| Skip Navigation Links | |
| Exit Print View | |

|
Oracle Solaris Administration: Security Services Oracle Solaris 11 Information Library |
| Skip Navigation Links | |
| Exit Print View | |

|
Oracle Solaris Administration: Security Services Oracle Solaris 11 Information Library |
1. Security Services (Overview)
Part II System, File, and Device Security
2. Managing Machine Security (Overview)
3. Controlling Access to Systems (Tasks)
4. Virus Scanning Service (Tasks)
5. Controlling Access to Devices (Tasks)
6. Using the Basic Audit Reporting Tool (Tasks)
7. Controlling Access to Files (Tasks)
Part III Roles, Rights Profiles, and Privileges
8. Using Roles and Privileges (Overview)
9. Using Role-Based Access Control (Tasks)
10. Security Attributes in Oracle Solaris (Reference)
Part IV Cryptographic Services
11. Cryptographic Framework (Overview)
12. Cryptographic Framework (Tasks)
Part V Authentication Services and Secure Communication
14. Network Services Authentication (Tasks)
17. Using Secure Shell (Tasks)
19. Introduction to the Kerberos Service
20. Planning for the Kerberos Service
21. Configuring the Kerberos Service (Tasks)
22. Kerberos Error Messages and Troubleshooting
23. Administering Kerberos Principals and Policies (Tasks)
Ways to Administer Kerberos Principals and Policies
Command-Line Equivalents of the SEAM Tool
The Only File Modified by the SEAM Tool
Print and Online Help Features of the SEAM Tool
Working With Large Lists in the SEAM Tool
Administering Kerberos Principals
Administering Kerberos Principals (Task Map)
Automating the Creation of New Kerberos Principals
How to View the List of Kerberos Principals
How to View a Kerberos Principal's Attributes
How to Create a New Kerberos Principal
How to Duplicate a Kerberos Principal
How to Modify a Kerberos Principal
How to Delete a Kerberos Principal
Administering Kerberos Policies
Administering Kerberos Policies (Task Map)
How to View the List of Kerberos Policies
How to View a Kerberos Policy's Attributes
How to Create a New Kerberos Policy
How to Duplicate a Kerberos Policy
How to Modify a Kerberos Policy
How to Delete a Kerberos Policy
Using the SEAM Tool With Limited Kerberos Administration Privileges
Administering Keytab Files (Task Map)
How to Add a Kerberos Service Principal to a Keytab File
How to Remove a Service Principal From a Keytab File
How to Display the Keylist (Principals) in a Keytab File
How to Temporarily Disable Authentication for a Service on a Host
24. Using Kerberos Applications (Tasks)
25. The Kerberos Service (Reference)
This section provides the step-by-step instructions used to administer principals with the SEAM Tool. This section also provides examples of command-line equivalents, when available.
|
Even though the SEAM Tool provides ease-of-use, it doesn't provide a way to automate the creation of new principals. Automation is especially useful if you need to add 10 or even 100 new principals in a short time. However, by using the kadmin.local command in a Bourne shell script, you can do just that.
The following shell script line is an example of how to automate the creation of new principals:
awk '{ print "ank +needchange -pw", $2, $1 }' < /tmp/princnames |
time /usr/sbin/kadmin.local> /dev/null
This example is split over two lines for readability. The script reads in a file called princnames that contains principal names and their passwords, and adds them to the Kerberos database. You would have to create the princnames file, which contains a principal name and its password on each line, separated by one or more spaces. The +needchange option configures the principal so that the user is prompted for a new password during login with the principal for the first time. This practice helps to ensure that the passwords in the princnames file are not a security risk.
You can build more elaborate scripts. For example, your script could use the information in the name service to obtain the list of user names for the principal names. What you do and how you do it is determined by your site's needs and your scripting expertise.
An example of the command-line equivalent follows this procedure.
See How to Start the SEAM Tool for more information.
$ /usr/sbin/gkadmin
The list of principals is displayed.
