Database Tools MCP Servers
Policies for MCP Server
The Database Tools MCP Server policies depend on the following:
- the MCP Server runtime identity
- the Database Tools Connection runtime identity
- the database authentication method
- the policy scope (Resource or Compartment)
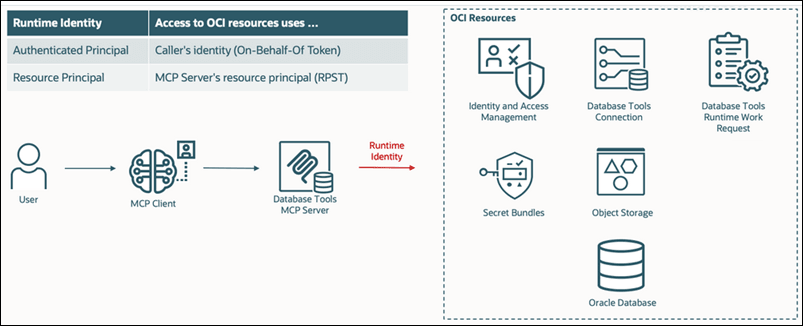
The following diagram shows how the Database Tools MCP Server uses the configured runtime identity to access OCI resources. Depending on the runtime identity configuration, OCI resource access is performed either using the authenticated user identity (On-Behalf-Of token) or the MCP Server resource principal.
Required IAM Permissions
IAM policies use the following syntax:
Allow <subject> to <verb> <resource-type> in <location> where <conditions>IAM policies define which users, groups, or resource principals can access MCP Server resources and related OCI services. The following table lists the IAM permissions required for the Database Tools MCP Server.
| Verb | Resource Type | Description | Required When | Subject | Location |
|---|---|---|---|---|---|
| use | database-tools-mcp-servers-invocation | Allows users to invoke the MCP Server | Always | MCP Users | Tenancy or Compartment |
| use | database-tools-connections | Allows use of Database Tools connections | Always | MCP Users or MCP Server | Tenancy or Compartment |
| use | database-tools-db-connect-obo | Allows the MCP Server to obtain database tokens on behalf of users | Using Token authentication | MCP Server | Tenancy |
| use | database-connections | Allows IAM-based database authentication | Using Token authentication | MCP Users | Tenancy or Compartment |
| use | database-tools-runtime-work-requests | Allows long-running asynchronous requests | Using asynchronous requests | MCP Users or MCP Server | Tenancy or Compartment |
| read | secret-bundles | Allows access to Vault secrets | Using password-based authentication or a key store | MCP Users or MCP Server or Connection | Tenancy or Compartment |
| use | buckets | Allows access to Object Storage buckets | Using asynchronous requests | MCP Users or MCP Server or Connection | Tenancy or Compartment |
| manage | objects | Allows object creation and management | Using asynchronous requests | MCP Users or MCP Server or Connection | Tenancy or Compartment |
Runtime Identity Models
The required policies depend on the runtime identity configuration.
-
MCP Server Runtime Identity
Determines which identity the MCP Server uses when accessing resources.
-
Authenticated_Principal: Requests run using the logged-in user identity.
-
Resource_Principal: Requests run using the MCP Server identity.
-
-
Connection Runtime Identity
Determines which identity is used for database access.
-
Authenticated_Principal: Database access uses the user identity.
-
Resource_Principal: Database access uses the Database Tools Connection resource identity.
-
-
Authentication Types
-
Token: Uses IAM token-based authentication.
-
Password: Uses database username and password authentication.
-
-
Policy Scope
Policies can be applied at either the resource level or compartment level.
-
Resource: Restricts access to a specific resource.
-
Compartment: Allows access to all matching resources in the compartment.
-
Policy Configurations
Choose the configuration that matches your deployment model.
