Security model
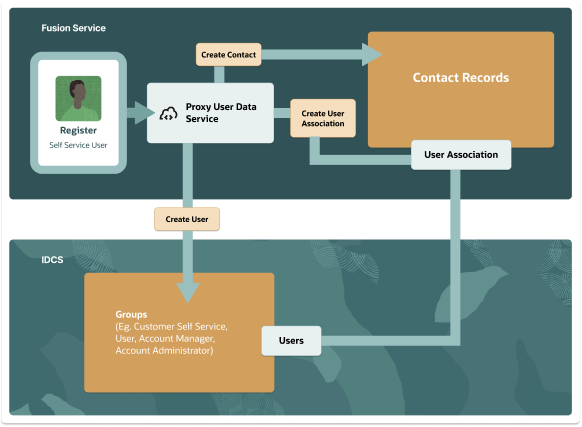
Contact records created in Fusion Service and users created in IDCS, map to a few proxy users that are created during initial setup.
The proxy users define the functional privileges that are accessible to the users.
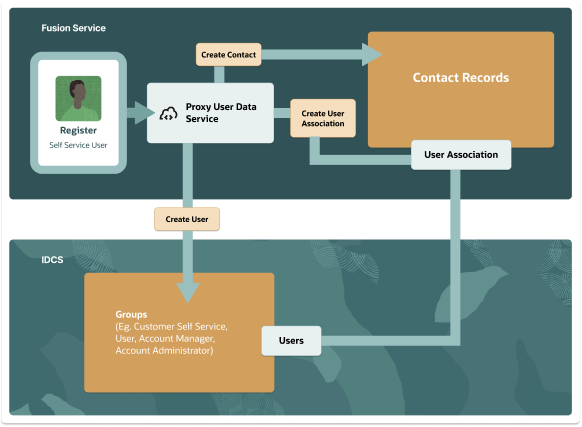
Contact records created in Fusion Service and users created in IDCS, map to a few proxy users that are created during initial setup.
The proxy users define the functional privileges that are accessible to the users.