When P6 Professional is connected to a P6 EPPM database, the administrator, using P6, can restrict a user's access to resource information.
When P6 Professional is connected to a P6 Professional database, the administrator can restrict a user's access to resource information.
The administrator can enable or disable resource security for each user. When resource security is disabled, the user has access to all resources. When resource security is enabled, the user has access to either none of the resources or selected parts of the resource hierarchy.
Note: Personal information (PI) may be stored in this area of P6 EPPM.
Administrators should refer to the Consent Notices section of the Application Administration Guide. All other users of P6 EPPM should refer to the Consent notices section of the Help.
How does resource security work?
To enable resource security, the administrator assigns each user to one or more resource nodes in the resource hierarchy. These are the user's root nodes. Then, the position of each root node in the resource hierarchy determines the resources to which the user has access. Once assigned to a resource node, the user has accessy to the root node and all of its children.
The administrator can give each user access to the following:
- All Resources
The user has access to all resources with no restriction. This option disables resource security.
For Admin superusers, resource security access settings are ignored; they are always granted All Resources access. - No Resources
The user has no access to resources. This is the default resource access to new users. Also, if a resource is deleted from the resource hierarchy, users that previously had been assigned to the deleted resource automatically get no access to resources.
If a user has no resources access, all global resource-related privileges are ignored. - Resource nodes (Selected Resources)
The user has access to the assigned resource nodes and their children.
Notes
- When connected to a P6 EPPM database: You need the appropriate global privilege to manage resource security.
When connected to a P6 Professional database: You need Add/Edit/Delete Users global privilege to manage resource security.
- In the Resource Assignments window you still have access to current project resources.
Example
The following examples illustrate how resource security applies to users assigned to different resource nodes:
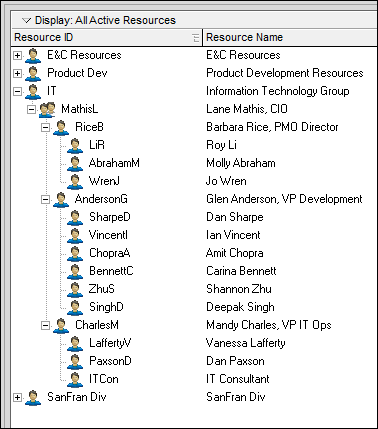
Shannon Zhu has restricted access with the root resource IT - Information Technology Group assigned. Shannon sees the following resources in the resource dictionary: IT, MathiasL, RiceB, LiR, AbrahamM, WrenJ, AndersonG, SharpeD, VincentI, ChopraA, BennettC, ZhuS, SinghD, CharlesM, LaffertyV, PaxsonD, and ITCon.
Vanessa Lafferty has restricted access with the root resources AndersonG - Glen Anderson, VP Development and CharlesM - Mandy Charles, VP IT Ops assigned. Vanessa sees the following resources in the resource dictionary: AndersonG, SharpeD, VincentI, ChopraA, BennettC, ZhuS, SinghD, CharlesM, LaffertyV, PaxsonD, and ITCon.
Roy Li has no resource access. Roy cannot see any resources in the Resource Administration page. Roy can see resources assigned to a project he has open.
Lane Mathis has access to All Resources. Lane can see all of the resources in the entire resource dictionary.