Creating an Operating System Report
Use Operating System update reports to check for new software updates and security advisories. For auditing purposes, create a change history report. Various types of update reports are available for Linux, Oracle Solaris, and Windows operating systems. You can export report results to CSV or PDF format.
Use operating system reports to obtain information about managed Oracle Solaris, Linux, and Windows operating systems.
Table 4-3 illustrates the various reports that are run in Oracle Enterprise Manager Ops Center and displays the type of report that are supported and run on an operating system.
Table 4-3 Compatibility of Reports on Operating System
| Report Name | Linux OS | Oracle Solaris 8, 9, and 10 | Oracle Solaris 11 | Microsoft Windows |
|---|---|---|---|---|
|
Change History Report |
Yes |
Yes |
Yes |
No |
|
CVE Compliance Report |
Yes |
Yes |
No |
No |
|
RSC Report |
Yes |
Yes |
No |
No |
|
System Catalog Report |
Yes |
Yes |
Yes |
No |
|
Oracle Solaris Update Compliance Report |
No |
Yes |
No |
No |
|
Baseline Analysis Report |
No |
Yes |
No |
No |
|
Update Compliance Report |
Yes |
Yes |
No |
No |
|
Incident Compliance Report |
Yes |
Yes |
No |
Yes |
|
Host Compliance Report |
Yes |
Yes |
No |
Yes |
|
Distribution Update Report |
Yes |
Yes |
No |
No |
|
Service Pack Compliance Report |
Yes |
No |
No |
No |
|
Package Compliance Report |
No |
Yes |
No |
No |
Updating Compliance Reports
Host Compliance and Incidence Compliance reports are available for Linux, Oracle Solaris, and Windows operating systems.
The following reports are available for Linux, Oracle Solaris, and Windows operating systems:
-
Host Compliance: Provides information on whether your system is compliant with security and bug fixes incidents.
-
Incidence Compliance: Provides information about the number of systems to which the selected operating system updates apply.
Oracle Linux and Oracle Solaris OS Update Reports
In addition to the reports created for all types of operating systems, reports are available for Oracle Linux and Oracle Solaris operating systems also.
-
Change History: Provides a history of Operating System update, install, and uninstall jobs completed on managed systems.
-
CVE Compliance: Provides information on incidents that are related to specific Common Vulnerability and Exposure Identifiers (CVE IDs) and the systems that have these incidents installed. CVE IDs are unique, common identifiers for publicly known security vulnerabilities.
-
Distribution Update: Provides a mapping between selected updates, CVEs, and selected distributions to find out whether the updates are installed.
-
Package Compliance: Provides the details of the selected packages on managed system that are compliant or not compliant with the latest recommended version available.
-
Recommended Software Configuration (RSC): Provides information about the system compliance for installing a specific application, such as the Oracle 11g Database, on an Oracle Solaris, or Linux Operating System.
-
Service Pack Compliance (Linux only): Provides information on incidents created by the publication and release of a service pack by a vendor. This helps in determining whether the system has the latest service packs released by the vendor.
-
Oracle Solaris Update Compliance (Oracle Solaris Operating System only): Provides information on whether an Oracle Solaris system is compliant with a specific update.
-
Baseline Analysis (Oracle Solaris Operating System only): This helps to check the compliance of systems against newly released Oracle Solaris baselines.
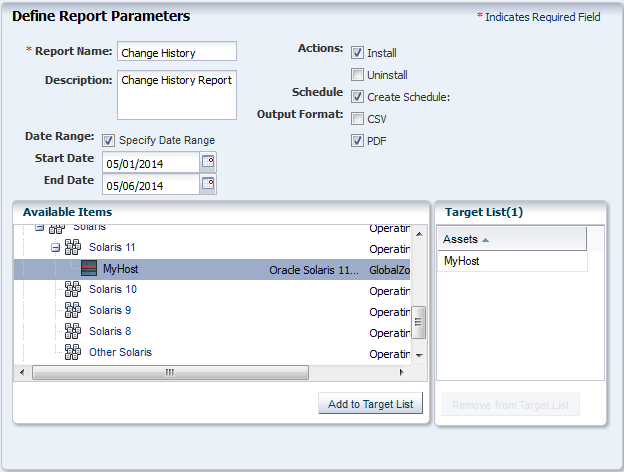
Creating a Change History Report
The Change History Report provides a history of operating system update install and uninstall jobs completed on managed Oracle Solaris or Linux systems. The report also displays the deployments made by the specific user, enabling you to track a team of operators.
