| Skip Navigation Links | |
| Exit Print View | |
|
Trusted Extensions User's Guide Oracle Solaris 10 8/11 Information Library |
| Skip Navigation Links | |
| Exit Print View | |
|
Trusted Extensions User's Guide Oracle Solaris 10 8/11 Information Library |
1. Introduction to Trusted Extensions Software
2. Logging In to Trusted Extensions (Tasks)
Desktops and Login in Trusted Extensions
Trusted Extensions Login Process
Identification and Authentication During Login
Review Security Attributes During Login
Logging In to Trusted Extensions
Identify and Authenticate Yourself to the System
Logging In Remotely to Trusted Extensions
How to Log In to a Remote Trusted Extensions Desktop
3. Working in Trusted Extensions (Tasks)
The following tasks step you through logging in to Trusted Extensions. You review and specify security information before reaching the desktop.
Be sure to type your username exactly as your administrator assigned it to you. Pay attention to spelling and capitalization.
Go to Choose a Trusted Desktop after your restart.
Press Return to confirm your username.
 | Caution - You should never see the trusted stripe when the login screen appears. If you ever see the trusted stripe while attempting to log in or unlock the screen, do not type your password. There is a possibility that you are being spoofed. A spoof is when an intruder's program is masquerading as a login program to capture passwords. Contact your security administrator immediately. |
For security purposes, the characters do not display in the field. The system compares the login name and password against a list of authorized users.
Troubleshooting
If the password that you provided is incorrect, a dialog box appears with the message:
Login incorrect; please try again.
Click OK to dismiss the error dialog box. Then, type the correct password.
If you do not restrict yourself to a single label, you can view data at different labels. The range in which you can operate is bounded at the upper end by the session clearance and at the lower end by the minimum label that your administrator assigned to you.
Always check that nothing is suspicious about the last login, such as an unusual time of day. If you have reason to believe that the time is not accurate, contact your security administrator.
Figure 2-1 Last Login Dialog Box
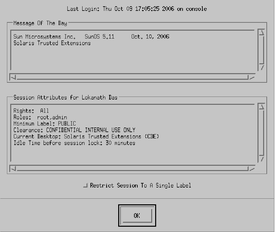
The Message of the Day field can contain warnings about scheduled maintenance or security problems. Always review the information in this field.
As Figure 2-1 shows, the Last Login dialog box indicates any roles that you can assume, your minimum label, and other security characteristics.
Click the Restrict Session to a Single Label button to log in to a single-label session.
You are presented with a label builder. If you are logging in at a single label, the label builder describes your session label. In a multilevel system, the label builder enables you to choose your session clearance.
Figure 2-2 Label Builder
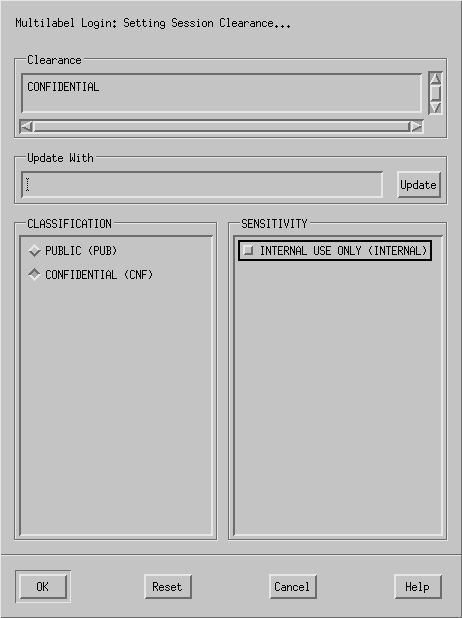
Deselect the current clearance, and click a classification and a sensitivity label.
Or, in the Clearance field, type a clearance.
Or, in the Update With field, type a label.
Deselect the current label, and click a different classification.
Or, in the Update With field, type a label.
The trusted desktop that you chose, either Trusted CDE or Trusted JDS, appears.
Workstations can be restricted to a limited range of session clearances and labels. For example, a workstation in a lobby might be limited to PUBLIC labels only. If the label or session clearance that you specify is not accepted, check with an administrator to determine if the workstation is restricted.
In a standard login, the shell initialization files are sourced at startup to provide a customized environment. In a failsafe login, the default values are applied to your system and no shell initialization files are sourced.
In Trusted Extensions, failsafe login is protected. Only superuser can access failsafe login.