Use Identity and Access Management (IAM) Authentication with Autonomous AI Database
Note:
Autonomous AI Database integration with Oracle Cloud Infrastructure (OCI) IAM is supported in commercial tenancies with identity domains as well as the legacy Oracle Cloud Infrastructure IAM, which does not include identity domains. Oracle Cloud Infrastructure IAM with identity domains was introduced with new OCI tenancies created after November 8, 2021. Autonomous AI Database supports users and groups in default and non-default identity domains.About Identity and Access Management (IAM) Authentication with Autonomous AI Database
Oracle Cloud Infrastructure IAM integration with Autonomous AI Database supports both database password authentication and token-based authentication. See Authenticating and Authorizing IAM Users for Oracle Autonomous AI Databases for complete details about the architecture for using IAM users on Autonomous AI Database.
IAM Database Password Authentication
Note:
Any supported 12c and above database client can be used for IAM database password access to Autonomous AI Database.An Oracle Cloud Infrastructure IAM database password allows an IAM user to log in to an Autonomous AI Database instance as Oracle Database users typically log in with a user name and password. The user enters their IAM user name and IAM database password. An IAM database password is a different password than the Oracle Cloud Infrastructure Console password. Using an IAM user with the password verifier you can login to Autonomous AI Database with any supported database client.
Identity and Access Management (IAM) SSO Token Based Authentication
There are several ways a database client can obtain an IAM database token:
-
A client application or tool can request the database token from IAM for the user and can pass the database token through the client API. Using the API to send the token overrides other settings in the database client. This type of IAM database token usage is supported for the following clients:
- JDBC-thin on all platforms
- Oracle Instant Client OCI-C on Linux
- Oracle Data Provider for .NET (ODP.NET) Core
-
If the application or tool does not support requesting an IAM database token through the client API, the IAM user can first use Oracle Cloud Infrastructure command line interface (CLI) to retrieve the IAM database token and save it in a file location. For example, to use SQL*Plus and other applications and tools using this connection method, you first obtain the database token using the Oracle Cloud Infrastructure (OCI) Command Line Interface (CLI). If the database client is configured for IAM database tokens, when a user logs in with the slash login form, the database driver uses the IAM database token that has been saved in a default or specified file location.
-
A client application or tool can use an Oracle Cloud Infrastructure IAM instance principal or resource principal to get an IAM database token, and use the IAM database token to authenticate itself to an Autonomous AI Database instance.
-
IAM users and OCI applications can request a database token from IAM with several methods, including using an API-key. See Configuring a Client Connection for SQL*Plus That Uses an IAM Token for an example. See About Authenticating and Authorizing IAM Users for an Oracle Autonomous AI Database for a description of other methods such as using a delegation token within an OCI cloud shell.
If a user enters a username/password to login, then the database driver uses the password verifier method to access the database regardless of the client's database token setting.
Prerequisites for Identity and Access Management (IAM) Authentication on Autonomous AI Database
Before using Identity and Access Management (IAM) authentication on Autonomous AI Database, you must ensure the following:
Use the Networking service to add a service gateway, a route rule, and an egress security rule to the VCN (Virtual Cloud Network) and subnets where your Autonomous AI Database resources reside.
- Create a service gateway in the VCN (Virtual Cloud Network) where your Autonomous AI Database resources reside by following the instructions in Task 1: Create the service gateway in Oracle Cloud Infrastructure Documentation.
- After creating the service gateway, add a route rule and an egress security rule to each subnet (in the VCN) where Autonomous AI Database resources reside so that these resources can use the gateway to use Identity and Access Management (IAM) authentication:
- Go to the Subnet Details page for the subnet.
- In the Subnet Information tab, click the name of the subnet's Route Table to display its Route Table Details page.
- In the table of existing Route Rules, check whether there is already a rule with the following characteristics:
- Destination: All IAD Services In Oracle Services Network
- Target Type: Service Gateway
- Target: The name of the service gateway you just created in the VCN
If such a rule does not exist, click Add Route Rules and add a route rule with these characteristics.
- Return to the Subnet Details page for the subnet.
- In the subnet's Security Lists table, click the name of the subnet's security list to display its Security List Details page.
- In the side menu, under Resources, click Egress Rules.
