9. Configure JMS Queue
The following steps are to be performed to configure the JMS Queue through the Weblogic Console:
- Create Data Sources for JMS Queue
- AQ-JMS Queue Configuration
- Outbound Queue Configuration
- Configure External Client Certificates
- Create Credentials and System Policies
- Deploy MDB EJB
Note
Ensure that MDB EJB is not configured and deployed (i.e. OfsllQueueApp.ear deployment) on the same server on which the other WebServices are deployed.
9.1 Create Data Sources for JMS Queue
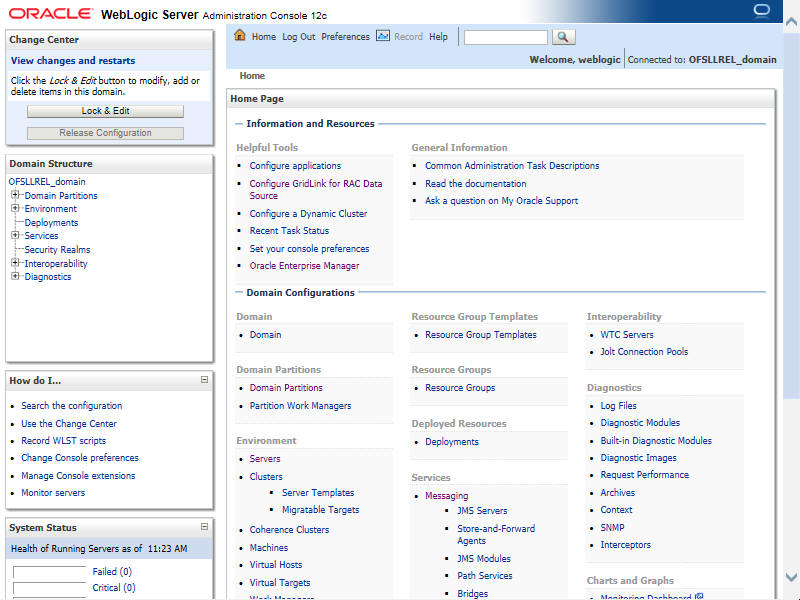
- Login to Oracle Weblogic 12c console (http://hostname:port/console).

- On successful login, the following window is displayed.
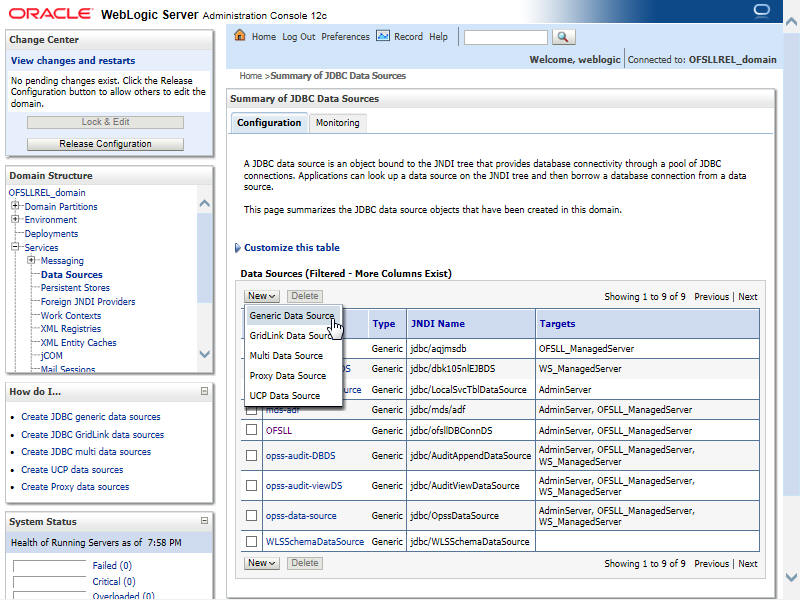
- Click Domain Name > Services > Data Sources. The following window is displayed.
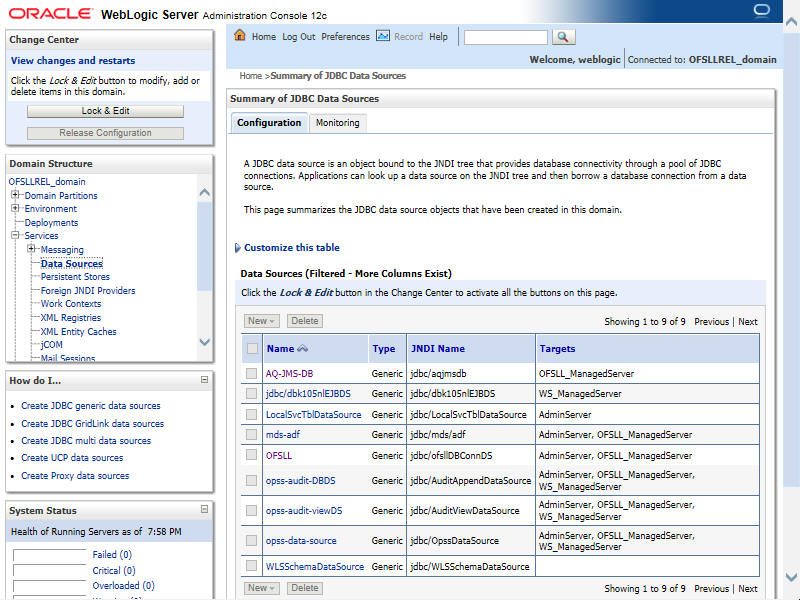
- Click ‘Lock & Edit’ button on the left panel. Click ‘New’ on right panel and select ‘Generic Data Source’.
- The following window is displayed.

