Prerequisites for Creating a Connection
Satisfy the following prerequisites specific to your environment to create a connection with the Oracle ERP Cloud Adapter.
- Subscribe to Oracle ERP Cloud
- Verify the Status of Location-Based Access Control (LBAC)
- Assign Required Roles to an Integration User
- Upload Files in Bulk and Insert Data into Oracle ERP Cloud Application Tables for New Integrations
- Upload Files to Oracle WebCenter Content
- Perform Prerequisites to Set Up the OAuth Authorization Code Credentials Security Policy
- Access the REST Catalog Through the Oracle ERP Cloud Adapter
- Create Custom Business Events
- Obtain the Oracle ERP Cloud Service Catalog Service WSDL, Event Catalog URL, or Interface Catalog URL (For Connections Created Prior to 2/18/20)
Subscribe to Oracle ERP Cloud
This action enables you to create an Oracle ERP Cloud user account with the correct privileges. You specify this user account when creating an Oracle ERP Cloud Adapter connection on the Connections page.
See Oracle ERP Cloud.
Verify the Status of Location-Based Access Control (LBAC)
Check if you have enabled Location-Based Access Control (LBAC) for Fusion Applications (for Oracle ERP Cloud).
If LBAC is enabled, you must allowlist (explicitly allow identified
entities access) the Oracle Integration NAT Gateway IP address in your LBAC. If you
do not perform this task, you can receive a 401 Access Denied error
or 403 Forbidden error from Oracle Fusion Applications.
See How Location-Based Access Works in Securing Oracle SCM Cloud and Doc ID 2615294.1 at Oracle Support Services.
Assign Required Roles to an Integration User
To use the Oracle ERP Cloud Adapter in an integration, you must assign specific roles to an integration user.
Associating the Integration User with the Following Roles and Privileges
| Role | Description |
|---|---|
|
Integration Specialist |
This is a job role and does not include data roles. Assign the Integration Specialist role that inherits Oracle ERP Cloud roles. This role applies to Release 13. |
|
Oracle ERP Cloud-specific data access to the integration user |
You must specify the specific data access roles based on the objects you want to integrate. This role applies to Release 13. See Managing Data Access for Users: Explained of Securing Oracle Cloud ERP. |
|
AttachmentsUser |
Provides access to the Attachments security group to download the log file or the output file with the ERP Integration Service. This role is automatically shipped. You must verify that this role is automatically assigned to the user. |
|
SOAOperator |
The SOA operator role is required to receive ERP business events. |
|
FND_MANAGE_CATALOG_SERVICE_PRIV |
The role to manage the web services catalog. |
|
Customer Relationship Management Application Administrator (for Oracle CRM Cloud implementations) |
See Chapter Customer Relationship Management Application Administrator (Job Role) in Security Reference for CX Sales and B2B Service. |
Additional roles may be required as per each interface requirements.
Using the Security Console
Use the Security Console to manage application security such as roles, users, certificates, and administration tasks. Access to the Security Console is provided by the predefined Security Manager role. Access the Security Console in the following ways:
-
Use the Manage Job Roles or Manage Duties tasks in the Setup and Maintenance work area.
-
Select Navigator, then Tools, then Security Console.

Description of the illustration sales_cloud_security.png
See Using the Security Console in Securing Oracle Cloud ERP.
Create Connections Based on the User Role
You can create more than one service integration user account in Oracle Fusion Applications for different Oracle Fusion Applications roles that exist to perform different tasks and then create different Oracle Integration connections using those user accounts.
For example, you can create multiple connections in Oracle Integration such as ERP1, ERP2, ERP3, and so on and associate each of these connections with a designated account in Oracle ERP Cloud, such as user_integration_1 (general ledger), user_integration_2 (HCM), and user_integration_3 (projects). These actions create different connections for invoking different Oracle ERP Cloud jobs using an Oracle Fusion Applications user account set up for that job.