- In the table of existing Egress Rules, check whether there is already a rule with the following characteristics:
- Stateless: No
- Destination: All IAD Services In Oracle Services Network
- IP Protocol: TCP
- Source Port Range: All
- Destination Port Range: 443
- If such a rule does not exist, click Add Egress Rules and add an egress rule with these characteristics.
The HTTP Proxy settings in your environment must allow the database to access the cloud service provider.
Note:
The network configuration including the HTTP Proxy can only be edited until the Exadata Infrastructure is in Requires Activation state. Once it is activated, you cannot edit those settings.Setting up an HTTP Proxy for an already provisioned Exadata Infrastructure needs a Service Request (SR) in My Oracle Support. See Create a Service Request in My Oracle Support for details.
Change External Identity Providers on Autonomous AI Database
Describes the steps to change the external identity provider from (IAM) authentication and authorization to another external authentication provider and vice-versa.
Oracle Cloud Infrastructure (IAM) authentication and authorization for users is enabled for newly provisioned Autonomous AI Databases and Autonomous Container Databases, by default. There are other external authentication schemes such as, Centrally Managed Users with Active Directory (CMU-AD), Azure AD, and Kerberos that you can enable for your Autonomous AI Database. However, there can only be one external authentication scheme enabled at any given time.
- Disable IAM integration using the DBMS_CLOUD_ADMIN.DISABLE_EXTERNAL_AUTHENTICATION procedure:
For example:
For additional information, see DISABLE_EXTERNAL_AUTHENTICATION Procedure.BEGIN DBMS_CLOUD_ADMIN.DISABLE_EXTERNAL_AUTHENTICATION; END; / - Follow the steps outlined in the following pages to configure another external authentication scheme of your choice:
- Re-enable IAM users to connect to Autonomous AI Database using Oracle Cloud Infrastructure (IAM) Authentication and Authorization.
As an ADMIN user, run the DBMS_CLOUD_ADMIN.ENABLE_EXTERNAL_AUTHENTICATION procedure with the parameters shown below:
BEGIN DBMS_CLOUD_ADMIN.ENABLE_EXTERNAL_AUTHENTICATION( type => 'OCI_IAM' force => TRUE ); END; /The above example disables any external authentication provider that is currently enabled and enables Oracle Cloud Infrastructure (IAM) Authentication and Authorization.
In this example:forceis set toTRUEto disable the external authentication that is currently enabled.typeis set to'OCI_IAM'to enable and use Oracle Cloud Infrastructure (IAM) Authentication and Authorization.
Note:
By default theforceparameter isFALSE. When another external authentication method is enabled andforceisFALSE, DBMS_CLOUD_ADMIN.ENABLE_EXTERNAL_AUTHENTICATION reports the following error:ORA-20004: Another external authentication is already enabled.See ENABLE_EXTERNAL_AUTHENTICATION Procedure for further reference.
- Verify the value of
IDENTITY_PROVIDER_TYPEsystem parameter as shown below:SELECT NAME, VALUE FROM V$PARAMETER WHERE NAME='identity_provider_type'; NAME VALUE ---------------------- ------- identity_provider_type OCI_IAM
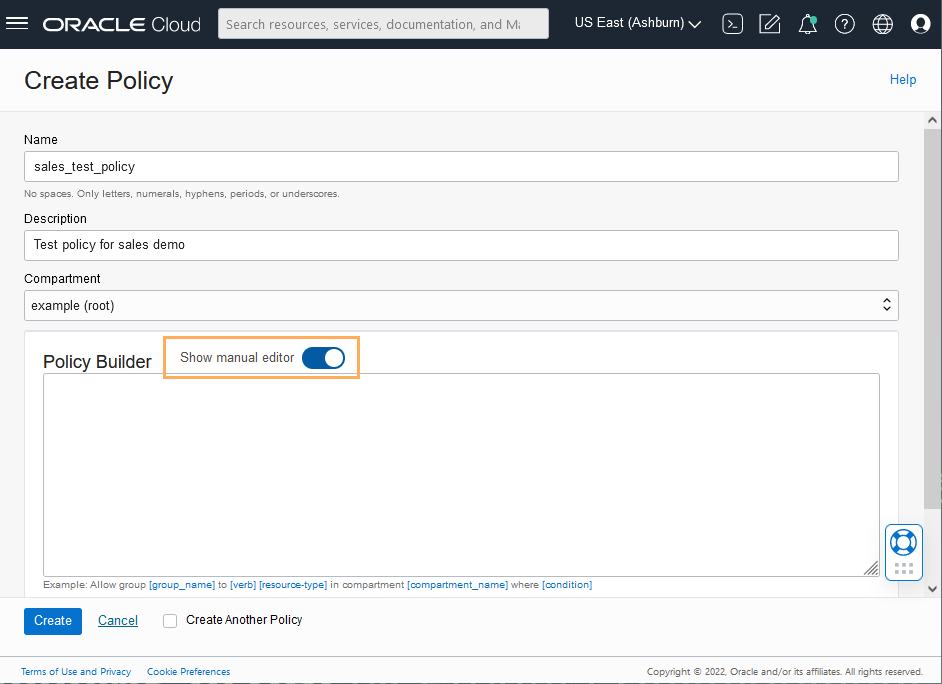
Create Identity and Access Management (IAM) Groups and Policies for IAM Users
