Group LDAP Mapper and Role Assignment
Group Mapper
The Group Mapper allows you to configure group mappings from LDAP into cncc-iam group mappings. Group mapper can be used to map LDAP groups from a particular branch of an LDAP tree into groups in cncc-iam. It also propagate user-group mappings from LDAP into user-group mappings in cncc-iam.
Steps to add Group-Mapper and assign roles
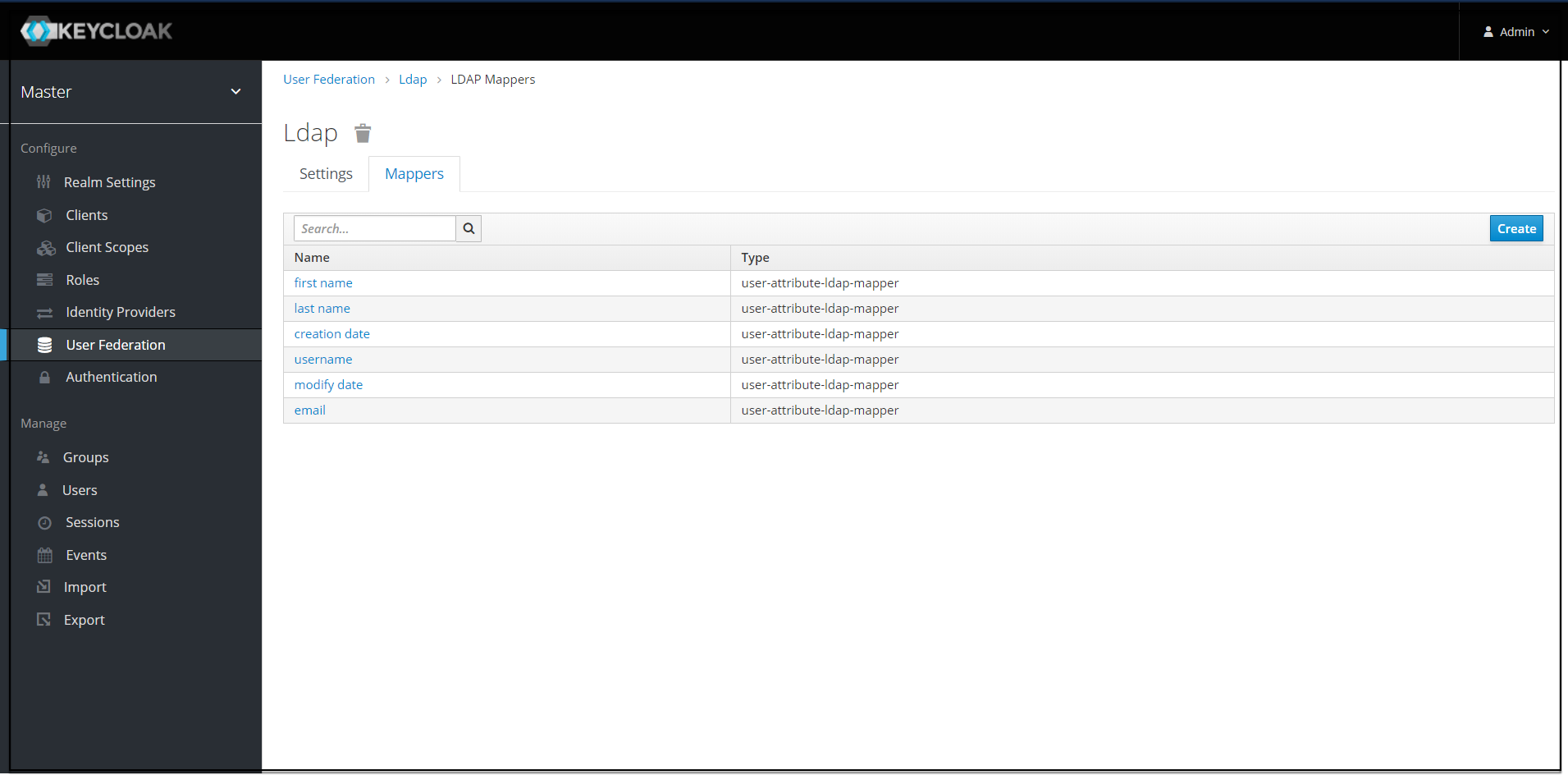
1. Click on Configure> User Federation. Click ldap (Console Display Name) and select the Mappers tab, and click Create.
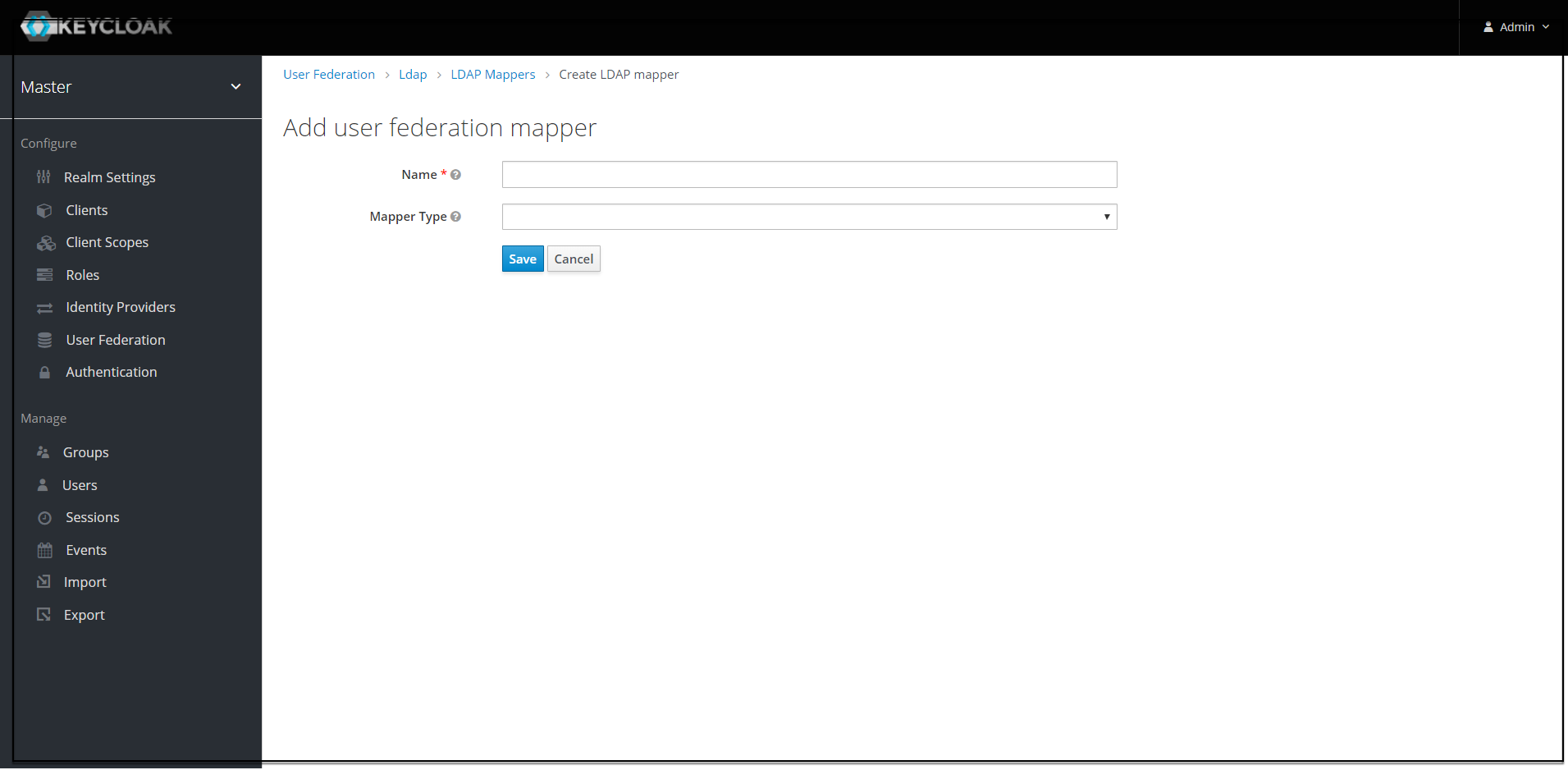
2. The Add User federation mapper page appears. Give an appropriate name for the field Name.Select 'group-ldap-mapper' as Mapper Type drop down menu. Click Save.