Option 1
- MCP Server runtime identity: AUTHENTICATED_PRINCIPAL
- Connection runtime identity: AUTHENTICATED_PRINCIPAL
- Authentication type: TOKEN
Resource-Scope Policy Statements
allow any-user to use database-tools-db-connect-obo in tenancy
where request.principal.id = '<mcp-server-ocid>'
allow group '<domain_name>/<group_name>' to use database-tools-mcp-servers-invocation
in compartment <compartment_name> where target.resource.id = '<mcp-server-ocid>'
allow group '<domain_name>/<group_name>' to use database-connections
in compartment <compartment_name> where target.database.id = '<database-ocid>'
allow group '<domain_name>/<group_name>' to use database-tools-connections
in compartment <compartment_name> where target.resource.id = '<connection-ocid>'Optional: Required only when secrets or key stores are used.
allow group '<domain_name>/<group_name>' to read secret-bundles in compartment <compartment_name>
where target.secret.id = '<secret-ocid>'Compartment-Scope Policy Statements
allow any-user to use database-tools-db-connect-obo in tenancy
where all {request.principal.type = 'databasetoolsmcpserver',
request.principal.compartment.id = '<compartment-ocid>'}
allow group '<domain_name>/<group_name>' to use database-tools-mcp-servers-invocation
in compartment <compartment_name>
allow group '<domain_name>/<group_name>' to use database-connections
in compartment <compartment_name>
allow group '<domain_name>/<group_name>' to use database-tools-connections
in compartment <compartment_name>Optional: Required only when secrets or key stores are used.
allow group '<domain_name>/<group_name>' to read secret-bundles
in compartment <compartment_name>Option 2
- MCP Server runtime identity: AUTHENTICATED_PRINCIPAL
- Connection runtime identity: AUTHENTICATED_PRINCIPAL
- Authentication type: PASSWORD
Resource-Scope Policy Statements
allow group 'domain_name'/'group_name' to use database-tools-mcp-servers-invocation
in compartment <compartment_name> where target.resource.id = '<mcp-server-ocid>'
allow group 'domain_name'/'group_name' to use database-tools-connections in
compartment <compartment_name> where target.resource.id = '<connection-ocid>'
Optional: Required when password credentials are stored in Vault.
allow group 'domain_name'/'group_name' to read secret-bundles in compartment <compartment_name>
where any {
target.secret.id = '<secret-ocid-1>',
target.secret.id = '<secret-ocid-2>' }Compartment-Scope Policy Statements
allow group '<domain_name>/<group_name>' to use database-tools-mcp-servers-invocation
in compartment <compartment_name>
allow group '<domain_name>/<group_name>' to use database-tools-connections
in compartment <compartment_name>
Optional: Required when password credentials are stored in Vault.
allow group '<domain_name>/<group_name>' to read secret-bundles in compartment <compartment_name>Option 3
- MCP Server runtime identity: AUTHENTICATED_PRINCIPAL
- Connection runtime identity: RESOURCE_PRINCIPAL
- Authentication type: TOKEN
Resource-Scope Policy Statements
allow any-user to use database-tools-db-connect-obo in tenancy
where request.principal.id = '<mcp-server-ocid>'
allow group '<domain_name>/<group_name>' to use database-tools-mcp-servers-invocation
in compartment <compartment_name> where target.resource.id = '<mcp-server-ocid>'
allow group '<domain_name>/<group_name>' to use database-connections
in compartment <compartment_name> where target.database.id = '<database-ocid>'
allow group '<domain_name>/<group_name>' to use database-tools-connections
in compartment <compartment_name> where target.resource.id = '<connection-ocid>'
Optional: Required only for asynchronous requests, Vault access, or Object Storage.
--Work Requests
allow group '<domain_name>/<group_name>' to use database-tools-runtime-work-requests
in compartment <compartment_name>
where target.resource.created-by-principal-id = request.principal.id
--Vault Secrets
allow any-user to read secret-bundles in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.secret.id = '<secret-ocid>'}
--Object Storage
allow any-user to use buckets in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.bucket.name = '<bucket-name>'}
allow any-user to manage objects in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.bucket.name = '<bucket-name>'}Compartment-Scope Policy Statements
allow any-user to use database-tools-db-connect-obo in tenancy
where request.principal.id = '<mcp-server-ocid>'
allow group '<domain_name>/<group_name>' to use
database-tools-mcp-servers-invocation in compartment <compartment_name>
allow group '<domain_name>/<group_name>' to use
database-connections in compartment <compartment_name>
allow group '<domain_name>/<group_name>' to use
database-tools-connections in compartment <compartment_name>
Optional: Required only for asynchronous requests, Vault access, or Object Storage.
