Understand App Gateway
Understand what an App Gateway is, why you should use it, and how App Gateway works to to protect access to your web applications.
- What is App Gateway?
- Why Should You Use App Gateway?
- How Does App Gateway Work?
- Set Up High Availability
Enable App Gateway. This is Standard License feature. To learn about these features, see Standard License Tier Features for Oracle Identity Cloud Service.
What is App Gateway?
App Gateway is a software appliance that enables you to integrate applications hosted either on a compute instance, in a cloud infrastructure, or in an on-premises server with Oracle Identity Cloud Service for authentication purposes.
App Gateway acts as a reverse proxy protecting web applications by restricting unauthorized network access to them. App Gateway intercepts any HTTP request to these applications and ensures that the users are authenticated with Oracle Identity Cloud Service before forwarding the request to these application. App Gateway propagates the authenticated user's identity to the applications.
If the user isn't authenticated with Oracle Identity Cloud Service, then App Gateway redirects the user to Oracle Identity Cloud Service's Sign In page for credential validation.
Why Should You Use App Gateway?
App Gateway is a non-intrusive integration method that uses a middle-tier layer to integrate web applications with Oracle Identity Cloud Service for authentication purposes.
Use App Gateway to:
-
Integrate enterprise applications hosted either on-premises or in a cloud infrastructure with Oracle Identity Cloud Service for authentication purposes.
For example, if you have a web applications hosted on-premises or in a cloud infrastructure, you can ingrate this application with any other cloud-based applications for single sign-on. Use App Gateway to integrate your web application with Oracle Identity Cloud Service, and then make sure that the other cloud-based applications use Oracle Identity Cloud Service as their authentication mechanism. All these applications will make use of the single sign-on provided by Oracle Identity Cloud Service.
-
Expose intranet web applications to internet access.
If your web application is hosted and accessed over your intranet and you want to expose access to this application over the internet, use App Gateway to proxy any internet request and to require users to authenticate with Oracle Identity Cloud Service before accessing your intranet web application. In this case, you deploy App Gateway in your network DMZ while your application remains in the intranet zone.
-
Integrate with applications that lack a native authentication mechanism and don't support SAML federation, OAuth, or OpenID Connect integration methods.
If your application doesn't support the standards for authentication that Oracle Identity Cloud Service supports (
SAML,OAuth, andOpenID Connect), and you can't use Oracle Identity Cloud Service's SDKs in your application, then you can use App Gateway to integrate your web application with Oracle Identity Cloud Service. -
Integrate with applications that support the HTTP Header-based authentication.
For web applications that support HTTP Header-based authentication, the App Gateway integration method requires no change to the web application's source code. You need to configure the application's authentication policies in Oracle Identity Cloud Service to add header variables in the request before App Gateway forwards the request to the application. By doing so, the application can identify the user authenticated with Oracle Identity Cloud Service.
How Does App Gateway Work?
The App Gateway is deployed within a customer’s infrastructure, regardless of whether the infrastructure is in the cloud, on-premises, or a hybrid one.
The App Gateway works as a reverse proxy, intercepting all requests from the client to the application. The App Gateway then verifies if a user is already logged in to Oracle Identity Cloud Service. If the user has logged in, then App Gateway adds header variables to the request so that the application being protected can access the header variable The application trusts App Gateway has identified the signed in user in Oracle Identity Cloud Service values and create the user session.
Ensure that the communication between App Gateway and application is secure to avoid changes in the header variable values before the request is sent to the application.
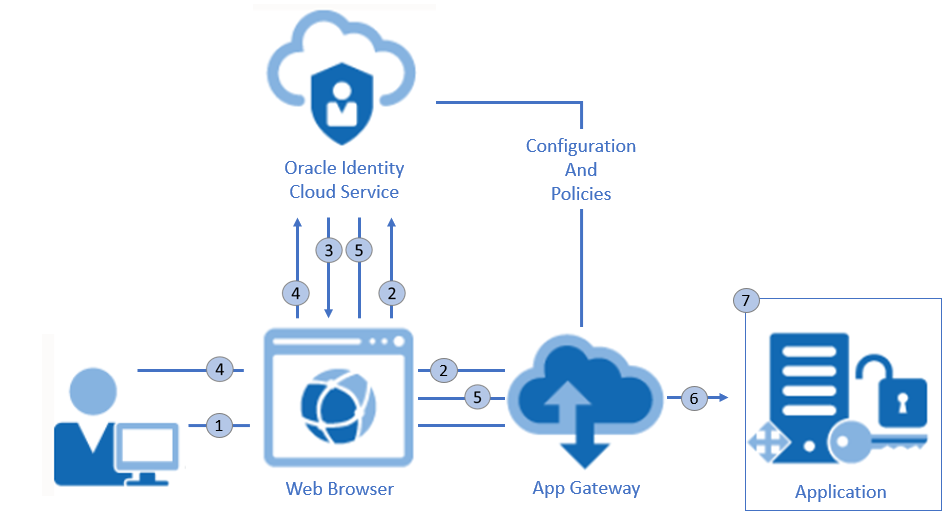
Description of the illustration appgateway_architecture.png
The following steps explain the form-based authentication flow between the web browser, App Gateway, and an enterprise application:
- In a web browser, a user requests access to an application through a URL exposed by App Gateway.