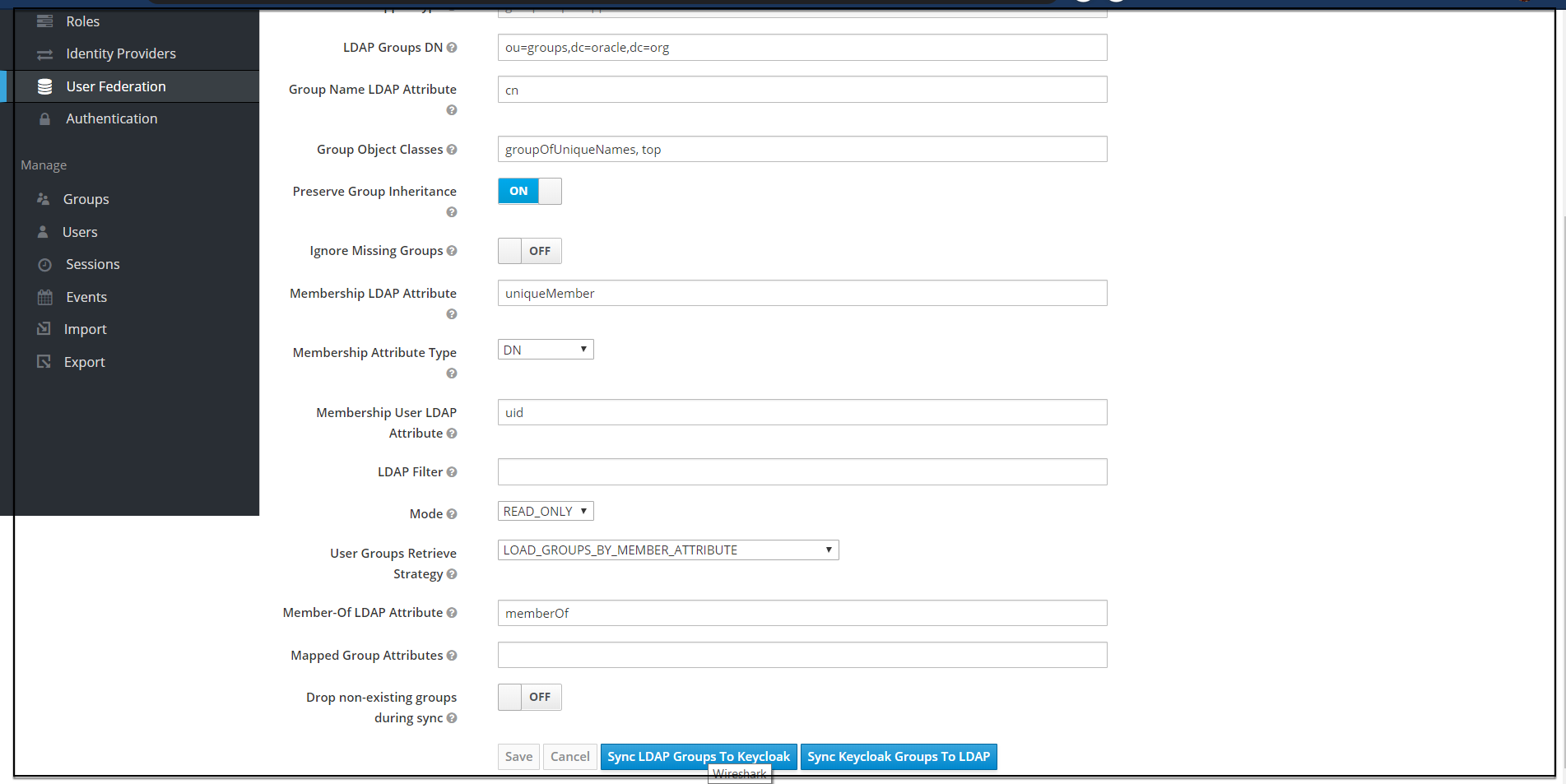
- The following screen appears.

Note:
When selected, default values will be set by cncc-iam. But you need change some values based on your ldap records.- 3. Provide the details for the following parameters.
- Fill LDAP Groups DN of the LDAP tree where your groups are.
- This path you can also see in ldap-ldif file and looks like this for the demo data : "ou=groups,dc=oracle,dc=org
- "Group Object Classes" is a field that needs to be modified for demo data. In the ldap-ldif file when you see any user, you can see the objectClass fields and values that the user has. In the current configuration, there are 2 values.
- The values in the chain must be provided. That is, the complete value as "groupOfUniqueNames, top" to be able to find the person correctly.
- Provide Membership LDAP Attribute. In our ldap-ldif file you can see user is attached to group by an attribute called "uniqueMember
4. Click on Save. New buttons appears next to the Save and Cancel. Synchronize LDAP Groups to Keyclaok and Synchronize Keyclaok Groups to LDAP.
