Security Configuration
The Oracle® Enterprise Session Border Controller (E-SBC) can provide security for VoIP and other multi-media services. E-SBC security includes access control, DoS attack, and overload protection, which help to secure service and protect the network infrastructure. E-SBC security lets legitimate users place a call during attack conditions, while protecting the service itself.
| auth-params | Configure authentication protocol, strategy, and servers. |
| authentication | Configure RADIUS and TACACS authentication. |
| cert-status-profile | Configure the information needed to contact an Online Certificate Status Protocol (OCSP) responder for certificate status. |
| certficate-record | Create a certificate record for either a CA or end entity. |
| dpd-params | Configure parameters to re-establish connections with unreachable Internet Key Exchange (IKE) peers. |
| ipsec-global-config | Configure global IPsec for authenticating and encrypting packets in communication sessions. |
| media-sec-policy | Create a media security policy. |
| password-policy | Create a password policy. |
| sdes-profile | Create a Session Description Protocol Security Descriptions (SDES) profile for media streams. |
| security-association | Configure a manual security association. |
| security-config | Configure security for VoIP and other multi-media services. |
| security-policy | Create a security policy. |
| sipura-profile | Create a SIPURA/Linksys profile. |
| tls-global | Configure session caching to allow a previously authenticated client to re-connect with the unique session identifier from the previous session. |
| tls-profile | Create a profile to define communications security for running SIP over TLS. |
Note:
Click Show Advanced in the navigation pane to display all of the Security objects in the preceding list.Audit Logs
The Oracle® Enterprise Session Border Controller (E-SBC) can record user actions in audit logs by way of the Web GUI. The audit logs record the creation, modification, and deletion of all user-accessible configuration elements, as well as attempted access to critical security data such as public keys. For each logged event, the system provides the associated user-id, date, time, event type, and success or failure data.
You can configure the system to record audit log information in either verbose mode or brief mode. Verbose mode captures the system configuration after every change, and displays both the previous settings and the new settings in addition to the event details. Brief mode displays only the event details. Although you can specify the recording mode, you cannot specify which actions the system records. The following list describes the actions that the system records.
| Global |
|
| Home tab |
|
| Configuration tab |
|
| Widgets tab |
|
| System tab |
|
| Monitor and Trace tab |
|
The system writes audit log events in Comma Separated Values (CSV) lists in the following format:
{TimeStamp,
src-user@address:port,Category,EventType,Result,Resource,Prev,
Detail}The following list describes each value written to an audit log event.
| TimeStamp | Shows the time when the system wrote the event to the audit log. |
| src-user@address:port | Identifies the system that wrote the audit log line. |
| Category | Classifies the event as:
|
| EventType | Identifies the action that caused the event as:
|
| Result | Identifies the outcome of the event as:
|
| Resource | Describes the action within the event. Some of the
numerous actions that the system can log include:
|
| Prev—(verbose mode) | Displays the setting prior to this change. |
| Details—(verbose mode) | Displays additional information about the change,
depending on the following event types:
|
As the E-SBC records audit log data, users with admin privileges can read, copy, and download that information from the Web GUI. No one can delete or edit the original log. You can View, Refresh, and Download audit logs by way of the System tab. When you click File Management, the system displays the File Type drop-down list, which includes "Audit Log" as a selection.
- The specified amount of time since the last transfer elapsed.
- The size of the audit log reached the specified threshold. (Measured in Megabytes)
- The size of the audit log reached the specified percentage of the allocated storage space.
The E-SBC transfers the audit logs to a designated directory on the target SFTP server. The audit log file is stored on the target SFTP server with a filename in the following format: audit<timestamp>. The timestamp is a 12-digit string the YYYYMMDDHHMM format.
- Configure secure FTP push. See "Secure FTP Push Configuration."
- Configure audit logging. See "Configure Audit Logging."
Secure FTP Push Configuration
You can configure the Oracle® Enterprise Session Border Controller (E-SBC) to securely send audit log files to an SFTP push receiver for storage. Configure secure FTP push before you configure audit logging.
It is also common for the SFTP server to run the Linux operating system. For Linux, the command ssh-keygen-e creates the public key that you need to import to the E-SBC. The ssh-keygen-e command sequence requires you to specify the file export type, as follows.
