| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Identity Synchronization for Windows 6.0 Installation and Configuration Guide |
| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Identity Synchronization for Windows 6.0 Installation and Configuration Guide |
Part I Installing Identity Synchronization for Windows
Windows NT Connector Subcomponents
System Components Distribution
Directory Server Connector and Plug-in
Windows NT Connector and Subcomponents
How Identity Synchronization for Windows Detects Changes in Directory Sources
How Directory Server Connectors Detect Changes
How Active Directory Connectors Detect Changes
How Windows NT Connectors Detect Changes
Using the Password Filter DLL to Obtain Clear-Text Passwords
Using On-Demand Password Synchronization to Obtain Clear-Text Passwords
Deployment Example: A Two-Machine Configuration
6. Synchronizing Existing Users and User Groups
9. Understanding Audit and Error Files
Part II Identity Synchronization for Windows Appendixes
A. Using the Identity Synchronization for Windows Command Line Utilities
B. Identity Synchronization for Windows LinkUsers XML Document Sample
C. Running Identity Synchronization for Windows Services as Non-Root on Solaris
D. Defining and Configuring Synchronization User Lists for Identity Synchronization for Windows
E. Identity Synchronization for Windows Installation Notes for Replicated Environments
This section explains how user entry and password changes are detected by Sun Java System Directory Server (Directory Server), Windows Active Directory, and Windows NT Connectors.
The information is organized as follows:
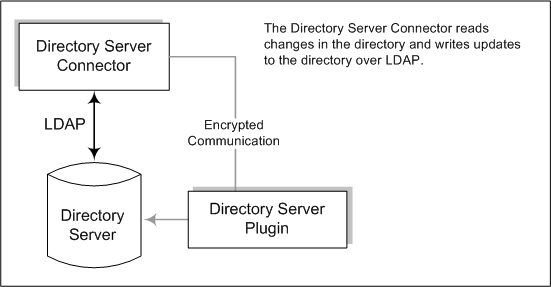
The Directory Server Connector examines the Directory Server retro changelog over LDAP to detect user entry and password change events. The Directory Server Plug-in helps the Connector do the following:
For more information about retro changelog, see Replication and the Retro Change Log Plug-In in Sun Directory Server Enterprise Edition 7.0 Reference.
Capture clear-text passwords by encrypting them and then making them available in the retro changelog. Without the Plug-in, only hashed passwords appear in the retro changelog, and hashed passwords cannot be synchronized.
Perform on-demand password synchronization with Active Directory. No Identity Synchronization for Windows components need to be installed in a Windows topology (See Using On-Demand Password Synchronization to Obtain Clear-Text Passwords.
Figure 1-4 How Directory Server Connectors Detect Changes
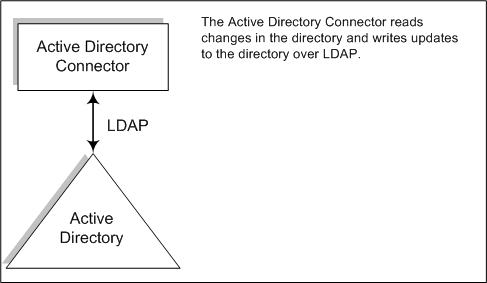
The Windows 2000/2003 Server Active Directory Connector detects user entry and password changes by examining the Active Directory USNChanged and PwdLastSet attribute values.
Unlike the Directory Server’s retro changelog, when you change attributes in an entry, Active Directory does not report which attributes changed. Instead, Active Directory identifies entry changes by incrementing the USNchanged attribute. To detect changes to individual attributes, an Active Directory Connector uses an in-process database called the object cache. The object cache stores a hashed copy of each Active Directory entry, which allows the Connector to determine exactly which attributes were modified in the entry.
You are not required to install Active Directory Connectors on Windows. These connectors can also run on other operating systems such as Solaris or Red Hat Linux, and detect or make changes remotely over LDAP.
Figure 1-5 How Active Directory Connectors Detect Changes
The Windows NT Connector detects user entry and password changes by examining the Security Log for audit events about user objects. Auditing must be enabled or Identity Synchronization for Windows cannot read log messages from Windows NT machine. To verify that audit logging is enabled, see Enabling Auditing on a Windows NT Machine.
Figure 1-6 How Windows NT Connectors Detect Changes
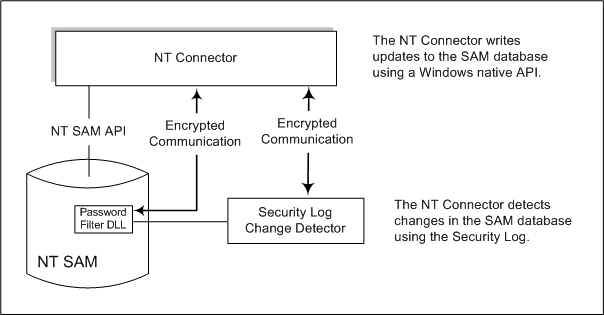
For a description of the Change Detector and the Password Filter DLL subcomponents, see Windows NT Connector Subcomponents.
This section explains two ways to obtain clear-text passwords. Clear-text passwords are needed to propagate password changes between Windows and Directory Server sources.
