3 Media and Documentation
3.1 Media Pack
This section lists the media package for Oracle Communications Cloud Native Core 3.25.2.2xx.0. To download the media package, see MOS.
Note:
The information provided in this section is accurate at the time of release but is subject to change. See the Oracle software delivery website for the latest information.Table 3-1 Media Pack Contents for Oracle Communications Cloud Native Core 3.25.2.2xx.0
| Description | NF Version | ATS Version | Upgrade Supported |
|---|---|---|---|
| Oracle Communications Cloud Native Core, Binding Support Function (BSF) | 25.2.200 | 25.2.200 | BSF 25.2.200 supports fresh installation and upgrade from 25.1.2xx and 25.2.1xx. For more information, see Oracle Communications Cloud Native Core, Binding Support Function Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Configuration Console (CNC Console) | 25.2.201 | NA | CNC Console 25.2.201 supports fresh installation and upgrade from 25.2.2xx, 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Configuration Console Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Configuration Console (CNC Console) | 25.2.200 | NA | CNC Console 25.2.200 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Configuration Console Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, cnDBTier (cnDBTier) | 25.2.201 | NA | cnDBTier 25.2.201 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, cnDBTier Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, Cloud Native Environment (CNE) | 25.2.201 | NA | CNE 25.2.201 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Cloud Native Environment Installation, Upgrade, and Fault Recovery Guide.
Note: In-service upgrades are not supported for OpenStack CNE deployments; however, they are supported for vCNE and Bare Metal environments. |
| Oracle Communications Cloud Native Core, Cloud Native Environment (CNE) | 25.2.200 | NA | CNE 25.2.200 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Cloud Native Environment Installation, Upgrade, and Fault Recovery Guide.
Note: In-service upgrades are not supported for OpenStack CNE deployments; however, they are supported for vCNE and Bare Metal environments. |
| Oracle Communications Cloud Native Core, Network Slice Selection Function (NSSF) | 25.2.200 | 25.2.200 | Upgrades are not supported in this release. NSSF 25.2.200 supports fresh installation only. For more information, see Oracle Communications Cloud Native Core, Network Slice Selection Function Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, Certificate Management (OCCM) | 25.2.200 | NA | OCCM 25.2.200 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Certificate Management Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Operations Services Overlay (OSO) | 25.2.202 | NA | OSO 25.2.202 supports fresh installation and upgrade from 25.2.2xx, 25.2.1xx, and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Operations Services Overlay Installation and Upgrade Guide. |
| Oracle Communications Operations Services Overlay (OSO) | 25.2.201 | NA | OSO 25.2.201 supports fresh installation and upgrade from 25.2.200, 25.2.1xx, and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Operations Services Overlay Installation and Upgrade Guide. |
| Oracle Communications Operations Services Overlay (OSO) | 25.2.200 | NA | OSO 25.2.200 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Operations Services Overlay Installation and Upgrade Guide. |
| Oracle Communications Cloud Native Core, Network Repository Function (NRF) | 25.2.201 | 25.2.201 | NRF 25.2.201 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Network Repository Function Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, Converged Policy (Policy) | 25.2.201 | 25.2.201 | Policy 25.2.201 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Converged Policy Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, Service Communications Proxy (SCP) | 25.2.202 | 25.2.202 | SCP 25.2.202 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Service Communication Proxy Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, Service Communications Proxy (SCP) | 25.2.201 | 25.2.201 | SCP 25.2.201 supports fresh installation and upgrade from 25.2.1xx and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Service Communication Proxy Installation, Upgrade, and Fault Recovery Guide. |
| Oracle Communications Cloud Native Core, Security Edge Protection Proxy (SEPP) | 25.2.200 | 25.2.200 | SEPP 25.2.200 supports fresh installation and upgrade from 25.2.1xx, and 25.1.2xx. For more information, see Oracle Communications Cloud Native Core, Security Edge Protection Proxy Installation, Upgrade, and Fault Recovery Guide. |
Cloud Native Core Upgrade
To ensure a smooth and supported upgrade process, follow the upgrade sequence outlined in the table below. Product does not recommend skipping intermediate versions unless explicitly showed:
Figure 3-1 Cloud Native Core Upgrade
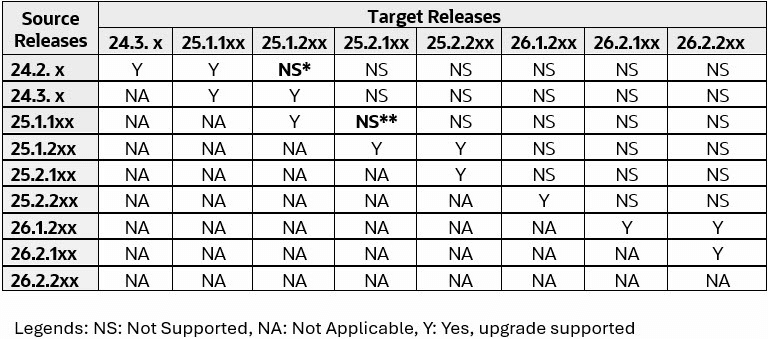
Note:
- * Policy, CNC Console, UDR, SLF, and cnDBTier supports upgrade from 24.2.x to 25.1.2xx (this exception applies only to upgrade from 24.2.x to 25.1.2xx).