- Specify the following details:
- Enter Data source Name: QueueAppDS
- Enter the JNDI Name as ‘jdbc/QueueAppDS’.
Note
If required, you may specify any other JNDI name, but ensure to use the same JNDI name during other configuration steps.
- Select ‘Oracle’ as Database Type.
- Click ‘Next’. The following window is displayed.

- Select the Database Driver ‘Oracle's Driver(Thin XA) for Services connections;Versions:Any’.
- Click ‘Next’. The following window is displayed.

- Click ‘Next’. The following window is displayed.
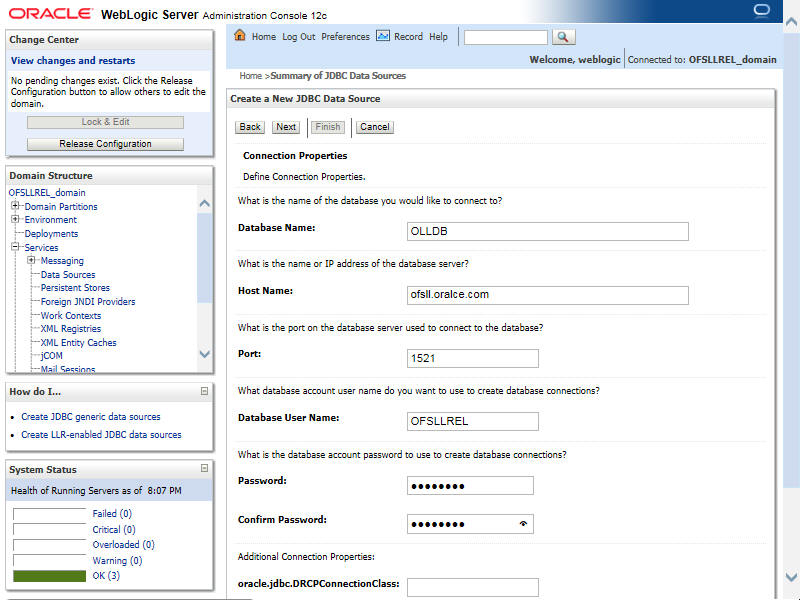
- Enter the Database details.
- Click ‘Next’. The following window is displayed.
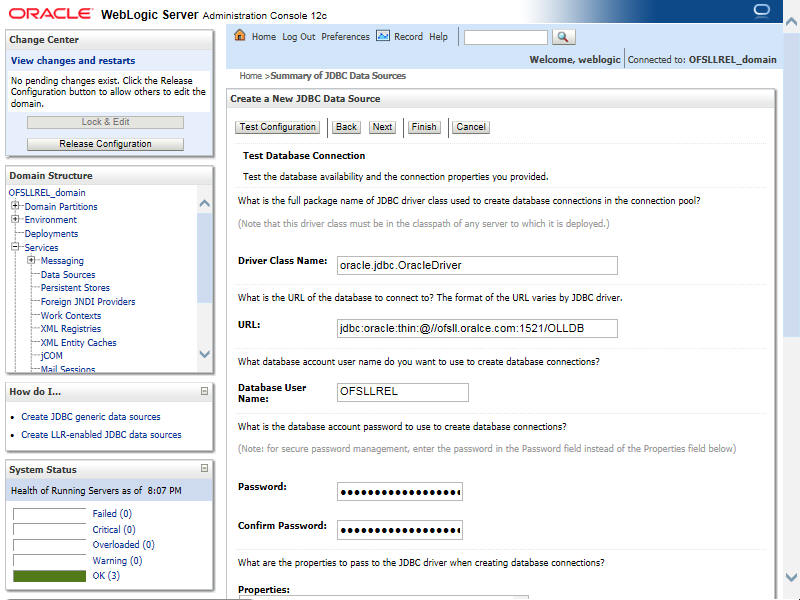
- Click ‘Test Configuration’. On completion, displays a confirmation message as ‘Connection test succeeded’.
- Click ‘Next’. The following window is displayed.

