| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Solaris Trusted Extensions Label Administration Oracle Solaris 11 Express 11/10 |
| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Solaris Trusted Extensions Label Administration Oracle Solaris 11 Express 11/10 |
1. Labels in Trusted Extensions Software (Overview)
2. Planning Labels in Trusted Extensions(Tasks)
3. Creating a Label Encodings File (Tasks)
4. Labeling Printer Output (Tasks)
5. Customizing the LOCAL DEFINITIONS Section (Tasks)
6. Planning an Organization's Encodings File (Example)
Identifying the Site's Label Requirements
Satisfying Information Protection Goals
Trusted Extensions Features That Address Labeling and Access
Climbing the Security Learning Curve
Analyzing the Requirements for Each Label
Requirements for CONFIDENTIAL: INTERNAL_USE_ONLY
Requirements for CONFIDENTIAL: NEED_TO_KNOW
Requirements for CONFIDENTIAL: REGISTERED
Names of Groups With NEED_TO_KNOW Label
Understanding the Set of Labels
Planning the Use of Words in MAC
Planning the Use of Words in Labeling System Output
Planning Unlabeled Printer Output
Planning for Supporting Procedures
Rules for Protecting a REGISTERED File or Directory
Rules for Configuring Printers
Rules for Handling Printer Output
Planning the Classification Values in a Worksheet
Planning the Compartment Values and Combination Constraints in a Worksheet
Planning the Clearances in a Worksheet
Planning the Printer Banners in a Worksheet
Planning the Channels in a Worksheet
Planning the Minimum Labels in an Accreditation Range
Planning the Colors in a Worksheet
Editing and Installing the label_encodings File
Specifying the Classifications
Specifying the Sensitivity Labels
Specifying the Information Labels
Specifying the Printer Banners
Specifying the Accreditation Range
Specifying the Local Definitions
Specifying the Default User Labels
Specifying the Column Headings in Label Builders
Configuring Users and Printers for Labels
SecCompany, Inc. is the name of a fictional company whose label requirements are modeled in this example. To protect the corporation's intellectual property, the company's legal department mandates that employees use three labels on all sensitive email and printed materials. The three labels, from most sensitive to least sensitive, are the following:
Confidential: Registered
Confidential: Need To Know
Confidential: Internal Use Only
The legal department also approves the use of an optional fourth label, Public. The Public label is for information that can be distributed to anyone without restrictions.
At SecCompany, the manager in charge of information protection makes use of all possible channels to communicate labeling requirements. However, some employees do not understand the requirements. Other employees forget about the requirements or ignore them. Even when labels are properly applied, the information is not always properly handled, stored, and distributed. For example, reports indicate that registered information is sometimes found unattended. Copies of registered information have been left next to copy machines and printers, in break rooms, and in lobbies.
The legal department wants a better way to ensure that information is properly labeled without relying totally on employee compliance. The system administrators want a better way to control the following:
Who can view sensitive information
Who can modify sensitive information
Which information is printed on which printers
How printer output is handled
How email at various levels of security is distributed internally and externally
Trusted Extensions software does not leave labeling decisions up to the discretion of computer users. All printer output from print servers that are configured with Trusted Extensions is automatically labeled according to the site's requirements.
Even though security was not yet fully understood at the company, the manager in charge of information protection knew that Trusted Extensions could implement the following features immediately:
Automatic labeling of print jobs
Printers with restricted access by label
Email with restricted access by label
In Trusted Extensions, each print job is automatically assigned a label. The label corresponds either to the level at which the user is working or to the user's level of responsibility.
The following figure shows an employee working at a level of INTERNAL_USE_ONLY. At this level, the work should be accessible only by people who have signed nondisclosure agreements with SecCompany. When an employee who has signed a nondisclosure agreement sends email to the printer, the print job is automatically assigned the label INTERNAL_USE_ONLY.
