Integrating CNC Console LDAP Server with CNC Console IAM
Overview
The CNC Console IAM can be used as an integration platform to connect it into existing LDAP and Active Directory servers.
User Federation in CNC Console-IAM let the user to sync users and groups from LDAP and Active Directory servers and assign roles respectively.
Sample LDAP ldif Filedn: dc=oracle,dc=org
objectclass: top
objectclass: domain
objectclass: extensibleObject
dc: oracle
dn: ou=groups,dc=oracle,dc=org
objectclass: top
objectclass: organizationalUnit
ou: groups
dn: ou=people,dc=oracle,dc=org
objectclass: top
objectclass: organizationalUnit
ou: people
dn: uid=ben,ou=people,dc=oracle,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: Ben Alex
sn: Alex
uid: ben
userPassword: benspass
dn: uid=bob,ou=people,dc=oracle,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: Bob Hamilton
sn: Hamilton
uid: bob
userPassword: bobspass
dn: uid=joe,ou=people,dc=oracle,dc=org
objectclass: top
objectclass: person
objectclass: organizationalPerson
objectclass: inetOrgPerson
cn: Joe Smeth
sn: Smeth
uid: joe
userPassword: joespass
dn: cn=admin,ou=groups,dc=oracle,dc=org
objectclass: top
objectclass: groupOfUniqueNames
cn: admin
uniqueMember: uid=ben,ou=people,dc=oracle,dc=org
ou: admins
dn: cn=scp,ou=groups,dc=oracle,dc=org
objectclass: top
objectclass: groupOfUniqueNames
cn: scp
uniqueMember: uid=ben,ou=people,dc=oracle,dc=org
uniqueMember: uid=joe,ou=people,dc=oracle,dc=org
ou: scpusers
dn: cn=nrf,ou=groups,dc=oracle,dc=org
objectclass: top
objectclass: groupOfUniqueNames
cn: nrf
uniqueMember: uid=ben,ou=people,dc=oracle,dc=org
uniqueMember: uid=bob,ou=people,dc=oracle,dc=org
ou: nrfusersSetting up User Federation with CNC Console IAM (LDAP Server integration)
- Go to CNCC IAM console
http://<cncc-iam-ingress-ip>:<cncc-iam-ingress-port> and
login using admin credentials provided during installation of CNCC IAM.
- Select Realm Settings and
click Add realm under
Cncc. Click the User Federation in the left pane. The User Federation screen
appears in the right pane.
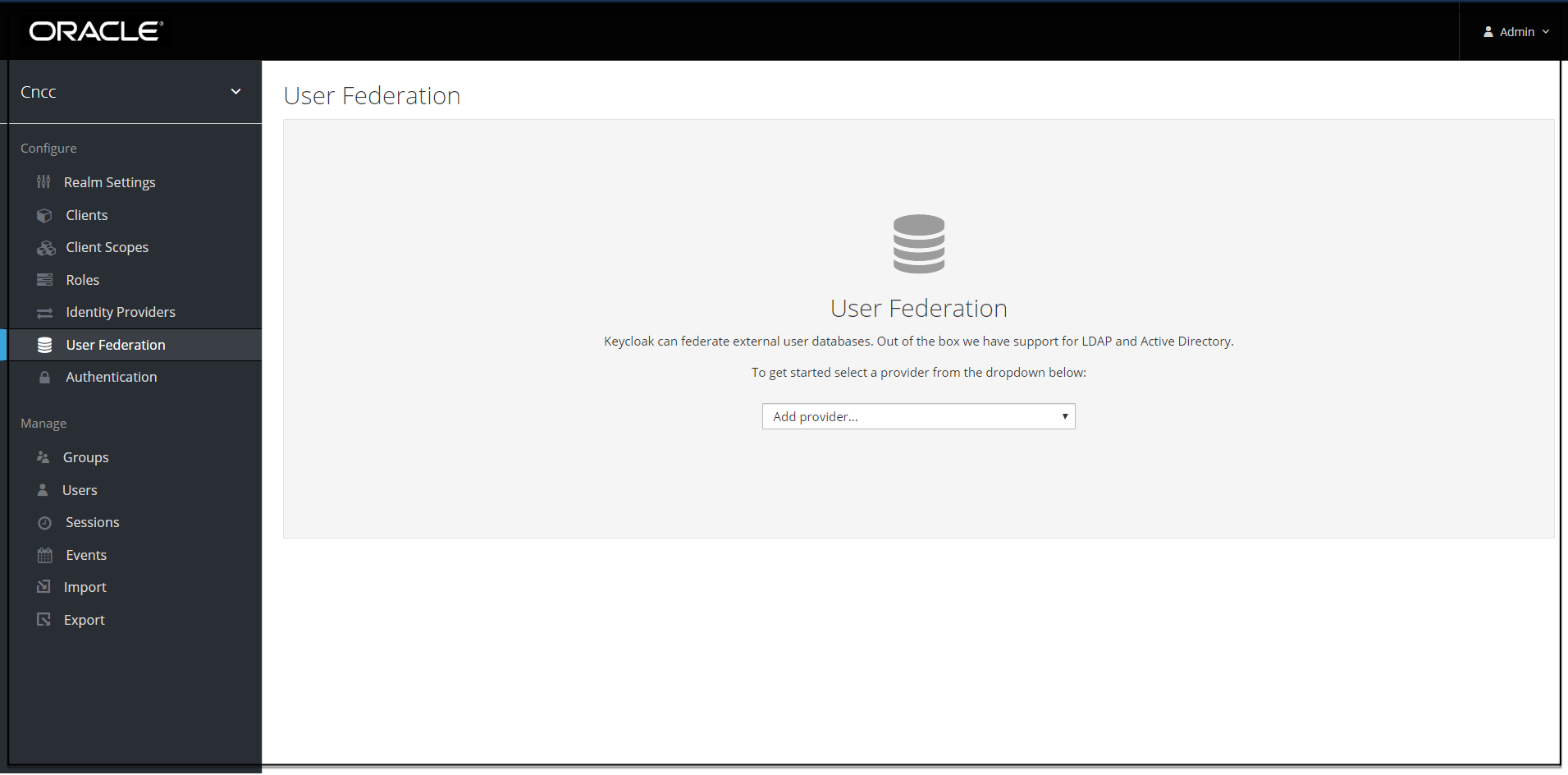
- From the drop down list in the User federation screen select ldap, the Add user federation
provider screen appears.
