Add Security Rules
If you plan to manually connect to your database via an Oracle Data Safe private endpoint, prior to registering your database, you need to add security rules to your virtual cloud network (VCN) to allow communication between your database and Oracle Data Safe. The private endpoint essentially represents the Oracle Data Safe service in your VCN with a private IP address in a subnet of your choice.
Overview
If your database resides in Oracle Cloud Infrastructure (OCI), you need to add an ingress security rule and an egress security rule to your database’s virtual cloud network’s (VCN’s) security lists or network security group (NSG) in OCI. Both stateful and stateless security rules are allowed. The ingress and egress rules do not need to be stored within the same security list, network security group, or same compartment.
-
The ingress security rule allows your database to receive incoming traffic from the Oracle Data Safe private endpoint.
-
The egress security rule allows the Oracle Data Safe private endpoint to send requests to the database.
If your database resides outside of OCI, you only need to add an egress security rule in OCI. You do not need to add an ingress security rule; however, in your own network environment, you need to allow your database to receive traffic from the Oracle Data Safe private endpoint.
There are two approaches that you can take when adding the security rules in OCI. The first approach is to allow communication between the Oracle Data Safe private endpoint and all database IP addresses within the same subnet (0.0.0.0/0) in OCI. With this configuration, the Oracle Data Safe private endpoint can connect to all of your databases in the subnet.
The other approach is to be more specific by configuring separate ingress and egress security rules as follows:
-
Ingress security rule: In the NSG or security list for your database, add an ingress rule that allows your database's private endpoint IP address on the database's port to receive incoming traffic from Oracle Data Safe's private endpoint IP address from all ports.
-
Egress security rule: In the NSG or security list for your Oracle Data Safe private endpoint, add an egress rule that allows Oracle Data Safe's private endpoint IP address on all ports to send requests to the database's private endpoint IP address on the database's port. If the database has multiple IP addresses, you need configure an egress rule for each IP address.
For more information about security lists and network security groups, see Access and Security in the Oracle Cloud Infrastructure documentation.
Security Rules for Autonomous AI Databases
For an Autonomous AI Database that uses an Oracle Data Safe private endpoint, you need to add an ingress security rule and egress security rule in Oracle Cloud Infrastructure.
-
Obtain the private IP address and NSG or security list for your database.
-
You can find the network information under Network on your database's page in the Oracle Cloud Infrastructure Console.
-
(Autonomous AI Database on Dedicated Exadata Infrastructure) Obtain the subnet or floating IP addresses (if known) and the name of the NSG or security list for your database. There can be up to 8 floating IP addresses for the database nodes.
-
-
Obtain the private IP address and NSG or security list for your Oracle Data Safe private endpoint.
- You can find the network information for your Oracle Data Safe private endpoint on the Private endpoint information page in the Oracle Data Safe service in Oracle Cloud Infrastructure.
-
Open the VCN for your database.
-
Create an ingress security rule in your database's NSG or security list.
-
Example for Autonomous AI Database Serverless with Private Endpoint Access Only: The database private endpoint IP address (10.0.0.112/32) on port 1522 receives incoming traffic from Oracle Data Safe's private endpoint IP address (10.0.0.79/32) from all ports.
-
Example for Autonomous AI Database on Dedicated Exadata Infrastructure: The Database private endpoint on port 2484 receives incoming traffic from Oracle Data Safe's private endpoint IP address (from all ports).
-
-
Create an egress security rule in your Oracle Data Safe private endpoint's NSG or security list.
-
Example for Autonomous AI Database Serverless with Private Endpoint Access Only: Oracle Data Safe's private endpoint IP address (10.0.0.79/32) on all ports sends requests to the database's private endpoint IP address (for example, 10.0.0.112/32) on the database's port (1522).
-
Example 1 for Autonomous AI Database on Dedicated Exadata Infrastructure: Oracle Data Safe's private endpoint (from all ports) sends requests to all IP addresses on the database's subnet on port 2484.
-
Example 2 for Autonomous AI Database on Dedicated Exadata Infrastructure: The egress rule for each floating IP address allows the Oracle Data Safe private endpoint (from all ports) to send requests to the floating IP address on port 2484.
-
Security Rules for Oracle Cloud Databases
For an Oracle Cloud Database, you need to add an ingress security rule and an egress security rule in Oracle Cloud Infrastructure.
-
Obtain the IP address(es) and NSG name for your database's private endpoint.
-
You can find your database information in your database's Console in Oracle Cloud Infrastructure.