Figure 6-1 Automatic Labeling of Print Jobs
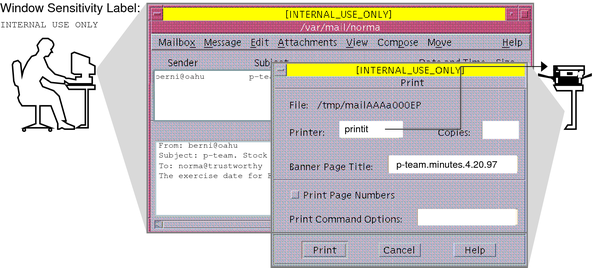
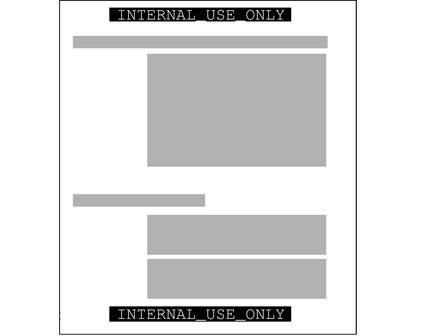
The following figure shows the email that was sent to the printer in Figure 6-1. The user's working label, INTERNAL_USE_ONLY, is printed at the top and bottom of every page.
Figure 6-2 Label Automatically Printed on Body Pages
Banner and trailer pages can include handling instructions. Printed below the sensitivity label, handling instructions provides distribution instructions for the printed material. The following example shows the text on the banner page of a print job. The sensitivity level of the print job is NEED_TO_KNOW in the department of HUMAN_RESOURCES.
NEED_TO_KNOW HR
DISTRIBUTE_ONLY_TO HUMAN RESOURCES (NON-DISCLOSURE AGREEMENT REQUIRED)
The instructions state that the information is only for human resources personnel who need to know the information. Also, the human resources personnel must have signed a nondisclosure agreement.
To retrieve a labeled printout, users must have access to a printer that prints at the label of the print job. A printer can be configured to print jobs at every label. For security, printers are configured to print only jobs within a restricted label range.
For example, Figure 6-3 illustrates that the legal department's printer has been set up to print only jobs that have been assigned one of three labels:
NEED_TO_KNOW LEGAL – Can be viewed only by permanent employees of SecCompany with a need to know within the legal department
INTERNAL_USE_ONLY – Can be viewed only by permanent employees of SecCompany and customers who have signed nondisclosure agreements
PUBLIC – Can be viewed by anyone
This printer setup excludes jobs that are sent at any other label. For example, this printer would reject jobs at the labels NEED_TO_KNOW MARKETING and REGISTERED.
Figure 6-3 How a Printer With a Restricted Label Range Handles Print Jobs
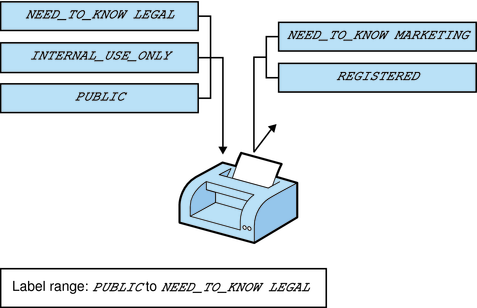
Printers in locations that are accessible to all employees can be similarly restricted. For example, printers can be configured to print jobs only at the two labels that all employees can view, INTERNAL_USE_ONLY and PUBLIC.
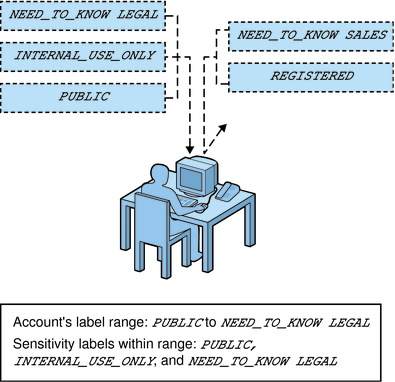
Similar to how the printer label range controls which jobs can be printed on a particular printer, a user's account label range limits which email the person can handle. The following figure shows email that is being labeled at the sensitivity label of the user's mail application. The email is sent to the mail application at that label.
Figure 6-4 User Receiving Email Within the Account Label Range
At SecCompany, gateways to the Internet are configured to screen email so that emails at inappropriate labels cannot be sent outside of the company. Inappropriate labels are any labels except PUBLIC.