Secure OPC and ICCP
This section explains how to secure OPC and ICCP VMDs/VCCs and nodes.
On this page:
Secure OPC
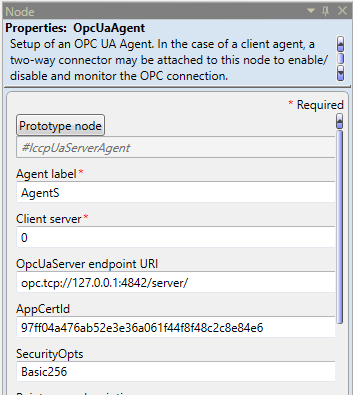
Secure OPC UA is encrypted at the transport layer. The setup of the encrypted connection requires the OPC UA server and the client to authenticate their peers’ certificates. Certificates are stored in certificate stores, which are places where certificates can be stored on a file system. All Windows systems provide a registry-based store called the Windows Certificate Store. From the Oracle Utilities Live Energy Connect (LEC) Configuration Manager, the OPC server and client VMDs have an OPC UA Agent node based on the OpcUaAgent template as shown in the following image:
You can use the following three properties to create a secure OPC UA connection:
- AppCertId (optional): Specifies the application certificate used by this OPC UA client or server. Specify the ID (thumbprint) of a certificate that was previously created and added to the appropriate Windows Certificate Store.
- Default Behavior: Required if SecurityOpts is specified as one of the secure options, otherwise the LEC Server’s OPC UA client/server will fail to start.
- SecurityOpts: Specifies the security modes to use:
- NONE means that no encryption is available (server) or requested (client).
- Basic256 means the Basic256 mode is used by the server. Invalid for client.
- Basic128Rsa15 means the Basic128Rsa15 mode is used by the server. Invalid for client.
- Basic256Sha256 means the Basic1256Sha256 mode is used by the server. Invalid for client.
- ALL means allow any of the above modes as a server. Invalid for client.
- BEST is a shortcut for Basic256Rsa256 as a server, or to use the best available secure option as a client.
Setting Secure OPC Properties in an LEC IFE Instance
The security properties are set in an LEC IFE instance at the time the header batch file is loaded (see the example AppTestAHeader.csv header file). This file is described in its entirety in Header Batch File Definitions. To ensure the security properties in the nodes AgentS and AgentC are set correctly, you need to edit the header batch file located in C:\ProgramData\LiveEnergyConnect\Config.
Search for the table header in the batch file that begins with the prototype node #IccpUaServerAgent. Prototype nodes begin with the pound sign (#). This line identifies all the prototype node properties that will be set by the batch file. These properties are identified by brackets (<>).
Example 1
#IccpUaServerAgent,<ServerIP>,<AppCertId>,<SecurityOpts>,<PointsPerSub>,<ServerNam e>,<PublishingInterval>,<CodeMapFile>,<MaxSubs>,<SubsPerSession>,<MaxSessions>
The next line identifies the actual values used for these fields in the agent node for the local OPC UA server. These values must have the exact same sequence as shown in Example 1.
Example 2
AgentS,opc.tcp://127.0.0.1:4842/server/,,NONE,,,,,50,10,5
The following table shows the Agent label and the OpcUaServer IP address followed by each security-related property defined in the second example line from the batch file as shown in Example 2.
| Agent label | OpcUaServer IP | AppCertId | SecurityOpts |
|---|---|---|---|
|
AgentS |
opc.tcp://127.0.0.1:4842/server/ |
Not set |
NONE |
AgentS is the agent label, which maps to the prototype #IccpUaServerAgent node in the preceding line, and opc.tcp://127.0.0.1:4842/server/ is the OPC UA Server IP address, which maps to <ServerIP>.
If there is no specification (not set), as shown under the AppCertId field, then22 the application certificate ID will be generated by LEC Server.
NONE means there is no encryption available (server) or requested (client).
- Specify your own values for the AppCertId, SecurityOpts properties in the same order as is in the line shown in Example 1. The order of these properties might differ in your header file.
- Repeat the same process for the OPC UA client agent. Search for the line beginning with the prototype node #IccpUaClientAgent, specifying your own values for the AppCertId and SecurityOpts properties in the following line, similar to Example 2 but with appropriate values for the client.
- Stop LEC Server and reload the header file.
- Restart LEC Server.
Disabling Secure OPC in an LEC Server Instance
To stop using Secure OPC, you will need to clear the security properties that are set in an LEC IFE instance at the time the header batch file is loaded. To ensure the security properties in the nodes based on the OpcUaAgent template, called AgentS and AgentC, are cleared, you need to edit the header batch file, named AppTestAHeader.csv.
Search for the table header in the batch file that begins with the prototype node #IccpUaServerAgent. Prototype nodes begin with the pound sign (#). This line identifies all prototype node properties that will be set or cleared by the batch file. These properties are identified by brackets (<>). Note that these properties can be listed in any order; however, the following line shown in Example 2 must use the same sequence.
Example 1
#IccpUaServerAgent,<ServerIP>,<AppCertId>,<SecurityOpts>,<PointsPerSub>,<ServerNam e>,<PublishingInterval>,<CodeMapFile>,<MaxSubs>,<SubsPerSession>,<MaxSessions>
The next line identifies the actual values used for these fields in the agent node for the local OPC UA server. These values must have the exact same sequence as <AppCertId> and <SecurityOpts> shown in Example 1.