-
A bare metal or vitual machine DB system has one private IP address.
-
Oracle Exadata Database Service on Dedicated Infrastructure can have multiple floating IP addresses for the database nodes. It can also have scan IP addresses for the database system. Oracle recommends that you use one of the scan IP addresses. You can find a scan IP address under Network on the DB System Information tab in Oracle Cloud Infrastructure. Alternatively, you can enter the private floating IP address of any one of the database nodes.
-
-
Obtain the private IP address and NSG name for the Oracle Data Safe private endpoint.
- You can find the Oracle Data Safe private endpoint information on the Private endpoint information page in the Oracle Data Safe service in Oracle Cloud Infrastructure.
-
Open the VCN for your database.
-
Create an ingress rule in your database's NSG.
- Example: The database private endpoint IP address (10.0.0.112/32) on port 1521 receives incoming traffic from Oracle Data Safe's private endpoint IP address (10.0.0.79/32) from all ports.
-
Create an egress rule in your Oracle Data Safe private endpoint's NSG.
-
Example: Oracle Data Safe's private endpoint IP address (10.0.0.79/32) on all ports sends requests to the database's private endpoint IP address (10.0.0.112/32) on port 1521.
-
(Oracle Exadata Database Service on Dedicated Infrastructure) Use one of the scan IP addresses for the database or use the private floating IP address of any one of the database nodes. The database port number is 1521.
-
Security Rules for Oracle Cloud@Customer Databases
For an Oracle Cloud@Customer database that uses an Oracle Data Safe private endpoint, you need to create an egress security rule in Oracle Cloud Infrastructure.
Note: You do not need to create an ingress security rule in Oracle Cloud Infrastructure. Instead, configure your own network to allow your database to receive traffic from the Oracle Data Safe private endpoint.
-
Obtain the IP address(es) and NSG name for your database's private endpoint.
-
Obtain the private IP address and NSG name for the Oracle Data Safe private endpoint.
- You can find the Oracle Data Safe private endpoint information on the Private endpoint information page in the Oracle Data Safe service in Oracle Cloud Infrastructure.
-
Open the VCN for your database.
-
Create an egress rule in the NSG or security list for Oracle Data Safe private endpoint.
-
(Oracle Exadata Database Service on Cloud@Customer Database) Configure the rule to allow communication between the Oracle Data Safe private endpoint (from any port) and all database server VIPs and SCAN addresses (all three). Always include the database server VIPs in the egress security rule. By default, every deployment of Oracle Exadata Database Service on Cloud@Customer is associated with a Single Client Access Name (SCAN), and the SCAN is associated with 3 IP addresses. Each database system configuration contains compute nodes (database servers). There is one database server VIP address per compute node in the VM cluster.
-
Example for Oracle Exadata Database Service on Cloud@Customer: The egress rule allows the Oracle Data Safe private endpoint (from any port) to send requests to two database server VIPs ( 1.1.1.3 and 1.1.1.5) and three SCAN addresses (1.1.1.6, 1.1.1.7, and 1.1.1.8) on port 1521.
The following diagram illustrates the Oracle Data Safe private endpoint, the database, and the egress security rule.
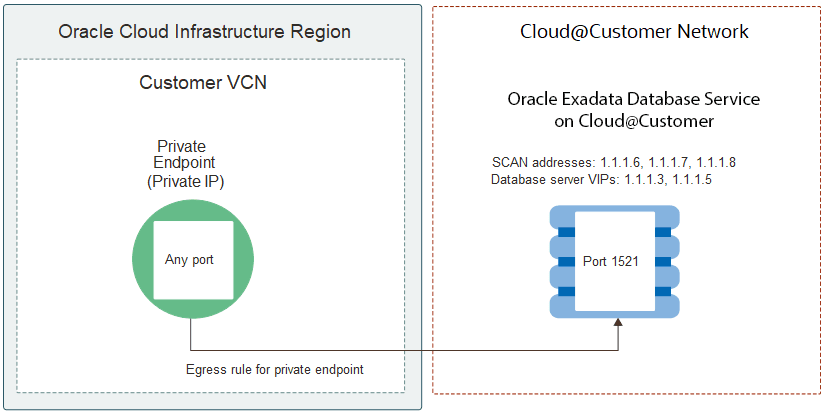
Description of the illustration exacc-egress-rule.png
The following screenshot shows you the Oracle Exadata Database Service on Cloud@Customer network configuration for the VM cluster in Oracle Cloud Infrastructure, where you can find the SCAN addresses and database server VIPs.