- ** SCP, SEPP, UDR, SLF, CNC Console, and cnDBTier supports upgrade from 25.1.1xx to 25.2.1xx.
CNE Upgrade
To ensure a smooth and supported upgrade process, follow the upgrade sequence outlined in the following table:
Figure 3-2 CNE Upgrade
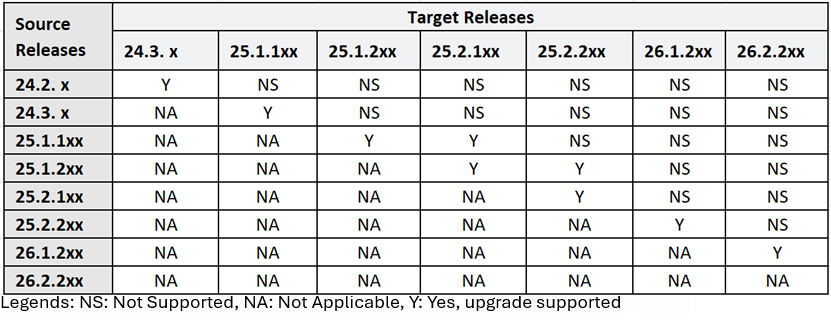
Note:
- If enabling following features in CNE, a fresh installation is required.
- Heterogenous Kubernetes nodes
- CNLB bypass for Egress traffic
- Dedicated CNLB Kubernetes node.
- For vCNE-Openstack upgrade, worker node interfaces are renamed and service disruption of application traffic is expected. It is advised to do offline upgrade after diverting application traffic away form instance that is upgraded.
- The in-service upgrades are supported only for BareMetal and VMware platforms and not for OpenStack.
3.2 Impacted Documents
The following table lists the documents that are impacted in the specific NF release version.
Table 3-2 Impacted Documents
| CNC NF | NF Version | Impacted Documents |
|---|---|---|
| BSF | 25.2.200 |
|
| CNC Console | 25.2.201 |
|
| CNC Console | 25.2.200 |
|
| cnDBTier | 25.2.201 |
|
| CNE | 25.2.200 |
|
| NSSF | 25.2.200 |
|
| NRF | 25.2.201 |
|
| OCCM | 25.2.200 |
|
| OSO | 25.2.202 |
|
| OSO | 25.2.201 |
|
| OSO | 25.2.200 |
|
| Policy | 25.2.201 |
|
| SCP | 25.2.202 |
|
| SCP | 25.2.201 |
|
| SEPP | 25.2.200 |
|
3.3 Compatibility Matrix
The following table lists the compatibility matrix for each network function:
Note:
- For seamless integration and optimal performance of CNC NFs on third party platform, the third party platform needs to be compatible with the specified Kubernetes version.
