The Oracle Private Cloud Appliance controller software allows you to add custom networks at the appliance level. This means that the necessary spine Cisco Nexus 9336C-FX2 Switch ports must be configured and cabled. For detailed information, refer to Appliance Uplink Configuration in the Oracle Private Cloud Appliance Installation Guide. Other hardware components also require configuration changes to enable the additional connectivity. These networks are then configured automatically in your Oracle VM environment, where they can be used for isolating and optimizing network traffic beyond the capabilities of the default network configuration. All custom networks, both internal and public, are VLAN-capable.
Custom networks must never be deleted in Oracle VM Manager. Doing so would leave the environment in an error state that is extremely difficult to repair. To avoid downtime and data loss, always perform custom network operations in the Oracle Private Cloud Appliance CLI.
The following network limitations apply:
The maximum number of custom external networks is 7 per tenant group or per compute node.
The maximum number of custom internal networks is 3 per tenant group or per compute node.
The maximum number of VLANs is 256 per tenant group or per compute node.
Only one host network can be assigned per tenant group or per compute node.
When configuring custom networks, make sure that no provisioning operations or virtual machine environment modifications take place. This might lock Oracle VM resources and cause your Oracle Private Cloud Appliance CLI commands to fail.
Creating custom networks requires use of the CLI. The administrator chooses between three types: a network internal to the appliance, a network with external connectivity, or a host network. Custom networks appear automatically in Oracle VM Manager. The internal and external networks take the virtual machine network role, while a host network may have the virtual machine and storage network roles.
The host network is a particular type of external network: its configuration contains additional parameters for subnet and routing. The servers connected to it also receive an IP address in that subnet, and consequently can connect to an external network device. The host network is particularly useful for direct access to storage devices.
For all networks with external connectivity the spine Cisco Nexus 9336C-FX2 Switch ports must be specified so that these are reconfigured to route the external traffic. These ports must be cabled to create the physical uplink to the next-level switches in the data center. For detailed information, refer to Appliance Uplink Configuration in the Oracle Private Cloud Appliance Installation Guide.
Creating a Custom Network
Using SSH and an account with superuser privileges, log into the active management node.
NoteThe default
rootpassword is Welcome1. For security reasons, you must set a new password at your earliest convenience.# ssh root@10.100.1.101 root@10.100.1.101's password: root@ovcamn05r1 ~]#
Launch the Oracle Private Cloud Appliance command line interface.
# pca-admin Welcome to PCA! Release: 2.4.1 PCA>
If your custom network requires public connectivity, you need to use one or more spine switch ports. Verify the number of ports available and carefully plan your network customizations accordingly. The following example shows how to retrieve that information from your system:
PCA> list network-port Port Switch Type State Networks ---- ------ ---- ----- -------- 1:1 ovcasw22r1 10G down None 1:2 ovcasw22r1 10G down None 1:3 ovcasw22r1 10G down None 1:4 ovcasw22r1 10G down None 2 ovcasw22r1 40G up None 3 ovcasw22r1 auto-speed down None 4 ovcasw22r1 auto-speed down None 5:1 ovcasw22r1 10G up default_external 5:2 ovcasw22r1 10G down default_external 5:3 ovcasw22r1 10G down None 5:4 ovcasw22r1 10G down None 1:1 ovcasw23r1 10G down None 1:2 ovcasw23r1 10G down None 1:3 ovcasw23r1 10G down None 1:4 ovcasw23r1 10G down None 2 ovcasw23r1 40G up None 3 ovcasw23r1 auto-speed down None 4 ovcasw23r1 auto-speed down None 5:1 ovcasw23r1 10G up default_external 5:2 ovcasw23r1 10G down default_external 5:3 ovcasw23r1 10G down None 5:4 ovcasw23r1 10G down None ----------------- 22 rows displayed Status: Success
For a custom network with external connectivity, configure an uplink port group with the uplink ports you wish to use for this traffic. Select the appropriate breakout mode
PCA> create uplink-port-group
MyUplinkPortGroup'1:1 1:2' 10g-4x Status: SuccessNoteThe port arguments are specified as
'x:y'wherexis the switch port number andyis the number of the breakout port, in case a splitter cable is attached to the switch port. The example above shows how to retrieve that information.You must set the breakout mode of the uplink port group. When a 4-way breakout cable is used, all four ports must be set to either 10Gbit or 25Gbit. When no breakout cable is used, the port speed for the uplink port group should be either 100Gbit or 40Gbit, depending on connectivity requirements. See Section 3.2.9, “create uplink-port-group” for command details.
Network ports can not be part of more than one network configuration.
Create a new network and select one of these types:
rack_internal_networkexternal_networkhost_network
Use the following syntax:
For an internal-only network, specify a network name.
PCA> create network
MyInternalNetworkrack_internal_network Status: SuccessFor an external network, specify a network name and the spine switch port group to be configured for external traffic.
PCA> create network
MyPublicNetworkexternal_networkMyUplinkPortGroupStatus: SuccessFor a host network, specify a network name, the spine switch ports to be configured for external traffic, the subnet, and optionally the routing configuration.
