| Oracle® Fusion Middleware Troubleshooting Guide for Oracle Mobile Security Suite Release 3.0.1 Part Number E51929-03 |
|
|
PDF · Mobi · ePub |
| Oracle® Fusion Middleware Troubleshooting Guide for Oracle Mobile Security Suite Release 3.0.1 Part Number E51929-03 |
|
|
PDF · Mobi · ePub |
This chapter describes how to gather server logs for Windows installations for troubleshooting Oracle Mobile Security Suite.
This chapter contains the following sections:
To turn on debug level logging, you use the Oracle Mobile Security Suite Diagnostic Tool.
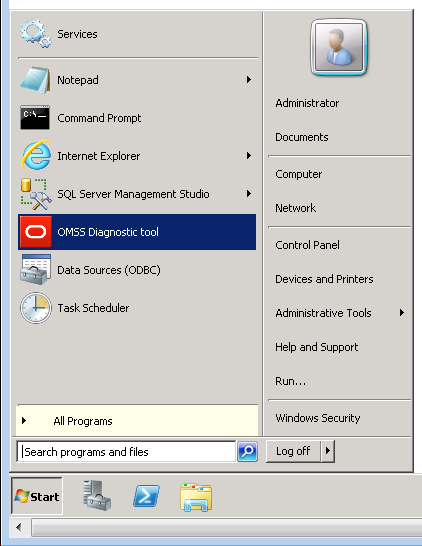
Click Troubleshoot.

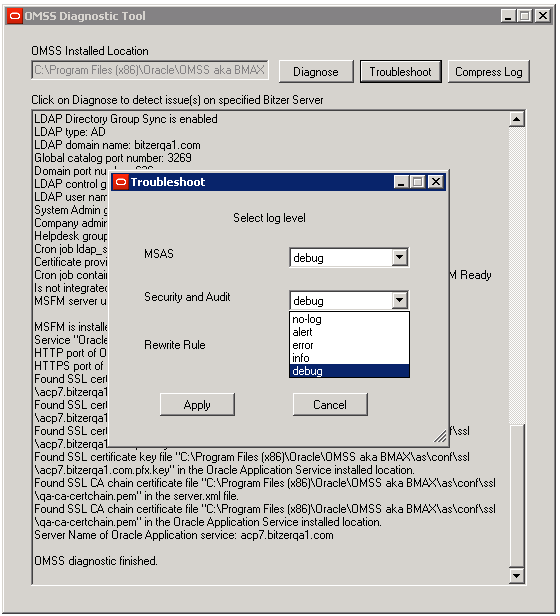
After reproducing the issue you have encountered, reduce the log level to its previous setting in a production environment, unless instructed otherwise by Oracle.
To collect logs, click Compress Log.

The following dialog is shown:
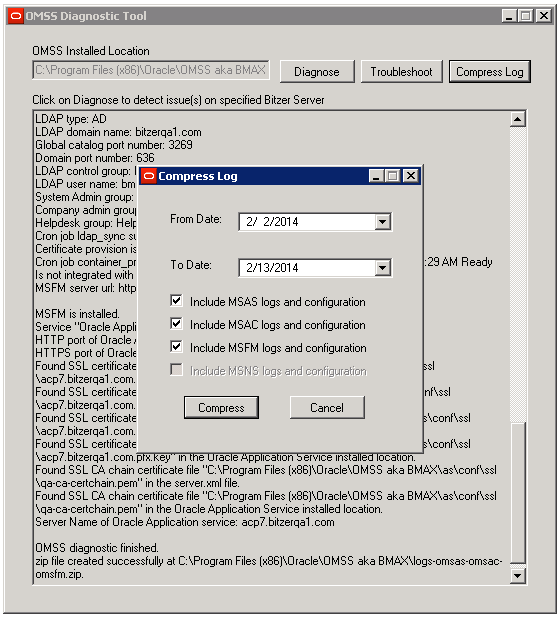
This dialog is used to easily collect information for each component, with the corresponding configuration. Depending on the size of the logs, this might take some time. After the collection is complete a zip file containing the logs and configuration files can be found in installation_directory\OMSS, for example: C:\Program Files (x86)\Oracle\OMSS.
By default, Mobile Security Access Server logs are found in:
install directory\OMSS\gateway\logs
For example:
C:\Program Files (x86)\Oracle\OMSS\gateway\logs
The following logs are created:
access.log
error.log
rewrite.log
Logs are rolled over once a day, and are time-stamped with the date.
access.log contains one line per request that is made to the Mobile Security Access Server.
The following table shows the format of access.log:
| Field | Format | Example | Direct Request | Proxy Request |
|---|---|---|---|---|
|
Remote IP Address |
IPv4 or IPv6 address |
|
Present |
Present |
|
Remote log name |
- |
|
- |
- |
|
User Identifier |
User principal name |
|
Present for authenticated requests |
Present for authenticated requests |
|
Time of Request |
[ |
|
Present |
Present |
|
Request line |
|
|
Present |
Present, path is always " |
|
Proxy Request Scheme |
http or https |
|
- |
Present |
|
Proxy Request URL |
URL encoding of hostname/path |
|
- |
Present |
|
HTTP Status Response |
HTTP Status Code |
|
Present |
Present |
|
Connection Status |
X means connection aborted + means connection kept alive - means connection closed |
|
Present |
Present |
|
Size of Response |
Size of Response in bytes |
|
Present |
Present |
|
Request Processing Time |
Time to process request in microseconds |
|
Present |
Present |
|
Request Thread ID |
Thread ID |
|
Present |
Present |
The following table shows the locations of Mobile Security Administrative Console logs:
| Log Type | Location of Log |
|---|---|
|
Installation |
|
|
Mobile Security Administrative Console |
|
|
User Interface (UI) |
|
|
Web service |
|
|
LDAP sync |
|
|
Scheduled task |
|
Logs are rolled over once a day, and are time-stamped with the date.
By default the logs do not contain much detail. Increase the log level to debug in Mobile Security Administrative Console for troubleshooting.
Client logs can be e-mailed using the "Send logs" function – this will package all necessary client logs.
The log level can be set to "verbose" in the Container app settings to gather detailed logs for troubleshooting.