[linux-vpn-1 ~]# ssh-keygen -e
Enter file in which the key is (/root/.ssh/id_rsa/): /etc/ssh/ssh_host_rsa_key.pubIf you cannot access the SFTP server directly, but you can access it from another Linux host, use the ssh-keyscan command to get the key. An example command line follows.
root@server:~$ssh-keyscan -t dsa sftp.server.comConfigure Secure FTP Push with Public Key Authentication
For increased security when sending files from the Oracle® Enterprise Session Border Controller (E-SBC) to an SFTP server, you can choose authentication by public key exchange rather than by password. To use a public key exchange, you must configure public key profiles on both devices and import the key from each device into the other.
The following list of tasks shows the process for configuring authentication by public key between the E-SBC and an SFTP server. For each step in the process, see the corresponding topic for detailed instructions.
- Generate an RSA public key on the E-SBC. See "Generate an RSA Public Key."
- Create a DSA public key on the SFTP server. See "Generate a DSA Public Key."
- Import the DSA public key from the SFTP server into the E-SBC using the known-host option in the Import Key dialog. See "Import a DSA Public Key."
- Add the RSA public key to the authorized_keys file in the .ssh directory on the SFTP server. See "Copy the RSA Public Key to the SFTP Server."
Generate an RSA Public Key
Add a public key profile on the Oracle® Enterprise Session Border Controller (E-SBC) and generate an RSA key. You will later import the RSA key into the SFTP server to enable authentication by way of public key exchange with the E-SBC.
- Generate a DSA public key.
Generate a DSA Public Key
Generate and save a DSA public key on the SFTP server. You will later import the DSA key into the Oracle® Enterprise Session Border Controller (E-SBC) to enable authentication by way of public key exchange with the SFTP server.
- Run the following command on the SFTP server:
ssh-keygen -e -f /etc/ssh/ssh_host_dsa_key.pub | tee sftp_host_dsa_key.pub
- Save the key to the authorized_keys file in the .ssh directory on the SFTP server.
- Import the DSA key into the E-SBC.
Import a DSA Public Key
Import a DSA public key from the SFTP server into the Oracle® Enterprise Session Border Controller (E-SBC).
- Generate and save a DSA public key on the SFTP server.
Perform the following procedure on the E-SBC and select "known-host" for type.
Copy the RSA public key to the SFTP server.
Copy the RSA Public Key to the SFTP Server
Copy the RSA public key from the from the Oracle® Enterprise Session Border Controller (E-SBC) to the authorized_keys file in the .ssh directory on the SFTP server.
- Confirm that the .ssh directory exists on the SFTP server.
- Confirm the following permissions: Chmod 700 for .ssh and Chmod 600 for authorized_keys.
When adding the RSA key to the authorized_keys file, ensure that no spaces occur inside the key. Insert one space between the ssh-rsa prefix and the key. Insert one space between the key and the suffix. For example, ssh-rsa <key> root@1.1.1.1.
- Access the SSH file system on a configured SFTP server with a terminal emulation program.
- Copy the RSA key to the SFTP server, using a text editor such as vi or emacs, and paste the RSA key to the end of the authorized_keys file.
Configure Audit Logging
The Oracle® Enterprise Session Border Controller (E-SBC) provides a means of tracking user actions through Audit Logs. You can specify how the system records audit log information, and where to send the logs for archiving. You can configure the system to record in either brief or verbose mode. Verbose mode captures the system configuration after every change, and displays both the previous and new settings in addition to the event details. Brief mode displays only the event details.
- Configure one or more push receivers to receive the audit logs. See the documentation for the receiver.
- If you want to use public keys for authentication between the E-SBC and the push receiver, configure public key profiles on both devices before configuring audit logging. See "Configure Secure File Transfer with Public Keys."
Configure Login Timeouts
The single instance ssh-config configuration element specifies SSH re-keying thresholds.
TACACS+ Authentication
The Web GUI supports TACACS+ authentication.
TACACS+ provides access control for routers, network access servers, and other networked computing devices by way of one or more centralized servers. The Oracle® Enterprise Session Border Controller (E-SBC), supports TACACS+ authentication and limited accounting services. For accounting services support, the E-SBC supports only authentication success and failure. The E-SBC does not support TACACS+ authentication.
Security Settings
Security configuration from the web GUI consists of creating the building blocks used to establish TLS-secured paths for signaling traffic.
- Configure Certificate Records.
- Configure TLS Profiles, which utilize your certificate records.
- Apply TLS Profiles to SIP Interfaces.
The dialogs available from the Security button allow you to perform the first two steps. You apply TLS profiles to SIP interfaces using controls within the SIP Interface dialog.
Certificate Configuration Process
You can perform the following certificate management tasks from the Web GUI in either Basic Mode or Expert Mode. The process for configuring certificates on the Oracle® Enterprise Session Border Controller (E-SBC) includes the following steps:
- Configure a Certificate Record on the E-SBC. See Add a Certificate Record.