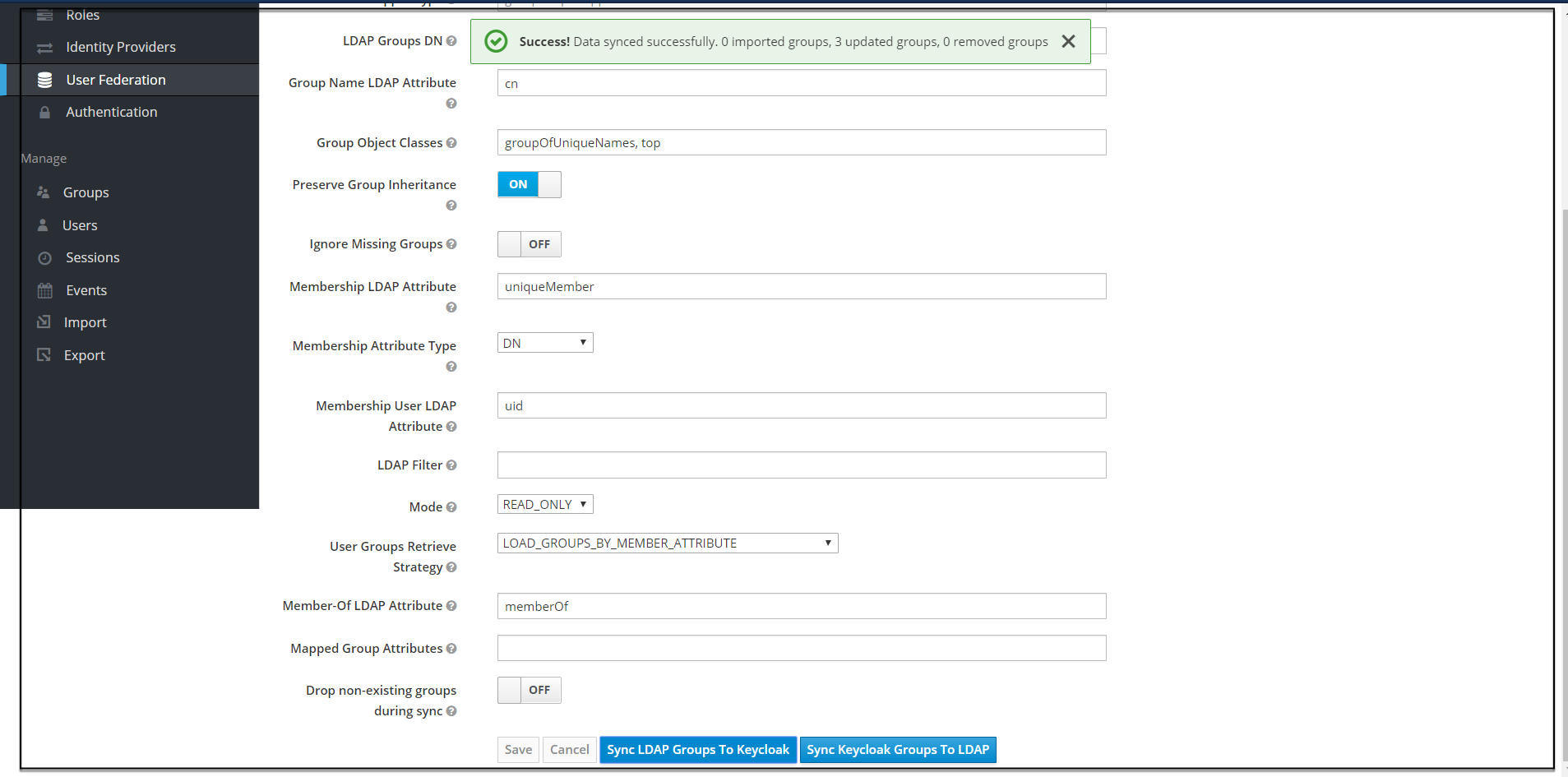
5. Click on Synchronize LDAP Groups to Keyclaok. The success message appears with the number of groups imported and so on.
Note:
If this step fails then you might need to check to the trouble shooting section and look at cncc-iam logs in debug mode.6. Click on the Groups at the left pane and click the View all groups at the right pane .
