Configuring YubiKey Challenge in the Oracle Advanced Authentication Self-Service Portal.
Introduction
This tutorial shows you how to use the Self-Service Portal to configure Yubikey with Oracle Advanced Authentication (OAA), for the purposes of multi-factor authentication.
Objectives
In this tutorial you will perform the following tasks:
- Configure your YubiKey in YubiKey Manager.
- Configure the YubiKey challenge factor in the Self-Service Portal.
Prerequisites
Before starting this tutorial ensure you have met these requirements:
- An Oracle Advanced Authentication deployment is available with Factor Verification enabled. See, Configuring Factor Verification.
- You have a YubiKey inserted in your device.
- You have access to the Self-Service Portal and can login with your user credentials.
Note: You can still follow this tutorial if factor verification is disabled, but you will not be able to verify if the factor is working before using it.
Task 1: Configure YubiKey Manager
In this section you configure your YubiKey in YubiKey Manager.
-
Download and install YubiKey Manager.
-
Start YubiKey Manager.
-
Insert the YubiKey into your device.
-
Select Applications then OTP.
-
In Long Touch Slot select Configure.
-
In Select Credential Type select Yubico OTP.
-
In the Yubico OTP screen:
- Select the Use serial check box.
- For Private ID select Generate.
- For Secret Key select Generate.
Note: It is important to make note of the values for
Public ID,Private ID, andSecret key. Once you click Finish you will not be able to retrieve these values again.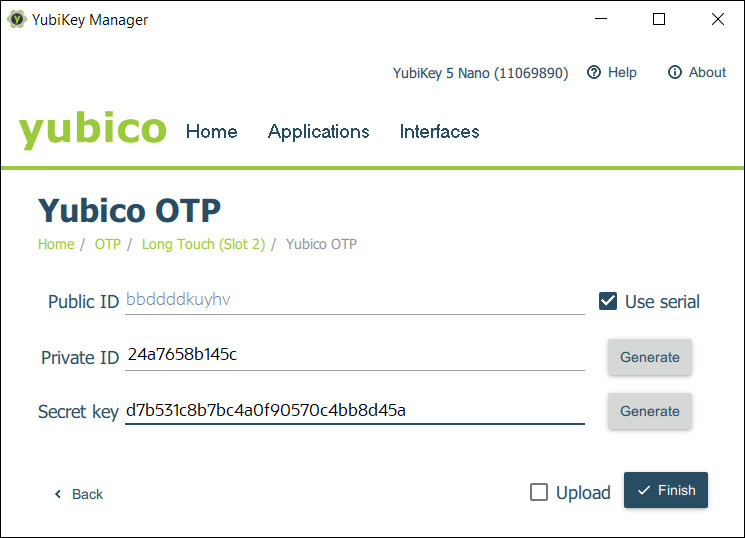
Task 2: Configure YubiKey in the Self-Service Portal
-
Access the Self-Service Portal. For example,
https://oaa.example.com/oaa/rui. -
Enter your user credentials. For example,
testuser/<password>. -
In the left navigation menu, select My Authenticators.
-
Select Add Authentication Factor and from the drop down menu select YubiKey OTP Challenge:

-
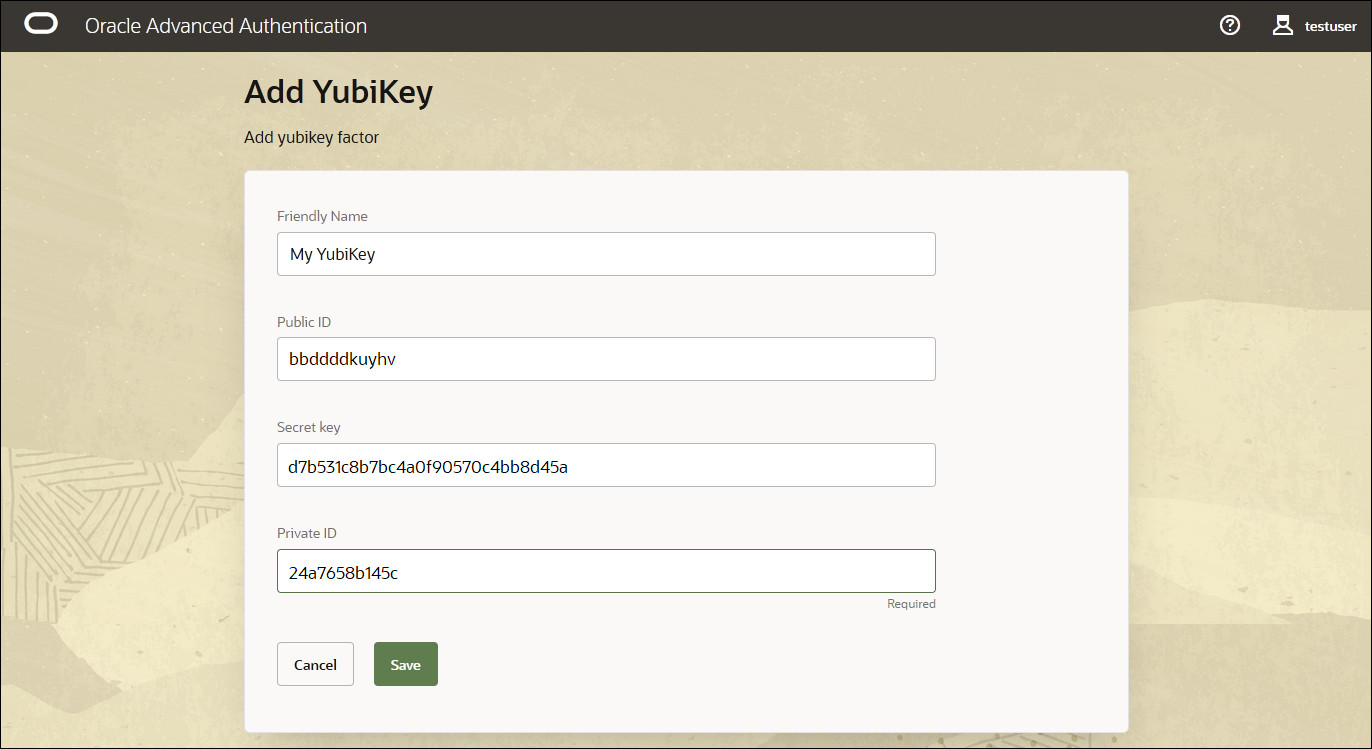
In the Add YubiKey screen enter the following:
Friendly Name:
My YubiKeyPublic ID:
<Public ID>Secret Key:
<Secret Key>Private ID:
<Private ID>Note: The values above should match the values generated in the Yubico OTP screen in Configure Yubikey Manager:
For example:
-
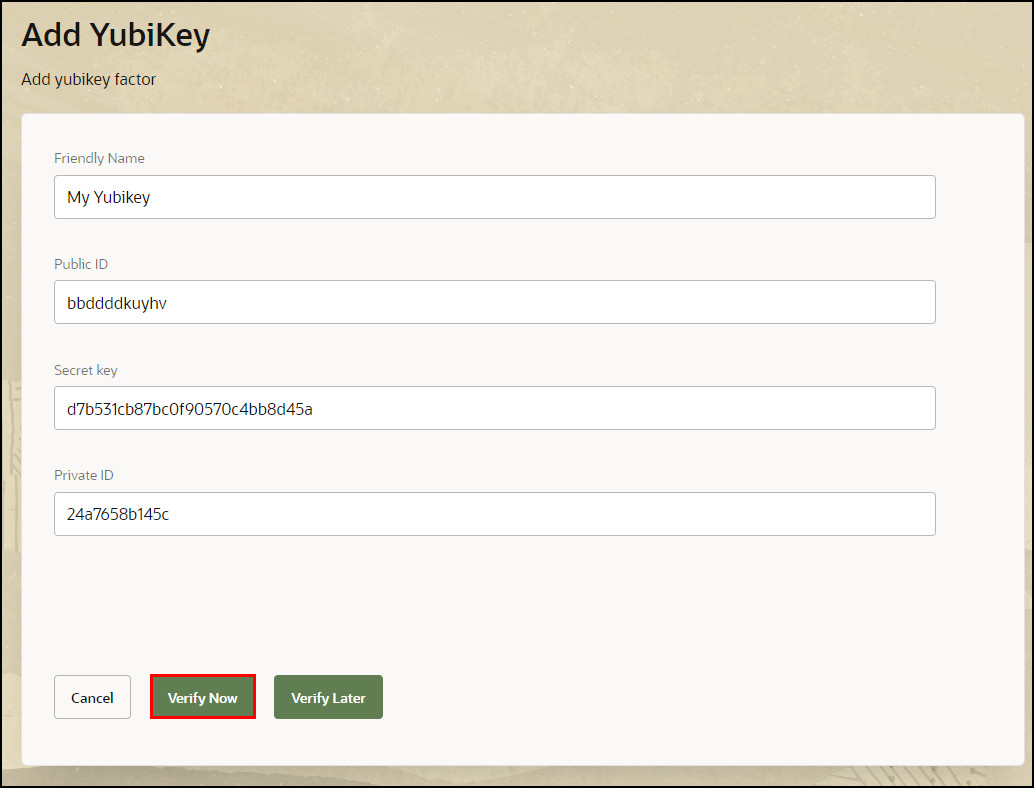
Click Verify Now:
Note: If factor verification is not enabled, Verify Now and Verify Later will not show. Instead, click Save.