Windows NT Connectors must obtain clear-text passwords to propagate password updates to the Sun Java System Directory Server. However, you cannot extract clear-text passwords from a Windows directory. By the time passwords are stored in the directories, the passwords have already been encrypted.
Windows NT provides a Password Filter DLL interface that allows components to capture clear-text passwords before they are stored in a directory permanently.
While Active Directory supports the same password filter as Windows NT, you must install the Password Filter DLL on every domain controller (not the Primary Domain Controller used by Window NT). Because this can be a significant installation burden, Identity Synchronization for Windows uses a different approach, called on-demand password synchronization, to synchronize password changes from Active Directory to Directory Server.
On-demand password synchronization provides a method to obtain new password values on Directory Server when users try to login after their password change on Windows 2000/2003.
On-demand password synchronization also allows you to synchronize passwords on Active Directory without using the Password Filter DLL.
The on-demand password synchronization process is as follows:
The user presses Ctrl-Alt-Del on a machine running Windows and changes his or her password. The new passwords are stored in Active Directory.
The Active Directory Connector polls the system at scheduled intervals.
When the Connector detects the password change, based on changes made to the USNchanged (Update Sequence Number) and PwdLastSet attributes, the Connector publishes a message on Message Queue about the password change. The message is transferred on an SSL-encrypted channel.
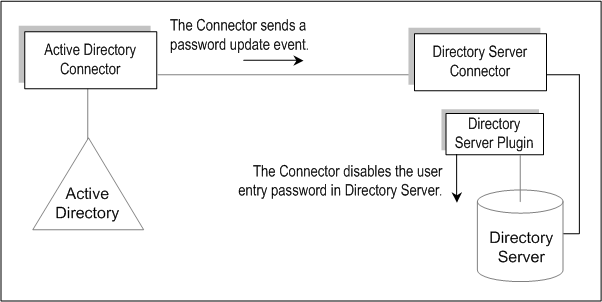
The Directory Server Connector receives the password change message from Message Queue (over SSL).
The Directory Server Connector sets the user entry’s dspswvalidate attribute to true, which invalidates the old password and alerts the Directory Server Plug-in of the password change.
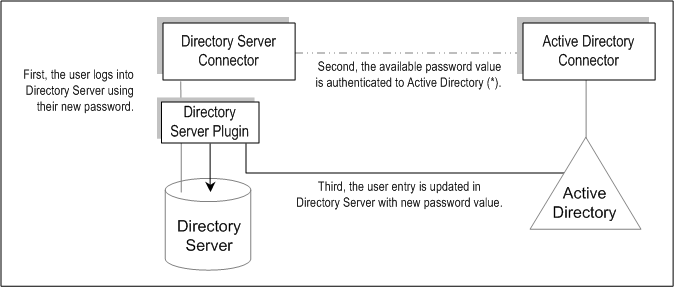
When the user tries to log in, using an LDAP application (such as Portal Server) to authenticate against the Directory Server, the Sun Java System Directory Server Plug-in detects that the password value in the Directory Server entry is invalid.
The Directory Server Plug-in searches for the corresponding user in Active Directory. When the Plug-in finds the user, the Plug-in tries to bind to Active Directory using the password provided when the user tried logging in to Directory Server.
If the bind against Active Directory succeeds, the Directory Server Plug-in sets the password and removes the invalid password flag from the user entry on Directory Server allowing the user to log in.
Identity Synchronization for Windows takes many precautions to ensure that you do not lose user change events, even when components become temporarily unavailable. Identity Synchronization for Windows’ reliability is similar to the TCP network protocol. TCP guarantees that even over a loosely and intermittently connected network, it will eventually deliver all data in order. Data sent during a temporary network outage is queued while the network is down and re-delivered after connectivity is restored. Identity Synchronization for Windows will eventually detect and apply user change events if one of the following components becomes temporarily unavailable:
Connector
Directory Server
Message Queue
Active Directory domain controller
Windows NT Primary Domain Controller
System manager
Configuration directory
If one of these components is not available, Identity Synchronization for Windows will delay synchronization until the affected component is available and contains all changes, even to passwords. This version of Identity Synchronization for Windows does not support Sun Cluster software or other true high-availability solutions. Because users do not interact with Identity Synchronization for Windows directly, high availability is not usually required. If you experience a catastrophic failure, you can reinstall Identity Synchronization for Windows components and use the idsync resync command to resynchronize all directory sources.
In most situations, when a component is unavailable, the program queues synchronization events and applies them only when the component becomes available. There are two exceptions to this process:
In a multimaster replication (MMR) Directory Server environment, external changes to Windows users can be synchronized to the preferred or secondary Directory Servers.
If the preferred Directory Server is unavailable, the Directory Server Connector will apply changes to one of the available secondary servers from the MMR topology.
While the Active Directory Connector can communicate with a single Active Directory domain controller only, the Directory Server Plug-in can fail between all Active Directory domain controllers while performing on-demand password synchronization. This point is where failover is most important. If the Directory Server Plug-in cannot contact an Active Directory domain controller to verify a user's new password, the user cannot log in to Directory Server.