Upload Files in Bulk and Insert Data into Oracle ERP Cloud Application Tables for New Integrations
When using an Oracle ERP Cloud Adapter connection in an existing integration, you must satisfy the following prerequisites for the upload of files in bulk and the insertion of data into Oracle ERP Cloud application tables.
-
Satisfy the following prerequisites for the bulk upload of files and the insertion of data into Oracle ERP Cloud application tables. This is only required for an ERP Cloud callback upon job completion. Only file-based data import (FBDI)-compliant jobs are supported for callbacks.
- Create a user similar to the Oracle ERP Cloud Adapter connection user in the My Services or Oracle Cloud Infrastructure Console. This user is linked to the Oracle Integration WebLogic security realm. The user name must exactly match the Oracle ERP Cloud user name. The password and email address can be anything. Ensure that this user has permissions to execute integrations in Oracle Integration. It is recommended that you have a role such as ServiceAdmin or ServiceDeveloper, which have executable permissions on integrations. Ensure that you select the Integration role for the Oracle ERP Cloud user in the Oracle ERP Cloud application.
-
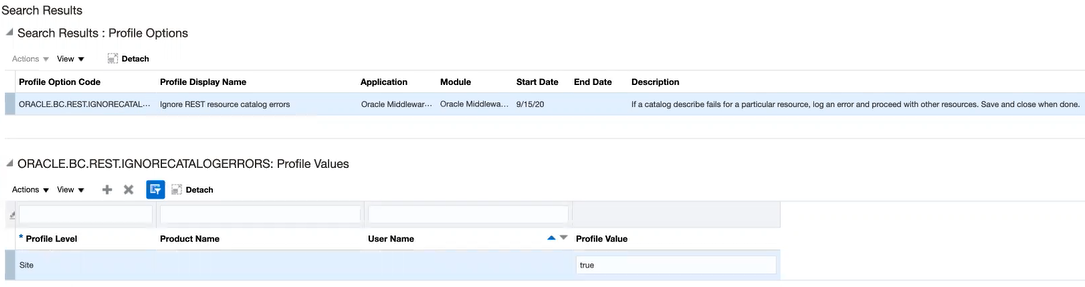
Import the following certificates:
-
In your browser, enter the service catalog URL:
For Release 13:https://hostname:port/fscmService/ServiceCatalogService?WSDL -
In the WSDL, navigate to the X509 certificates section:
Description of the illustration erp_certificates.png -
Copy the first certificate string to a file.
Note:
For each certificate file that you create, add your certificate string between the-----BEGIN CERTIFICATE-----and-----END CERTIFICATE-----lines for the certificate to be successfully imported into Oracle Integration. For example:-----BEGIN CERTIFICATE----- certificate_string -----END CERTIFICATE-----Otherwise, you may receive an
Invalid Certificateerror. -
Copy the second certificate to a file. You have two certificate files (for example,
erp_cert1.ceranderp_cert2.cer). -
In the Upload Certificate dialog in Oracle Integration, import both certificates as Message Protection Certificate types and enter unique alias names. See Upload an SSL Certificate.
-
Satisfy the following manifest file recommendations (that is, the properties file in the zip file that must be uploaded to Universal Content Management (UCM)).
-
The manifest file expects import process details in the following format:
<job package name>,<job def name>,<Manifest file name>,<job parameters (comma separated)>For example:
oracle/apps/ess/financials/payables/invoices/transactions,APXIIMPT,AP,#NULL,#NULL,#NULL,#NULL,#NULL,#NULL,#NULL,INVOICE -
The manifest file name should be a prefix of the actual zip file name if it contains
_. Otherwise, it should just be the name. For example, if the zip file name isAP_301.zip, the manifest file name should beAP.propertiesand the third value in the manifest should be the manifest file name. If the zip file name isAP.zip, the manifest file name should beAP.propertiesand the third value in the manifest should be the manifest file name. -
Only one job is supported per invoke. You can have multiple entries in the manifest property file to import data from the interface table to the applications tables in batches of up to 10 for sequential or up to 5 for parallel processing. For example, the journal import data file has records of 10 ledgers. The property file has 10 entries with the unique ledger name as a parameter. After the data file is loaded in the interface table, the import process has 10 subprocesses for each ledger.