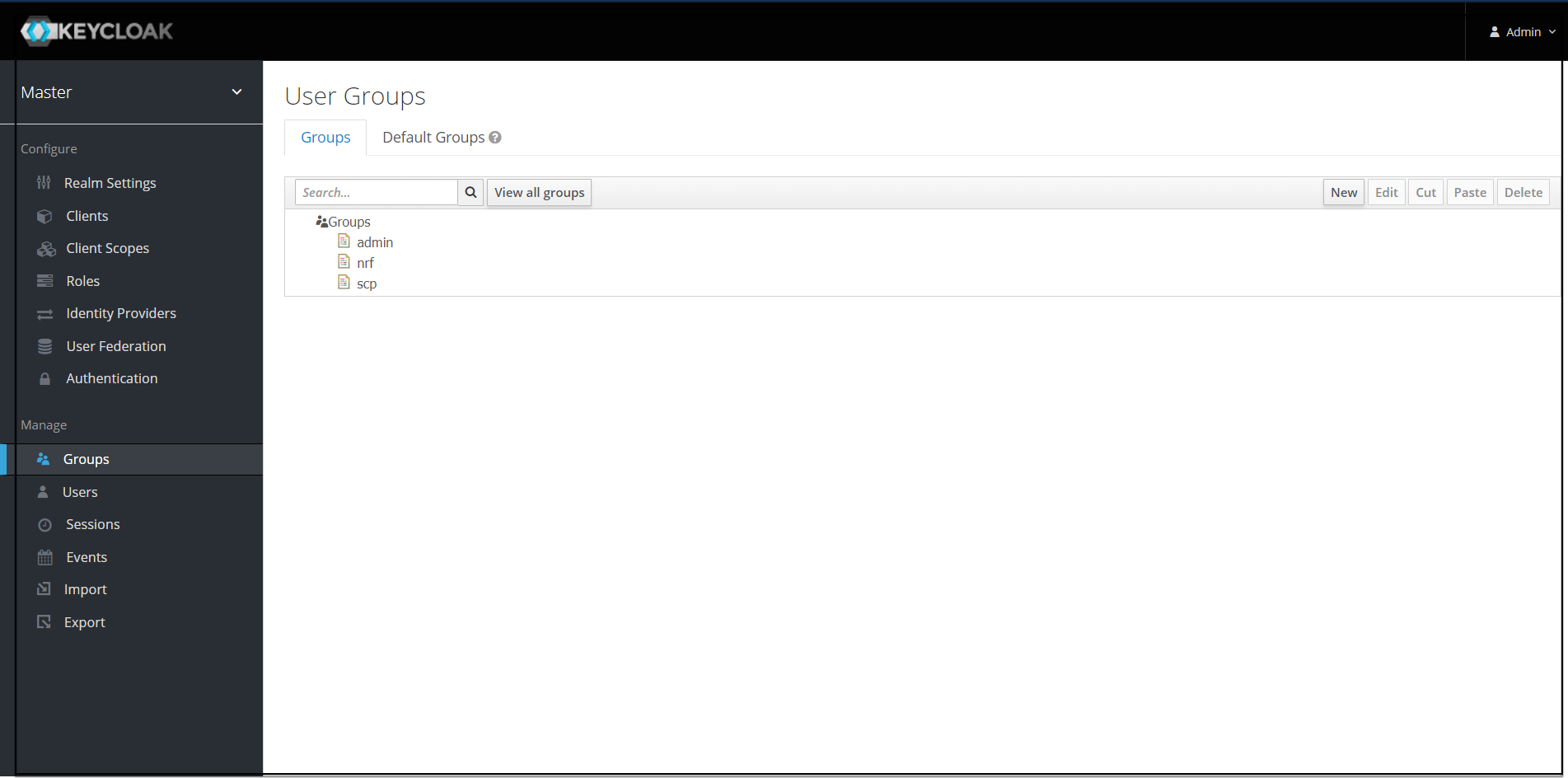
7. Click on any group and click Edit. The following tabs appear: Settings, Attributes, Role Mappings, and Members.
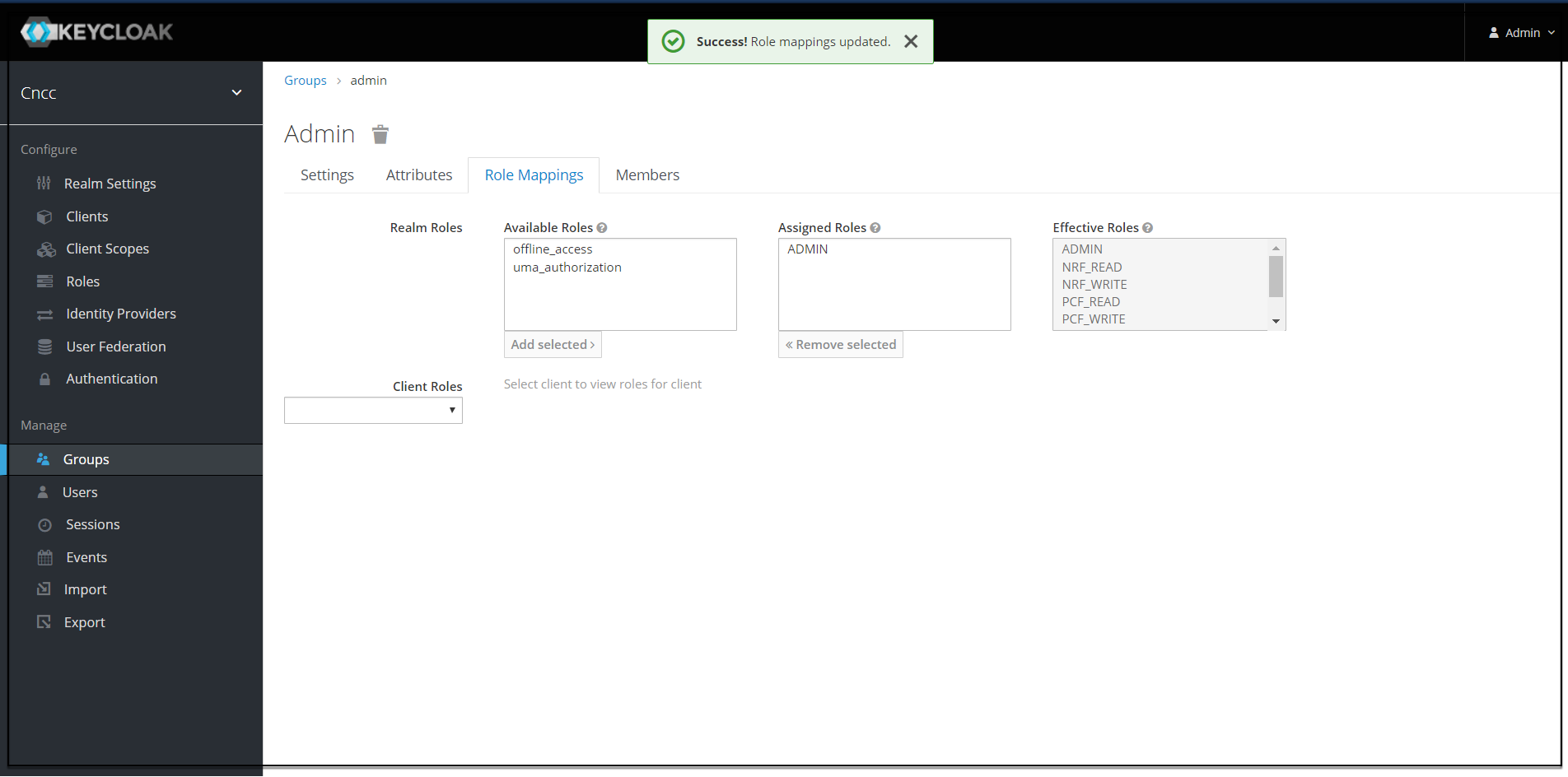
- Select Role Mapping tab to see a list of roles that are pre-defined in cncc-iam.
- Select one or more roles and assign it to the group. For example, If group "admin" is assigned with role "ADMIN", it means that any user which belongs to the admin group will be automatically assigned the admin role which allows him to access all the NF resource of CNC console that it supports
- Once done you can test authentication and authorization by logging into CNC Console GUI.
Note:
When the password of user is updated from CNCC-IAM and sent to LDAP, it is always sent in plain-text. This is different from updating the password to built-in CNCC-IAM database, when the hashing and salting is applied to the password before it is sent to DB. In the case of LDAP, the CNCC-IAM relies on the LDAP server to provide hashing and salting of passwords.Note:
Most of LDAP servers (Microsoft Active Directory, RHDS, FreeIPA) provide this by default. Some others (OpenLDAP, ApacheDS) may store the passwords in plain-text by default and you may need to explicitly enable password hashing for them.