Describes the steps to write policy statements for an IAM group to enable IAM user access to Oracle Cloud Infrastructure resources, specifically Autonomous AI Database instances.
A policy is a group of statements that specifies who can access particular resources, and how. Access can be granted for the entire tenancy, databases in a compartment, or individual databases. This means you write a policy statement that gives a specific group a specific type of access to a specific type of resource within a specific compartment.
Note:
Defining a policy is required to use IAM tokens to access Autonomous AI Database. A policy is not required when using IAM database passwords to access Autonomous AI Database.To enable Autonomous AI Database to allow IAM users to connect to the database using IAM tokens:
Notes for creating policies for use with IAM users on Autonomous AI Database:
-
Policies can allow IAM users to access Autonomous AI Database instances across the entire tenancy, in a compartment, or can limit access to a single Autonomous AI Database instance.
-
You can use either instance principal or resource principal to retrieve database tokens to establish a connection from your application to an Autonomous AI Database instance. If you are using an instance principal or resource principal, you must map a dynamic group. Thus, you cannot exclusively map instance and resource principals; you only can map them through a shared mapping and putting the instance or resource instance in an IAM dynamic group.
You can create Dynamic Groups and reference dynamic groups in the policies you create to access Oracle Cloud Infrastructure. See Plan Access Controls and Create Supporting Resources and Managing Dynamic Groups for details.
Add IAM Users on Autonomous AI Database
To add IAM users to allow access to Autonomous AI Database, map database global users to IAM groups or users with
CREATE USER or ALTER USER statements (with
IDENTIFIED GLOBALLY AS clause).
The authorization of IAM users to an Autonomous AI Database instance works by mapping IAM global users (schemas) to IAM users (exclusive mapping) or IAM groups (shared schema mapping).
To authorize IAM users on an Autonomous AI Database instance:
Note:
Database users that are notIDENTIFIED GLOBALLY can continue to
login as before, even when the Autonomous AI Database is enabled for IAM authentication.
To exclusively map a local IAM user to an Oracle Database Global User:
-
Log in as the ADMIN user to the database that is enabled to use IAM (the ADMIN user has the required
CREATE USERandALTER USERsystem privileges that you need for these steps). -
Create a mapping between the Autonomous AI Database user (schema) with
CREATE USERorALTER USERstatements and include theIDENTIFIED GLOBALLY ASclause, specifying the IAM local IAM user name.For example, to create a new database global user named
peter_fitchand map this user to an existing local IAM user namedpeterfitch:CREATE USER peter_fitch IDENTIFIED GLOBALLY AS 'IAM_PRINCIPAL_NAME=peterfitch'The following example shows how to create the user by specifying a non-default domain,
sales_domain:CREATE USER peter_fitch2 IDENTIFIED GLOBALLY AS 'IAM_PRINCIPAL_NAME=sales_domain/peterfitch';
Add IAM Roles on Autonomous AI Database
Optionally, create global roles to provide additional database roles and privileges to IAM users when multiple IAM users are mapped to the same shared global user.