Perform the following steps to create a change history report:
See Viewing a Report Result for more information about viewing a report result.
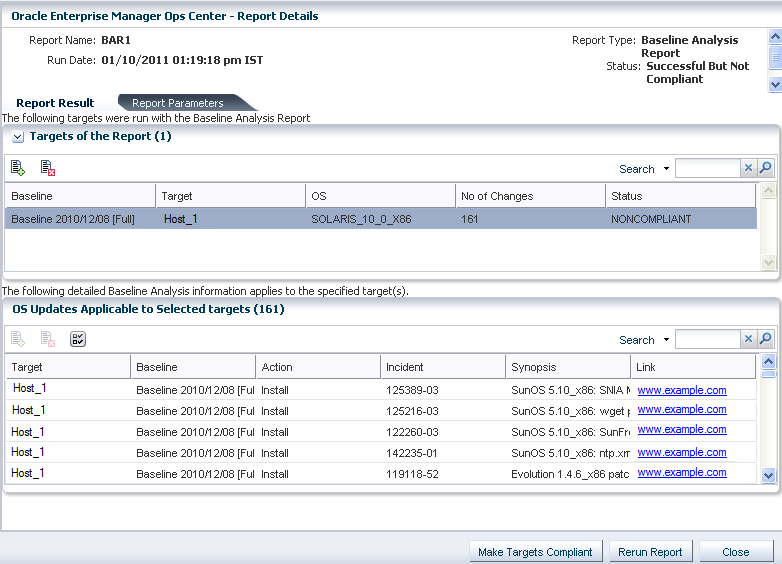
Creating a Baseline Analysis Report
An Oracle Solaris baseline is a dated collection of Oracle Solaris updates, update metadata, and tools. Oracle releases Oracle Solaris baselines on a monthly basis. A Baseline Analysis Report checks the compliance of Oracle Solaris systems against newly released Oracle Solaris baseline.
When you install the updates of a baseline on a host, that system is considered to be compliant with that baseline.
Each dated baseline contains these update sets:
-
Full: Includes all Oracle Solaris updates
-
Recommended: Includes Oracle Solaris recommended updates and security updates
-
Security: Includes only Oracle Solaris security updates
All baselines include updates for a specific time frame. However, the Full baseline often contains Oracle Solaris operating system updates that are not included in the Recommended baseline. The Full baseline includes additional updates based on feedback from various customer support groups within Oracle. Recommended baseline does not includes these updates.
To install the Recommended and Security baselines, you must either deploy two jobs or have a job that includes multiple tasks. This might result in multiple reboots, for example, if both tasks (baselines) include updates that have Single User mode requirements.
Oracle Enterprise Manager Ops Center's Knowledge Base (KB) is updated with the information about the baselines. This is done a few days after the official release of baselines by Oracle.
Note:
The Oracle Solaris 8 Operating System was placed into End of Service Live (EOSL) on March 31, 2009. Oracle Solaris 8 Operating System baselines are available through March 2009. The KB might contain artificial baselines after that date. Do not use baselines dated after March 2009.
Oracle Solaris baselines enables you to easily identify the update level of your hosts. For example, install some test hosts with a particular baseline. Test these hosts for a period to see whether the updates in this baseline are stable enough to be used on production hosts. When the testing reveals that this baseline is stable, install the same baseline on production hosts.
Oracle Solaris baselines are available as a component in the recommended component list. This contains a list of dated baselines.
The Baseline Analysis report helps to verify the compliance of your system against the newly-released baselines (as and when they are available in Knowledge Base).
The Baseline Analysis Report (BAR) enables you to determine whether the managed system is compliant with recently released Oracle Solaris baselines. Baselines pertain only to Oracle Solaris systems. This section describes Oracle Solaris baselines, white list, black list, and how to run a Baseline Analysis report in connected and disconnected mode of the Enterprise Controller.
The Baseline Analysis Report (BAR) describes how to generate a BAR. The report gives the compliance status of the managed system with the selected Oracle Solaris baseline that was released.
