Specify Custom Header Security Values to Authenticate with Endpoint Applications
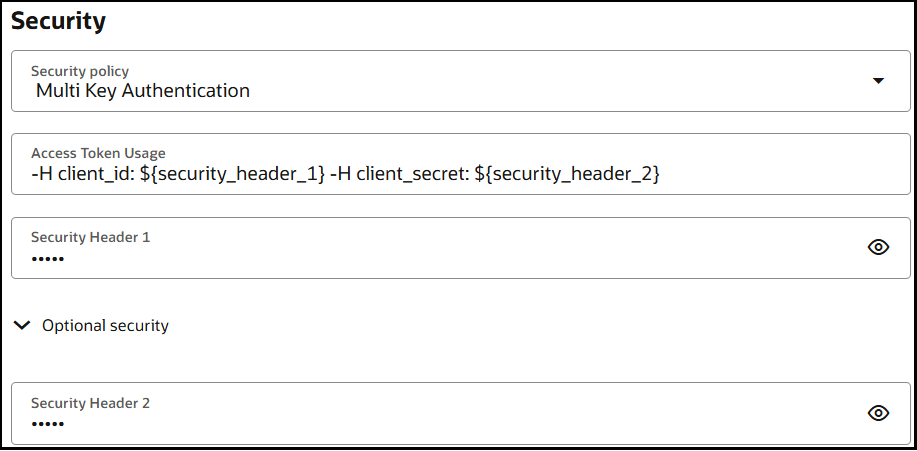
You can use the Multi Key Authentication security policy to specify custom header security values in your REST Adapter invoke connection to use to authenticate with your endpoint application. These values are included in the HTTP request header at runtime.
Instead of only the following setting appearing in the HTTP
request.
Authorization: Bearer tokenYou can specify up to five custom security headers in the HTTP request
during connection
creation:
client_id: value
client_secret: value
x-request-id: value
x-signature: hash
timestamp: valueWhere:
client_id: Identifies the consumer.client_secret: Authenticates the consumer.x-request-id: Performs traceability.signature: Ensures request integrity.timestamp: Prevents replay attacks.
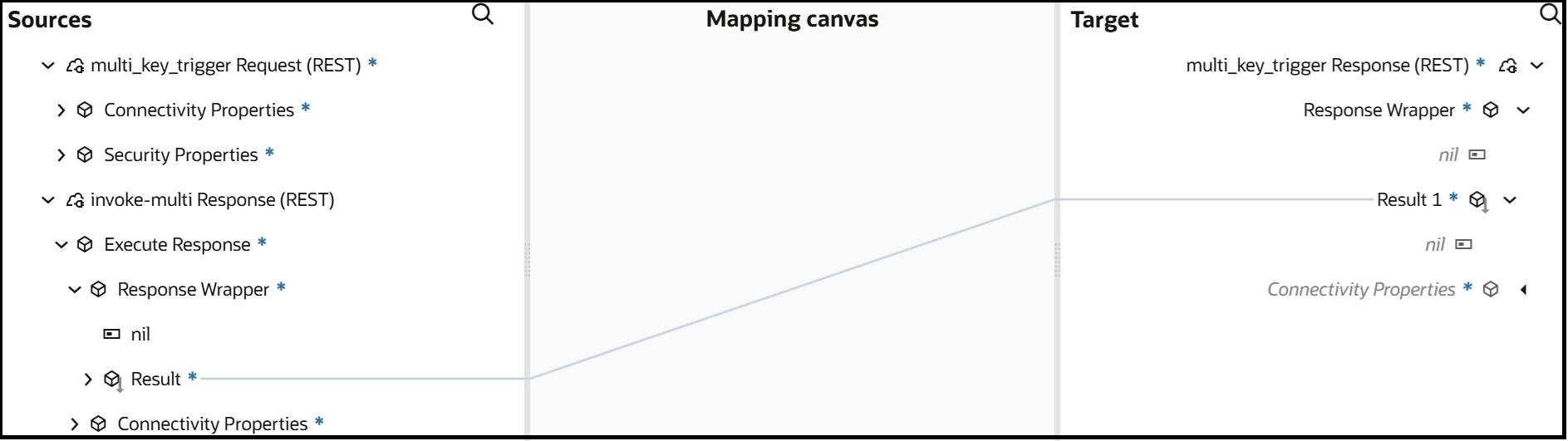
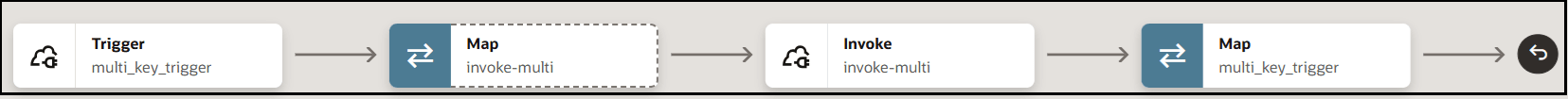
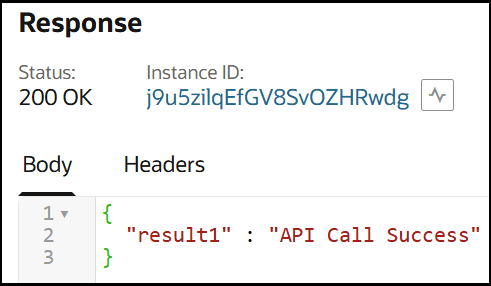
The following use case provides an overview of creating and
running an integration in which two headers (client_id and
client_secret) are specified during connection creation to
authenticate with the endpoint application at runtime.