- Select target Server as ‘OFSLL_ManagedServer’.
- Click ‘Finish’ to activate the changes.
Update the following parameters in JDBC data source connection pool:
- Select Services > Data Sources > select the QueueAppDS data source > Connection Pool.
- Initial capacity and Maximum capacity is defaulted to 30, if the number of concurrent users are more this needs to be increased.
- To Enable GRI (Generic Recovery Interface) CLOB logging from MDB to DB, click Advanced button and deselect the 'Wrap Data Types' check box.
- Click Advanced button and update the ‘Inactive Connection Timeout’ to 300 seconds.
- Click 'Save' and restart the Data source.
9.2 AQ-JMS Queue Configuration
AQ-JMS queue is used to hold webservice invocation exception messages. It provides a mechanism for third parties to handle communication related failures.
Perform the following steps to configure AQ-JMS queue in application server.
9.2.1 Create JMS Server
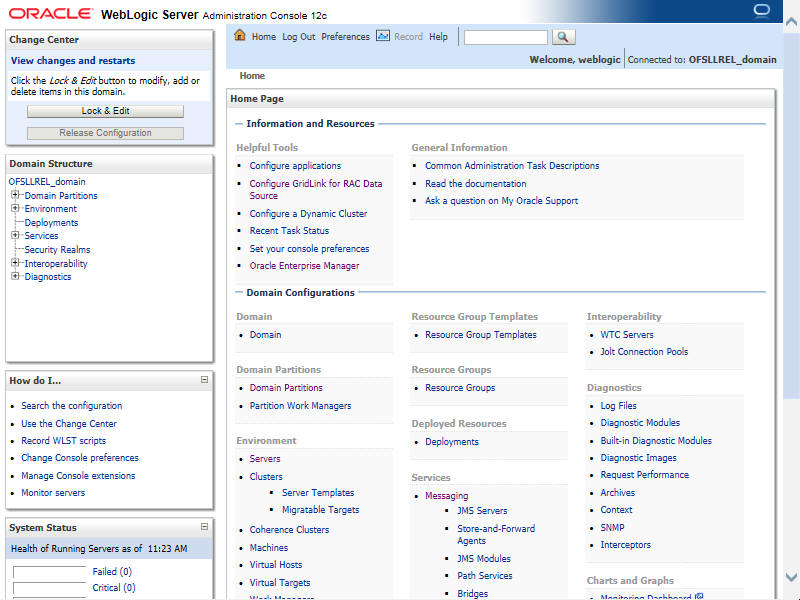
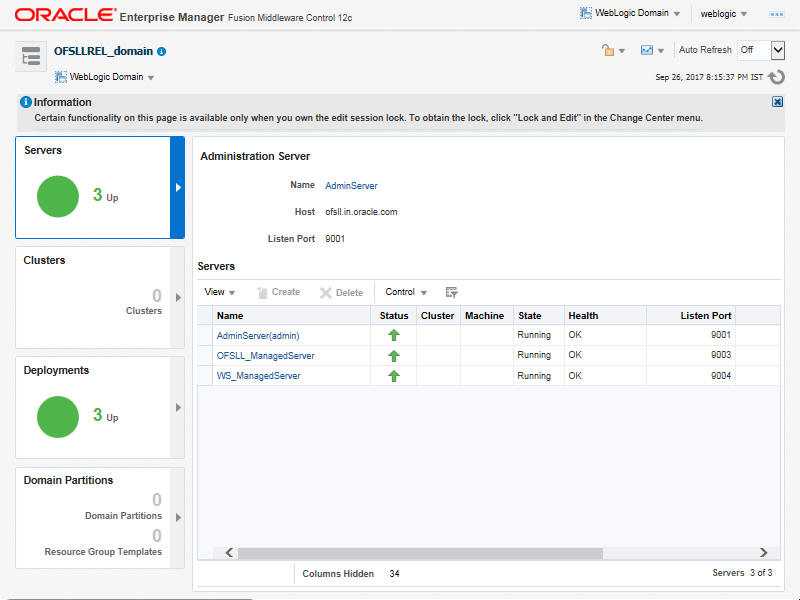
- Login to WebLogic Server 12c console (http://hostname:port/console). The following screen is displayed.

- Specify the Weblogic administrator user name and password and click 'Log In'. The Oracle Weblogic home page is displayed.