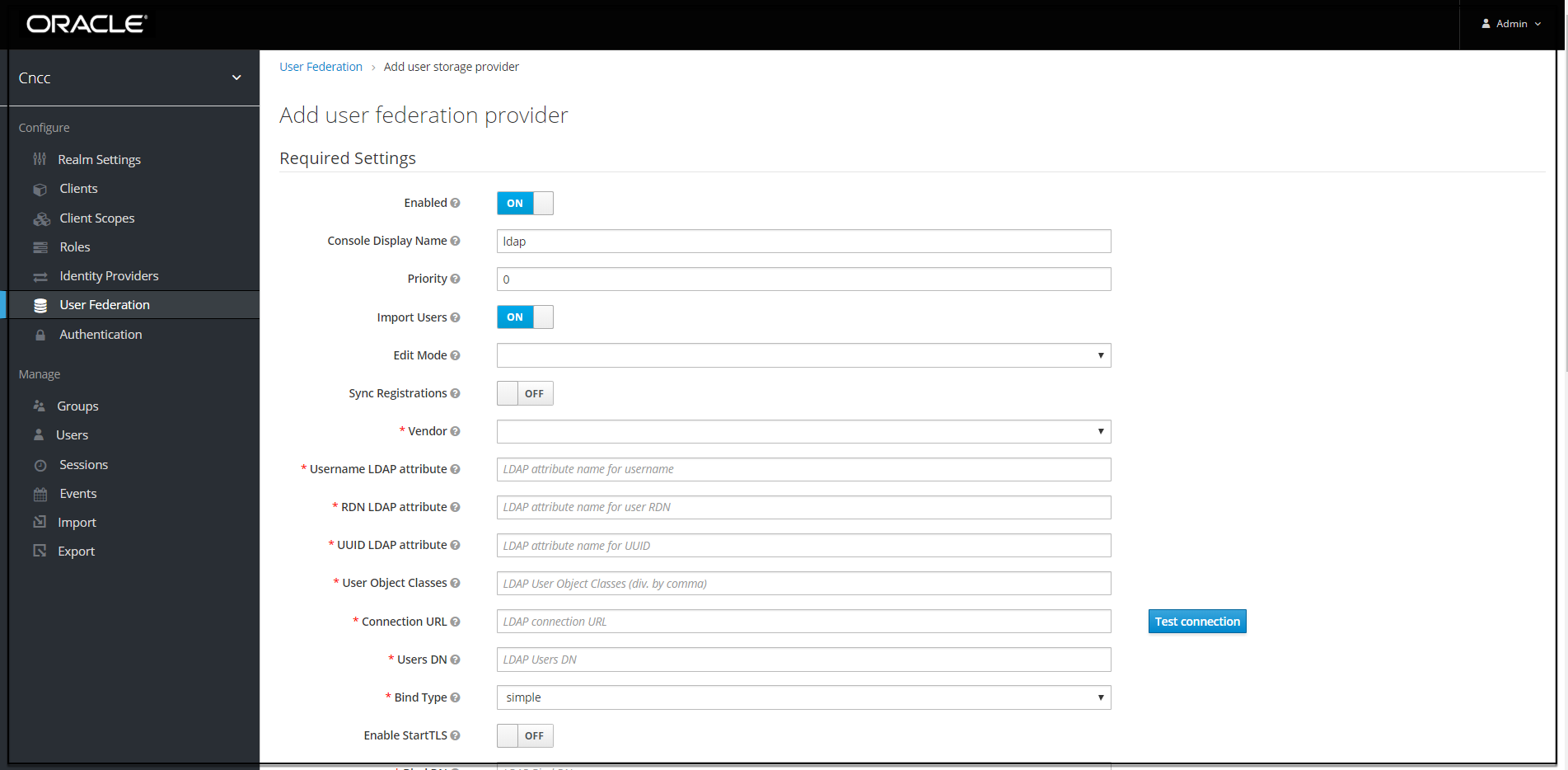
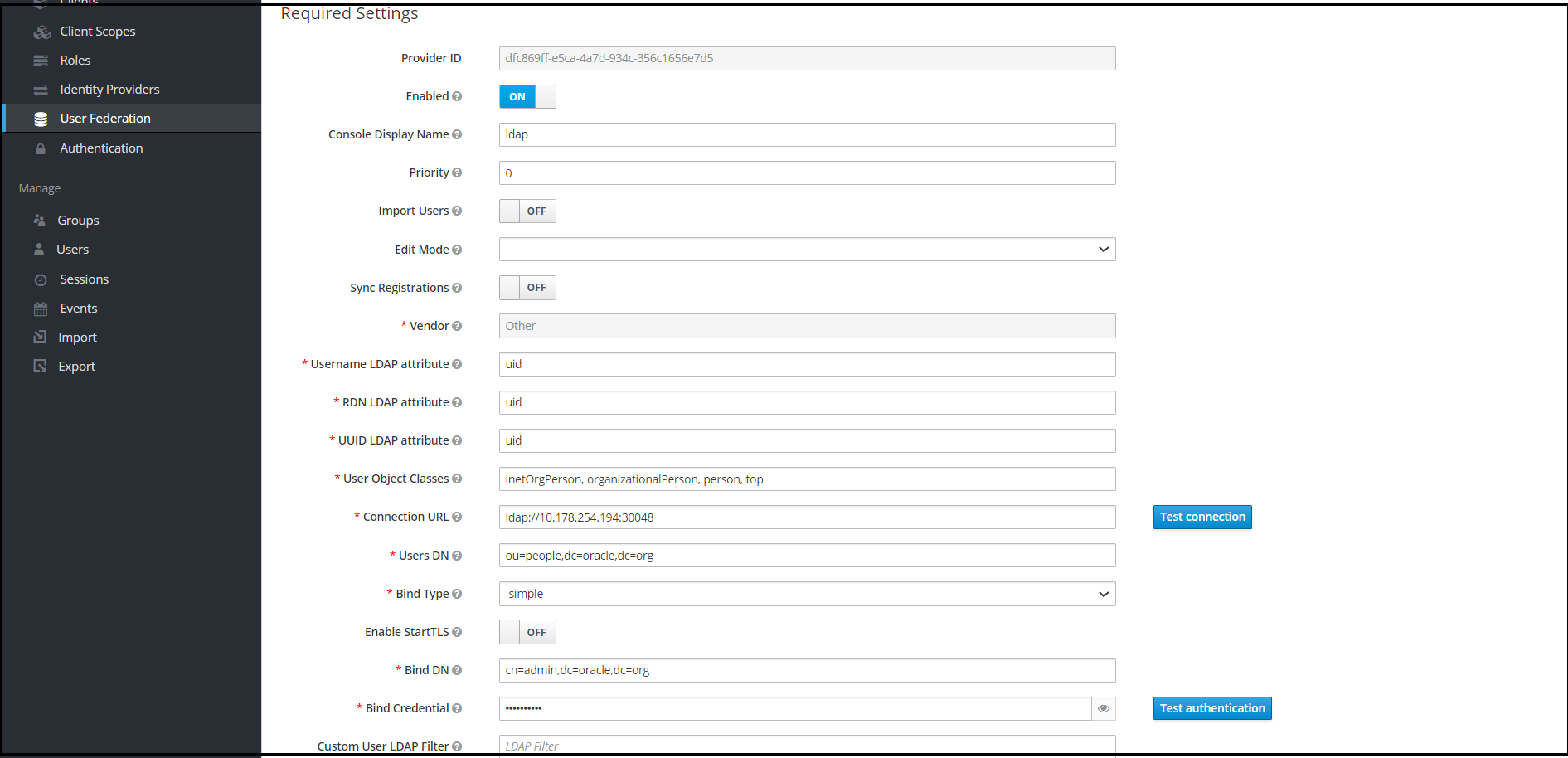
- Fill the following parameters:
- Console Display Name: Enter the display name.
- Vendor: Enter the LDAP server provider name for the company.