Table 3-3 Compatibility Matrix
| CNC NF | NF Version | CNE | cnDBTier | OSO | ASM S/W | Kubernetes | CNC Console | OCNADD | OCCM | OCI Adaptor |
|---|---|---|---|---|---|---|---|---|---|---|
| BSF | 25.2.200 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2xx | NA | 25.2.2xx | NA |
| CNC Console | 25.2.201 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 1.11.8 |
1.34.x 1.33.x 1.32.x |
NA | 25.2.2xx | 25.2.2xx | 25.2.2xx |
| CNC Console | 25.2.200 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 1.11.8 |
1.34.x 1.33.x 1.32.x |
NA | 25.2.2xx | 25.2.2xx | 25.2.2xx |
| OCCM | 25.2.200 |
25.2.2xx 25.2.1xx 25.1.2xx |
NA | NA | NA |
1.34.x 1.33.x 1.32.x |
25.2.2xx | NA | NA | NA |
| CNE | 25.2.201 | NA | NA | NA | NA | 1.34.x | NA | NA | NA | NA |
| CNE | 25.2.200 | NA | NA | NA | NA | 1.34.x | NA | NA | NA | NA |
| OSO | 25.2.202 | NA | NA | NA | NA |
1.34.x 1.33.x 1.32.x |
NA | NA | NA | NA |
| OSO | 25.2.201 | NA | NA | NA | NA |
1.34.x 1.33.x 1.32.x |
NA | NA | NA | NA |
| OSO | 25.2.200 | NA | NA | NA | NA |
1.34.x 1.33.x 1.32.x |
NA | NA | NA | NA |
| cnDBTier | 25.2.201 |
25.2.2xx 25.2.1xx 25.1.2xx |
NA | NA | NA |
1.34.x 1.33.x 1.32.x |
NA | NA | NA | NA |
| NRF | 25.2.201 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
NA |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2xx | 25.2.2xx | 25.2.2xx | 25.2.2xx |
| NSSF | 25.2.200 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2xx | NA | 25.2.2xx | NA |
| OCI Adaptor | 25.2.200 | NA | NA | NA | NA |
1.34.x 1.33.x 1.32.x |
NA | NA | NA | NA |
| Policy | 25.2.201 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2x | NA | 25.2.2x | NA |
| SCP | 25.2.202 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2xx | 25.2.2xx | 25.2.2xx | 25.2.2xx |
| SCP | 25.2.201 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2xx | 25.2.2xx | 25.2.2xx | 25.2.2xx |
| SEPP | 25.2.200 |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
25.2.2xx 25.2.1xx 25.1.2xx |
1.21.6 1.14.6 |
1.34.x 1.33.x 1.32.x |
25.2.2xx | 25.2.2xx | 25.2.2xx | 25.2.2xx |
3.4 3GPP Compatibility Matrix
The following table lists the 3GPP compatibility matrix for each network function:
Table 3-4 3GPP Compatibility Matrix
| CNC NF | NF Version | 3GPP |
|---|---|---|
| BSF | 25.2.2xx |
|
| CNC Console | 25.2.2xx | NA |
| cnDBTier | 25.2.2xx | NA |
| NSSF | 25.2.2xx |
|
| OCCM | 25.2.2xx |
|
| OSO | 25.2.2xx | NA |
| OCI Adaptor | 25.2.2xx | NA |
| NRF | 25.2.2xx |
|
| Policy | 25.2.2xx |
|
| SCP | 25.2.2xx |
|
| SEPP | 25.2.2xx |
|
Note:
Refer to the Compliance Matrix spreadsheet for details on NFs' compliance with each 3GPP version mentioned in this table.3.5 Common Microservices Load Lineup
This section provides information about common microservices and ATS for the specific NF versions in Oracle Communications Cloud Native Core Release 3.25.2.2xx.0.