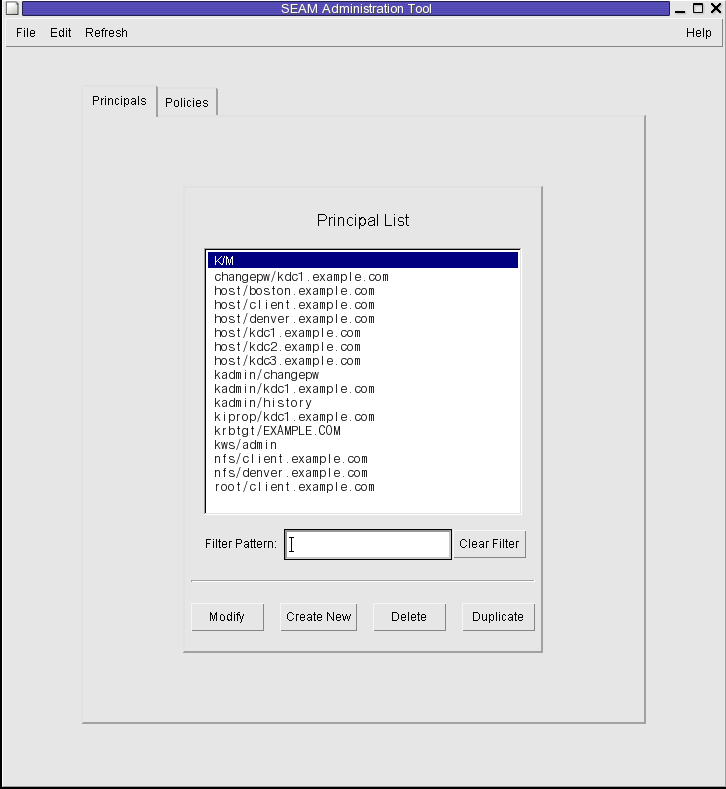
Type a filter string in the Filter field, and press Return. If the filter succeeds, the list of principals that match the filter is displayed.
The filter string must consist of one or more characters. Because the filter mechanism is case sensitive, you need to use the appropriate uppercase and lowercase letters for the filter. For example, if you type the filter string ge, the filter mechanism displays only the principals with the ge string in them (for example, george or edge).
If you want to display the entire list of principals, click Clear Filter.
Example 23-1 Viewing the List of Kerberos Principals (Command Line)
In the following example, the list_principals command of kadmin is used to list all the principals that match kadmin*. Wildcards can be used with the list_principals command.
kadmin: list_principals kadmin* kadmin/changepw@EXAMPLE.COM kadmin/kdc1.example.con@EXAMPLE.COM kadmin/history@EXAMPLE.COM kadmin: quit
An example of the command-line equivalent follows this procedure.
See How to Start the SEAM Tool for more information.
$ /usr/sbin/gkadmin
The Principal Basics panel that contains some of the principal's attributes is displayed.
Three windows contain attribute information. Choose Context-Sensitive Help from the Help menu to get information about the various attributes in each window. Or, for all the principal attribute descriptions, go to SEAM Tool Panel Descriptions.
Example 23-2 Viewing a Kerberos Principal's Attributes
The following example shows the first window when you are viewing the jdb/admin principal.
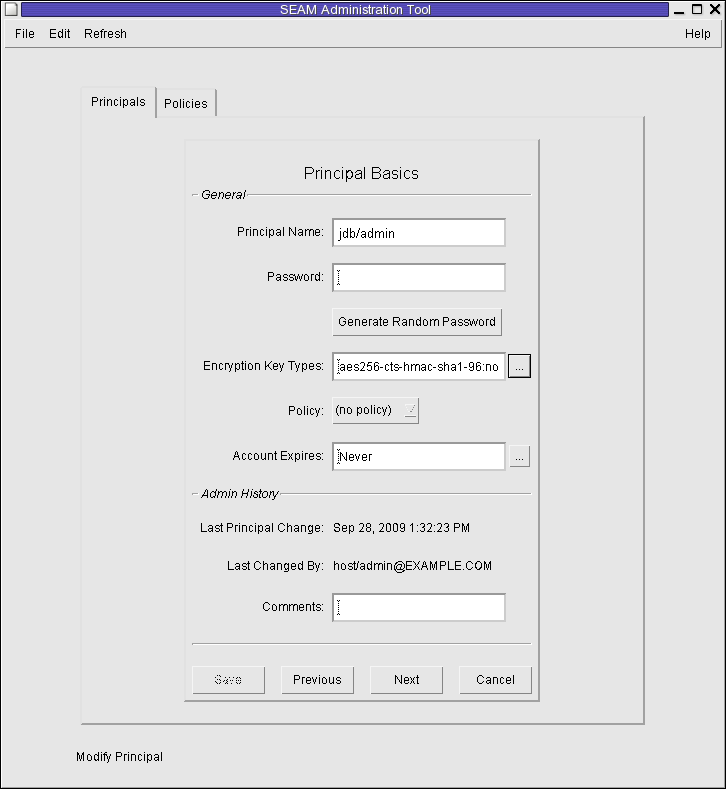
Example 23-3 Viewing a Kerberos Principal's Attributes (Command Line)
In the following example, the get_principal command of kadmin is used to view the attributes of the jdb/admin principal.