- Click Domain Name > Services > Messaging > JMS Server.
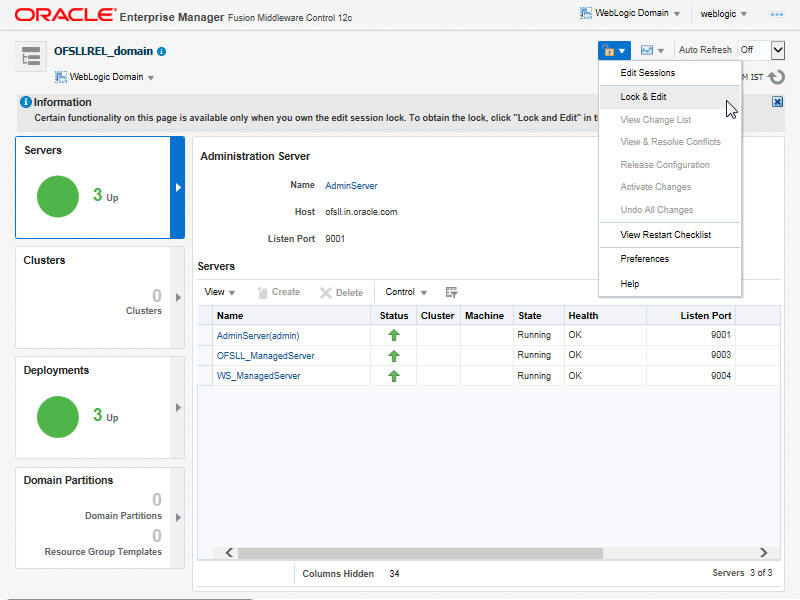
- In the main window, click 'Lock & Edit'. The following window is displayed.

- Click 'New'. The following window is displayed.

- Specify the JMS Server Name as ‘OfsllJMSServer’. Click ‘Next’, the following window is displayed.

- Select 'None' as the Persistent Store type. Click 'Next', the following window is displayed.

- Select the target managed server and click 'Finish'.
- Click 'Activate Changes' under Change Center. Once done, the following window is displayed:

9.2.2 Create JMS Module
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The following window is displayed.

- Click 'New'. The following screen is displayed.

- Specify the following details:
- Enter the System Module Name as ‘OfsllJMSModule’
- Enter the Description File Name as ‘OfsllJMSModule’
- Click ‘Next’. The following screen is displayed.

- Select the target server and click 'Next'. The following window is displayed.

- Click 'Finish' to save and activate the changes. Once done, the following window is displayed.

9.2.3 Subdeployment
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The main window displays the list of JMS modules available.
- Select the created JMS module ‘OfsllJMSModule’ and click 'Subdeployments' tab. The following window is displayed.

- Click 'New'. The following screen is displayed.

- Specify the Subdeployment Name as ‘OfsllJMSSD’. Click 'Next', the following window is displayed.

- Select the check box against the newly created JMS Server and click ‘Finish’. Once done, the following window is displayed.

9.2.4 Create JMS Connection Factory
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The main window displays the list of JMS modules available.
- Select the newly created JMS module ‘OfsllJMSModule’. The following window is displayed.

- Click 'New’. The following window is displayed.

- Click 'Next'. The following window is displayed.

- Select 'Connection Factory' option and click 'Next'. The following window is displayed.

- Specify the following details:
- Enter the Name of the Connection Factory as 'OfsllJMSCF’
- Enter the JNDI Name as ‘jms/OfsllJMSCF’
- Select the check box 'XA Connection Factory Enabled'
- Click 'Next'. The following window is displayed.

- Click 'Advanced Targeting'. The following window is displayed.

- Select the Subdeployments as ‘OfsllJMSSD’ from the drop down list.
- Under JMS Servers, select the check box against 'ofsllJMSServer'.
- Click 'Finish' to save and activate the changes. Once done, the following window is displayed.

9.2.5 Create JMS Queue
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The main window displays the list of JMS modules available.
- Select the newly created JMS module ‘OfsllJMSModule’. The following window is displayed.

- Click ‘New’. The following window is displayed.

- Select the 'Queue' option and click 'Next'. The following window is displayed.

- Specify the following details while creating new JMS System Module Resources:
- Enter the Name of the Queue as 'OfsllJMSQueue’
- Enter the JNDI Name as 'jms/OfsllJMSQueue’
- Select the Template as 'None'
- Click 'Next'. The following window is displayed.

- Select the Subdeployments as 'OfsllJMSSD' from the drop-down list.
- Click ‘Finish’ to save and activate the changes. Once done, the following window is displayed.

9.3 Outbound Queue Configuration
Outbound Queue provides a mechanism to consume AQ messages from the database and send those messages to MDBs.
Perform the following steps to configure Outbound queue in application server.
- Create Persistent Stores
- Create JMS Server
- Create JMS Module
- SubDeployment
- Create JMS Connection Factory
- Create JMS Queue
9.3.1 Create Persistent Stores
- Login to Oracle Weblogic 12c console (http://hostname:port/console).

- On successful login, the following window is displayed.
- Click Domain Name > Services > Persistent Stores

- Click 'Lock & Edit' button on the left panel. Click 'New' on right panel and select 'Create JDBCStore'

- Specify the following details:
- Name: OfsllStore
- Prefix Name: Ofsll

- Click 'Next'. The following window is displayed.

