PeopleSoft
PeopleSoft is an Oracle enterprise application suite that supports human capital management, financials, supply chain, and campus solutions. If you want to deploy PeopleSoft in Google Cloud or migrate PeopleSoft from your data center to Google Cloud, you can plan for secure, low latency topology leveraging Oracle AI Database@Google Cloud.
Learn about reference architecture to run Oracle PeopleSoft in Google Cloud leveraging Oracle AI Database@Google Cloud for Database layer and Google Compute Engineer (GCE) for web and app layers. This configuration provides low latency configuration as the Oracle AI Database Services are deployed in same Google Cloud Data center.
Currently, Oracle Exadata Database Service on Dedicated Infrastructure, Oracle Autonomous AI Database Service, and Oracle Exadata Database Service on Exascale Infrastructure are supported with Oracle AI Database@Google Cloud. You can check regional availability matrix to determine supported services by OCI and Google Cloud regions.
This document is intended for cloud architects, infrastructure administrators, and PeopleSoft system administrators responsible for designing, deploying, and operating PeopleSoft environments. Familiarity with PeopleSoft architecture and components, Oracle AI Database, and cloud platforms including Oracle Cloud Infrastructure (OCI) and Google Cloud Platform (GCP) is recommended.
Architecture
This architecture demonstrates the deployment of Oracle PeopleSoft applications in single availability zone of GCP region. For deployment of Disaster Recovery, similar configuration can be deployed across multiple GCP regions. To configure the databases to use Oracle Active Data Guard and Application stack, you can use rsync to synchronize the file systems across regions. For more information on designing and implementing disaster recovery architectures, see Oracle Maximum Availability Architecture for Oracle AI Database@Google Cloud.
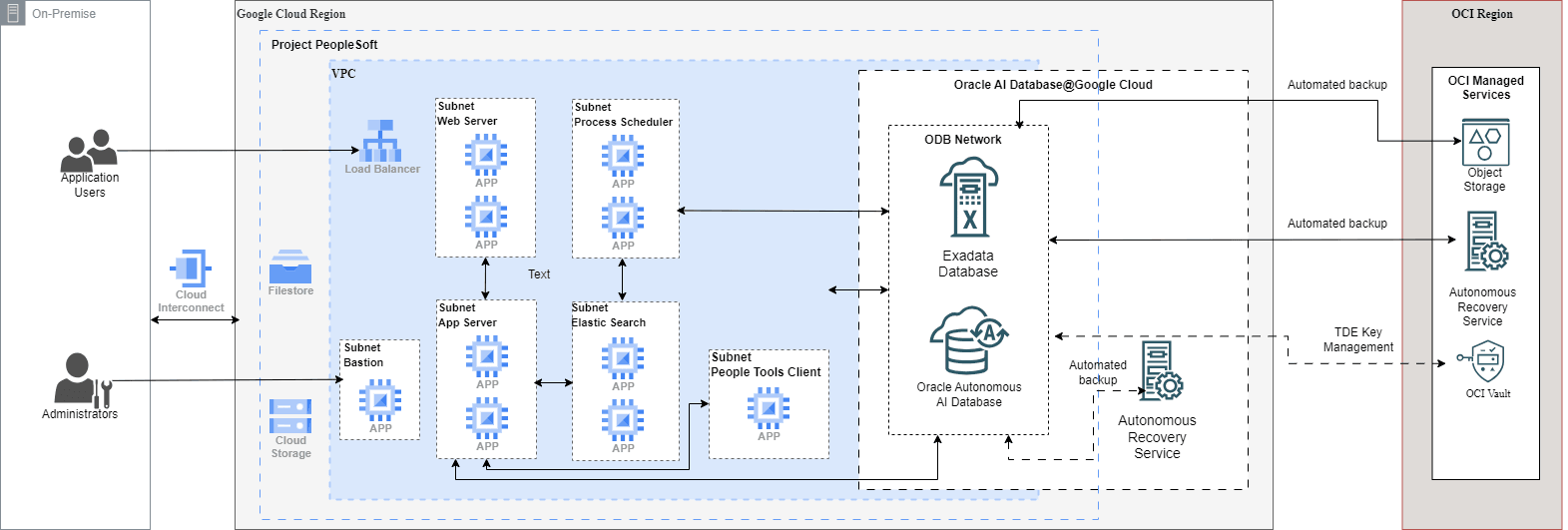
This architecture deploys all components within a single GCP region and highlights important design considerations for PeopleSoft on GCP with Oracle AI Database@Google Cloud.