PCA> create network
MyHostNetworkhost_networkMyUplinkPortGroup\ 10.10.10 255.255.255.0 10.1.20.0/24 10.10.10.250 Status: SuccessNoteIn this example the additional network and routing arguments for the host network are specified as follows, separated by spaces:
10.10.10= subnet prefix255.255.255.0= netmask10.1.20.0/24= route destination (as subnet or IPv4 address)10.10.10.250= route gateway
The subnet prefix and netmask are used to assign IP addresses to servers joining the network. The optional route gateway and destination parameters are used to configure a static route in the server's routing table. The route destination is a single IP address by default, so you must specify a netmask if traffic could be intended for different IP addresses in a subnet.
Details of the create network command arguments are provided in Section 3.2.7, “create network” in the CLI reference chapter.
CautionNetwork and routing parameters of a host network cannot be modified. To change these settings, delete the custom network and re-create it with updated settings.
Connect the required servers to the new custom network. You must provide the network name and the names of the servers to connect.
PCA> add network
MyPublicNetworkovcacn07r1Status: Success PCA> add networkMyPublicNetworkovcacn08r1Status: Success PCA> add networkMyPublicNetworkovcacn09r1Status: SuccessVerify the configuration of the new custom network.
PCA> show network
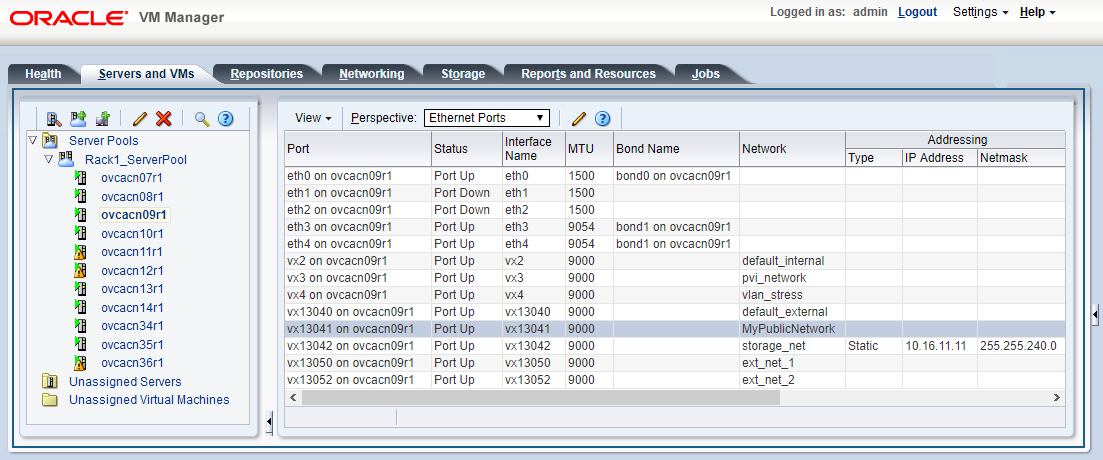
MyPublicNetwork---------------------------------------- Network_Name MyPublicNetwork Trunkmode None Description None Ports ['1:1', '1:2'] vNICs None Status ready Network_Type external_network Compute_Nodes ovcacn07r1, ovcacn08r1, ovcacn09r1 Prefix None Netmask None Route Destination None Route Gateway None ---------------------------------------- Status: SuccessAs a result of these commands, a VxLAN interface is configured on each of the servers to connect them to the new custom network. These configuration changes are reflected in the Networking tab and the Servers and VMs tab in Oracle VM Manager.
NoteIf the custom network is a host network, the server is assigned an IP address based on the prefix and netmask parameters of the network configuration, and the final octet of the server's internal management IP address.
For example, if the compute node with internal IP address 192.168.4.9 were connected to the host network used for illustration purposes in this procedure, it would receive the address 10.10.10.9 in the host network.
Figure 2.4 shows a custom network named MyPublicNetwork, which is VLAN-capable and uses the compute node's
vx13041interface.To disconnect servers from the custom network use the remove network command.
WarningBefore removing the network connection of a server, make sure that no virtual machines are relying on this network.
When a server is no longer connected to a custom network, make sure that its port configuration is cleaned up in Oracle VM.
PCA> remove network
MyPublicNetworkovcacn09r1************************************************************ WARNING !!! THIS IS A DESTRUCTIVE OPERATION. ************************************************************ Are you sure [y/N]:y Status: Success
Deleting a Custom Network
Before deleting a custom network, make sure that all servers have been disconnected from it first.
Using SSH and an account with superuser privileges, log into the active management node.
NoteThe default
rootpassword is Welcome1. For security reasons, you must set a new password at your earliest convenience.# ssh root@10.100.1.101 root@10.100.1.101's password: root@ovcamn05r1 ~]#
Launch the Oracle Private Cloud Appliance command line interface.
# pca-admin Welcome to PCA! Release: 2.4.1 PCA>
Verify that all servers have been disconnected from the custom network. No vNICs or nodes should appear in the network configuration.
CautionRelated configuration changes in Oracle VM must be cleaned up as well.
PCA> show network MyPublicNetwork ---------------------------------------- Network_Name MyPublicNetwork Trunkmode None Description None Ports ['1:1', '1:2'] vNICs None Status ready Network_Type external_network Compute_Nodes None Prefix None Netmask None Route_Destination None Route_Gateway None ----------------------------------------
Delete the custom network.
PCA> delete network
MyPublicNetwork************************************************************ WARNING !!! THIS IS A DESTRUCTIVE OPERATION. ************************************************************ Are you sure [y/N]:y Status: SuccessCautionIf a custom network is left in an invalid or error state, and the delete command fails, you may use the
--forceoption and retry.