Generate a Dependency Vulnerability Analysis Report
You can configure a job to generate a Dependency Vulnerability Analysis (DVA) report for a Maven, Node.js/Javascript, or Gradle application. This report can help you analyze any publicly known vulnerabilities in the application's dependencies.
WARNING:
The DVA report functionality is being deprecated and will no longer be supported in the next release of Visual Builder Studio. As of 26.07, the DVA report will be unavailable.When a build runs, VB Studio scans the job's POM file (Maven), package.json file (Node.js/Javascript), or build.gradle file (Gradle) and checks the direct and transitive dependencies against the National Vulnerability Database (NVD). See https://nvd.nist.gov/ to find more about NVD.
- NPM: Data may be retrieved from the NPM Public Advisories,
https://www.npmjs.com/advisories. - RetireJS: Data may be retrieved from the RetireJS community,
https://retire.js/github.io/retire.js/. - Sonatype OSS Index: Data may be retrieved from the Sonatype OSS Index.
https://sonatype.ossindex.org.
For any vulnerabilities found, you can configure the job to mark the build as failed or file an issue. If email notifications have been enabled or if a Slack webhook has been configured, you can be notified about these actions through email or Slack.
To configure a job to scan for security vulnerabilities:
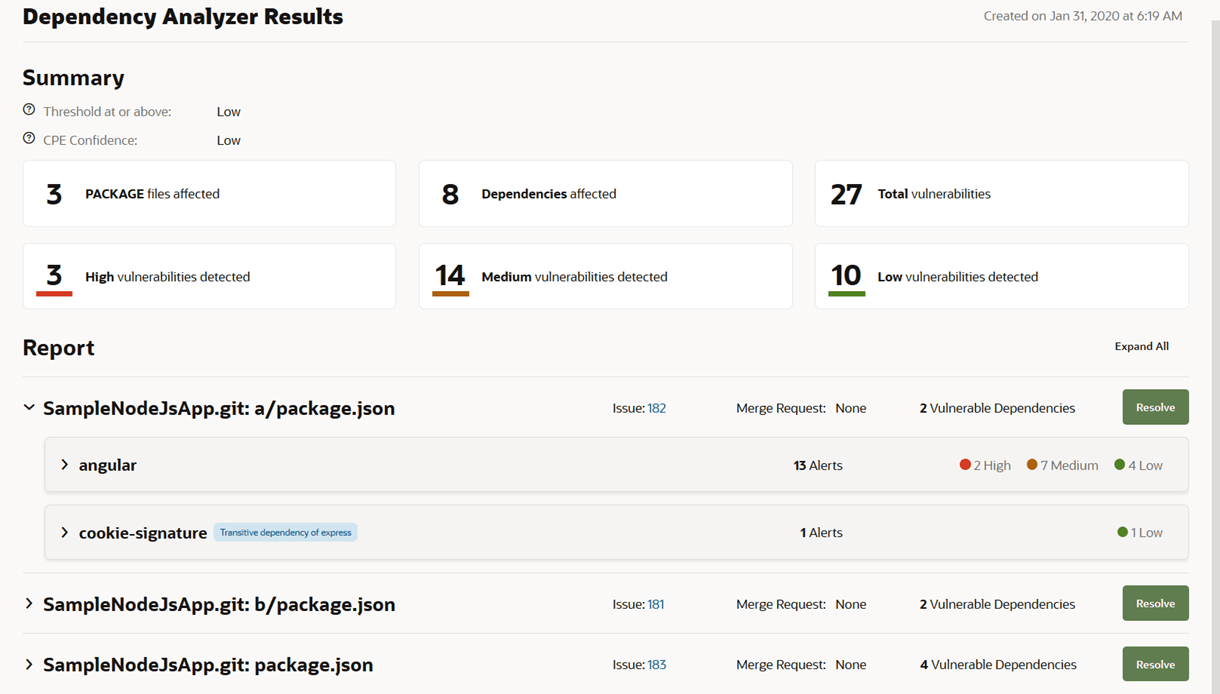
- Issue ID, if the Create issue for every affected file check box was selected. Click the issue link to open it.
You can also open the Project Home page and check the recent activities feed about the issue's create notification. You should see a message that an issue was created, such as System created Defect 2: Vulnerabilities in -MavenJavaApp. If an issue was previously created for the vulnerability, a comment will be added to the issue and a message like System commented Defect 2: Vulnerabilities in - MavenJavaApp will be added to the activities feed.
- Merge request ID, if the Resolve button was clicked to resolve the vulnerabilities. Click the merge request link to open it.
- Number of vulnerabilities
- Name of each dependency where a vulnerability is found
- Each dependency's type (direct or transitive)
A transitive dependency displays a Transitive label next to the name. A direct dependency displays no label.
- Number of alerts and alert categories of vulnerabilities (High, Medium, or Low)
- Expand each dependency to view its vulnerabilities
To mute a vulnerability's alerts, expand the vulnerability in the Report section, and click Mute in Alerts. In the Mute Vulnerability dialog box, review the details, and click Mute. The muted vulnerability won't be reported during the next run and it will not cause the build to fail. It will simply be included in the report as a muted vulnerability that should be used only for reference or to be unmuted and dealt with at some future time.
Muted vulnerabilities will only show up in a report for the latest build, not in reports for any previous builds.
To fix a reported vulnerability, use Resolve and the dropdown menu in the analysis tool to change the dependency's version to one that doesn't have the vulnerability.