The use of global roles is optional when using either an exclusive IAM mapping to user (schema) or shared user mapping on Autonomous AI Database. For example, all privileges and roles can be granted to the shared schema and all IAM users who map to the shared schema would be granted the privileges and roles assigned to the shared schema.
You can use a global role to optionally differentiate users who use the same shared
schema. For example, a set of users can all have the same shared schema and the shared
schema could have the CREATE SESSION privilege. Then global roles can
be used to provide differentiated privileges and roles assigned to different groups of
users who all use the same shared schema.
Granting additional roles to IAM users in Autonomous AI Database works by mapping Autonomous AI Database global roles to IAM groups.
To map Autonomous AI Database global roles to IAM groups:
If you want to add additional global role mappings for other IAM groups, follow these steps for each IAM group.
Create IAM Database Password for IAM Users
To add an IAM user and allow the IAM user to login to Autonomous AI Database by supplying a username and password, you must create an IAM database password.
See Working with IAM Database Passwords for more information.
Connect to Autonomous AI Database with Identity and Access Management (IAM) Authentication
After the database ADMIN user maps global users and global roles to the IAM users and IAM groups, users log in to the Autonomous AI Database instance using their Oracle Cloud Infrastructure IAM credentials or access the database through an Oracle Cloud Infrastructure IAM database token.
You can still log in to the Autonomous AI Database using your local database account username and password (non-global database user account).
You can use a database client to access an Autonomous AI Database instance as an Oracle Cloud Infrastructure IAM user. To use a client with Oracle Cloud Infrastructure IAM username and password credentials and a password verifier, the database client must be 12c or newer.
-
JDBC-Thin with support for IAM Token Authentication is supported with the following:
-
JDBC version 19.13.0.0.1 (or later): See JDBC and UCP Downloads for JDBC drivers.
-
JDBC version 21.4.0.0.1 (or later): See JDBC and UCP Downloads for JDBC drivers.
See Support for IAM Token-Based Authentication for more information:
-
- SQL*Plus and Oracle Instant Client: Supported with SQL*Plus and Instant Client on Linux versions 19.13 or later, and Instant Client on Linux versions 21.4 or later.
See Identity and Access Management (IAM) Token-Based Authentication for more information.
-
The database client can also be configured to retrieve a database token using the IAM username and IAM database password.
See Client Connections That Use a Token Requested by an IAM User Name and Database Password for more information.
-
.NET clients (latest version of Linux or Windows). .NET software components are available as a free download from the following sites:
Note:
If your Autonomous AI Database instance is in Restricted Mode, only the users with the RESTRICTED SESSION privilege such as ADMIN can connect to the database.
About Connecting to an Autonomous AI Database on Dedicated Exadata Infrastructure Instance Using IAM
IAM users can connect to the Autonomous AI Database on Dedicated Exadata Infrastructure instance by using either an IAM database password verifier or an IAM token.
Using the IAM database password verifier is similar to the Oracle Database password authentication process. However, instead of the password verifier (encrypted hash of the password) being stored in the Autonomous AI Database on Dedicated Exadata Infrastructure, the verifier is instead stored as part of the Oracle Cloud Infrastructure (OCI) IAM user profile.
The second connection method, the use of an IAM token for the database, is more modern. The use of token-based access is a better fit for Cloud resources such as Autonomous AI Database on Dedicated Exadata Infrastructure. The token is based on the strength that the IAM endpoint can enforce. This can be multi-factor authentication, which is stronger than the use of passwords alone. Another benefit of using tokens is that the password verifier (which is considered sensitive) is never stored or available in memory.
Client Connections That Use an IAM Database Password Verifier
After you have configured the authorization needed for the IAM user, this user can log in using existing client application, such as SQL*Plus or SQLcl without additional configuration.
The IAM user enters the IAM user name and IAM database password (not the Oracle Cloud Infrastructure (OCI) console password) using any currently supported database client. The only constraint is that the database client version be either Oracle Database release 12.1.0.2 or later to use Oracle Database 12c passwords. The database client must be able to use the 12C password verifier. Using the 11G verifier encryption is not supported with IAM. No special client or tool configuration is needed for the IAM user to connect to the Autonomous AI Database on Dedicated Exadata Infrastructure instance.