Table 3-5 Common Microservices Load Lineup for Network Functions
| CNC NF | NF Version | Alternate Route Svc | App-Info | ASM Configuration | ATS Framework | Config-Server | Debug-tool | Egress Gateway | Ingress Gateway | Helm Test | Mediation | NRF-Client | Perf-Info |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| BSF | 25.2.200 | 25.2.108 | 25.2.204 | 25.2.200 | 25.2.202 | 25.2.204 | 25.2.203 | 25.2.108 | 25.2.108 | 25.2.203 | NA | 25.2.202 | 25.2.204 |
| CNC Console | 25.2.201 | NA | NA | NA | NA | NA | 25.2.205 | NA | 25.2.111 | 25.2.205 | NA | NA | NA |
| CNC Console | 25.2.200 | NA | NA | NA | NA | NA | 25.2.203 | NA | 25.2.108 | 25.2.203 | NA | NA | NA |
| OCCM | 25.2.200 | NA | NA | NA | NA | NA | 25.2.203 | NA | NA | 25.2.203 | NA | NA | NA |
| NSSF | 25.2.200 | 25.2.108 | 25.2.202 | 25.2.200 | 25.2.200 | 25.2.202 | 25.2.203 | 25.2.108 | 25.2.108 | 25.2.203 | NA | 25.2.202 | 25.2.202 |
| NRF | 25.2.201 | 25.2.110 | 25.2.208 | 25.2.200 | 25.2.204 | NA | 25.2.203 | 25.2.110 | 25.2.110 | 25.2.205 | NA | NA | 25.2.208 |
| Policy | 25.2.201 | 25.2.110 | 25.2.209 | 25.2.201 | 25.2.204 | 25.2.209 | 25.2.204 | 25.2.110 | 25.2.110 | 25.2.205 | NA | 25.2.203 | 25.2.209 |
| SCP | 25.2.202 | NA | NA | 25.2.200 | 25.2.203 | NA | 25.2.204 | NA | NA | 25.2.205 | 25.2.203 | NA | NA |
| SCP | 25.2.201 | NA | NA | 25.2.200 | 25.2.203 | NA | 25.2.204 | NA | NA | 25.2.205 | 25.2.203 | NA | NA |
| SEPP | 25.2.200 | 25.2.110 | 25.2.208 | 25.2.201 | 25.2.204 | 25.2.208 | 25.2.204 | 25.2.110 | 25.2.110 | 25.2.205 | 25.2.203 | 25.2.203 | 25.2.208 |
3.6 Generic Open Source Software Compatibility on Any Platform
Note:
The Software Requirement column in the following table indicates one of the following:- Mandatory: Absolutely essential; the software cannot function without it.
- Recommended: Suggested for optimal performance or best practices but not strictly necessary.
- Conditional: Required only under specific conditions or configurations.
- Optional: Not essential; can be included based on specific use cases or preferences.
Table 3-6 Generic Open Source Software Compatibility on Any Platform
| Software | Tested Software Version | Software Requirement | Category | Sub-Category | Category Requirement | Usage Description | ||
|---|---|---|---|---|---|---|---|---|
| NF 25.2.2xx | NF 25.2.1xx | NF 25.1.2xx | ||||||
| Kubernetes | 1.33.2 | 1.33.1 | 1.32.0 | Mandatory | Orchestration | Container Orchestration | Mandatory | Kubernetes orchestrates scalable, automated NF deployments for high availability and efficient resource utilization.
Impact: Preinstallation is required. Without orchestration capabilities, deploying and managing network functions (NFs) can become complex, leading to inefficient resource utilization and potential downtime. |
| Helm | 3.19.1 | 3.18.0 | 3.17.1 | Mandatory | Management | Kubernetes Package Management | Mandatory | Helm, a package manager, simplifies deploying and managing NFs on Kubernetes with reusable, versioned charts for easy automation and scaling.
Impact: Preinstallation is required. Not using this capability may result in error-prone and time-consuming management of NF versions and configurations, impacting deployment consistency. |
| Podman | 4.9.4 | 4.9.4 | 4.9.4 | Recommended | Runtime | Containerized NF Image Management | Mandatory | Podman manages and runs containerized NFs without requiring a daemon, offering flexibility and compatibility with Kubernetes.
Impact: Preinstallation is required. Podman is a part of Oracle Linux. Without efficient container management, the development and deployment of NFs could become cumbersome, impacting agility. |
| containerd | 2.1.4 | 2.0.5 | 1.7.24 | Recommended | Runtime | Container Runtime | Mandatory | Containerd manages container lifecycles for running NFs efficiently in Kubernetes.
Impact: A lack of a reliable container runtime could lead to performance issues and instability in NF operations. |
| Velero | 1.16.2 | 1.13.2 | 1.13.2 | Recommended | Backup | Backup and Disaster Recovery for Kubernetes | Optional | Velero backs up and restores Kubernetes clusters for 5G NFs, ensuring data protection and disaster recovery.
Impact: Without backup and recovery capabilities, customers would risk data loss and extended downtime, requiring a full cluster reinstall in case of failure or upgrade. |
| Kyverno | 1.15.0 | 1.13.4 | 1.13.4 | Recommended | Security | Kubernetes Policy Management | Mandatory | Kyverno is a Kubernetes policy engine that allows to manage and enforce policies for resource configurations within a Kubernetes cluster.