Note:
This must usually fill the defaults for many of the fields. But in case user have a different setup than the defaults, enter the correct values to be provided. Current set up is Spring embedded LDAP, so select the last option "Other" from the drop-down list. This fills in many of the required fields.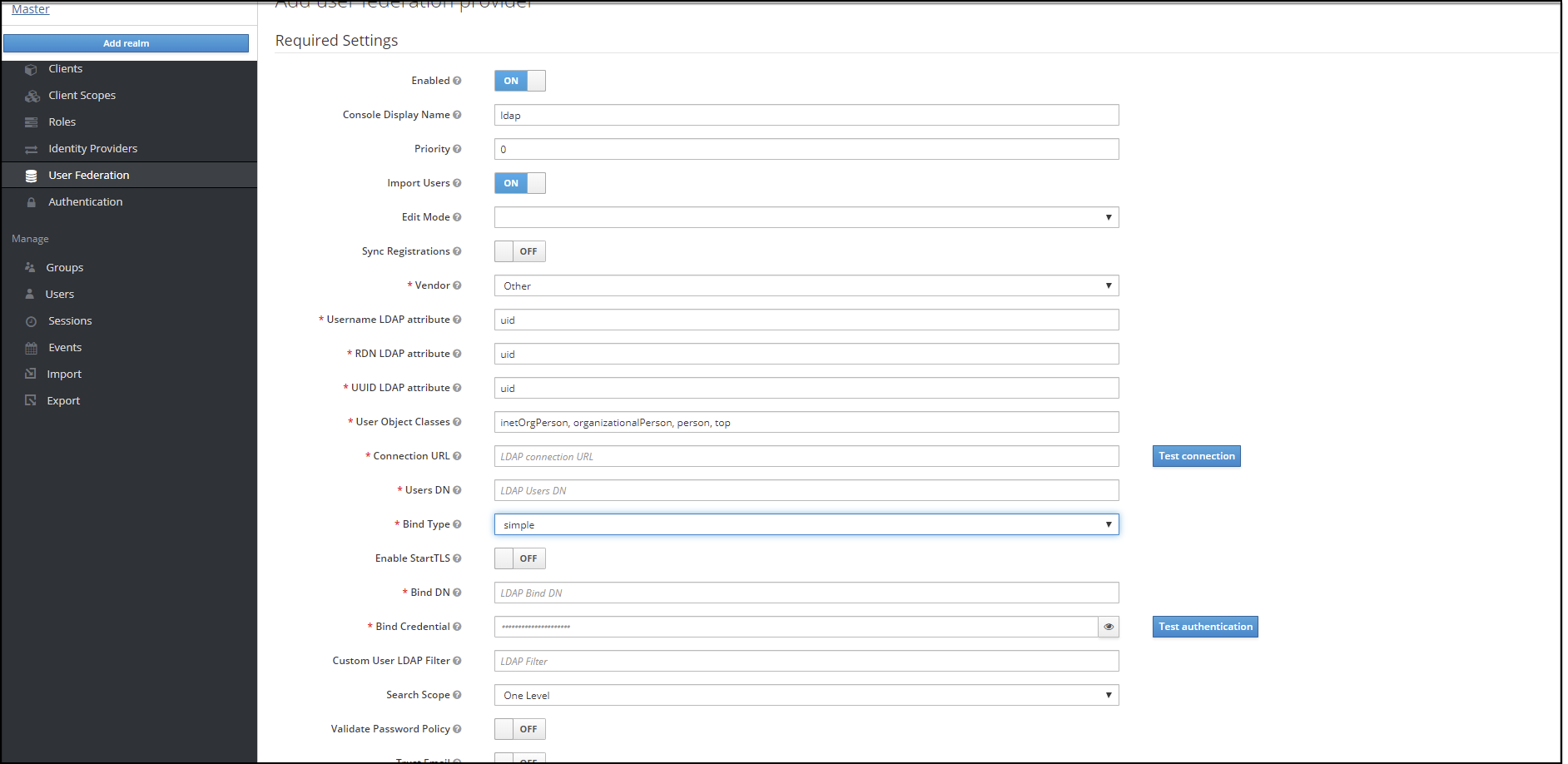
- Most companies have the UUID LDAP attribute value set as "entryUUID". If you don't have this field, than just use another unique identifier.
- The default setting for Import Users is 'ON'. Change it to 'OFF' to disable user sync.
- Provide company LDAP server details.
- If the LDAP is secured then select 'simple' from the Bind Type drop down and provide the admin bind username and password else select Bind Type as "none". Sample data for the field Bind DN "cn=admin,dc=oracle,dc=org".
- Click "Test Connection" and "Test Authentication".
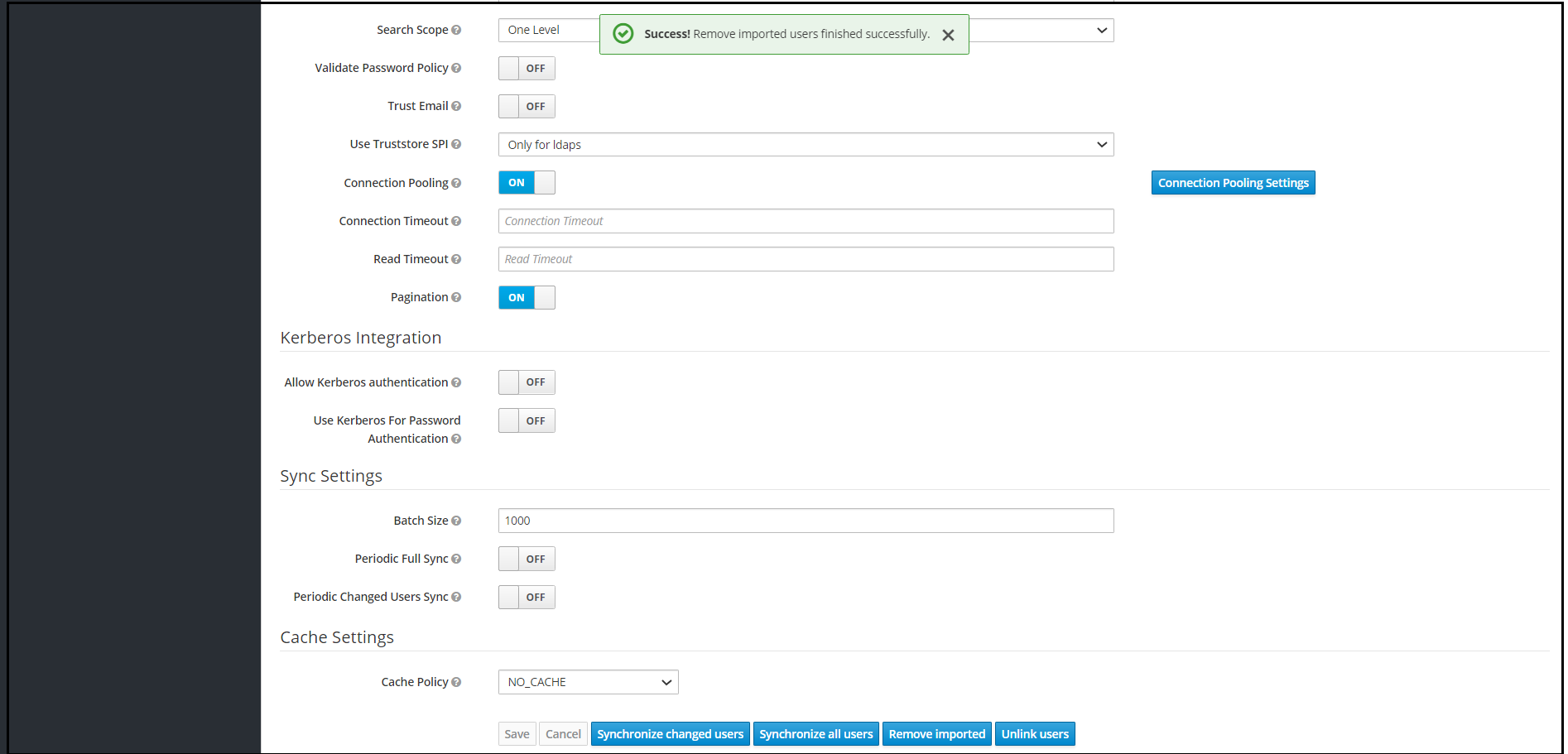
- Set Cache policy as "NO_CACHE".
- After filling the required fields, the screen appears as below. Click Save.
- New buttons (Synchronize changed users, Synchronize all users, Remove
imported, Unlink users) appears next to the Save and Cancel.