- Select 'OFSLLREL' Data source from the drop-down list. Click 'Next'. The following window is displayed.

- Select the Target as OFSLL_ManagedServer from the drop-down list. Click 'Next'. The following window is displayed.

- Click 'Finish' to activate the changes.
In case you are creating a cluster setup, continue the below steps:
- Click Domain Name > Environment > Clusters. The following window is displayed.

- Click 'app_cluster'. The following window is displayed.

- Click 'Lock & Edit' button on the left panel. The following window is displayed.

- Click 'Migration' tab and choose Migration Basis as ‘Consensus’ from the drop-down list.
- Click 'Save' to activate the changes.
9.3.2 Create JMS Server
- Login to WebLogic Server 12c console (http://hostname:port/console). The following screen is displayed.

- Specify the Weblogic administrator user name and password and click 'Log In'. The Oracle Weblogic home page is displayed.

- Click Domain Name > Services > Messaging > JMS Server.
- In the main window, click 'Lock & Edit'. The following window is displayed.

- Click 'New'. The following window is displayed.

- Specify the JMS Server Name as ‘OfsllOutboundServer’. Click ‘Next’, the following window is displayed.

- Select 'OfsllStore' as the Persistent Store type. Click 'Next', the following window is displayed.

- Select the target managed server and click 'Finish'.
- Click 'Activate Changes' under Change Center section in LHS menu. Once done, the following window is displayed:

- Once done the following window is displayed:

9.3.3 Create JMS Module
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The following window is displayed.

- Click 'New'. The following screen is displayed.

- Specify the following details:
- Enter the System Module Name as ‘OfsllOutboundModule’
- Enter the Description File Name as ‘OfsllOutboundModule’
- Click ‘Next’. The following screen is displayed.

- Select the target server and click 'Next'. The following window is displayed.

- Click 'Finish' to save and activate the changes. Once done, the following window is displayed.

9.3.4 SubDeployment
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The main window displays the list of JMS modules available.
- Select the created JMS module ‘OfsllOutboundModule’ and click 'Subdeployments' tab. The following window is displayed.

- Click 'New'. The following screen is displayed.

- Specify the Subdeployment Name as ‘OfsllOutboundSD’. Click 'Next', the following window is displayed.

- Select the check box against the newly created OfsllOutboundServer and click ‘Finish’.
- Once done, the following window is displayed.

You can further click 'New 'to create more Queues and repeat the steps explained above.
9.3.5 Create JMS Connection Factory
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The main window displays the list of JMS modules available.

- Select the newly created JMS module ‘OfsllModule’. The following window is displayed.

- Click 'New’. The following window is displayed.

- Select 'Connection Factory' option and click 'Next'. The following window is displayed.

- Specify the following details:
- Enter the Name of the Connection Factory as 'OfsllOutboundCF’
- Enter the JNDI Name as ‘jms/OfsllOutboundCF’
- Select the check box 'XA Connection Factory Enabled'
- Click 'Next'. The following window is displayed.

- Click 'Advanced Targeting' button. The following window is displayed.

- Do the following:
- Select the Subdeployments as ‘OfsllOutboundSD’ from the drop down list.
- Under JMS Servers, select the check box against 'OfsllOutboundServer'.
- Click 'Finish' to save and activate the changes. Once done, the following window is displayed.

9.3.6 Create JMS Queue
- Login to WebLogic Server 12c console (http://hostname:port/console) by specifying the Weblogic administrator user name and password.
- Click Domain Name > Services > Messaging > JMS Modules. The main window displays the list of JMS modules available.
- Select the newly created JMS module ‘OfsllOutboundModule’. The following window is displayed.

- Click ‘New’. The following window is displayed.

- Select the 'Distributed Queue' option and click 'Next'. The following window is displayed.

- Specify the following details while creating new JMS System Module Resources:
- Enter the Name of the Queue as 'OfsllOutboundQueue’
- Enter the JNDI Name as 'jms/OfsllOutboundQueue’
- Select the Template as 'None'
- Click 'Next'. The following window is displayed.

- Click 'Advanced Targeting' button. The following window is displayed.

- Select the Subdeployments as 'OfsllOutboundSD' from the drop-down list.
- Click ‘Finish’ to save and activate the changes. Once done, the following window is displayed.

You can further click 'New 'to create more Queues and repeat the steps explained above.
9.4 Configure External Client Certificates
The Webhook option in OFSLL extends the support of interfacing with third-party applications by sending REST API based notifications of changes through system generated Webhook event actions.
In a Webhook setup you can notify the changes that are done in OFSLL by triggering Webhook request as an event action and propagate the information to the dependant third-party applications (client) through specific https communication channel.
For webhook HTTPS communication, client certificates are to be imported in Weblogic OPSS keystore for each channel.
Follow the below steps to import the certificates.
- Login to the Oracle Enterprise Manager 12c console. (i.e. http://hostname:port/em)
- Click on ‘Weblogic Domain’ drop-down list and navigate to Security > Keystore.

