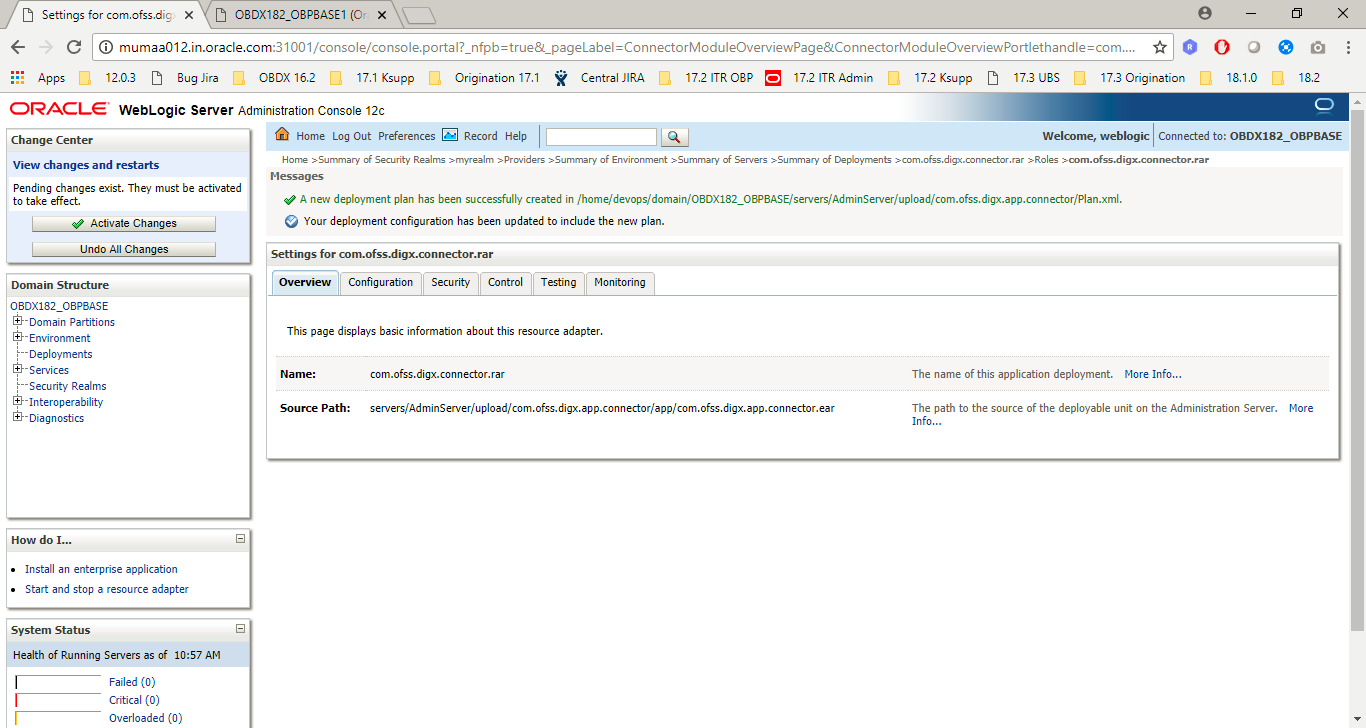
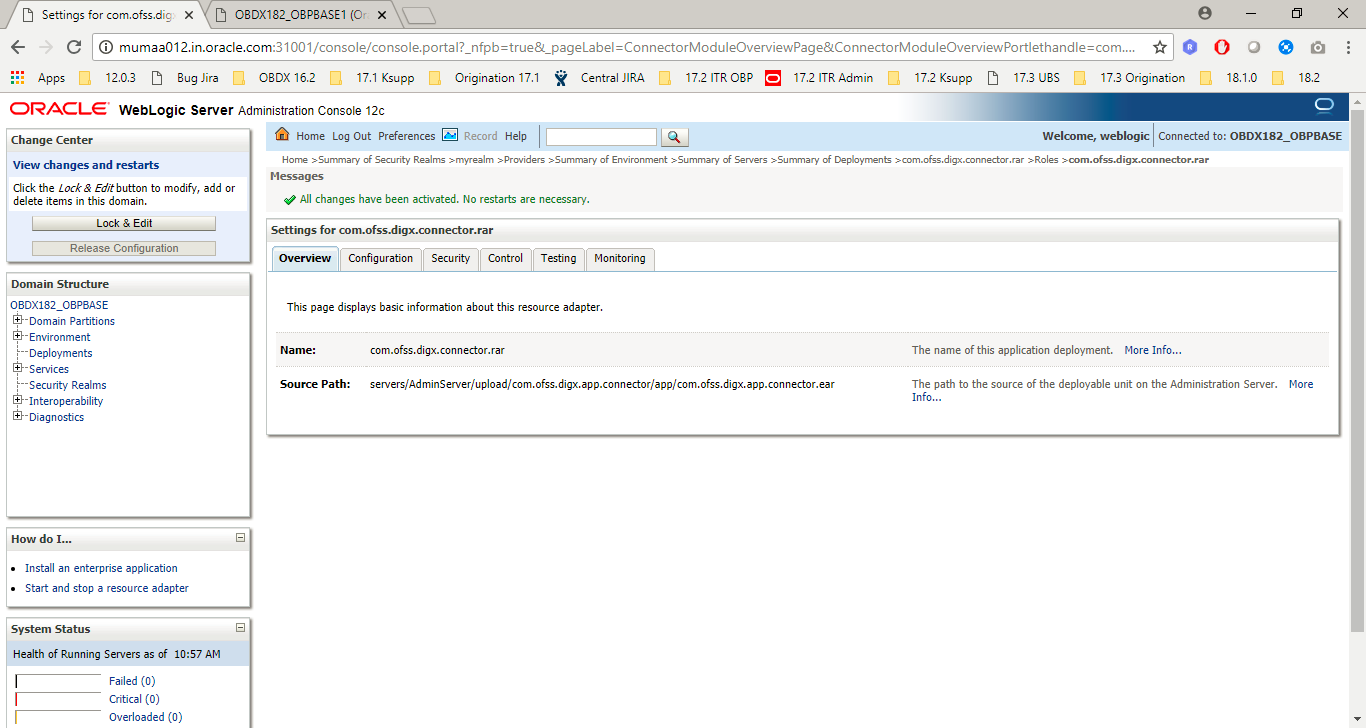
- Click on Activate changes.
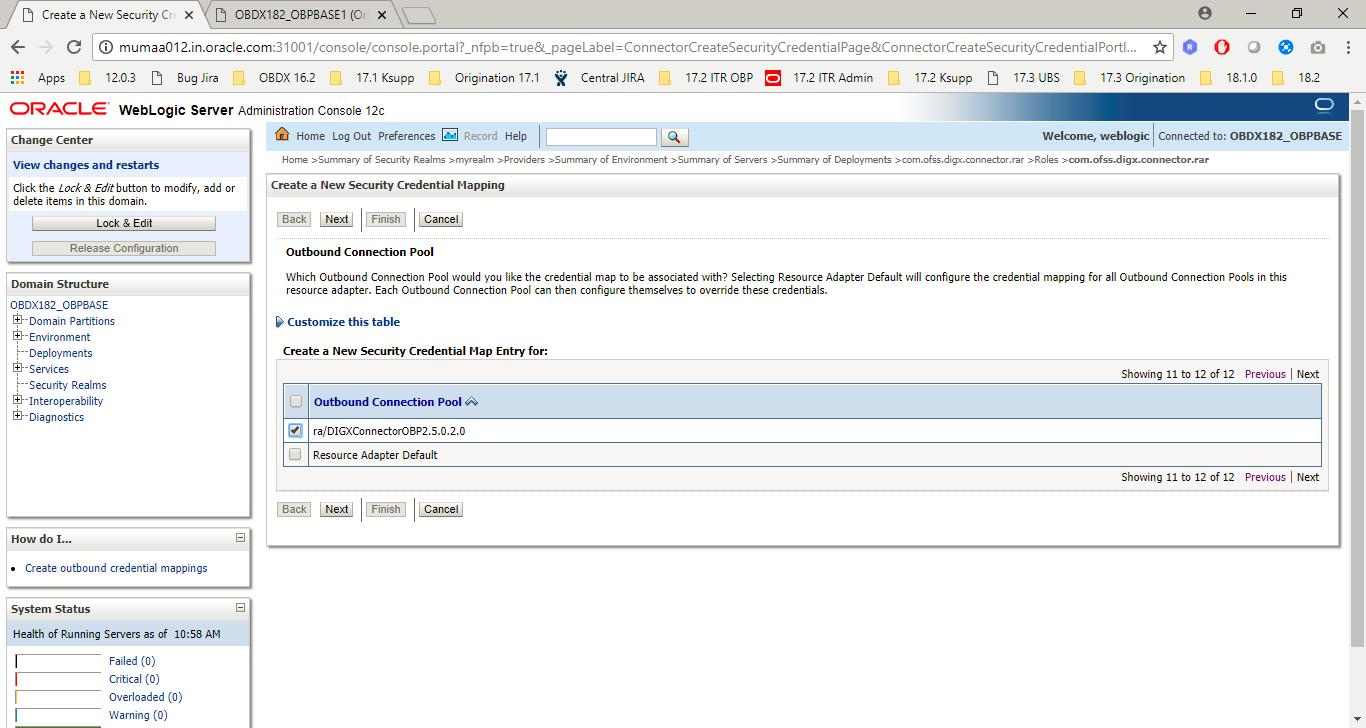
- Click on Security tab of connector, click on “Outbound credentials mapping”, click on “New” and select the newly created provider “ra/DIGXConnectorOBP” and click on “Next”.