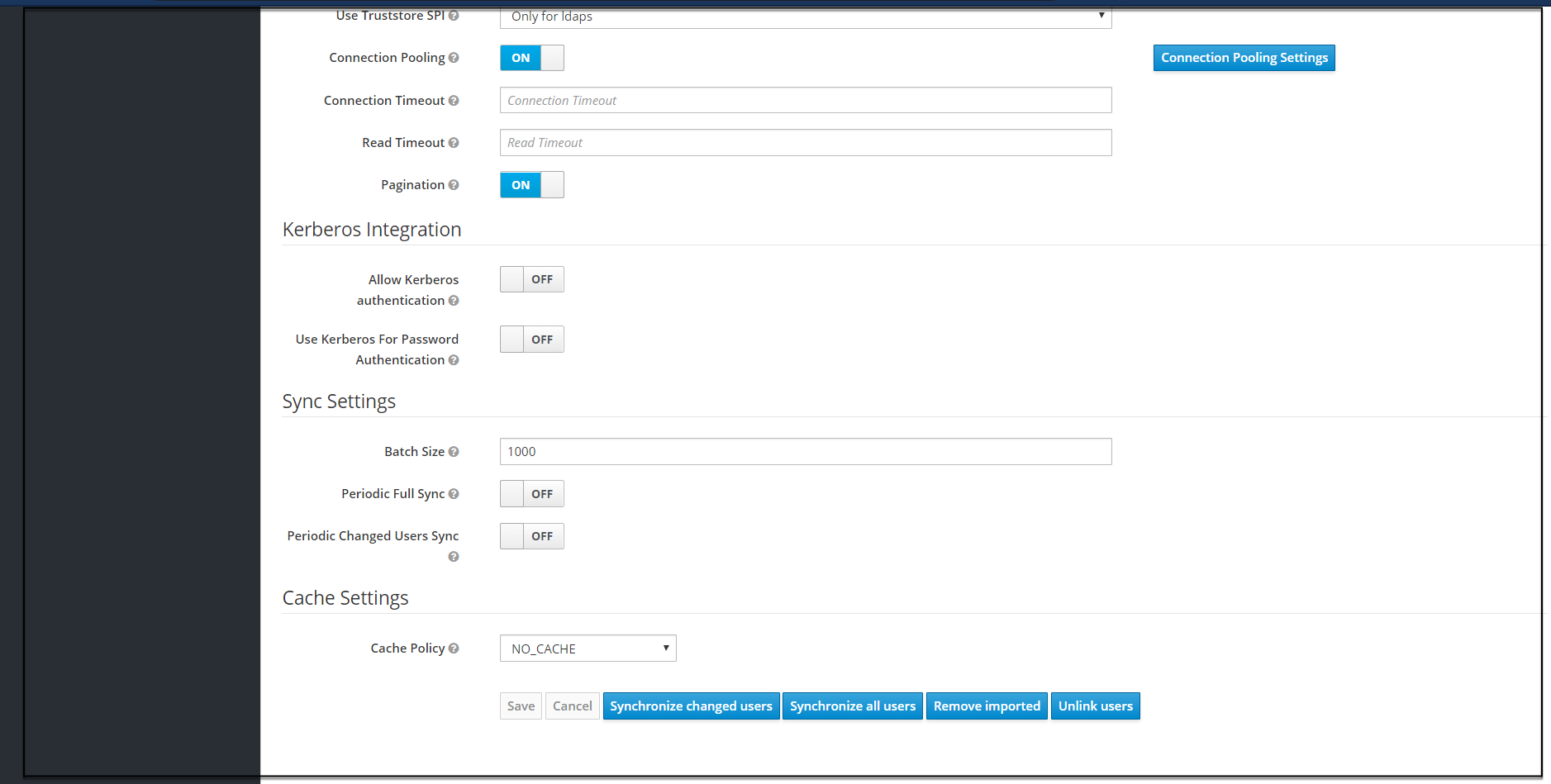
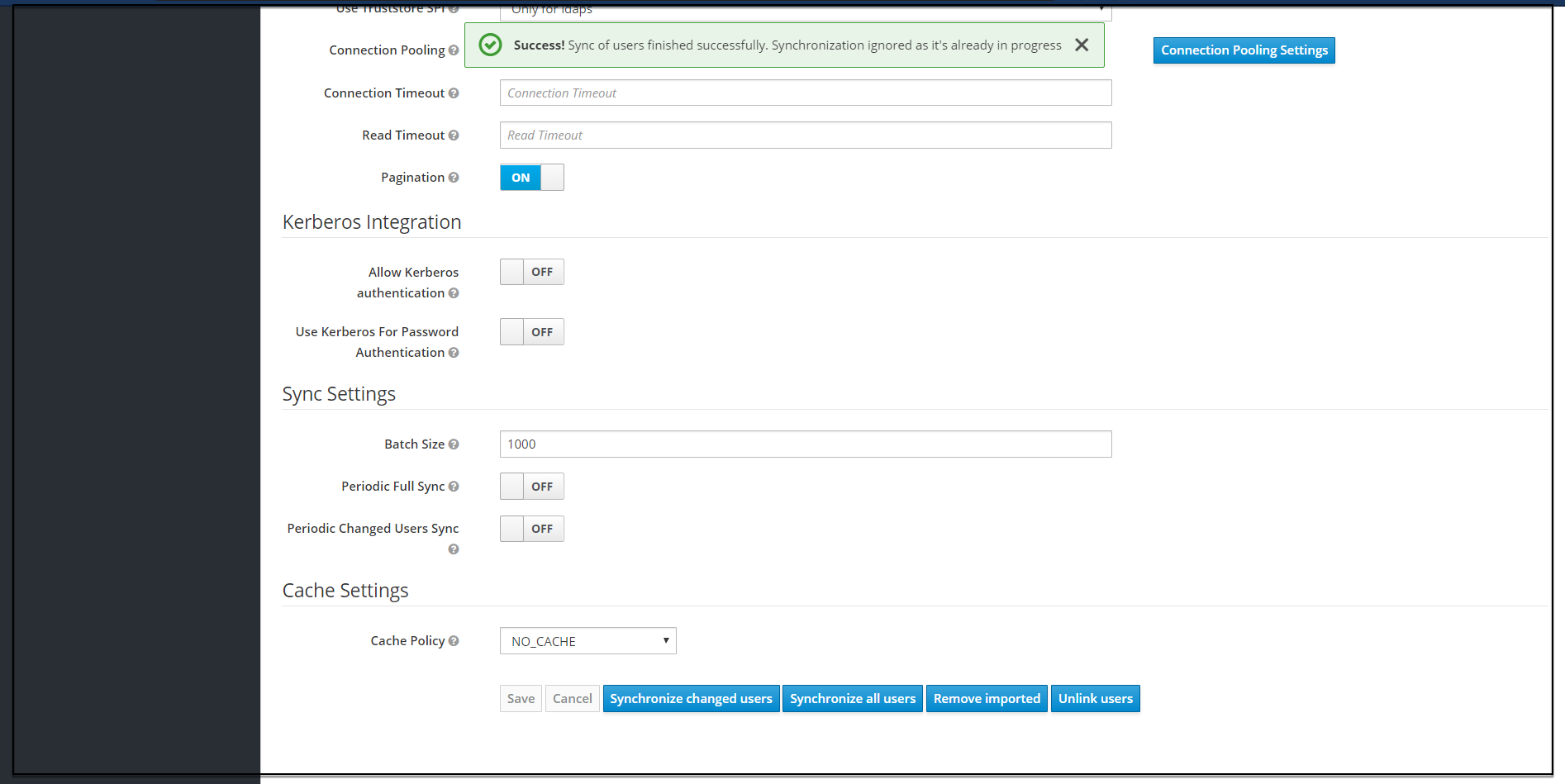
- If a user has to be import to CNCC-IAM, Click Synchronize all users. If
the synchronization is successful, the success message appears. If the
synchronization fails, then check the trouble shooting section and look at
cncc-iam logs in debug mode.
- The user can view the imported users by clicking Users under Manage
in the left pane and click View all users in the right pane. The list of
users and details appears.