You can generate two types of BARs:
-
Agent-based BAR
-
Database-based BAR
In an agent-based BAR, a simulated job is run against the managed hosts. This type of report takes time to complete because it checks for dependent components and missing dependencies, and then downloads the updates that must be installed. When you run a compliance job from this report result, the job is completed quickly because the updates are downloaded. However, to improve the report performance of a BAR, skip the downloads in a simulated job by deselecting this option.
In a database-based BAR, the report is run against the database of the management server, the selected baselines are broken down into individual update IDs, and then formed into an incidents list. The report is generated based on the information that are available on the database. Based on the report result, run a compliance job.
White List
A white list is the list of updates that is required to install in addition to the updates in the baseline.
To establish a white list, create a profile using the Required setting. You can also specify a white list when generating a Baseline Analysis Report. Select the white list either from the created profile or enter the update IDs separated by new lines.
For example, baseline B includes updates X, Y, and Z, and the white list has updates U, V, and W. When the Baseline Analysis report is created, the host is marked compliant only when all six updates X, Y, Z, U, V, and W are present.
Black List
A black list is a list of updates that you do not want to install. Create a black list by creating a policy with the specified action for the updates.
Select a black list option while creating a Baseline Analysis Report. Select the black list either from the created policy or enter the update IDs separated by new lines.
If a particular update in the profile is set with the policy component setting as Never for an install action, then the update is not installed. If the update is installed, it will not be uninstalled or removed.
For example, if baseline A has updates X, Y, and Z, and the black list specifies only Y and Z, the system is compliant if X is installed. If the updates Y and Z are installed, they will not get uninstalled if you run a compliance job from the report results. If Y and Z are not installed, they are not listed in the non compliant result and are not added in the compliance job.
Creating a Baseline Analysis Report
This report provides information about the hosts that are compliant with a baseline operating system.
See Viewing a Report Result for more information about viewing a report result and generating a compliance job from the result.
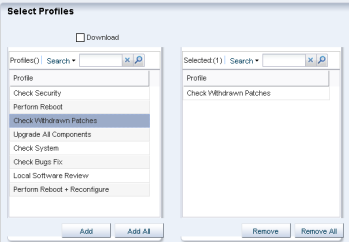
Profile Analysis Report
A Profile Analysis Report provides information about Oracle Solaris or Linux systems' compliance with the Operating System Update Profiles that you define in Oracle Enterprise Manager Ops Center.
The update profiles include both the system-defined and user-defined profiles in Oracle Enterprise Manager Ops Center.
Note:
Avoid running reports for system-defined profiles like Perform Reboot+Reconfigure and Perform Reboot as these profiles do not contain any updates.
You can modify the update list that is applied to generate the report by selecting a white list and a black list.
A white list is the list of updates to install. To establish a white list, create a profile using the required setting. Select the white list either from the created profile or enter the update IDs separated by new lines.
For example, baseline B includes updates X, Y, and Z, and the white list has updates U, V, and W. When the Baseline Analysis Report is created, the host is marked compliant only when all six updates (X, Y, Z, U, V, and W) are present.
A black list is a list of updates that you do not want them to be installed. You create a black list by creating a policy with the specified action for the updates. Select the black list either from the created policy or enter the update IDs separated by new lines.
When a particular update in the profile is set with the policy component setting as Never for the install action, then the update is not installed. When the update is installed, it is not uninstalled or removed.
For example, when baseline A has updates X, Y, and Z, and the black list specifies only Y and Z, the system is compliant when X is installed. Even if the updates Y and Z are installed, they are not uninstalled when you run a compliance job from the report results.
Creating Profile Analysis Report
Procedure to create a Profile Analysis Report.
See Viewing a Report Result for more information about viewing a report result and generating a compliance job from the result.
Recommended Software Configuration Report
A Recommended Software Configuration provides information about the system compliance for installing a specific application, such as the Oracle 11g Database, on an Oracle Solaris or Linux operating system.
The Knowledge Base provides a list of application configuration requirements with which you can check your system compliance status.
For example, you can check the system compliance status of Oracle Solaris operating system for installing Oracle 11g Database. The report provides information about the updates that must be installed, uninstalled, or upgraded for installing the Oracle database.