Networking Tier
This architecture shows the deployment of PeopleSoft application in a single availability zone of GCP ensuring low latency. The architecture consists of one Google Cloud VPC with bastion host, load balancer, web server, application server, process scheduler and elastic server in separate subnets and ODB Network with Oracle AI Database. Connectivity to on-premises environments can be established using Cloud Interconnect (Dedicated/Partner) with Cloud Router for private, low-latency access (or Cloud VPN as an alternative). Compute Engine VM instances for web server, application server, process scheduler and elastic server can be placed in multiple instance groups.
The bastion host is deployed in a subnet with an external IP address (public), while all other PeopleSoft and database components reside in subnets without external IP addresses. External IP addresses can be attached to specific instances based on business or operational requirements. Secure access to private instances is provided over port22 (SSH) through the bastion host or via Cloud Interconnect/VPN when direct connectivity to on-premises data centers is configured.
PeopleSoft application components are deployed across a single GCP zone to ensure low latency connectivity. The database is deployed in a single zone with Oracle RAC enabled by default. For regional redundancy, the database can be deployed in a second zone or region using Oracle Data Guard, providing high availability and disaster recovery at the regional level.
Networking Design Considerations
- When planning IP address space, account for Oracle AI Database@Google Cloud subnet requirements and address space consumption scenarios.
- Plan DNS configuration carefully, especially when using custom DNS resolvers, to support Oracle AI Database@Google Cloud DNS resolution requirements.
- For multi-region disaster recovery architectures, consider detailed network connectivity patterns and inter-region routing for Oracle AI Database@Google Cloud.
- Review backup and recovery prerequisites early in the design phase to ensure network access requirements are met.
- Use Network Security Groups (NSGs) to restrict access to database virtual machines:
- Allow SSH (port 22) access only through GCP Bastion VM.
- Allow database traffic (port 1521) exclusively from approved PeopleSoft application subnets and authorized on-premises networks.
Bastion Host
A GCP bastion host provides a secure and controlled administrative access point to the Google Cloud VPC hosting Oracle PeopleSoft workloads.
The bastion host is deployed in a dedicated public management subnet and acts as a jump point to reach virtual machines in private subnets that do not have external (public) IP addresses, ensuring they are not directly exposed to the public internet. By using a bastion host, the architecture maintains a single, known access point that can be centrally monitored and audited, while avoiding the need to expose public IP addresses or open inbound ports on individual virtual machines.
In this architecture, target virtual machines do not require external IP addresses. Administrative access is established using SSH (port 22) from an administrator workstation to the bastion host, and then onward from the bastion to private instances over internal IPs. Firewall rules can be scoped tightly so that inbound SSH is allowed only to the bastion host (for example, from corporate public IP ranges), and private subnets allow SSH/RDP only from the bastion subnet or bastion service account, reducing the attack surface.
As an alternative to a traditional bastion with a public IP, GCP also supports Identity-Aware Proxy (IAP) TCP forwarding, which enables administrative access to private instances without opening inbound SSH/RDP from the internet. With IAP, access is authenticated and authorized using Cloud IAM, and sessions can be logged via Cloud Audit Logs. This approach further reduces exposure by keeping instances private and minimizing the need for inbound firewall rules.
The bastion host enables administrators to connect to private PeopleSoft components using SSH for Linux and RDP for Windows (where applicable). Connections are initiated from the administrator’s workstation and routed through the bastion (or through IAP), ensuring administrative sessions are controlled, auditable, and not directly exposed to the public network.
By centralizing administrative access and eliminating direct VM exposure, a GCP bastion pattern (or IAP-based access) enhances security while maintaining operational access to private workloads.
