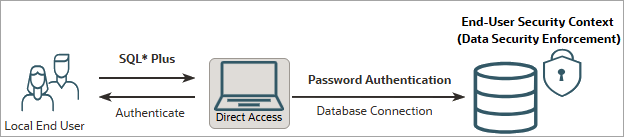
6.1 Local End Users Connecting Directly
In this scenario, end users are created and managed in the database, and connect using a SQL client (for example, SQL*Plus) and password-based authentication. No application or IAM system is involved.
Use case
Because it is the simplest scenario to configure, this setup is ideal for development and testing environments, product demonstrations, or applications with a small, manageable number of users who connect directly to the database.
Database authentication flow
Prerequisite setup: To enable Deep Sec for this scenario, you must create an end-user account identified by password in the database and assign it data roles that are managed locally. In addition, you must grant the end user the system privilege to create a database session.
The runtime flow is as follows:
- User login: The end user connects directly to the database using their user name and password.
- Database authentication: The database authenticates the user against their local end-user account.
- Security context establishment: Upon successful connection, the database establishes an end-user security context. The end user's granted data roles are activated, and the corresponding data grants are enforced for all subsequent SQL operations of the end user.
Configuration path
- Configure the database for local end-user authentication. See Set Up Local Authentication for Direct Logon.
Example configuration
For a step-by-step example of this configuration, see Configure Oracle Deep Data Security for Direct Logon with Local End Users.