- Generate a Certificate request by the E-SBC. See Generate a Certificate Request.
- Import a Certificate into the E-SBC. See Import a Certificate.
- Reboot the system.
Create a Certificate Record
Use the certificate-record element to add certificate records to the Oracle® Enterprise Session Border Controller (E-SBC).
- If this certificate record is used to present an end-entity certificate, associate a private key with this certificate record by using a certificate request.
- If this certificate record is created to hold a CA certificate or certificate in pkcs12 format, a private key is not required.
- Create TLS profiles, using the certificate records to further define the encryption behavior and to provide an entity that you can apply to a SIP interface.
Generate a Certificate Request
Use the certificate-record element to select a certificate record and generate a certificate request.
- Confirm that the certificate record exists.
To get a certificate authorized by a Certificate Authority (CA), you must generate a certificate request from the certificate record on the device and send it to the CA.
- When the CA replies with the certificate, import the certificate to the device with the corresponding certificate record.
Import a Certificate
Use the certificate-record element to import a certificate into the Oracle® Enterprise Session Border Controller (E-SBC).
Use this procedure to import either a device certificate or an end-station CA certificate for a mutual authentication deployment. You must import the certificate to the corresponding certificate record for the E-SBC. End-station CA certificates may or may not need to be imported against a pre-configured certificate record.
- Apply the corresponding certificate record to the intended SIP interface.
SDES Configuration for a Media Stream
- Create at least one SDES profile that specifies the parameter values to negotiate during the offer-answer exchange.
- Create at least one Media Security Policy that specifies the key exchange protocols and protocol specific profiles.
- Assign the appropriate Media Security Policy to the appropriate realm.
- Create an interface-specific security policy that enables the E-SBC to identify inbound and outbound media streams treated as SRTP and SRTCP.
TLS Profile Configuration
The Transport Layer Security (TLS) profile specifies the information required to run SIP over TLS.
TLS is a cryptographic protocol that provides communication security over the Internet. TLS encrypts the segments of network connections at the Application layer for the Transport layer, using asymmetric cryptography for key exchange, symmetric encryption for confidentiality and message authentication codes for message integrity.
Create a TLS profile, using your certificate records, to further define the encryption behavior and create the configuration element that you apply to the SIP interface. You can configure an end entity certificate and a trusted Certification Authority (CA) certificate for a TLS policy. CA certificates are issued by a CA to itself or to a second CA for the purpose of creating a defined relationship between the two entities. A certificate that is issued by a CA to itself is referred to as a trusted root certificate, because it is intended to establish a point of ultimate trust for a CA hierarchy. Once the trusted root has been established, it can be used to authorize subordinate CAs to issue certificates on its behalf.
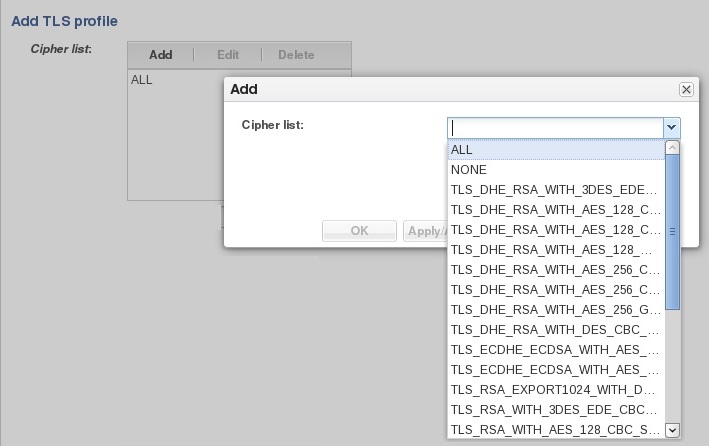
Suite B and Cipher List Support
The Oracle® Enterprise Session Border Controller (E-SBC) supports full control of selecting the ciphers that you want to use for Transport Layer Security (TLS). The system defaults to DEFAULT for the Cipher List parameter in the TLS Profile configuration. Oracle recommends that you delete ALL and add only the particular ciphers that you want, choosing the most secure ciphers for your deployment.
- key-algor—Public key algorithm. Supports RSA and ECDSA. Default: RSA Security. You must select ECDSA to support suite B.
- ecdsa-key-size—ECDSA key size. Supports p256 and p384.
Configure the list of ciphers that you want to use from the Cipher List element in the TLS Profile configuration. The system provides a drop-down list of all supported ciphers. One-by-one, you can add as many ciphers as your deployment requires.