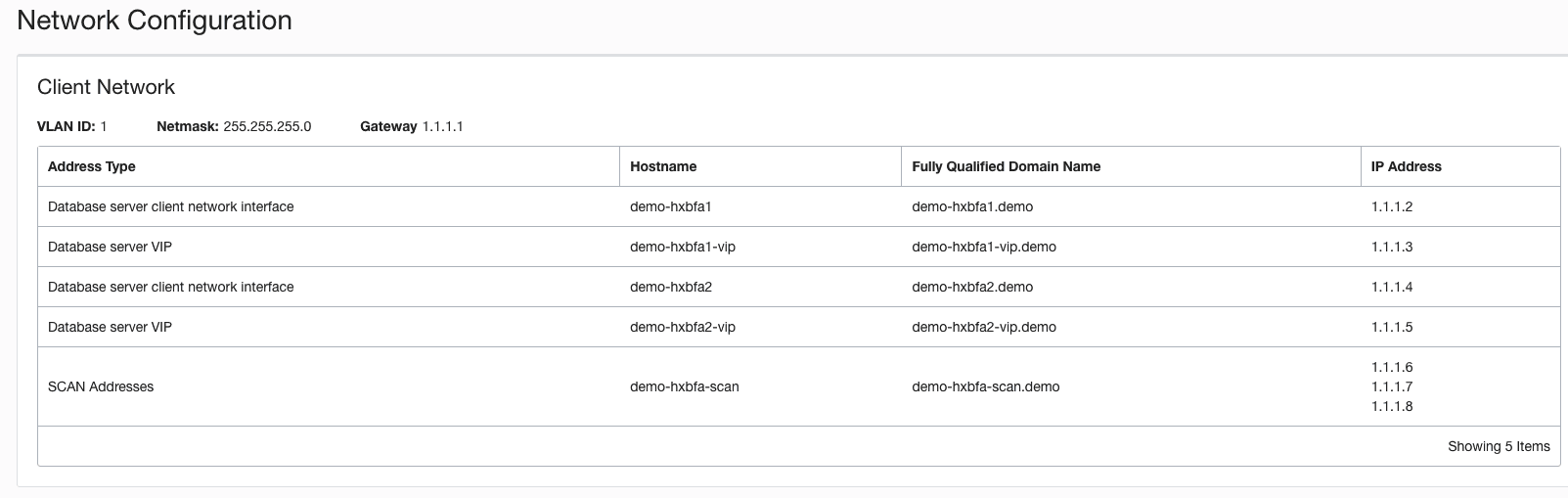
Description of the illustration exacc-network-configuration.png
-
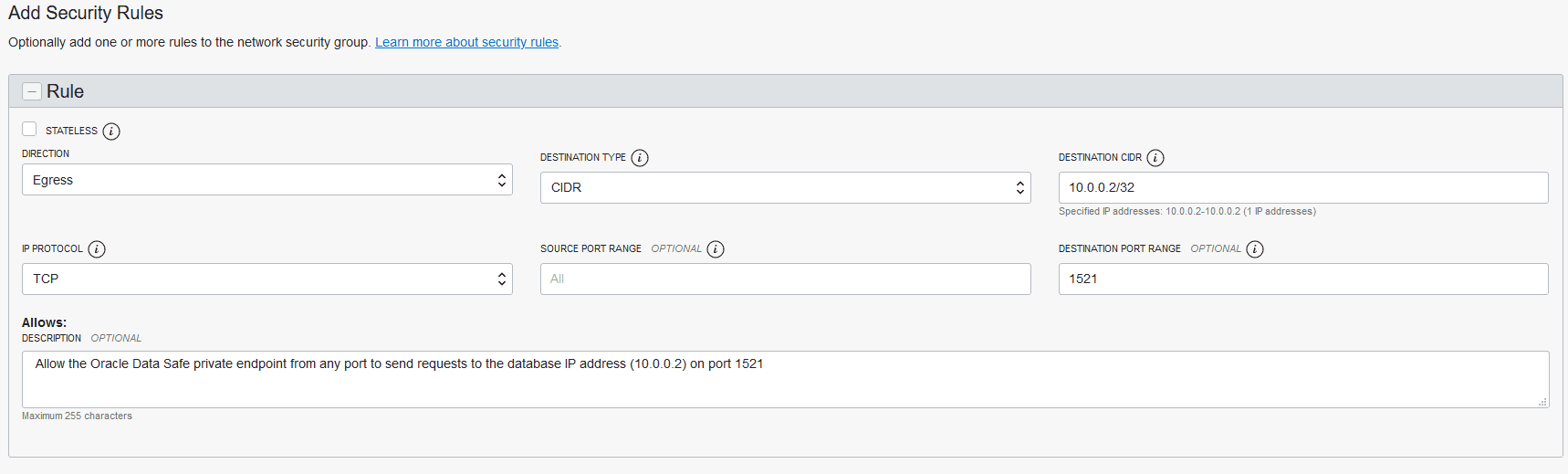
Security Rule for On-Premises Oracle Databases
If you are using an Oracle Data Safe private endpoint to connect to your on-premises Oracle database, you need to create an egress security rule in the virtual cloud network (VCN) of your private endpoint.