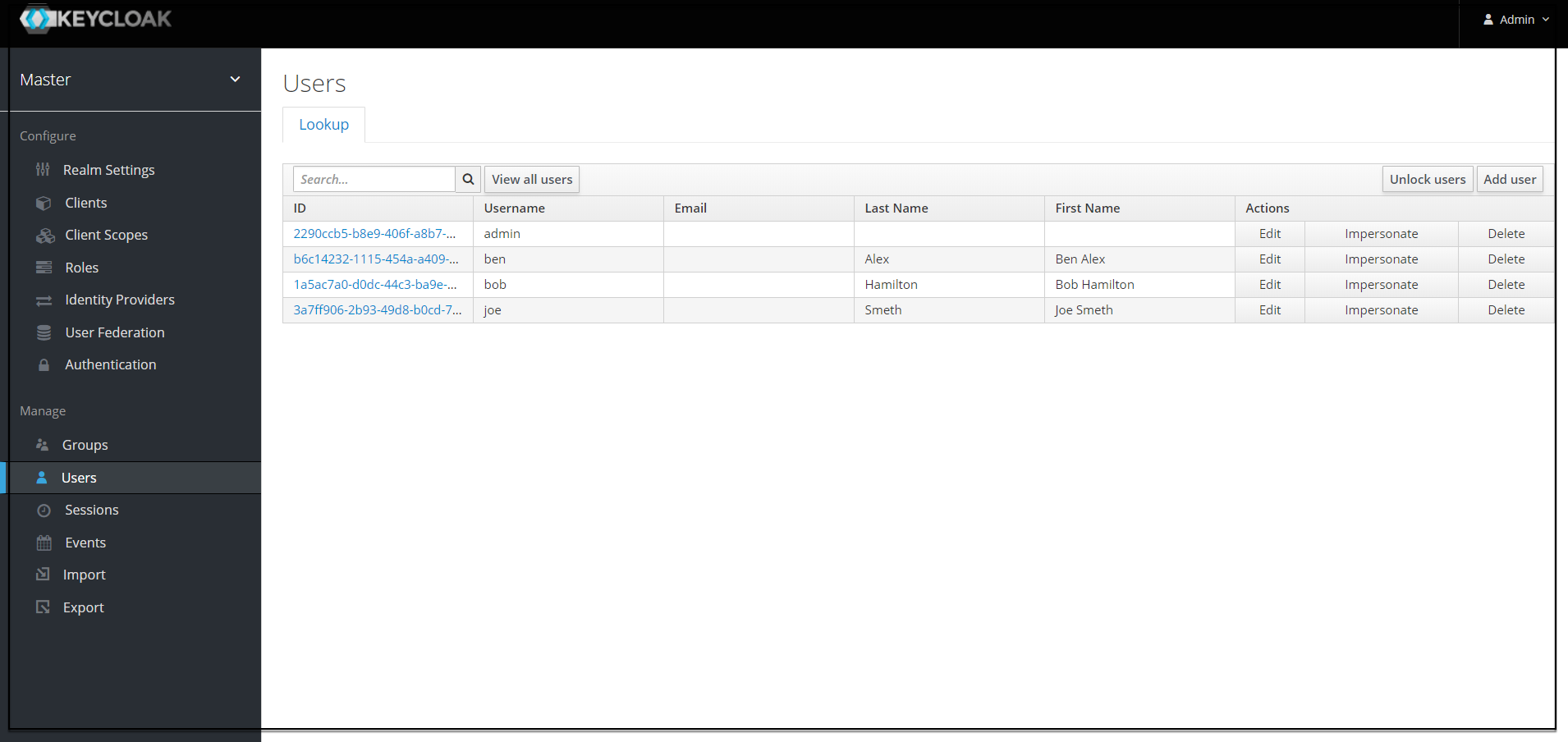
- The user can remove the imported users by clicking the Remove imported
and set Import Users to OFF to ensure that the users are not
imported to CNCC IAM on your subsequent logins.
Note:
The steps 8 and 9 are optional.Group LDAP Mapper and Role Assignment
Group Mapper
The Group Mapper allows you to configure group mappings from LDAP into cncc-iam group mappings. Group mapper can be used to map LDAP groups from a particular branch of an LDAP tree into groups in cncc-iam. It also propagates user-group mappings from LDAP into user-group mappings in cncc-iam.
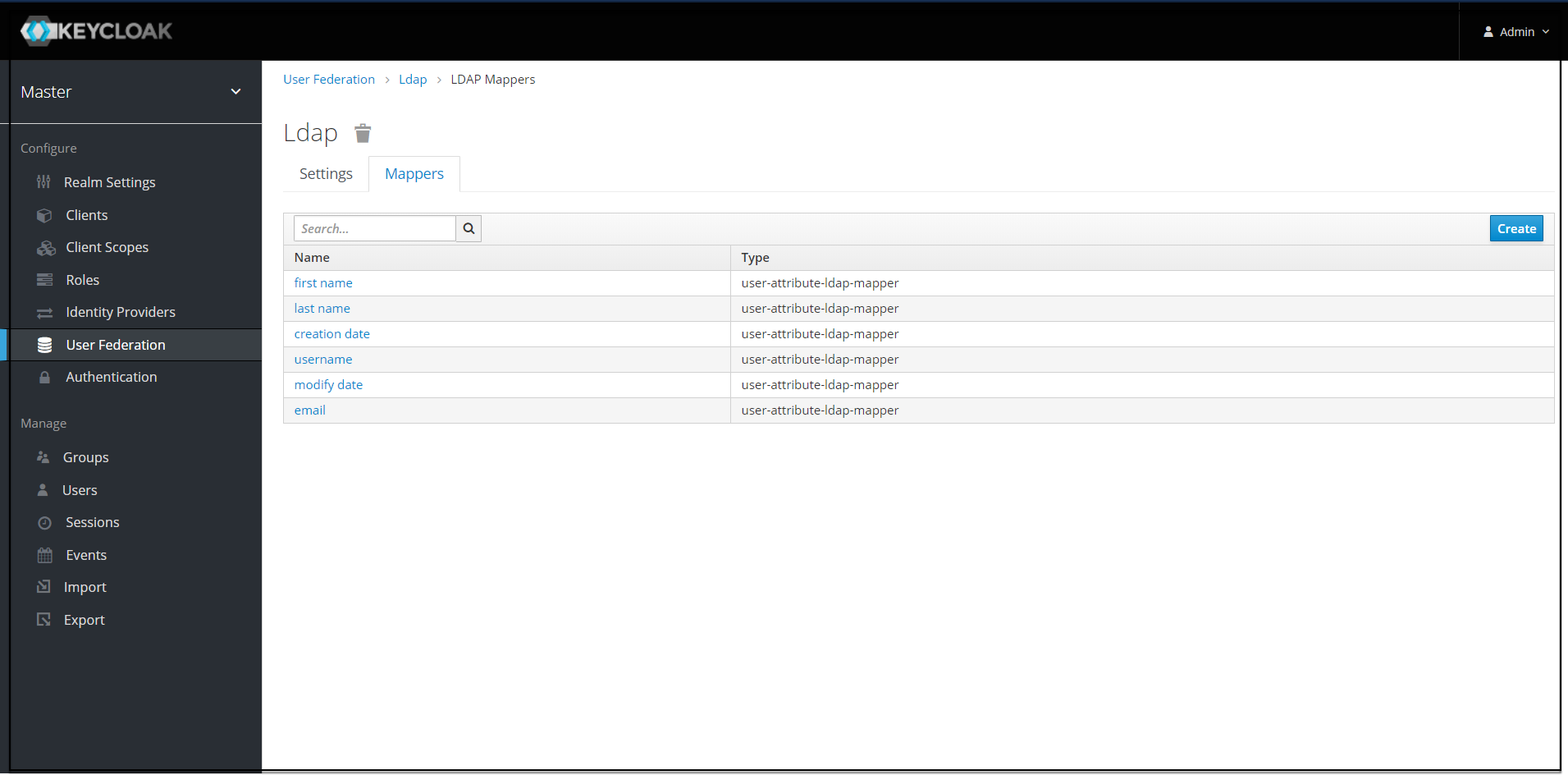
- Click Configure and select User Federation. Click
ldap (Console Display Name) and select the Mappers tab,
and click Create.