Impact: Failing to implement policy enforcement could lead to misconfigurations, resulting in security risks and instability in NF operations, affecting reliability. |
| MetalLB | 0.15.2 | 0.14.4 | 0.14.4 | Recommended | Networking | Load Balancer for Kubernetes | Mandatory | MetalLB provides load balancing and external IP management for 5G NFs in Kubernetes environments.
Impact: MetalLB is used as LB solution in CNE. LB is mandatory for the solution to work. Without load balancing, traffic distribution among NFs may be inefficient, leading to potential bottlenecks and service degradation. |
| CoreDNS | 1.12.0 | 1.12.0 | 1.11.3 | Recommended | Networking | Service Discovery for Kubernetes | Mandatory | CoreDNS is the DNS server in Kubernetes, which provides DNS resolution services within the cluster.
Impact: DNS is an essential part of deployment. Without proper service discovery, NFs would struggle to communicate with each other, leading to connectivity issues and operational failures. |
| Multus | v4.2.1-thick | v4.2.1-thick | 4.1.3 | Recommended | Networking | Networking for Kubernetes traffic segregation | Conditional | Multus enables multiple network interfaces in Kubernetes pods, allowing custom configurations and isolated paths for advanced use cases such as NF deployments, ultimately supporting network segregation.
Impact: Without this capability, connecting NFs to multiple networks could be limited, impacting network performance and isolation. |
| Fluentd | 1.17.1 | 1.17.1 | 1.17.1 | Recommended | Logging | Logging Agent | Mandatory | Fluentd is an open-source data collector that streamlines data collection and consumption, allowing for improved data utilization and comprehension.
Impact: Not utilizing centralized logging can hinder the ability to track NF activity and troubleshoot issues effectively, complicating maintenance and support. |
| OpenSearch | 2.19.1 | 2.19.1 | 2.15.0 | Recommended | Logging | Search/ Analytics/ Logging | Mandatory | OpenSearch provides scalable search and analytics for 5G NFs, enabling efficient data exploration and visualization.
Lack of a robust analytics solution could lead to challenges in identifying performance issues and optimizing NF operations, affecting overall service quality. |
| OpenSearch Dashboard | 2.19.1 | 2.19.1 | 2.15.0 | Recommended | Logging | Dashboard/ Visualization for OpenSearch | Mandatory | OpenSearch Dashboard visualizes and analyzes data for 5G NFs, offering interactive insights and custom reporting.
Impact: Without visualization capabilities, understanding NF performance metrics and trends would be difficult, limiting informed decision-making. |
| AlertManager | 0.28.0 | 0.28.0 | 0.28.0 | Recommended | Alerting | Alerting (Integration with Prometheus) | Mandatory | Alertmanager is a component that works in conjunction with Prometheus to manage and dispatch alerts. It handles the routing and notification of alerts to various receivers.
Impact: Not implementing alerting mechanisms can lead to delayed responses to critical issues, potentially resulting in service outages or degraded performance. |
| prometheus-kube-state-metric | 2.17.0 | 2.16.0 | 2.15.0 | Recommended | Monitoring | Kubernetes Metrics (for Prometheus) | Mandatory | Kube-state-metrics is a service that generates metrics about the state of various resources in a Kubernetes cluster. It's commonly used for monitoring and alerting purposes.
Impact: Without these metrics, monitoring the health and performance of NFs could be challenging, making it harder to proactively address issues. |
| Prometheus Operator | 0.85.0 | 0.83.0 | 0.80.1 | Recommended | Monitoring | Prometheus Instance Management in Kubernetes | Conditional | The Prometheus Operator is used for managing Prometheus monitoring systems in Kubernetes. Prometheus Operator simplifies the configuration and management of Prometheus instances.
Impact: Not using this operator could complicate the setup and management of monitoring solutions, increasing the risk of missed performance insights. |
| prometheus-node-exporter | 1.10.2 | 1.9.1 | 1.8.2 | Recommended | Monitoring | Node-Level Metrics for Prometheus | Mandatory | Node Exporter is a Prometheus exporter for collecting hardware and OS-level metrics from Linux hosts.