Client Connections That Use a Token
For IAM token access to the Autonomous AI Database on Dedicated Exadata Infrastructure, the client application or tool requests a database token from IAM for the IAM user.
The client application will pass the database token directly to the database client through the database client API.
If the application or tool has not been updated to request an IAM token, then the IAM user can use Oracle Cloud Infrastructure (OCI) command line interface (CLI) to request and store the database token. You can request a database access token (db-token) using the following credentials:
- Security tokens (with IAM authentication), delegation tokens (in the OCI cloud shell) and
API-keys, which are credentials that represent the IAM user to enable the authentication - Instance principal tokens, which enable instances to be authorized actors (or principals) to perform actions on service resources after authenticating
- Resource principal token, which is a credential that enables the application to authenticate itself to other Oracle Cloud Infrastructure services
When the IAM users logs into the client with a slash / login and the OCI_IAM parameter is configured (sqlnet.ora, tnsnames.ora, or as part of a connect string), then the database client retrieves the database token from a file. If the IAM user submits a user name and password, the connection will use the IAM database verifier access described for client connections that use IAM database password verifiers. The instructions in this guide show how to use the OCI CLI as a helper for the database token. If the application or tool has been updated to work with IAM, then follow the instructions for the application or tool. Some common use cases include the following: SQL*Plus on-premises, SQLcl on-premises, SQL*Plus in Cloud Shell, or applications that use SEP wallets.
-
Configure a client connection for SQL*Plus to use an IAM database password.
-
Configure a client connection for SQL*Plus that uses an IAM token.
-
Access the database through an Oracle Cloud Infrastructure IAM database token using an instance principal.
Configuring a Client Connection for SQL*Plus That Uses an IAM Database Password
You can configure SQL*Plus to use an IAM database password.
Configuring a Client Connection for SQL*Plus That Uses an IAM Token
You can configure a client connection for SQL*Plus that uses an IAM token.
TOKEN_AUTH
parameter, the IAM user can log in to the Autonomous AI Database instance by running the following command to start SQL*Plus. You can include
the connect descriptor itself or use the name of the descriptor from the
tnsnames.ora
file.connect /@exampledb_highOr:
connect /@(description=
(retry_count=20)(retry_delay=3)
(address=(protocol=tcps)(port=1522)
(host=example.us-phoenix-1.oraclecloud.com))
(connect_data=(service_name=aaabbbccc_exampledb_high.example.oraclecloud.com))
(security=(ssl_server_cert_dn="CN=example.uscom-east-1.oraclecloud.com,
OU=Oracle BMCS US, O=Example Corporation,
L=Redwood City, ST=California, C=US")
(TOKEN_AUTH=OCI_TOKEN)))
The database client is already configured to get a db-token
because TOKEN_AUTH has already been set, either through the
sqlnet.ora file or in a connect string. The database client gets the
db-token and signs it using the private key and then sends the token to
the Autonomous AI Database. If an IAM user name and IAM
database password are specified instead of slash /, then the database
client will connect using the password instead of using the
db-token.
Use Instance Principal to Access Autonomous AI Database with Identity and Access Management (IAM) Authentication
After the ADMIN user enables Oracle Cloud Infrastructure IAM on Autonomous AI Database, an application can access the database through an Oracle Cloud Infrastructure IAM database token using an instance principal.
See Accessing the Oracle Cloud Infrastructure API Using Instance Principals for more information.
Configure Proxy Authentication
Proxy authentication allows an IAM user to proxy to a database schema for tasks such as application maintenance.
Proxy authentication is typically used to authenticate the real user and then authorize them to use a database schema with the schema privileges and roles in order to manage an application. Alternatives such as sharing the application schema password are considered insecure and unable to audit which actual user performed an action.
A use case can be in an environment in which a named IAM user who is an application database administrator can authenticate by using their credentials and then proxy to a database schema user (for example, hrapp). This authentication enables the IAM administrator to use the hrapp privileges and roles as user hrapp in order to perform application maintenance, yet still use their IAM credentials for authentication. An application database administrator can sign in to the database and then proxy to an application schema to manage this schema.
You can configure proxy authentication for both the password authentication and token authentication methods.