- Click on ‘Create Stripe’.

- Enter the Stripe Name as ‘OFSLL_STRIPE’.

- Click ‘OK’. The following OFSLL_STRIPE is created.

- Select the newly created ‘OFSLL_STRIPE’ and click ‘Keystore’.
- Enter the Keystore Name as ‘OFSLL_KSS’ and click ‘OK’.

- Select ‘OFSLL_KSS’ and click ‘Manage’..

- Click ‘Import’.

- In the below ‘Import Certificate’ screen, specify the following details:
- Certificate Type: Trusted Certificate
- Alias: webhook Channel Name
- Choose file: webhook channel certificate

- Click ‘OK’.
9.5 Create Credentials and System Policies
In order Configure MDB flow, you need to create credentials and system policies. The credentials are accessed through CSF framework which is managed by Oracle Weblogic Server. The keys are managed by Maps and Maps need to be given with Permissions.
- Login to Oracle Enterprise Manager (http://hostname:port/em).
- On the left panel, right click on OFSLLREL_domain and select Security > System Policies > Credentials. The following window is displayed.
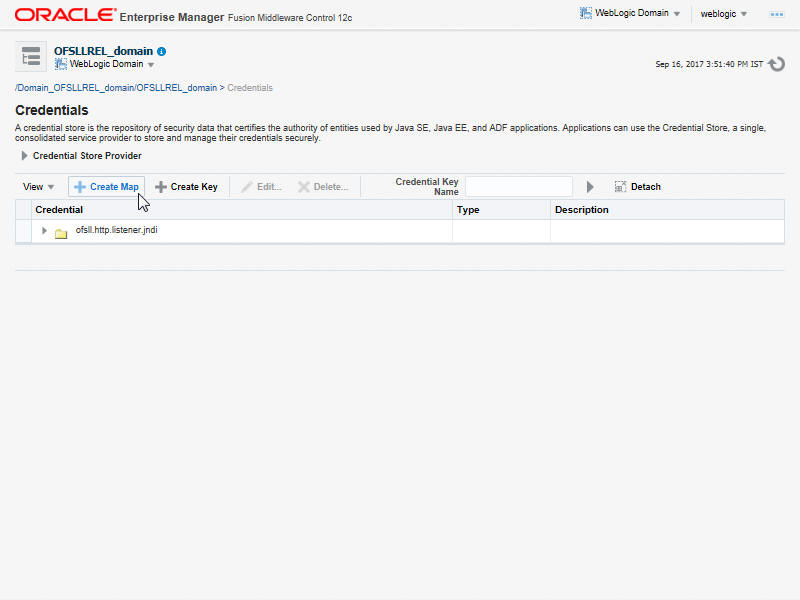
- Click ‘Create Map’. The following window is displayed.

- Enter Map Name as ‘ofsll.int.bureau’ and click ‘OK’.
- Click ‘Create Key’. The following window is displayed.

