Understanding JSON Web Token Authentication
To provide single sign on access using JD Edwards EnterpriseOne and any JWT producing authority, including Oracle Mobile Cloud Service, you need to configure the EnterpriseOne Server trust of the HTML Server, add an existing certificate to a new keystore, and then configure the HTML Server with a certificate. These configurations allow you to establish a trust relationship between a token provider (such as Mobile Cloud Service) and an EnterpriseOne AIS Server and HTML Server.
For authentication with a JWT, the following must take place:
The public key certificate used for token generation by the third party must be provided.
You must store this certificate in a secure Java keystore (.jks) and upload it to the EnterpriseOne HTML Server.
You must configure the EnterpriseOne HTML Server with the keystore name, keystore password, and certificate alias.
Principal passed in the JWT must match the EnterpriseOne user ID.
You must configure the EnterpriseOne HTML Server as a trusted node through a single sign-on trust configuration.
#u30143895__CEGCCIEB shows the authentication flow in an environment in which JWT is used for authentication.
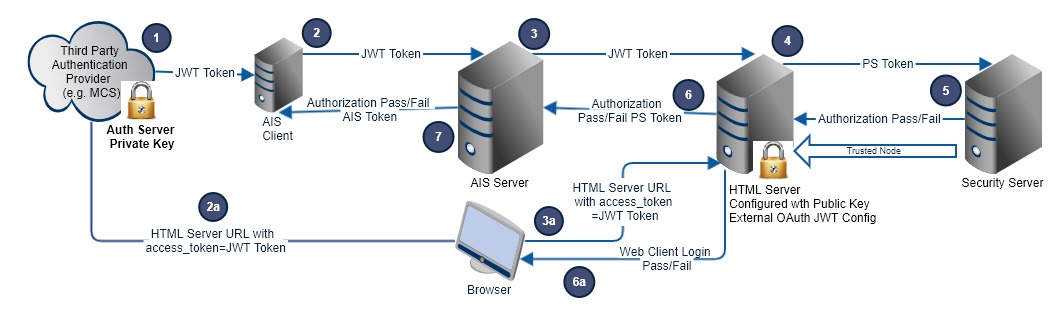
The following steps describe the authentication flow:
A JWT is generated with the private key and sent in the Bearer header of an AIS token request. (Stateless requests are also supported).
The JWT is forwarded to the EnterpriseOne HTML Server by the AIS Server in the Bearer if login is required, and the AIS Server is configured to allow a JWT.
The JWT is validated against the public key, the token timeout is validated, and the principal (user) is extracted from the JWT payload. A PS Token is generated for that user and sent for authorization by the Security Server (EnterpriseOne Enterprise Server).
The Security Server checks the PS token with SSO node trust, and then an authorization response is returned to the EnterpriseOne HTML Server.
The authorization response is returned to the AIS Server. The PS Token is included in the response.
The authorization response is returned to the AIS client (third-party). If passed, for a token request the response includes an AIS token.