PeopleSoft Application Tier
All instances in the application tier are configured and connected to database instances that are in the active state. The application tier contains the following PeopleSoft Internet Architecture components:
- PeopleSoft web servers: The PeopleSoft web servers receive application requests from the web environment, the internet, and the intranet through the load balancer. Incoming traffic is distributed by the load balancer over port 8000 (example). It forwards the requests to the Oracle Tuxedo Jolt port on the application server. In the architecture diagram, multiple web servers are deployed to support high availability.
- ElasticSearch servers: The Oracle PeopleSoft search framework provides a standard method to use search indexes for all PeopleSoft applications. The search framework depends on ElasticSearch servers and interacts with the PeopleSoft web servers over port 9200 (example).
- PeopleSoft application servers: PeopleSoft application servers handle the bulk of the workload in the PeopleSoft system. It runs the business logic and processes all application requests from the web server over Oracle Tuxedo Jolt ports over port 9000 (example). The application server also maintains the SQL connection to the database over port 1521. Application requests are received at the web server, forwarded to the application servers, and then submitted to the database servers.
- PeopleSoft Process Scheduler: An instance of the PeopleSoft Process Scheduler is required in order to run batch processes or jobs, such as NVision.
- PeopleTools client: PeopleTools clients are Windows-based and are also referred to as the PeopleTools Development Environment. These clients run on supported Microsoft Windows platforms and can connect to the PeopleSoft database using client connectivity software (two-tier connection) over port 1521 or through a PeopleSoft application server (three-tier connection) over port 7000. The PeopleTools client is an integrated part of the PeopleSoft Internet Architecture, as it helps administrators perform management and migration tasks.
Set up Google Cloud file storage to stage PeopleSoft software. A single shared file system can be created to distribute and share software binaries across PeopleSoft application servers, web servers, and Elasticsearch servers. Filestore is typically used for this purpose (NFS), and a higher-performance Filestore tier (for example, Enterprise/High Scale, as appropriate) is recommended over lower tiers to provide higher throughput and lower latency.
Database Tier
For high availability requirements, we recommend using one of the following Oracle AI Database@Google Cloud options to set up PeopleSoft database instances:
- Oracle Autonomous AI Database Serverless
- Oracle Exadata Database Service on Dedicated Infrastructure
- Oracle Exadata Database Service on Exascale Infrastructure
The database instances are configured for high availability with Oracle Real Application Clusters (RAC) enabled. To achieve availability zone redundancy for the database, use Oracle Active Data Guard in synchronous mode to replicate the database across availability zones.
A prerequisite for Active Data Guard is to establish a private networking path between availability zones, either through:
- Deploying two different ODB networks in a VPC, or
- OCI backbone connectivity using VCN peering with Local Peering Gateways
Port 1521 must be open for communication with Oracle Active Data Guard, as Data Guard transport services use port 1521 to transmit redo log files. For detailed networking design considerations, see Maximum Availability Architecture (MAA).
Backup and Recovery
Automated database backups can be configured using Oracle Autonomous Recovery Service or OCI Object Storage, depending on the selected database service and recovery requirements.
Data Encryption
For data in transit, Oracle AI Database@Google Cloud services are accessible only through encrypted communication channels. By default, the Oracle Net client is configured to use encrypted sessions, ensuring that all database connections are protected in transit.
Oracle AI Database@Google Cloud protects data at rest using Transparent Data Encryption (TDE), which is enabled by default with no customer configuration required. TDE automatically encrypts database files, redo and undo logs, backups, and other persistent data when written to storage, and transparently decrypts the data when accessed by authorized processes. Encryption is managed using a hierarchical key model, where a master encryption key protects tablespace keys that in turn encrypt the data.
Cross-region Oracle Data Guard is not supported when customer-managed encryption keys are stored in Google Cloud Key Management Service (KMS)
Migration to Oracle AI Database@Google Cloud
Oracle Zero Downtime Migration (ZDM) provides multiple migration workflows to move PeopleSoft databases to Oracle AI Database@Google Cloud.