- Specify the following details:
- Select Map as ‘ofsll.int.bureau’ from the drop down list.
- Specify Key as ‘jdbc_ds_key’
- Select Type as ‘Generic’ from the drop down list.
- Specify the Credential as ‘jdbc/QueueAppDS’
- Click ‘OK’.
- Similarly you need to create the following Maps and corresponding keys as indicated in following table.
Maps
Keys
Description
ofsll.int.bureau
This map is used to setup keys for all credit bureau interfaces
ProxyServer
Name of the proxyServer to be configured
ProxyPort
Port to which ProxyServer is running.
ExpEcalsURL
The Experian Connection URL to be configured.
ExpDirectExperianEnabled
If you set value as true, then you would be setting ecals response URL. Else, the Ecals request URL
ExpCertPath
The location of .jks file which contains the valid certificate for Experian Credit Bureau.
ExpBusUserNamePassword
Login Credentials to be configured for Experian Business reports.
ExpConUserNamePassword
Login Credentials to be configured for Experian Consumer reports.
EfxURL
The Equifax Connection URL to be configured.
EfxCertPath
The location of .jks file which contains the valid certificate for Equifax Credit Bureau.
EfxUserNamePassword
Login credentials to be configured for accessing Equifax Reports.
TucCertPath
The location of .jks file which contains valid certificate for Transunion Bureau .
TucCertPassword
The password that requires to read the valid .jks certificate for the Transunion Bureau.
TucUserNamePassword
Login credentials to be configured for accessing Transunion reports
TucConnectionURL
The Transunion URL to be configured.
jdbc_ds_key
Datasource configured to retrieve data for bureau.
source
Configured as EXTERNAL for actual call.
ofsll.int.outbound
This map is used to setup keys for the RouteOne and Dealer track call back from OFSLL.
roUserNamePassword
Login Credentials used at the time of call back from OFSLL to RouteOne Interface.
dtUsernamePassword
Login Credentials used at the time of Call back from OFSLL to Dealer Track Interface.
jdbc_ds_key
Datasource configured to retrieve data for outbound Resources.
roPostDealerUsernamePasswd
Credentials required to upload the dealer details to Route One Portal
roPostDealerWbsURL
Route One Post Dealer Web Service url
roDealerUploadURL
Route One URL to upload the Dealer details
dtPostDealerUsernamePasswd
Credentials required to upload the dealer details to Dealer Track Portal
dtPostDealerWbsURL
Dealer Track Post Dealer Web Service url
dtDealerUploadURL
Dealer Track URL to upload the Dealer details
VertexUserNamePd
Credentials required to connect to VERTEX web service
VertexTrustedId
ID required to connect to VERTEX web service
TorqueItsUserNamePassword
Credentials required to connect to TorqueIts web service
TorqueItsURL
TorqueIts Decision service URL
ProxyHost
Name of the proxyServer to be configured.
ProxyPort
Port to which ProxyServer is running.
ofsll.int.bip
This Map is used to setup all the Keys required to setup interface with BIP to generate reports.
local_top_dir
Define the path of the local BIP server where you would like place the generated BIP reports.
email_from_addr
Define the From Email address to be used while sending email for the generated BIP reports.
emailBodyContentPath
The path for ‘file.properties’ file that contains the content of the subject and body required while sending letter, report or correspondence as mail to the applicant or producer.
For example; /tmp/file.properties
*Refer to note below for details on ‘file.properties’ file creation for email configuration.
fax_server
Configure the name of Fax server to be used to fax the generated BIP reports.
jdbc_ds_key
Datasource configured to retrieve data for BIP.
ofsll.int.filetransfer
This map is used to setup keys for all credit bureau interfaces
sftp_key
Credentials to login to SFTP server(Username/Password)
sftp_top_dir
Top root directory for SFFTP server
sftp_servers
SFTP server names
ofsll.int.security
bip_key
This is BIP login credentials
ofsll.int.gri
GriURL
GRI web service URL to be configured.
GriAPIKey
GRI API key to be configured
ProxySet
System Level Proxy Enabled/Disabled. Value can be either true or false.
True= proxy required
False = proxy not required
ProxyHost
Name of the proxyServer to be configured.
Set only if ProxySet =true.
ProxyPort
Port on which ProxyServer is running.
Set only if ProxySet =true.
jdbc_ds_key
Datasource configured to retrieve the request XML for GRI.
GriCertPath
The location of .jks file which contains the valid certificate for GRI.
Configure only when a valid certificate is available.
ofsll.int.common
This map is used to setup keys for common JMS Queue
OfsllJMSQueueJNDI
The JMS queue JNDI name to be configured
OfsllJMSQueueCF
The JMS queue connection factory to be configured
OfsllJMSServerURL
The JMS server url to be configured.
Ex: t3://<JMS server host>:<JMS server port>
outbound_jms_queue_con_factory
The JMS connection factory to be configured.
jms/OfsllOutboundCF
outbound_jms_queue
The JMS queue to be configured.
jms/OfsllOutboundQueue
weblogic_cluster_ind
This is to be configured based on the environment i.e. for weblogic cluster environment set it as ‘Y’. Else, set it to ‘N’.
oubtbound_jms_queue_provider_url
The JMS server url to be configured.
Ex: For non clustered environment - t3://<JMS server host>:<JMS server port>
Ex: For clustered environment - t3://<JMS server host>:<JMS server port>,<JMS server host>:<JMS server port>
jdbc_ds_key
Datasource configured to read the message from the table.
ofsll.int.webhook
jdbc_ds_key
Datasource configured to retrieve data for Webhook.
* A new file(file.properties) needs to be created and copied to the application server in the same path as mentioned in the value corresponding to the key 'emailBodyContentPath' under the map 'ofsll.int.bip'. The file should have the following contents:
- letter_subject='Text that is configurable and would be the subject of the mail'
- letter_body='Text that is configurable and would be the body of the mail'
- correspondence_subject='Text that is configurable and would be the subject of the mail'
- correspondence_body='Text that is configurable and would be the body of the mail'
- report_subject='Text that is configurable and would be the subject of the mail'
- report_body='Text that is configurable and would be the body of the mail'
- On the left panel, right click on OFSLLREL_domain and select Security > System Policies. The following window is displayed.

- Click ‘Create’. The following window is displayed.

- Enter the codebase as ‘file:${domain.home}/lib/OfsllCommonCSF.jar’
- Click ‘Add’. The following window is displayed.