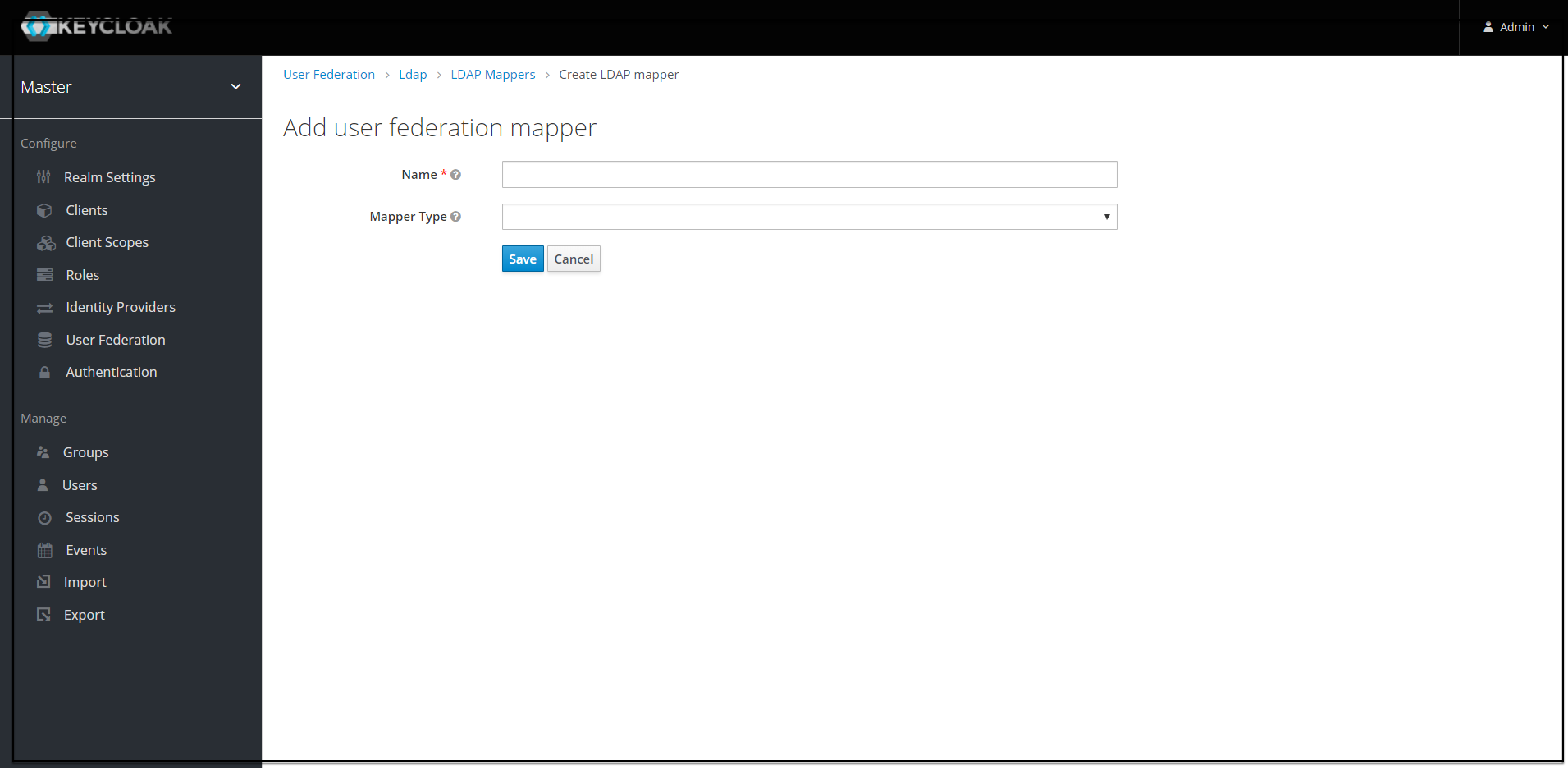
- The Add User
federation mapper page appears. Give an appropriate name for the
field Name. Select
'group-ldap-mapper' as Mapper Type drop down menu. Click Save.
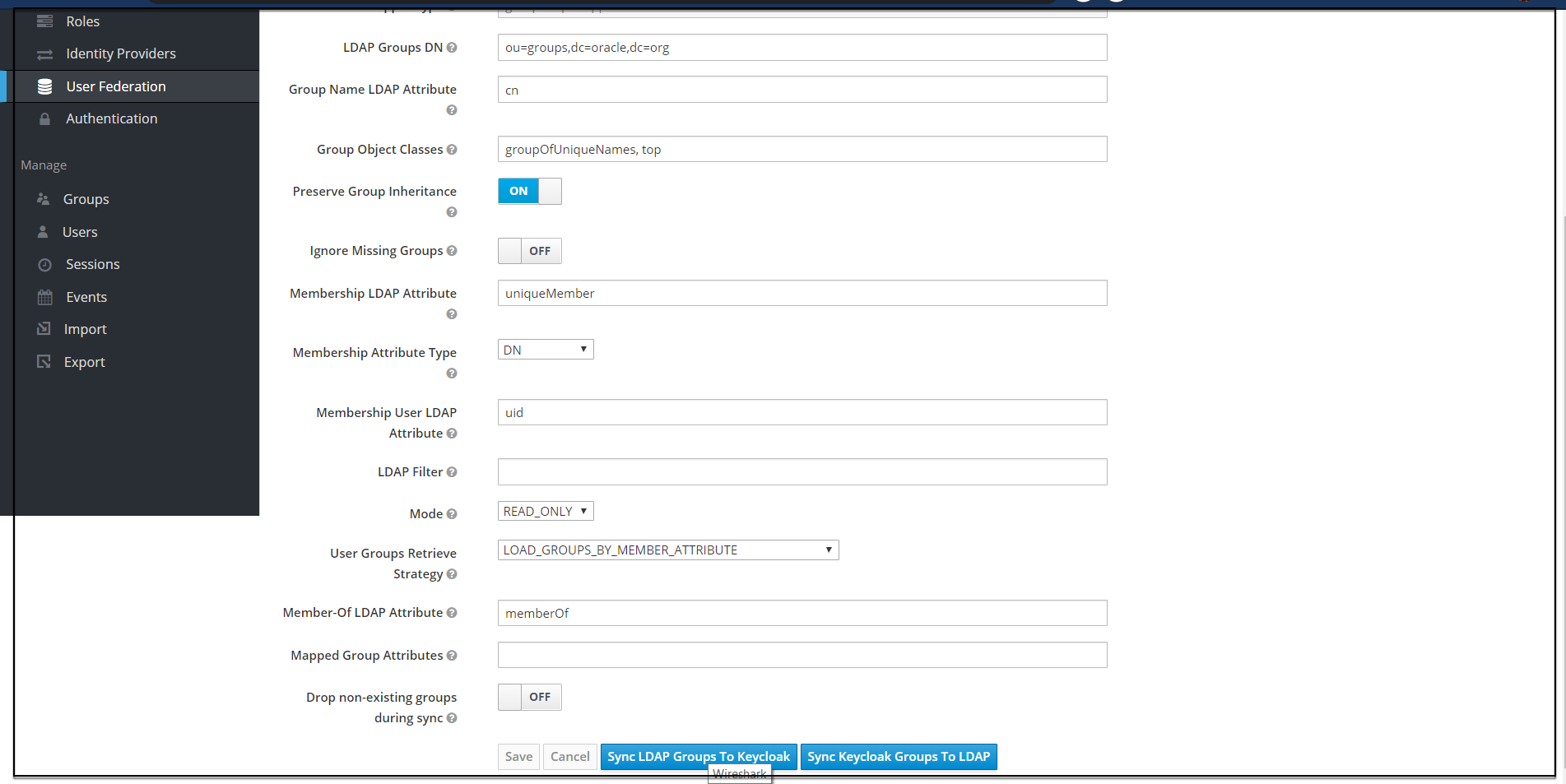
The following screen appears.