Migration to Exadata Database, Exascale Database, and Base Database
- Physical Online Migration
The physical online migration workflow supports migrations between the same database versions and platforms. This approach uses direct data transfer and the
restore from servicemethod to create the target database, avoiding the use of intermediate backup storage. Oracle Data Guard is used to keep the source and target databases synchronized, enabling a minimal-downtime migration. - Physical Offline Migration
The physical offline migration workflow supports migrations between the same database versions and platforms. The target database is created using Recovery Manager (RMAN) backup and restore. Google Cloud Filestore is used to provide an NFS file share for storing RMAN backup files during the migration process.
- Logical Online Migration
The logical online migration workflow supports migrations between the same or different database versions and platforms. This workflow uses Oracle Data Pump export and import to create the target database. Google Cloud Filestore provides an NFS file share to store the Data Pump dump files. Oracle GoldenGate is used to synchronize the source and target databases, enabling a minimal-downtime migration.
- Logical Offline Migration
The logical offline migration workflow supports migrations between the same or different database versions and platforms. The target database is created using Oracle Data Pump export and import. Google Cloud Filestore provides an NFS file share to store the Data Pump dump files used during the migration.
Migration to Autonomous AI Database (Serverless)
- Logical Online Migration
The logical online migration workflow supports migrations between the same or different database versions and platforms. This workflow uses Oracle Data Pump export and import to create the target Autonomous AI Database. Google Cloud Filestore provides an NFS file share for storing Data Pump dump files, while Oracle GoldenGate keeps the source and target databases synchronized to achieve a minimal-downtime migration.
- Logical Offline Migration
The logical offline migration workflow supports migrations between the same or different database versions and platforms. The target Autonomous AI Database is created using Oracle Data Pump export and import. Google Cloud Filestore provides an NFS file share to store the Data Pump dump files used during the migration.
Components Overview
| Component | Purpose |
|---|---|
| Oracle AI Database@Google Cloud |
Oracle AI Database@Google Cloud provides Oracle Exadata Database Service on Dedicated Infrastructure, deployed and operated in Google Cloud with native Google Cloud integration. It combines Exadata performance and Oracle AI Database capabilities with Google Cloud networking, security, and consumption models. The offering includes Oracle Exadata Database Service on Dedicated Infrastructure, Oracle Exadata Database Service on Exascale Infrastructure, Oracle Autonomous AI Database Service, and Oracle Base Database Service for hosting the database layer. |
| Load Balancer | Load Balancer distributes incoming traffic across web or application servers and continuously monitors backend health probes to send traffic only to healthy instances. This ensures even traffic distribution, high availability, and automatic failover without application |
| Bastion | Google Cloud Bastion Virtual Machine enables secure RDP and SSH access to virtual machines over HTTPS without requiring public IP addresses. It improves security by centralizing administrative access and reducing exposure to inbound internet threats. |
| Autonomous Recovery Service | Autonomous Recovery Service provides automated backup, continuous data protection, and fast recovery for Oracle AI Database(s). It reduces data loss and recovery time by autonomously managing backups, validation, and restore operations. |
| Object Storage | Object Storage provides durable, scalable storage for unstructured data using a bucket-and-object model. It is commonly used for backups, archival, and data sharing with built-in security and lifecycle controls |
| OCI Vault | OCI Vault provides centralized management of encryption keys and secrets using Oracle-managed HSMs. It enables strong security, key rotation, and access control for protecting data across OCI services. |
| Google Cloud Filestore | Google Cloud Filestore provides fully managed, shared file storage for Google Cloud using the standard NFS protocol. It enables applications to access scalable, high-performance, highly available file shares without managing underlying file servers or storage infrastructure. |
| Google Cloud Key Management Service (Cloud KMS) | Google Cloud Key Management Service (Cloud KMS) is a managed service that provides secure creation, storage, and lifecycle management for secrets, encryption keys and certificated used by enterprise applications. |
Learn more
- PeopleSoft Information Portal
- PeopleSoft on the Oracle Help Center
- Support for PeopleSoft Applications Running in a Multicloud Environment (Doc ID 3066912.1)
- Learn more about Single Sign on for PeopleSoft
- E-SEC: What Is Microsoft Entra and Is Entra Supported For Authentication Into PeopleSoft? (Doc ID 3073875.1)
- E-SEC: PT 8.x How to Setup External Single Signon Solutions with PeopleSoft (KB563357)