-
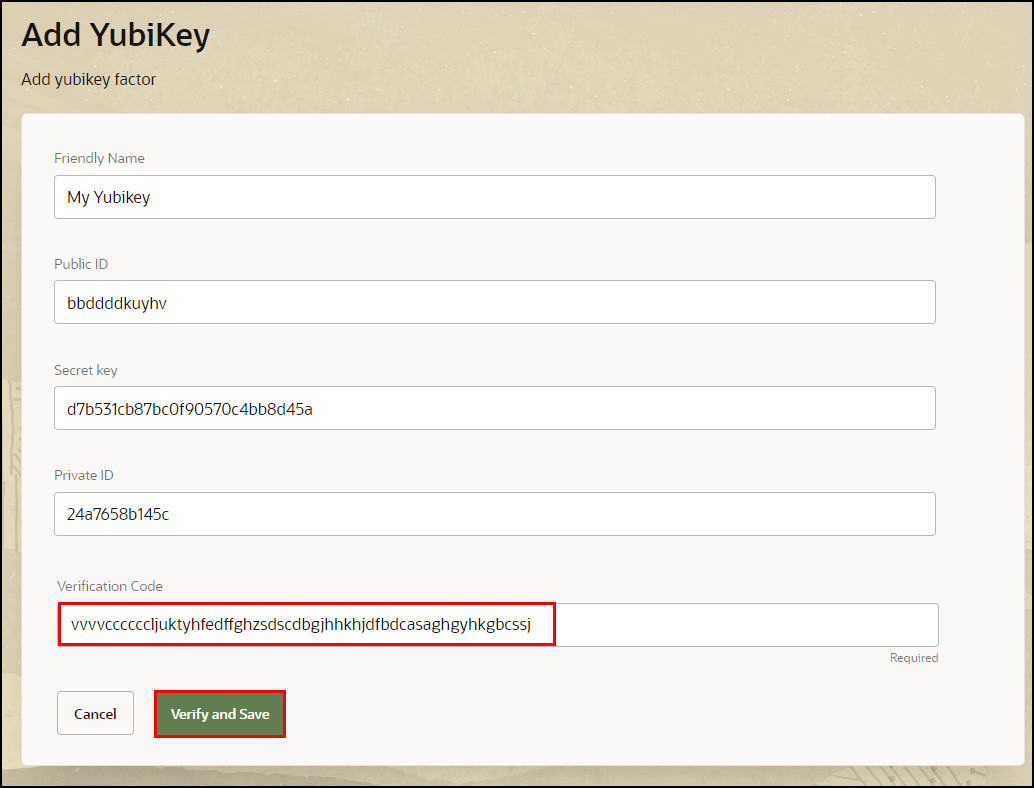
Click inside the Verification code field, and then touch (long touch) the YubiKey in your USB port. The verification code should populate. Click Verify and Save.
-
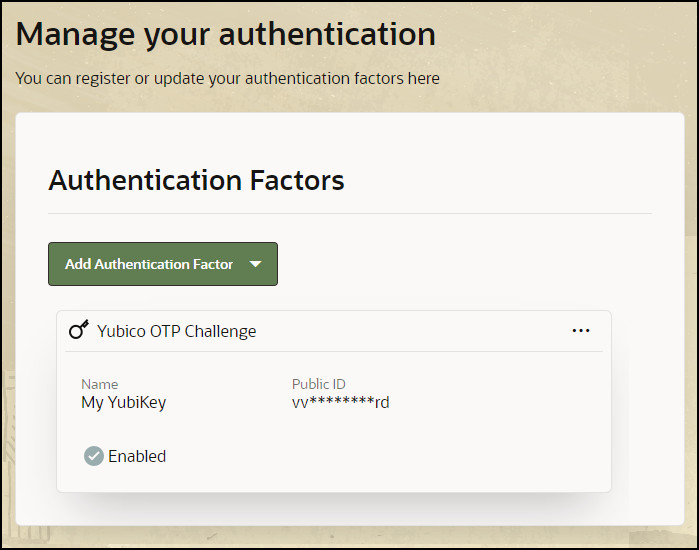
If the verification is successful, the Self-Service Portal will show the factor has been added:
Learn More
- To learn how to use factors with Windows device authentication and Oracle Universal Authenticator, see Configuring Device Authentication on Windows Using Oracle Access Management and Multi-Factor Authentication.
- To learn how to use factors when accessing an OAM protected application with MFA, see Integrate Oracle Access Management with Oracle Advanced Authentication.
Feedback
To provide feedback on this tutorial, please contact idm_user_assistance_ww_grp@oracle.com
Acknowledgements
- Author - Russ Hodgson
More Learning Resources
Explore other labs on docs.oracle.com/learn or access more free learning content on the Oracle Learning YouTube channel. Additionally, visit education.oracle.com/learning-explorer to become an Oracle Learning Explorer.
For product documentation, visit Oracle Help Center.
Configuring YubiKey Challenge in the Oracle Advanced Authentication Self-Service Portal
F55486-02
May 2024