- Select the check box 'Select here to enter details for a new permission'.
- Specify the following details as the first permission class.
Permission Class
Resource Name
Permission Actions
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.bureau,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.filetransfer,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.outbound,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.bip,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.gri,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.common,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.http.listener.jndi,keyName=*
read
oracle.security.jps.service.credstore.CredentialAccessPermission
context=SYSTEM,mapName=ofsll.int.webhook,keyName=*
read, write, update
oracle.security.jps.service.keystore.KeyStoreAccessPermission
stripeName=OFSLL_STRIPE,keystoreName=OFSLL_KSS,alias=*
read
- Click ‘OK’.
9.6 Deploy MDB EJB
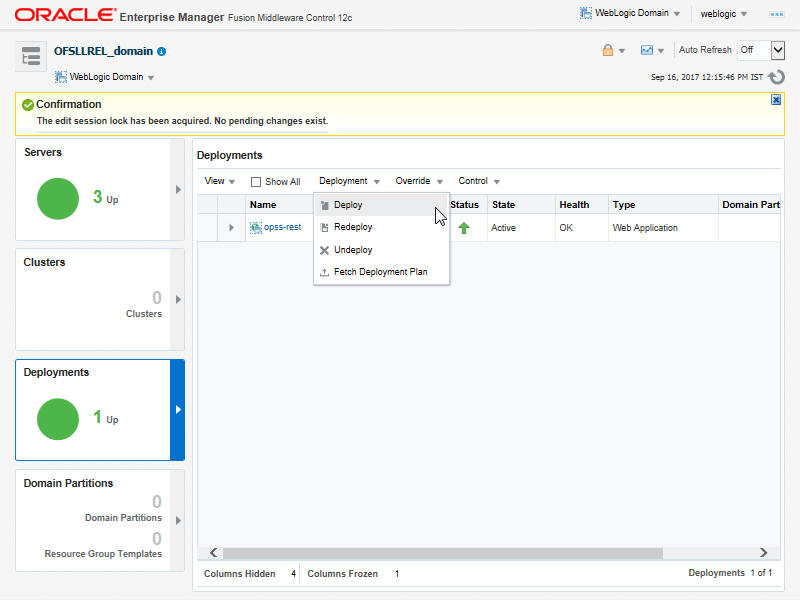
- Login to Web Logic application server enterprise manager (e.g.:http://hostname:port/em)
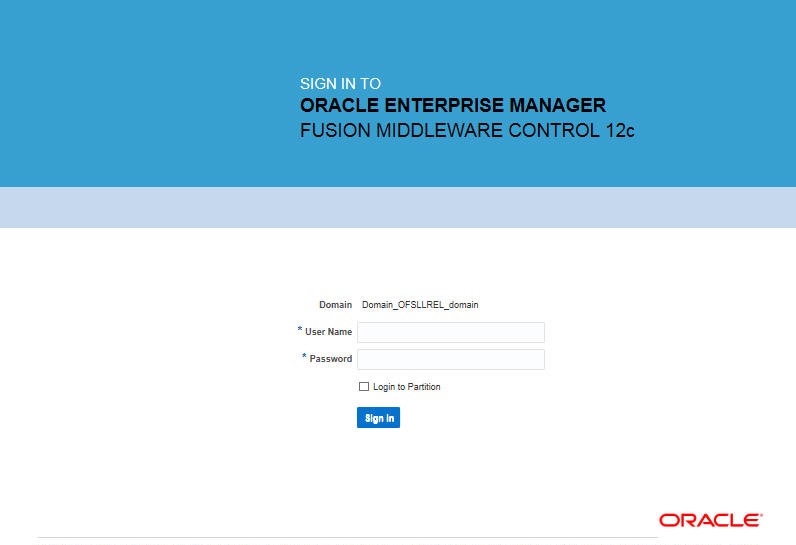
- Enter valid login credentials. The following window is displayed.
- Select ‘Lock & Edit’ option in the lock drop-down list available in the header.
- Click ‘Deployment’ in the left panel. The following window is displayed.
- Select ‘Deploy’ from the Deployment drop-down list. The following window is displayed.
- The following window is displayed.

- Browse to the folder containing the MDB EJB. Eg: C:/OfsllQueueApp.ear
- Click ‘Next’. The following window is displayed.

- Select the server on which the MDB EJB needs to be deployed.
- Click ‘Next’. The following window is displayed.

- Select the option ‘Install and start application (servicing all requests)’.
- Check the context root and click ‘Next’.The following window is displayed.

- Click ‘Deploy’. On successful deployment, the following window is displayed.

- Click ‘Close’. Post deployment, you need to activate the changes by selecting ‘Active Changes’ option from ‘Edit Session’ drop-down list as indicated in step 4 above.
Note
While starting the ‘OFSLLREL_ManagedServer’, always start with option ‘-DUseSunHttpHandler=true’ to enforce the weblogic server to uses SUN SSL implementation.