- App Gateway intercepts the request, verifies the user doesn't have a session with Oracle Identity Cloud
Service, and then redirects the user's browser to the Oracle Identity Cloud
Service's Sign In page.
In step 2, if the user has a session with Oracle Identity Cloud Service, it means that the user has already signed in to Oracle Identity Cloud Service. If so, then an access token is sent to App Gateway, and then the remaining steps are skipped.
- Oracle Identity Cloud Service presents the Sign In page or whichever sign-in mechanism has been configured for Oracle Identity Cloud Service.
- The user signs in to Oracle Identity Cloud Service.
- Upon successful authentication, Oracle Identity Cloud Service creates a session for the user and issues an access token to App Gateway.
- App Gateway uses the token to identify the user. It then adds header variables to the request and forwards the request to the application.
- The application receives the header information, validates the user's identity, and starts the user session.
Any subsequent request to the application's protected resources is intercepted by App Gateway. App Gateway identifies the user, adds header variables to the request, and forwards the request to the application.
To sign out, the user calls an application's logout URL. The App Gateway identifies the logout URL and redirects the user to the Oracle Identity Cloud
Service's OAuth logout endpoint (/oauth2/v1/userlogout). After Oracle Identity Cloud
Service signs the user out, Oracle Identity Cloud
Service can redirect the user's browser to a URL of the application which can then remove the application's user session.
Set Up High Availability
Use a load balancer to achieve high availability for multiple instances of App Gateway.
If high-availability is a requirement to access your web application, you can have multiple App Gateways, configure each of them to integrate with Oracle Identity Cloud Service, and use a load balancer to balance the request among the App Gateway instances.
The following architecture diagram shows the components required for high availability.
Figure 29-1 App Gateway Load Balancer Diagram
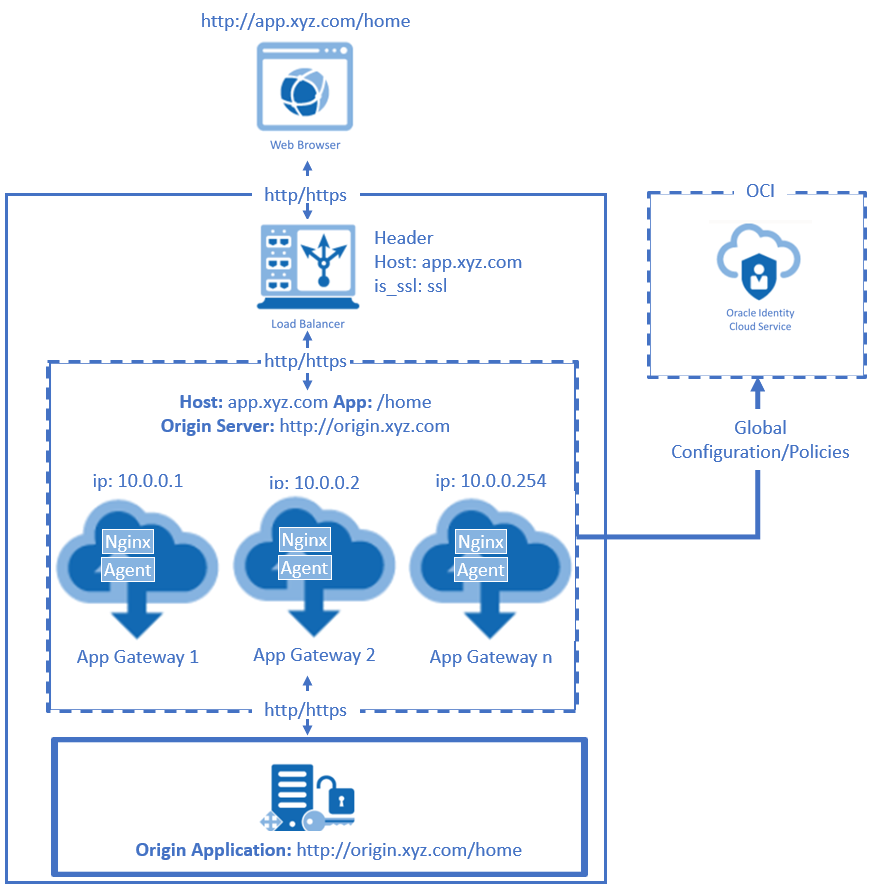
This architecture requires that you install and configure more than one instance of App Gateway. Each App Gateway instance is configured to link to the same Oracle Identity Cloud Service URL, and to use the same Client ID and Client Secret from the App Gateway registration in Oracle Identity Cloud Service console.
Use a load balancer to distribute request between the App Gateway instances.
Additionally, the load balancer must perform health checks via HTTP with HTTP keepalives enabled for a duration that exceeds the health check interval. This prevents the load balancer from redirecting browser requests to an offline App Gateway instance.
The health check endpoint of App Gateway is /cloudgate/v1/about.