--Work Requests
allow group '<domain_name>/<group_name>' to use
database-tools-runtime-work-requests in compartment <compartment_name>
--Vault Secrets
allow any-user to read secret-bundles in compartment <compartment_name>
where request.principal.id = '<connection-ocid>'
--Object Storage
allow any-user to use buckets in compartment <compartment_name>
where request.principal.id = '<connection-ocid>'
allow any-user to manage objects in compartment <compartment_name>
where request.principal.id = '<connection-ocid>'Option 4
- MCP Server runtime identity: RESOURCE_PRINCIPAL
- Connection runtime identity: RESOURCE_PRINCIPAL
- Authentication type: PASSWORD
Resource-Scope Policy Statements
allow group '<domain_name>/<group_name>' to use database-tools-mcp-servers-invocation
in compartment <compartment_name> where target.resource.id = '<mcp-server-ocid>'
allow any-user to use database-tools-connections in compartment <compartment_name>
where all {
request.principal.id = '<mcp-server-ocid>',
target.resource.id = '<connection-ocid>'
}Optional: Required only for asynchronous requests, Vault secrets, or Object Storage.
--Work Requests
allow any-user to use database-tools-runtime-work-requests
in compartment <compartment_name>
where all {
request.principal.id = '<mcp-server-ocid>',
target.resource.created-by-principal-id = request.principal.id
}
--Vault Secrets
allow any-user to read secret-bundles in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.secret.id = '<secret-ocid-1>'
}
allow any-user to read secret-bundles in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.secret.id = '<secret-ocid-2>'
}
--Object Storage
allow any-user to use buckets in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.bucket.name = '<bucket-name>'
}
allow any-user to manage objects in compartment <compartment_name>
where all {
request.principal.id = '<connection-ocid>',
target.bucket.name = '<bucket-name>'
}Compartment-Scope Policy Statements
allow group '<domain_name>/<group_name>' to use database-tools-mcp-servers-invocation
in compartment <compartment_name>
allow any-user to use database-tools-connections in compartment <compartment_name>
where request.principal.id = '<mcp-server-ocid>'Optional: Required only for asynchronous requests, Vault secrets, or Object Storage.
--Work Requests
allow any-user to use database-tools-runtime-work-requests in compartment <compartment_name>
where request.principal.id = '<mcp-server-ocid>'
--Vault Secrets
allow any-user to read secret-bundles in compartment <compartment_name>
where request.principal.id = '<connection-ocid>'
--Object Storage
allow any-user to use buckets in compartment <compartment_name>
where request.principal.id = '<connection-ocid>'
allow any-user to manage objects in compartment <compartment_name>
where request.principal.id = '<connection-ocid>'Use these service-specific variables in IAM policy conditions to restrict access to specific resources, for example, a particular Vault secret or Object Storage bucket.
| Resource | Variable |
|---|---|
| Database Tools Connection | target.resource.id |
| Database Tools MCP Server | target.resource.id |
| Database Connection | target.resource.id |
| Autonomous Database |
target.id |
| Autonomous Database Dedicated |
target.database.id |
| Pluggable Database | Only the general
variables are supported.
For more information, see Details for the Database Service. |
| Vault Secret | target.secret.id
See Details for Vault, Key Management and Secret Management Service. |
| Object Storage |
target.bucket.name target.object.name |
Least-Privilege IAM Policies for MCP Administrators
This section describes the IAM policies and identity domain roles that are required for administrators to manage Database Tools MCP Servers, Toolsets and Connections.
Default Domain
To manage MCP Servers, a user must belong to an IAM group in the Default Identity Domain that is granted the policies listed below.