Impact: Without node-level metrics, visibility into infrastructure performance would be limited, complicating the identification of resource bottlenecks. |
| Prometheus | 3.6.0 | 3.4.1 | 3.2.0 | Mandatory | Monitoring | Metrics/Monitoring System | Mandatory | Prometheus is a popular open-source monitoring and alerting toolkit. It collects and stores metrics from various sources and allows for alerting and querying.
Impact: Not employing this monitoring solution could result in a lack of visibility into NF performance, making it difficult to troubleshoot issues and optimize resource usage. |
| Grafana | 7.5.17 | 7.5.17 | 9.5.3 | Recommended | Visualization | Monitoring/Visualization Tool | Mandatory | Grafana is a popular open-source platform for monitoring and observability. It provides a user-friendly interface for creating and viewing dashboards based on various data sources.
Impact: Without visualization tools, interpreting complex metrics and gaining insights into NF performance would be cumbersome, hindering effective management. |
| Calico | 3.30.3 | 3.29.3 | 3.29.1 | Recommended | Networking | Networking/Network Security for Kubernetes | Mandatory | Calico provides networking and security for NFs in Kubernetes with scalable, policy-driven connectivity.
Impact: CNI is mandatory for the functioning of 5G NFs. Without CNI and proper plugin, the network could face security vulnerabilities and inadequate traffic management, impacting the reliability of NF communications |
| metrics-server | 0.7.2 | 0.7.2 | 0.7.2 | Recommended | Monitoring | Resource Metrics for Kubernetes | Mandatory | Metrics server is used in Kubernetes for collecting resource usage data from pods and nodes.
Impact: Without resource metrics, auto-scaling and resource optimization would be limited, potentially leading to resource contention or underutilization. |
| snmp-notifier | 2.0.0 | 2.0.0 | 1.6.1 | Recommended | Notification | SNMP Notification Service | Mandatory | snmp-notifier sends SNMP alerts for 5G NFs, providing real-time notifications for network events.
Impact: Without SNMP notifications, proactive monitoring of NF health and performance could be compromised, delaying response to critical issues. |
| Jaeger | 1.72.0 | 1.69.0 | 1.65.0 | Recommended | Tracing | Distributed Tracing | Mandatory | Jaeger provides distributed tracing for 5G NFs, enabling performance monitoring and troubleshooting across microservices.
Impact: Not utilizing distributed tracing may hinder the ability to diagnose performance bottlenecks, making it challenging to optimize NF interactions and user experience. |
| rook | 1.17.7 | 1.16.7 | 1.16.6 | Recommended | Storage | Storage Orchestration | Mandatory | Rook is the Ceph orchestrator for Kubernetes that provides storage solutions. It is used in bm CNE solution.
Impact: CSI is mandatory for the solution to work. Not utilizing Rook could increase the complexity of deploying and managing Ceph, making it difficult to scale storage solutions in a Kubernetes environment. |
| cinder-csi-plugin | 1.33.0 | 1.32.0 | 1.32.0 | Recommended | Storage | Block Storage Plugin | Mandatory | Cinder CSI (Container Storage Interface) plugin is for provisioning and managing block storage in Kubernetes. It is often used in OpenStack environments to provide persistent storage for containerized applications.
Impact: Cinder CSI Plugin is used in OpenStack vCNE solution. Without this integration, provisioning block storage for NFs could be manual and inefficient, complicating storage management. |
3.7 Redhat Openshift Compliance Matrix
The following table lists the planned Redhat Openshift compliance matrix for each network function.