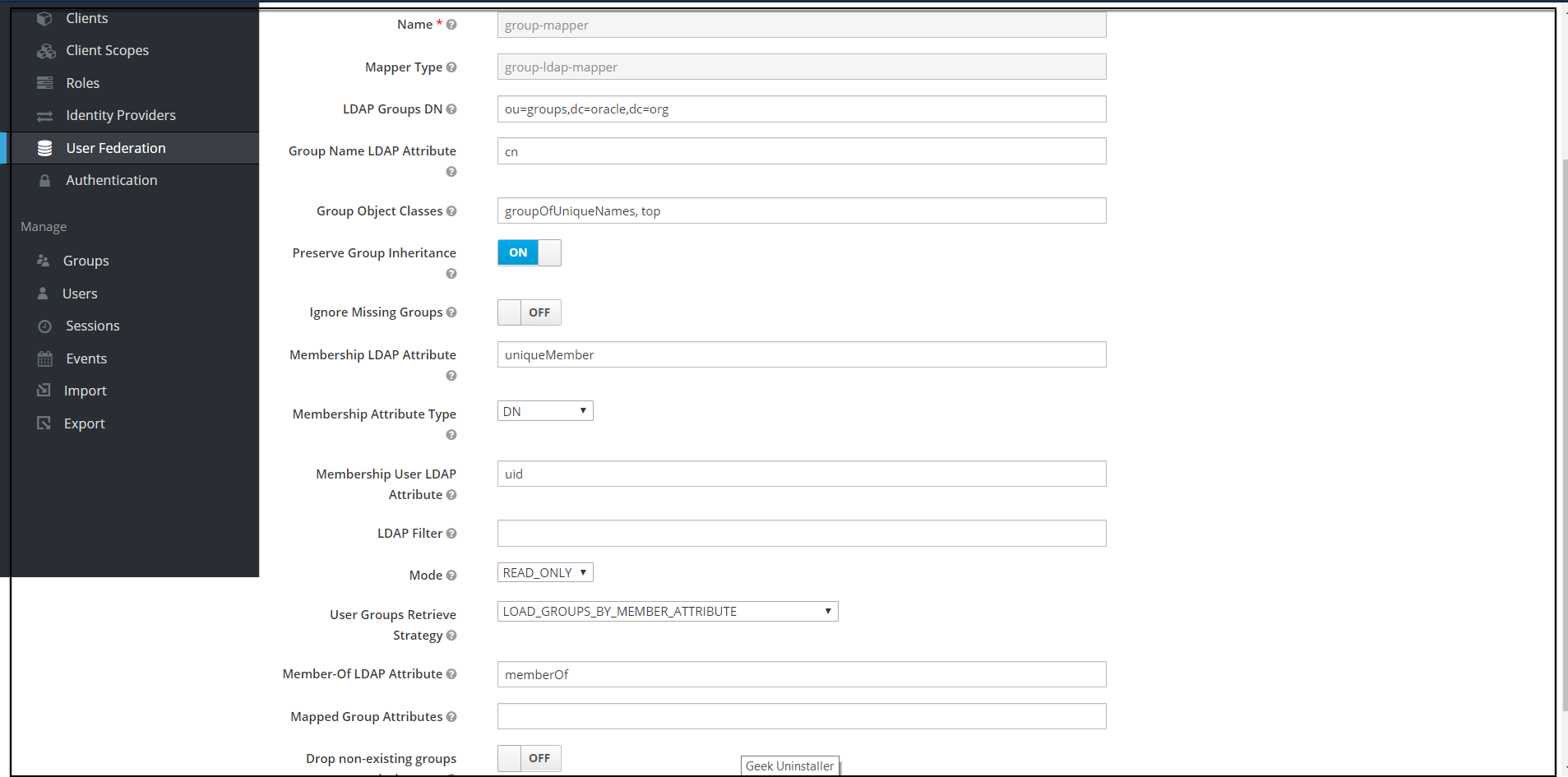
Note:
When selected, default values will be set by cncc-iam. But you need change some values based on your ldap records. - Click Save. New buttons appears next to the Save and Cancel. They are Synchronize LDAP Groups
to Keyclaok and Synchronize Keyclaok Groups to LDAP.
- Click Synchronize LDAP Groups
to Keyclaok. The success message appears with the number of groups
imported and so on.
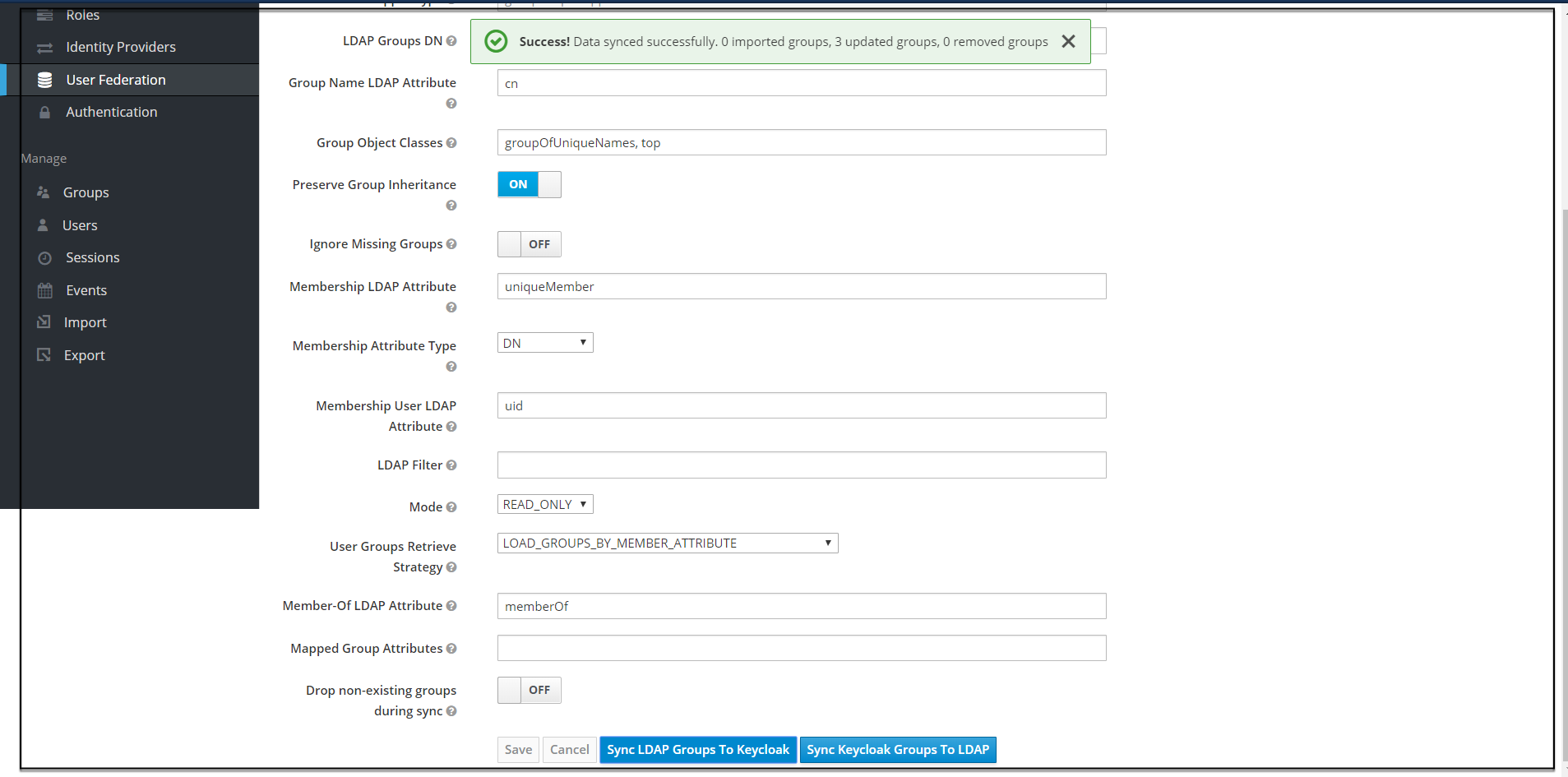
Note:
If this step fails then you might need to check to the trouble shooting section and look at cncc-iam logs in debug mode. - Select the Groups in the left pane and click the View all groups in
the right pane.