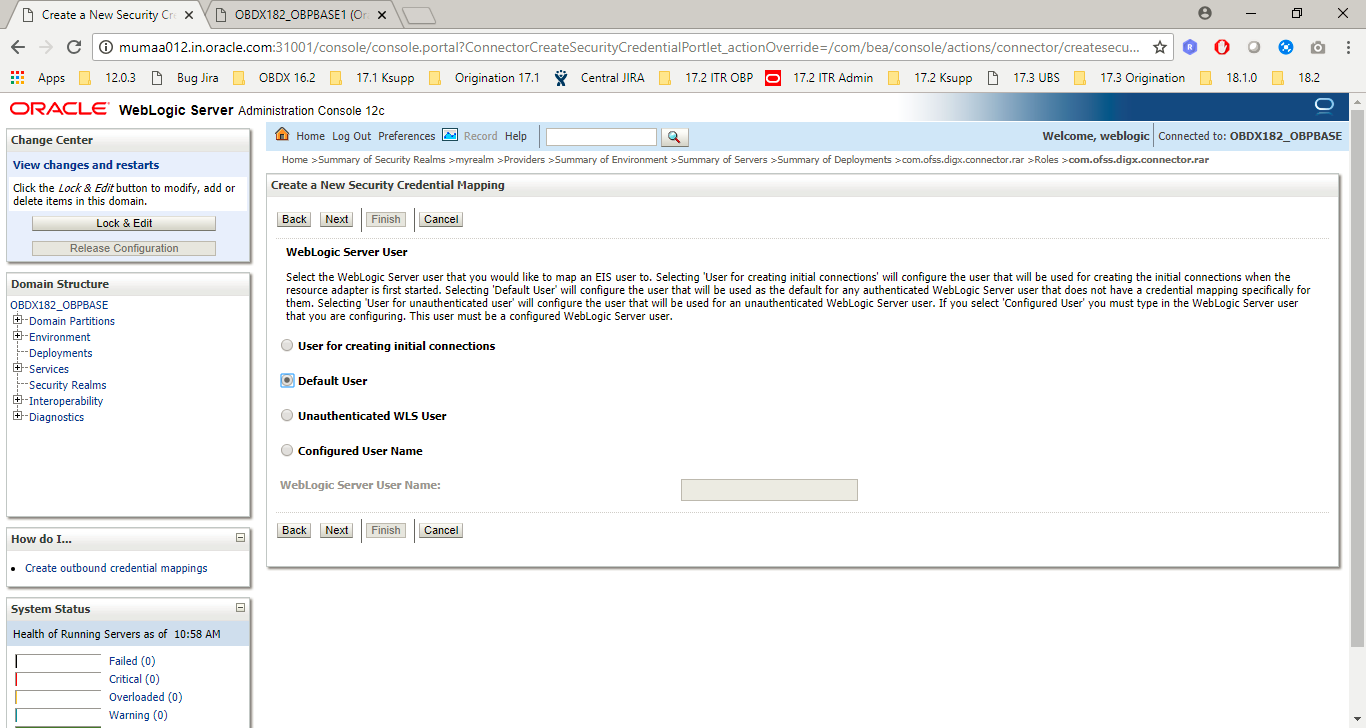
- Select the default user and Click on “Next”.
- Provide the user details as provided by OBP Team and Click on Finish.
- Restart managed server to take effects.