Example 2
AgentS,opc.tcp://127.0.0.1:4842/server/,,,,,,,50,10,5
The following table shows the Agent label and the OpcUaServer IP address followed by each security-related property that is defined in the second example line from the batch
| Agent label | OpcUaServer IP | AppCertId | SecurityOpts |
|---|---|---|---|
|
AgentS |
opc.tcp://127.0.0.1:4842/server/ |
|
|
AgentS is the agent label, which maps to the prototype #IccpUaServerAgent node in the preceding line, and opc.tcp://127.0.0.1:4842/server/ is the OPC UA Server IP address, which maps to <ServerIP>.
The empty space, nothing specified, usually indicates the default, which means the application certificate ID will be generated by LEC Server. However, in this instance, it actually clears the value for the AppCertId property.
The empty space under the SecurityOpts property clears the value for this property, too.
- Clear the values for the AppCertId, AuthorizedCerts, SecurityOpts properties in the same order as is in the line shown in Example 1. Note that the order of the prototype node properties in your batch file might differ from the order shown in Example 1.
- Repeat the same process for the OPC UA client agent. Search for the line beginning with the prototype node #IccpUaClientAgent, clearing the values for the AppCertId and SecurityOpts properties in the correct order.
- Stop LEC Server and reload the header file.
- Restart LEC Server.
Windows Certificate Stores
LEC Server’s OPC UA server and client access certificates stored in the Windows Certificate Store.
Note: The Oracle Utilities Live Energy Connect (LEC Server) software was formerly known as LiveData RTI Server. For this reason, the following certificate sub stores still reference LiveData.
The following sub-stores are created and used:
- LocalMachine\LiveData OPCUA Server App – where LEC’s OPC UA server certificates are stored.
- LocalMachine\LiveData OPCUA Server Trusted – where LEC’s OPC UA server looks to find public certificates of connecting clients. If a copy of the client’s presenting certificate is stored here, the client is considered trusted and the connection may be accepted. CA certificates/chains also be stored here. This allows any presented client certificate signed by the CA to be considered trusted. Certificate Revocation Lists (CRLs) may also be imported there to disallow certain client certificates signed by CAs stored here.
- LocalMachine\LiveData OPCUA Server Issuer – where LEC’s OPC UA server looks for CA certificates/chains to validate trusted client certificates if said certificates are not self-signed.
- LocalMachine\LiveData OPCUA Server Rejected – where LEC’s OPC UA server stores certificates presented by connecting clients that are not trusted. Rejected certificates may be copied or moved from here to the trusted store.
- LocalMachine\LiveData OPCUA Client App – where LEC’s OPC UA client certificates are stored.
- LocalMachine\LiveData OPCUA Client Trusted – where LEC’s OPC UA client looks to find public certificates presented by servers it is connecting to. If a copy of the server’s presenting certificate is stored here, the server is considered trusted and the connection may proceed. CA certificates/chains also be stored here. This allows any presented server certificate signed by the CA to be considered trusted. Certificate Revocation Lists (CRLs) may also be imported there to disallow certain client certificates signed by CAs stored here.
- LocalMachine\LiveData OPCUA Client Issuer – where LEC’s OPC UA client looks for CA certificates/chains to validate trusted server certificates if said certificates are not self-signed.
- LocalMachine\LiveData OPCUA Client Rejected – where LEC’s OPC UA client stores certificates presented by connected servers that are not trusted. Rejected certificates may be copied or moved from here to the trusted store.
Certificate Details and Requirements
The LEC Server’s Secure OPC UA client and server utilize X.509 V3 certificates for encryption and peer authentication. Below are specific certificate requirements:
- A minimum key length of 2048 bits is required, with a maximum of 4096 bits allowed.
- A Common Name (CN) is required, though its content is not important.
- Key Usage required usages: Digital Signature, Non-Repudiation, Key Encipherment, Data Encipherment, Certificate Signing
- Certain X.509 V3 extensions are required:
- Subject Alternative Name - must be provided with the following names:
- URI - (at least one) of the form URL=urn:<host>:<peer application name>
- At least one of the following:
- IP Address – one or more specifying and IP address to be associated with the endpoint, as seen by the receiving client or server.
- DNS Name – one of more specifying the hostname to be associated with the endpoint, as seen by the receiving client or server.
- Basic Constraints – must be provided with self-signed certificates to indicate:
- Subject Type = End Entity
- Path Length Constraint = 0
- Enhanced Key Usage – Server Authentication and Client Authentication required
- Subject Alternative Name - must be provided with the following names:
LEC Server ships with and installs OPC UA client and server certificates that is suitable for testing locally on a single machine, with OPC UA client and server endpoints specified with the localhost IP address 127.0.0.1. Also included is MakeLegalUaCert.bat that can be used and modified to create suitable certificates for network connections.
Secure ICCP
Secure ICCP provides security for the transport and application layers with certificates.
You need to set up Secure ICCP when you configure your LEC Server. Refer the Oracle Utilities Live Energy Connect Installation Guide and the Oracle Utilities Live Energy Connect Certificate Deployment Procedure for Using Secure ICCP document for instructions on configuring LEC Server for Secure ICCP.