kadmin: getprinc jdb/admin Principal: jdb/admin@EXAMPLE.COM Expiration date: [never] Last password change: [never] Password expiration date: Wed Apr 14 11:53:10 PDT 2011 Maximum ticket life: 1 day 16:00:00 Maximum renewable life: 1 day 16:00:00 Last modified: Mon Sep 28 13:32:23 PST 2009 (host/admin@EXAMPLE.COM) Last successful authentication: [never] Last failed authentication: [never] Failed password attempts: 0 Number of keys: 1 Key: vno 1, AES-256 CTS mode with 96-bit SHA-1 HMAC, no salt Key: vno 1, AES-128 CTS mode with 96-bit SHA-1 HMAC, no salt Key: vno 1, Triple DES with HMAC/sha1, no salt Key: vno 1, ArcFour with HMAC/md5, no salt Key: vno 1, DES cbc mode with RSA-MD5, no salt Attributes: REQUIRES_HW_AUTH Policy: [none] kadmin: quit
An example of the command-line equivalent follows this procedure.
See How to Start the SEAM Tool for more information.
Note - If you are creating a new principal that might need a new policy, you should create the new policy before you create the new principal. Go to How to Create a New Kerberos Policy.
$ /usr/sbin/gkadmin
The Principal Basics panel that contains some attributes for a principal is displayed.
Both the principal name and the password are mandatory.
Click on the box to the right of the encryption key types field to open a new window that displays all of the encryption key types available. Click OK after selecting the required encryption types.
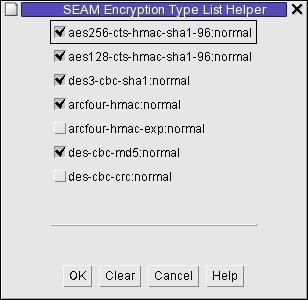
Three windows contain attribute information. Choose Context-Sensitive Help from the Help menu to get information about the various attributes in each window. Or, for all the principal attribute descriptions, go to SEAM Tool Panel Descriptions.
See How to Modify the Kerberos Administration Privileges for more details.
Example 23-4 Creating a New Kerberos Principal
The following example shows the Principal Basics panel when a new principal called pak is created. The policy is set to testuser.
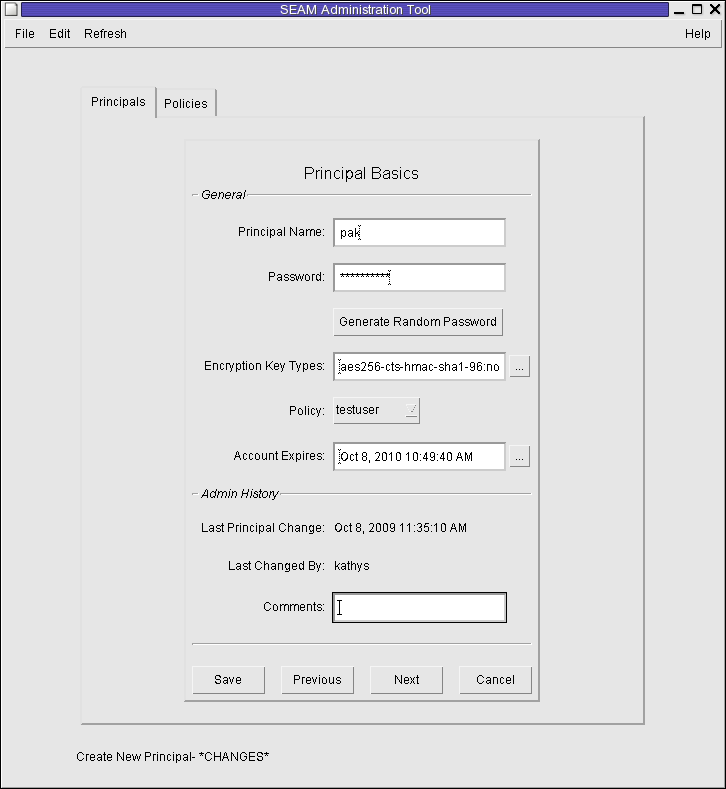
Example 23-5 Creating a New Kerberos Principal (Command Line)
In the following example, the add_principal command of kadmin is used to create a new principal called pak. The principal's policy is set to testuser.
kadmin: add_principal -policy testuser pak Enter password for principal "pak@EXAMPLE.COM": <Type the password> Re-enter password for principal "pak@EXAMPLE.COM": <Type the password again> Principal "pak@EXAMPLE.COM" created. kadmin: quit
This procedure explains how to use all or some of the attributes of an existing principal to create a new principal. No command-line equivalent exists for this procedure.