-
-
-
Satisfy the following prerequisites to configure the integration that uses the bulk import feature:
-
Map the following parameters to the Oracle ERP Cloud Adapter.
-
Map parameter
ICSFileReferenceto theFile Referenceparameter from the other adapter (for example, the FTP Adapter, the REST Adapter, or whichever adapter you used that has theICSFileReferenceparameter). -
Map the
FileNameparameter from the source schema to the target schema (the target schema is the Oracle ERP Cloud bulk import schema). TheFileNamemust be unique for every request.
-
-
Upload Files to Oracle WebCenter Content
To upload files to Oracle WebCenter Content (Universal Content Manager) with the Oracle ERP Cloud Adapter, you must satisfy the following prerequisites.
-
Create a PGP Public Key:
To upload encrypted files, a PGP public key is required. You must generate the PGP public key and save it for upload. The supported algorithm for the public key is RSA for encryption and the key size must be 1024 bits in length.
The process for uploading files into Oracle ERP Cloud is:
-
You encrypt files using the Oracle ERP Cloud public key.
-
The data-loading process decrypts files using the Oracle ERP Cloud private key.
-
-
Configure Security and User Access
Once you have configured security groups and doc accounts for the file to upload, you can configure the Oracle ERP Cloud Adapter to upload the file to Oracle WebCenter Content.
See Understanding Security and User Access in Administering Oracle WebCenter Content.
Perform Prerequisites to Set Up the OAuth Authorization Code Credentials Security Policy
Perform the following prerequisites to set up the OAuth Authorization Code Credentials security policy with an Oracle Fusion Applications identity domain or a non-Oracle Fusion Applications identity domain (for example, the Oracle Integration identity domain).
Set Up the OAuth Authorization Code Credentials Security Policy with the Oracle Fusion Applications Identity Domain
You must create a resource application to represent the Oracle Fusion Applications resource and a client application for Oracle Integration to use the OAuth Authorization Code Credentials security policy. Once these tasks are completed, you can successfully configure a connection on the Connections page. You do not need to create any JWT signing certificates for upload into Oracle Fusion Applications.
Create an Identity Domain Resource Application to Represent the Oracle Fusion Applications Resource
- Create an identity domain resource application to represent the
Oracle Fusion Applications resource.
- Log in to the identity domain as the domain administrator.
- In the navigation pane, click Identity & Security.
- Click Domains.
- Select your compartment.
- Click the identity domain.
- In the navigation pane, click Integrated applications.
- Click Add application.
- Select Confidential Application, then click Launch workflow.
-
- On the Details page, provide a name (for example,
FA Resource), and click Next. - On the Client page, click Next without making changes.
- On the Resources page, click Configure this application as a resource server now.
- Optionally update the value in the Access Token Expiration field.
- Select Is Refresh Token Allowed.
- In the Primary Audience field, add
the Oracle Fusion Applications URL and port. This is the primary
recipient where the token is
processed.
https://FA_URL:443 - In the Scopes section, click Add.
- In the Scope field, enter
/. - In the Description field, enter All.
- Select Requires Consent.
- Click Add, then click Next.
- On the Web Tier Policy and Authorization pages, click Next without making any changes.
- Click Finish to complete resource application creation.
- Click Activate to activate your client application. The resource server representing the resource is now active.
- On the Details page, provide a name (for example,
Create the Confidential Client Application for Oracle Integration
- Sign in as the identity domain administrator to the Oracle Cloud Infrastructure Console.
- In the navigation pane, click Identity & Security.
