| Oracle® Communications Security Edge Protection Proxy (SEPP) Cloud Native User's Guide Release 1.0 F16984-01 |
|
 Previous |
 Next |
| Oracle® Communications Security Edge Protection Proxy (SEPP) Cloud Native User's Guide Release 1.0 F16984-01 |
|
 Previous |
 Next |
This section explains the Security Edge Protection Proxy (SEPP) architecture.
The Security Edge Protection Proxy is a decentralized solution and composed of control plane (N32-C) and forwarding plane (N32-F). This solution is deployed between two NFs belonging to different PLMNs that use the N32 interface to communicate with each other.
Figure 2-1 Security Edge Protection Proxy Architecture
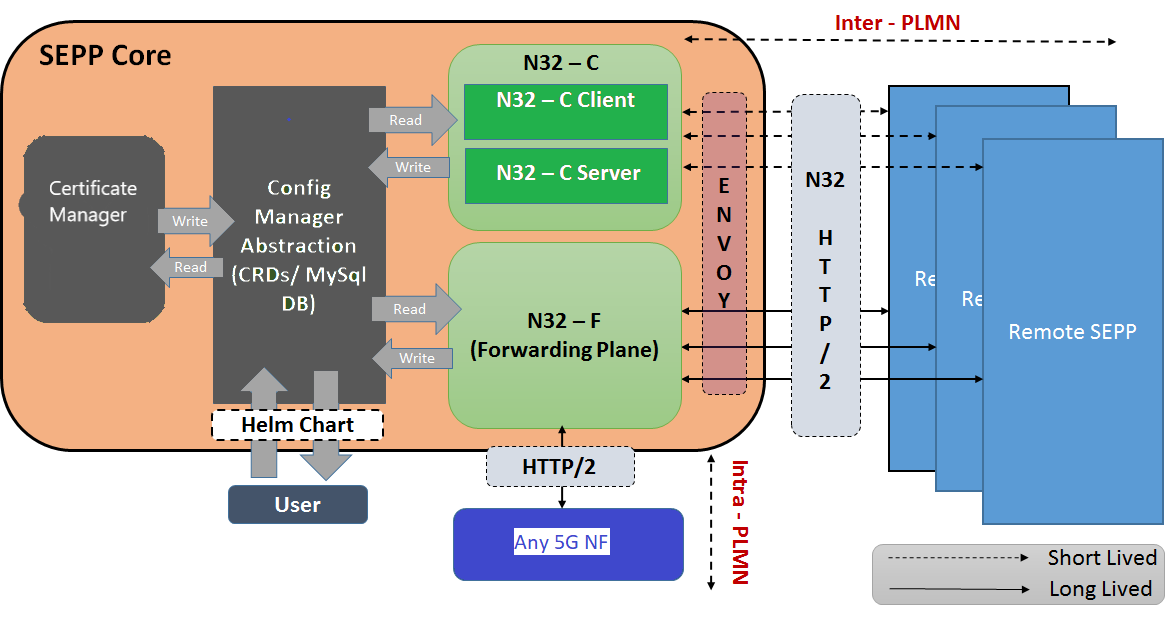
The above architecture diagram shows an overview of SEPP deployment and functionality:
For information on installing SEPP, see the OCSEPP Cloud Native Installation Guide.