See How to Start the SEAM Tool for more information.
$ /usr/sbin/gkadmin
The Principal Basics panel is displayed. All the attributes of the selected principal are duplicated, except for the Principal Name and Password fields, which are empty.
Both the principal name and the password are mandatory. To make an exact duplicate of the principal you selected, click Save and skip to Step 7.
Three windows contain attribute information. Choose Context-Sensitive Help from the Help menu to get information about the various attributes in each window. Or, for all the principal attribute descriptions, go to SEAM Tool Panel Descriptions.
See How to Modify the Kerberos Administration Privileges for more details.
An example of the command-line equivalent follows this procedure.
See How to Start the SEAM Tool for more information.
$ /usr/sbin/gkadmin
The Principal Basics panel that contains some of the attributes for the principal is displayed.
Three windows contain attribute information. Choose Context-Sensitive Help from the Help menu to get information about the various attributes in each window. Or, for all the principal attribute descriptions, go to SEAM Tool Panel Descriptions.
Note - You cannot modify a principal's name. To rename a principal, you must duplicate the principal, specify a new name for it, save it, and then delete the old principal.
See How to Modify the Kerberos Administration Privileges for more details.
Example 23-6 Modifying a Kerberos Principal's Password (Command Line)
In the following example, the change_password command of kadmin is used to modify the password for the jdb principal. The change_password command does not let you change the password to a password that is in the principal's password history.
kadmin: change_password jdb Enter password for principal "jdb": <Type the new password> Re-enter password for principal "jdb": <Type the password again> Password for "jdb@EXAMPLE.COM" changed. kadmin: quit
To modify other attributes for a principal, you must use the modify_principal command of kadmin.
An example of the command-line equivalent follows this procedure.
See How to Start the SEAM Tool for more information.
$ /usr/sbin/gkadmin
After you confirm the deletion, the principal is deleted.
See How to Modify the Kerberos Administration Privileges for more details.
Example 23-7 Deleting a Kerberos Principal (Command Line)
In the following example, the delete_principal command of kadmin is used to delete the jdb principal.
kadmin: delete_principal pak Are you sure you want to delete the principal "pak@EXAMPLE.COM"? (yes/no): yes Principal "pak@EXAMPLE.COM" deleted. Make sure that you have removed this principal from all ACLs before reusing. kadmin: quit
No command-line equivalent exists for this procedure.
See How to Start the SEAM Tool for more information.
$ /usr/sbin/gkadmin
The Properties window is displayed.
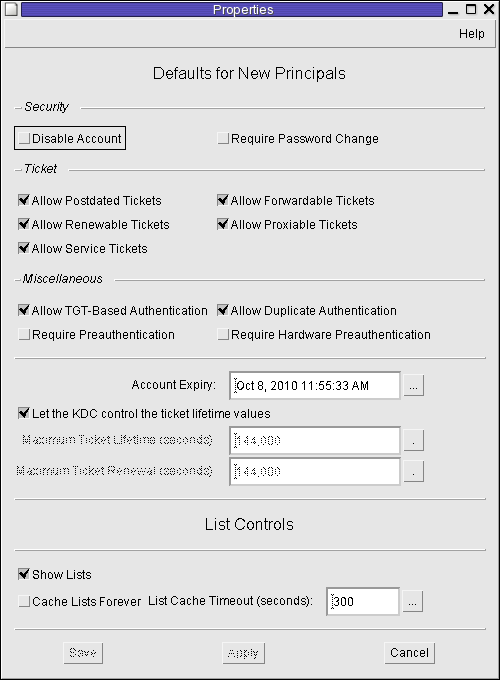
Choose Context-Sensitive Help from the Help menu for information about the various attributes in each window.
Even though your site probably has many user principals, you usually want only a few users to be able to administer the Kerberos database. Privileges to administer the Kerberos database are determined by the Kerberos access control list (ACL) file, kadm5.acl. The kadm5.acl file enables you to allow or disallow privileges for individual principals. Or, you can use the '*' wildcard in the principal name to specify privileges for groups of principals.
An entry in the kadm5.acl file must have the following format:
principal privileges [principal-target]
| ||||||||||||||||||||||||||||||
Example 23-8 Modifying the Kerberos Administration Privileges
The following entry in the kadm5.acl file gives any principal in the EXAMPLE.COM realm with the admin instance all the privileges on the Kerberos database:
*/admin@EXAMPLE.COM *
The following entry in the kadm5.acl file gives the jdb@EXAMPLE.COM principal the privileges to add, list, and inquire about any principal that has the root instance.
jdb@EXAMPLE.COM ali */root@EXAMPLE.COM