TLS Cipher Updates
Note the following changes to the DEFAULT cipher list.
- TLS_DHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_DHE_RSA_WITH_AES_256_CBC_SHA256
- TLS_DHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_DHE_RSA_WITH_AES_128_CBC_SHA256
- TLS_RSA_WITH_AES_256_CBC_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA384
- TLS_RSA_WITH_AES_256_GCM_SHA384
- TLS_RSA_WITH_AES_128_GCM_SHA256
- TLS_RSA_WITH_AES_128_CBC_SHA
- TLS_RSA_WITH_3DES_EDE_CBC_SHA
- TLS_RSA_WITH_NULL_SHA256 (debug only)
- TLS_RSA_WITH_NULL_SHA (debug only)
- TLS_RSA_WITH_NULL_MD5 (debug only)
- TLS_DHE_RSA_WITH_AES_256_CBC_SHA
- TLS_RSA_WITH_AES_256_CBC_SHA
- TLS_DHE_RSA_WITH_AES_128_CBC_SHA
- TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
Note:
You configure TLS ciphers by way of the cipher-list parameter in tls-profile.Securing Communications Between the E-SBC and SDM with TLS
You can use the Transport Layer Security (TLS) protocol to secure the communications link between the Oracle® Enterprise Session Border Controller (E-SBC) and the Oracle Communications Session Delivery Manager (SDM). Note that the systems use Acme Control Protocol (ACP) for this messaging.
- Configure a TLS profile. The tls-profile object is located under security, where you add certificates, select cipher lists, and specify the TLS version for each profile.
- Configure system-config element's acp-tls-profile parameter to specify this TLS profile.
Note:
This feature requires SDM version 8.1 and above.Add a TLS Profile
Use the tls-profile element to specify the parameters for running SIP over Transport Layer Security (TLS).
- Add one or more certificate records to the Oracle® Enterprise Session Border Controller that you need for this profile.
Create a TLS profile, using your certificate records, to further define encryption behavior and create the configuration element that you apply to the SIP interface. You can configure an end-entity certificate and a trusted Certification Authority (CA) certificate for a TLS profile.
TLS Session Caching
Transport Layer Security (TLS) session caching allows the Oracle® Enterprise Session Border Controller to cache key information for TLS connections, and to set the length of time that the information is cached.
When TLS session caching is not enabled, the Oracle® Enterprise Session Border Controller and a TLS client perform the handshake portion of the authentication sequence in which they exchange a shared secret and encryption keys are generated. One result of the successful handshake is the creation of a unique session identifier. When an established TLS connection is torn down and the client wants to reinstate it, this entire process is repeated. Because the process is resource-intensive, you can enable TLS session caching to avoid repeating the handshake process for previously authenticated clients to preserve valuable Oracle® Enterprise Session Border Controller resources.
When TLS session caching is enabled on the Oracle® Enterprise Session Border Controller, a previously authenticated client can request re-connection using the unique session identifier from the previous session. The Oracle® Enterprise Session Border Controller checks its cache, finds the session identifier, and reinstates the client. This process reduces the handshake to three messages, which preserves system resources.
If the client offers an invalid session identifier, for example, one that the Oracle® Enterprise Session Border Controller has never seen or one that has been deleted from its cache, the system does not allow the re-connection. The system negotiates the connection as a new connection.
Configure TLS-Global Session Caching
Use the tls-global element to enable tls-global session caching to allow the Oracle® Enterprise Session Border Controller (E-SBC) to cache the session identifier for possible re-connection with a former client.
- Configure a TLS profile.
Session caching is a global setting for all TLS operations on the E-SBC. You must enable session caching and set the session cache timeout. Note that the number 0 disables session cache timeout. When the session cache timeout is disabled, cache entries never age and they remain until you delete them. RFC 2246, the TLS Protocol Version 1.0, recommends setting session cache timeout to the maximum of 24 hours.
Configure an SPL Plugin
Use the spl-config element to configure the parameters for integrating System Programming Language (SPL) plugin extensions with the Oracle® Enterprise Session Border Controller (E-SBC).
- Confirm that the SPL engine is installed on the E-SBC.
- Plan the order in which you configure multiple SPL plugins because the E-SBC executes the SPL plugins in the order of configuration.
Note:
The E-SBC includes all SPL plugins, except for Comfort Noise Generation. You must manually upload the Comfort Noise Generation SPL plugin to the E-SBC performing the following procedure.- Execute the SPL plugin file.
- Synchronize the SPL across HA pairs.