Note: You do not need to create an ingress security rule in Oracle Cloud Infrastructure. Instead, configure your own network to allow your database to receive traffic from the Oracle Data Safe private endpoint.
-
Obtain the private IP address of your on-premises Oracle database.
-
The IP address is where the Oracle database listener is running (for example, 10.0.0.2).
-
For a Real Application Cluster (RAC) database, you need to specify the IP addresses for the RAC database nodes and not the SCAN IP addresses. Whether you specify all the nodes in your RAC database depends on how you configured your pluggable databases (PDBs).
-
-
Obtain the private IP address and the name of the NSG or security list for your Oracle Data Safe private endpoint.
- You can find the Oracle Data Safe private endpoint information on the Private endpoint information page in the Oracle Data Safe service in Oracle Cloud Infrastructure.
-
Create an egress security rule in the NSG or security list for your Oracle Data Safe private endpoint.
-
Example: The egress rule allows Oracle Data Safe's private endpoint IP address (10.0.0.79/32) on all ports to send requests to the database's private IP address (10.0.0.2/32) on the database's port 1521.
-
Security Rules for Oracle Databases on Compute Instances
If your database resides in Oracle Cloud Infrastructure (OCI), you need to add an ingress security rule and egress security rule. If your database resides outside of OCI, create an egress security rule in Oracle Cloud Infrastructure and configure your own network to allow your database to receive traffic from the Oracle Data Safe private endpoint.
-
Obtain the IP address and the name of the NSG or security list for your database's private endpoint.
- You can find your database information in your database's Console in Oracle Cloud Infrastructure
-
Obtain the IP address and the name of the NSG or security list for the Oracle Data Safe private endpoint.
- You can find the Oracle Data Safe private endpoint information on the Private endpoint information page in the Oracle Data Safe service in Oracle Cloud Infrastructure.
-
Create an ingress security rule in the VCN for your database, either in Oracle Cloud Infrastructure or in a non-Oracle cloud environment.
-
Example: The ingress rule allows your database's private endpoint IP address (10.0.0.112/32) on the database's port 1521 to receive incoming traffic from Oracle Data Safe's private endpoint IP address (10.0.0.79/32) from all ports.
-
If your database resides outside of OCI, configure your own network to allow your database to receive traffic from the Oracle Data Safe private endpoint.
-
-
Create an egress security rule in the VCN for your Oracle Data Safe's private endpoint in Oracle Cloud Infrastructure.
- Example: The egress rule allows Oracle Data Safe's private endpoint IP address (10.0.0.79/32) on all ports to send requests to the database's private endpoint IP address (10.0.0.112/32) on the database's port 1521.
Security Rule for Amazon RDS for Oracle
If you are using an Oracle Data Safe private endpoint to connect to your Amazon RDS for Oracle database, you need to create an egress security rule in the virtual cloud network (VCN) of your private endpoint.
Note: You do not need to create an ingress security rule in Oracle Cloud Infrastructure. Instead, configure your own network to allow your database to receive traffic from the Oracle Data Safe private endpoint.
-
Obtain the private IP address of your Amazon RDS for Oracle database.
-
Obtain the private IP address and the name of the NSG or security list for your Oracle Data Safe private endpoint.
- You can find the Oracle Data Safe private endpoint information on the Private endpoint information page in the Oracle Data Safe service in Oracle Cloud Infrastructure.
-
Create an egress security rule in the NSG or security list for your Oracle Data Safe private endpoint.
- Example: The egress rule allows Oracle Data Safe's private endpoint IP address (10.0.0.79/32) on all ports to send requests to the database's private IP address (10.0.0.2/32) on the database's port 1521.