Table 3-7 Redhat Openshift Compliance Matrix
| CNC NF Release | Webscale | RedHat Openshift | Kubernetes | Helm | F5 ASM | F5 SPK |
|---|---|---|---|---|---|---|
| cnDBTier 25.2.201 | 1.3.x | 4.7.x | 1.20.x | 3.12.3 | 1.11.8 | NA |
| 1.5.x | 4.12.x | 1.25.x | 3.12.3 | 1.14.6 | 1.7.11 | |
| OSO 25.2.200 | 1.3.x | 4.7.x | 1.20.x | 3.12.3 | 1.11.8 | NA |
| 1.5.x | 4.12.x | 1.25.x | 3.12.3 | 1.14.6 | 1.7.11 | |
| BSF 25.2.200 | 1.3.x | 4.7.x | 1.20.x | 3.12.3 | 1.11.8 | NA |
| 1.5.x | 4.12.x | 1.25.x | 3.12.3 | 1.14.6 | 1.7.11 | |
| OCCM 25.2.200 | 1.3.x | 4.7.x | 1.20.x | 3.12.3 | 1.11.8 | NA |
| 1.5.x | 4.12.x | 1.25.x | 3.12.3 | 1.14.6 | 1.7.11 | |
| CNCC 25.2.200 | 1.3.x | 4.7.x | 1.20.x | 3.12.3 | 1.11.8 | NA |
| 1.5.x | 4.12.x | 1.25.x | 3.12.3 | 1.14.6 | 1.7.11 | |
| NSSF 25.2.200 | 1.3.x | 4.7.x | 1.20.x | 3.12.3 | 1.11.8 | NA |
| 1.5.x | 4.12.x | 1.25.x | 3.12.3 | 1.14.6 | 1.7.11 |
3.8 Security Certification Declaration
This section lists the security tests and the corresponding dates of compliance for each network function:
3.8.1 BSF Security Certification Declaration
Release 25.2.200
Table 3-8 BSF Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Feb 17, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Jan 13, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Feb 24, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Feb 24, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.
3.8.2 CNC Console Security Certification Declaration
Table 3-9 CNC Console Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Apr 14, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Feb 06, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Apr 14, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Apr 14, 2026 | No findings |
Table 3-10 CNC Console Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Feb 16, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Feb 06, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Feb 16, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Feb 16, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.
3.8.3 cnDBTier Security Certification Declaration
Release 25.2.201
Table 3-11 cnDBTier Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Feb 26, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Feb 26, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Feb 26, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Feb 26, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found or pending during internal security testing.
3.8.4 OCCM Security Certification Declaration
Table 3-12 OCCM Security Certification Declaration
| Compliance Test Description | Test Completion | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Feb 13, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Feb 11, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Feb 13, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Feb 13, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.
3.8.5 NRF Security Certification Declaration
Release 25.2.201
Table 3-13 NRF Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Mar 30, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Mar 30, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Mar 30, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Mar 30, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.
3.8.6 NSSF Security Certification Declaration
Release 25.2.200
Table 3-14 NSSF Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Feb 10, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
Feb 10, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Feb 10, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Feb 10, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.
3.8.7 OCI Adaptor Security Certification
Table 3-15 OCI Adaptor Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
Apr 2, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
NA | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
Apr 2, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
Apr 2, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found or pending during internal security testing.
3.8.8 Policy Security Certification Declaration
Release 25.2.201
Table 3-16 Policy Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
March 18, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
March 10, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
March 20, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
March 20, 2026 | No findings |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.
3.8.9 SCP Security Certification Declaration
Release 25.2.202
Table 3-17 SCP Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
May 05, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
April 01, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
May 05, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
May 05, 2026 | No findings |
Release 25.2.201
Table 3-18 SCP Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
April 01, 2026 | No unmitigated critical or high findings |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
April 01, 2026 | No unmitigated critical or high findings |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
April 01, 2026 | No unmitigated critical or high finding |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
April 01, 2026 | No findings |
3.8.10 SEPP Security Certification Declaration
Table 3-19 SEPP Security Certification Declaration
| Compliance Test Description | Test Completion Date | Summary |
|---|---|---|
| Static Source Code Analysis
Additional Info: Assesses adherence to common secure coding standards |
April 02, 2026 | No unmitigated critical or high findings. Scan done through Fortify. |
| Dynamic Analysis (including fuzz testing)
Additional Info: Tests for risk of common attack vectors such as OWASP Top 10 and SANS 25 |
April 02, 2026 | No unmitigated critical, high, medium, and low findings. Scan done through RestFuzz. |
| Vulnerability Scans
Additional Info: Scans for CVEs in embedded 3rd party components |
April 02, 2026 | No unmitigated critical or high findings. Scan done through Blackduck. |
| Malware Scans
Additional Info: Scans all deliverable software packages for the presence of known malware |
April 02, 2026 | No issues found. Scan done through McAfee. |
Overall Summary: No critical or severity 1 security issues were found during internal security testing.