For an Oracle Solaris operating system, you cannot upgrade a update component from the existing lower version to the recommended higher version. Such instances will be marked as Error in the RSC report result. In such scenarios, you cannot make the target system fully compliant with the recommended software components by the report.
You can generate different types of RSCs:
-
Agent-based RSC
-
Database-based RSC
In an agent-based RSC, the report is generated based on the information from the target system. The dependencies for the updates are checked and downloaded when required. This report takes time to generate because it checks dependencies and downloads updates that must be installed.
In a database-based RSC, the report is generated based on the target system information that is available on the database of the Enterprise Controller. The dependencies are not checked and required updates are not downloaded. This type of report is generated quickly.
Creating Recommended Software Configuration Report
Procedure to create a Recommended Software Configuration report.
See Viewing a Report Result for more information about viewing a report result and generating a compliance job from the result.
Creating an Oracle Solaris Update Compliance Report
The Oracle Solaris Update Compliance report determines whether a specific Oracle Solaris system is compliant with a particular released Update.
To create an Oracle Solaris Update Compliance Report, perform the following steps:
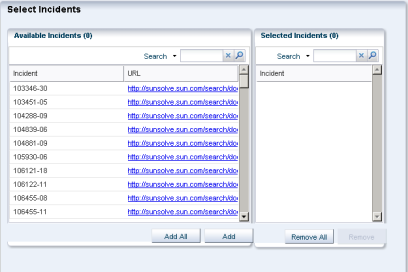
Creating an Incident Compliance Report
You can run an incident compliance report to determine whether the incidents on the managed hosts are compliant with the latest released version.
Incidents are the updates that are available for an application or feature. Incidents apply to one or more packages or RPMs.
Creating an Incident Compliance Report for Oracle Solaris or Linux
Procedure to create an Incident Compliance Report for Oracle Solaris or Linux.
You can run an incident compliance report to determine whether the incidents on the managed hosts are compliant with the latest released version.
See Viewing a Report Result for more information about viewing a report result and generating a compliance job from the result.
Creating an Incident Compliance Report for Microsoft Windows
You can run an incident compliance report to determine whether the incidents on the managed hosts are compliant with the latest released version.
The Incident Compliance Report provides information about whether your systems are compliant with the Windows updates incidents. This report displays the number of systems to which the selected Windows updates apply, how many systems have the updates installed, and how many systems require the updates to be installed to make the systems compliant. You can create a Windows update job based on the results of an Incident Compliance Report.
To create an Incident Compliance Report for Microsoft Windows, perform the following steps:
Creating a Host Compliance Report
You can run a host compliance report to determine whether the hosts are compliant with security and bug fix incidents. This report displays the number of updates that are applicable to each system, and whether the updates are installed or must be installed to make the system compliant.
You can also create an update job based on the results of a Host Compliance Report.
Creating Host Compliance Report for Oracle Solaris or Linux
The Host Compliance Report provides information if your systems are compliant with update incidents.
To Create a Host Compliance Report for Oracle Solaris or Linux, perform the following steps:
See Viewing a Report Result for more information about viewing a report result and generating a compliance job from the result.
Creating Host Compliance Report for Microsoft Windows
The Host Compliance Report for Windows provides information if your systems are compliant with the Windows updates incidents. This report displays the number of Windows updates that are applicable to each system, and whether the updates are installed or must be installed to make the system compliant. You can also create a Windows update job based on the results of a Host Compliance Report.
To create a Host Compliance Report for Microsoft Windows, perform the following steps:
System Catalog Report
A System Catalog Report lists the current catalog of one or more systems. A system catalog contains a list of operating system software components that are installed on a managed system. Catalogs provide the capability to directly manipulate the installed software components on a single operating system or a group of operating systems.
After an operating system is available and selected, you can view and modify the catalogs, and create historical catalogs. Historical catalogs are snapshots of the system. The software automatically takes a snapshot of the operating system after running a job on the operating system, including when you discover and manage the operating system. A snapshot is stored as a catalog with the time stamp and job details after every update job that you run on a system.
You can create a new catalog at any time and use it to record the state of a system. Catalogs enables us to rollback our system to any previous configuration or to create a profile that is used to apply a consistent configuration throughout our datacenter.
Creating a System Catalog Report
Procedure to create a System Catalog Report.
See Viewing a Report Result for more information about viewing a report result and generating a compliance job from the result.