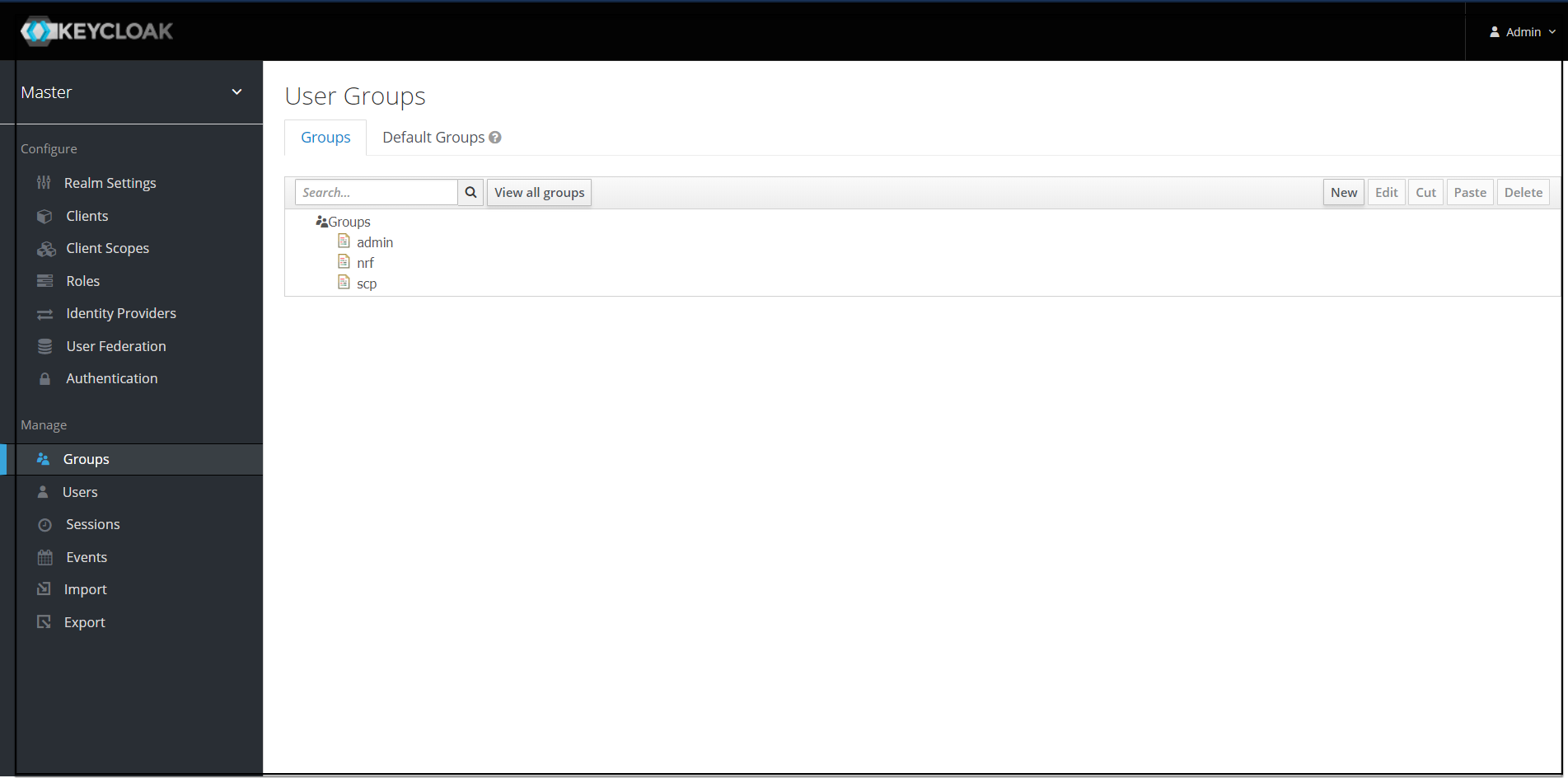
- Click any group and click Edit. The following
tabs appear: Settings,
Attributes, Role Mappings, and Members.
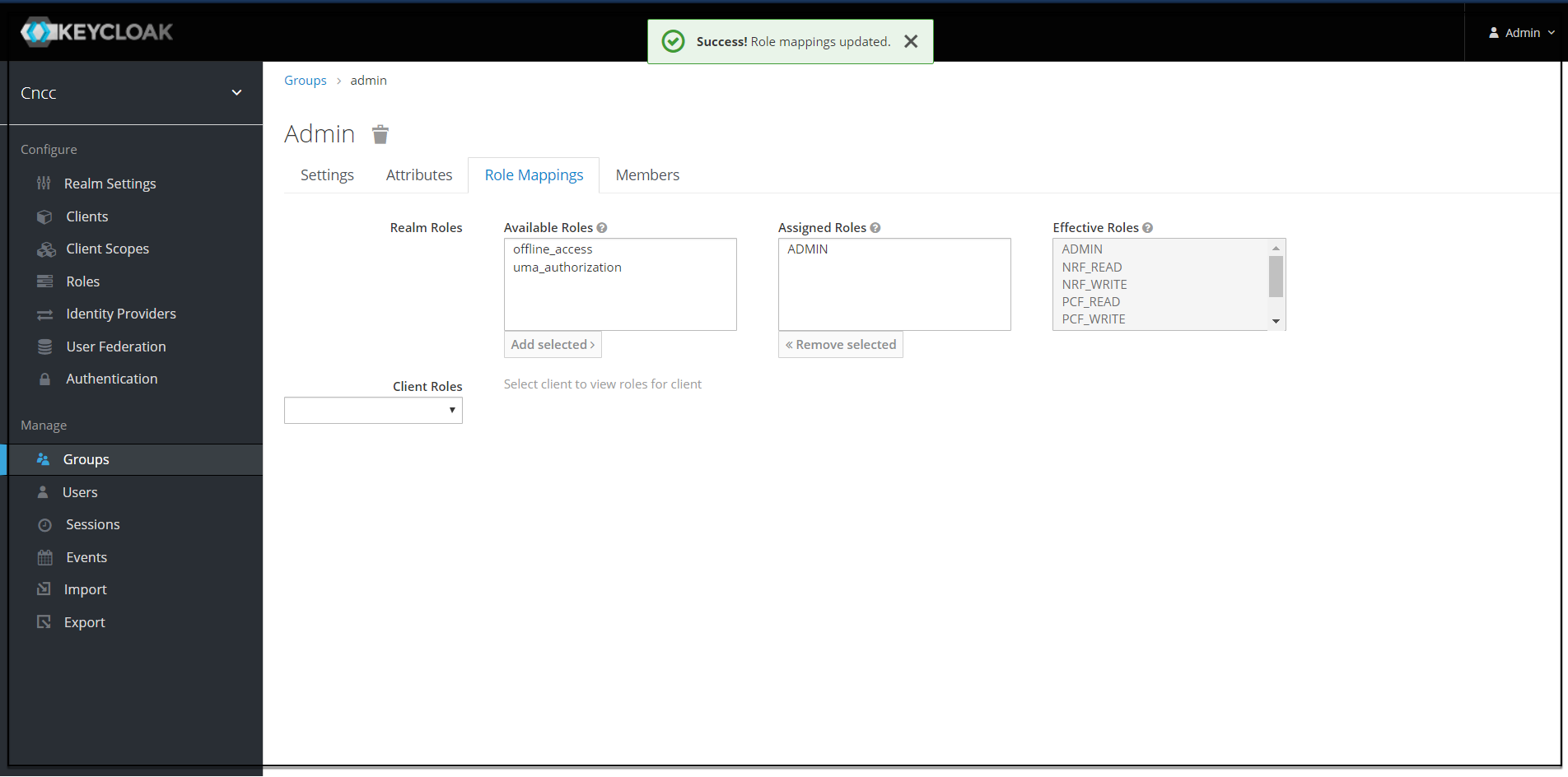
- Select Role Mapping tab to see a list of roles that are pre-defined in cncc-iam.
- Select one or more roles from Available Roles and assign it to the group. For example, If group "admin" is assigned with role "ADMIN", it means that any user which belongs to the admin group will be automatically assigned the admin role which allows him to access all the NF resource of CNC console that it supports.
- Once done you can test authentication and authorization by logging into CNC Console GUI.
Note:
- When the password of user is updated from CNCC-IAM and sent to LDAP, it is always sent in plain-text. This is different from updating the password to built-in CNCC-IAM database, when the hashing and salting is applied to the password before it is sent to DB. In the case of LDAP, the CNCC-IAM relies on the LDAP server to provide hashing and salting of passwords.
- Most of LDAP servers (Microsoft Active Directory, RHDS, FreeIPA) provide this by default. Some others (OpenLDAP, ApacheDS) may store the passwords in plain text by default and user need to explicitly enable password hashing for them.
Note:
For more information about the user roles, refer APPENDIX.