Configuring Proxy Authentication for the IAM User
To configure proxy authentication for an IAM user, the IAM user must already have a mapping to a global schema (exclusive or shared mapping). A separate database schema for the IAM user to proxy to must also be available.
-
Log in to the Autonomous AI Database instance as a user who has the
ALTER USERsystem privileges. -
Grant permission for the IAM user to proxy to the local database user account.An IAM user cannot be referenced in the command so the proxy must be created between the database global user (mapped to the IAM user) and the target database user.In the following example,
hrappis the database schema to proxy to, andpeterfitch_schemais the database global user exclusively mapped to userpeterfitch.ALTER USER hrapp GRANT CONNECT THROUGH peterfitch_schema;
At this stage, the IAM user can log in to the database instance using the proxy. For example:
CONNECT peterfitch[hrapp]@connect_string
Enter password: passwordCONNECT [hrapp]/@connect_stringValidating the IAM User Proxy Authentication
-
Log in to the Autonomous AI Database instance as a user who has the
CREATE USERandALTER USERsystem privileges. -
Connect at the IAM user and execute the
SHOW USERandSELECT SYS_CONTEXTcommands. For example, suppose you want to check the proxy authentication of the IAM userpeterfitchwhen they proxy to database userhrapp. You will need to connect to the database using the different types of authentication methods shown here, but the output of the commands that you execute will be the same for all types.-
For password authentication:
CONNECT peterfitch[hrapp]/password\!@connect_string SHOW USER; --The output should be USER is "HRAPP" SELECT SYS_CONTEXT('USERENV','AUTHENTICATION_METHOD') FROM DUAL; --The output should be "PASSWORD_GLOBAL" SELECT SYS_CONTEXT('USERENV','PROXY_USER') FROM DUAL; --The output should be "PETERFITCH_SCHEMA" SELECT SYS_CONTEXT('USERENV','CURRENT_USER') FROM DUAL; --The output should be "HRAPP" -
For token authentication:
CONNECT [hrapp]/@connect_string SHOW USER; --The output should be USER is "HRAPP " SELECT SYS_CONTEXT('USERENV','AUTHENTICATION_METHOD') FROM DUAL; --The output should be "TOKEN_GLOBAL" SELECT SYS_CONTEXT('USERENV','PROXY_USER') FROM DUAL; --The output should be "PETERFITCH_SCHEMA" SELECT SYS_CONTEXT('USERENV','CURRENT_USER') FROM DUAL; --The output should be "HRAPP"
-
Use Database Link with IAM Authenticated Users
You can use a database link to connect from one Autonomous AI Database instance to another as an Oracle Cloud Infrastructure IAM user.
You can use either connected user or fixed user database link to connect to an Autonomous AI Database as an Oracle Cloud Infrastructure IAM user.
Note:
Current user database link is not supported for connecting to an Autonomous AI Database as an Oracle Cloud Infrastructure IAM user.-
Connected User Database Link: For a connected user database link, an IAM user must be mapped to a schema in both the source and target databases connected by a database link. You can use a database password verifier or an IAM database token to use a connected user database link.
-
Fixed User Database Link: A fixed user database link can be created using a database user or an IAM user. When using an IAM user as a fixed user database link, the IAM user must have a schema mapping in the target database. The IAM user for a database link can be configured with a password verifier only.
Disable Identity and Access Management (IAM) Authentication on Autonomous AI Database
Describes the steps to disable IAM external authentication user access for Autonomous AI Database.
ALTER SYSTEM command as shown below:ALTER SYSTEM RESET IDENTITY_PROVIDER_TYPE SCOPE=BOTH;
If you also want to update access to IAM from the resource, that is, Autonomous Container Database or Autonomous AI Database, you may need to remove or modify the IAM group and the policies you set up to allow access to IAM from those resources.
Notes for Using Autonomous AI Database Tools with Identity and Access Management (IAM) Authentication
Provides notes for using Autonomous AI Database tools with IAM authentication enabled.
- Oracle APEX is not supported for IAM users with Autonomous AI Database. See Access Oracle Application Express Administration Services for information on using regular database users with Autonomous AI Database.
-
Database Actions is not supported for IAM users with Autonomous AI Database. See Enabling User Access to Database Actions for information on using regular database users with Autonomous AI Database.