Replace <group_name> and <compartment> with your values.
| Policy | Access Level |
|---|---|
| allow group <group_name> to manage database-tools-mcp-family in compartment <compartment> | Manage Database Tools MCP Servers, MCP Toolsets, Database Tools Connections and Database Tools Private Endpoints |
| allow group <group_name> to use vaults in compartment <compartment> | Required to work with Vault resources used for secrets. |
| allow group <group_name> to use keys in compartment <compartment> | Required to work with Vault encryption keys used by secrets. |
| allow group <group_name> to manage secret-family in compartment <compartment> | Create, update, and delete Vault secrets referenced by connections or MCP Server configuration. |
| allow group <group_name> to manage virtual-network-family in compartment <compartment> | Required to create and manage Database Tools private endpoints. |
| allow group <group_name> to read autonomous-database-family in compartment <compartment> | Required to get display name of Autonomous Database. |
| allow group <group_name> to read database-family in compartment <compartment> | Required to get display name of databases and pluggable databases. |
| allow group <group_name> to manage domain in compartment <compartment> | Required only if you need to register MCP clients
(for example, create integrated applications) in an identity
domain.
You do not need all the permissions granted by manage domain, only the permission DOMAIN_RESOURCES_ADMINISTER is required. |
For a user in a specific identity domain, the following table lists the required policy statements.
| Policy | Access Level |
|---|---|
| allow group <identity_domain_name>/<group_name> to manage database-tools-mcp-family in compartment <compartment> | Manage Database Tools MCP Servers, MCP Toolsets, Database Tools Connections and Databse Tools Private Endpoints |
| allow group <identity_domain_name>/<group_name> to use vaults in compartment <compartment> | Required to work with Vault resources used for secrets. |
| allow group<identity_domain_name>/<group_name> to use keys in compartment <compartment> | Required to work with Vault encryption keys used by secrets. |
| allow group <identity_domain_name>/<group_name> to manage secret-family in compartment <compartment> | Create, update, and delete Vault secrets referenced by connections or MCP Server configuration. |
| allow group <identity_domain_name>/<group_name> to manage virtual-network-family in compartment <compartment> | Required to create and manage Database Tools private endpoints. |
| allow group <identity_domain_name>/<group_name> to read autonomous-database-family in compartment <compartment> | Required to get display name of Autonomous Database. |
| allow group <identity_domain_name>/<group_name> to read database-family in compartment <compartment> | Required to get display name of databases and pluggable databases. |
Identity Domain Roles
To manage MCP Clients of MCP Servers a, user in an Identity Domain requires the Application Administrator or the Identity Domain Administrator role.
See Assigning Users to Roles for information about assigning users to administrator roles.
| Role | Description |
|---|---|
| Application Administrator | Application Administrators can manage applications in identity domain. They can create, update, activate, deactivate, and delete applications. |
| Identity Domain Administrator | Identity domain administrators have superuser privileges for an identity domain. They can manage users, groups, applications, and system configuration settings. |
MCP Server Administrator Tools
To use the MCP Server Administrator Tools, you must have the
MCP_Administrator role and the required IAM polices to perform
the requested operation.
| Tool Name | Required Information |
|---|---|
| listCustomRoles | - |
| updateCustomRoles | - |
| createMcpToolset | Compartment Id is optional. Defaults to the MCP Server Compartment Id |
| readMcpToolset | Only reads the MCP Toolset related to the specific MCP Server. |
| updateMcpToolset | Only updates the MCP Toolset related to the specific MCP Server. |
| deleteMcpToolset | Only deletes the MCP Toolset related to the specific MCP Server. |
| listMcpToolset |
Compartment Id is optional. Defaults to the MCP Server Compartment Id. Only returns the MCP Toolset of the specific MCP Server. |
| searchMcpToolset |
Only returns the MCP Toolset of the specific MCP Server. |
| moveMcpToolset | The target Compartment Id is required. |
| createSqlReport |
Compartment Id is optional. Defaults to the MCP Server Compartment Id. |
| readSqlReport | SQL Report Id is required. |
| updateSqlReport | SQL Report Id is required. |