- Click Domains.
- Select your compartment.
- Click the identity domain.
- In the navigation pane, click Integrated applications.
- Click Add application.
- Select Confidential Application, then click Launch workflow.
- Enter a name. The remaining fields on this page are optional and can be ignored.
- Click Next.
- In the Client configuration box, select Configure this application as a client now.
- For authorization code, select Refresh token and Authorization code in the Allowed grant types section.
- In the Redirect URL field, enter the
redirect URL of the client application. After user login, this URL is redirected
to with the authorization code. You can specify multiple redirect URLs. This is
useful for development environments in which you have multiple instances, but
only one client application due to licensing issues. For example:
Note:
If you don't know the following information, check with your administrator:
- If your instance is new or upgraded from Oracle Integration Generation 2 Generation 2 to Oracle Integration Generation 2.
- The complete instance URL with the region included (required for new instances).
For Connections… Include the Region as Part of the Redirect URL? Example of Redirect URL to Specify… Created on new Oracle Integration Generation 2 instances Yes. https://OIC_instance_URL.region.ocp.oraclecloud.com/icsapis/agent/oauth/callbackCreated on instances upgraded from Oracle Integration Generation 2 Generation 2 to Oracle Integration Generation 2
No. This applies to both:
- New connections created after the upgrade
- Existing connections that were part of the upgrade
https://OIC_instance_URL.ocp.oraclecloud.com/icsapis/agent/oauth/callbackFor the OAuth authorization code to work, the redirect URI must be set properly.
- Under Resources, click Add
Scope to add appropriate scopes.
If the Oracle Fusion Applications instance is federated with the identity domain, the Oracle Integration cloud service application is listed among the resources for selection. This enables the client application to access Oracle Integration.
- Search for the Oracle Fusion Applications resource application created in Create an Identity Domain Resource Application to Represent the Oracle Fusion Applications Resource.
- Select the resource and click >.
- Select the scope, then click Add.
- Click Next without making changes on the Resource and Web Tier Policy pages.
- On the Authorization page, click Finish.
The Application Added dialog shows the client ID and client secret values.
- Copy and save these values. You need this information when creating
a connection for the OAuth Authorization Code Credentials security policy on the
Connections page.
Note the following details for successfully authenticating your account on the Connections page.
If The... Then... Identity domain safeguarding Oracle Integration and the Oracle Fusion Applications resource application are the same. Log in to Oracle Integration using the local Oracle Fusion Applications user created earlier. You must create a connection and click Provide Consent on the Connections page for authentication to succeed. Identity domain safeguarding Oracle Integration and the Oracle Fusion Applications resource application are different. Log in to Oracle Integration using a general Oracle Integration developer account, create a connection, and click Provide Consent on the Connections page. You need to log in to the Oracle Fusion Applications resource identity domain application using the local Oracle Fusion Applications user account created earlier. - Activate the application.
Resolve Errors That Occur When Clicking Provide Consent
After you configure the OAuth Authorization Code Credentials security policy on the Connections page, you must test your connection.
If you are logged in to Oracle Integration with an Oracle Integration
user account and click Provide Consent to test the OAuth
flow, consent is successful. However, when you test the connection, it fails with an
Unauthorized 401 error.
- Log out of Oracle Integration and log back in with a user account that exists in Oracle Fusion Applications.
- Return to the Connections page and retest the connection.
The connection is successful this time.
Set Up the OAuth Authorization Code Credentials Security Policy with a Non-Oracle Fusion Applications Identity Domain
You must set up trust between Oracle Fusion Applications and an identity domain and create a client application for Oracle Integration to use the OAuth Authorization Code Credentials security policy. Once these tasks are completed, you can successfully configure a connection on the Connections page. Use this option when you are integrating with a non-Oracle Fusion Applications identity domain, such as the Oracle Integration identity domain.
Set Up Trust Between Oracle Fusion Applications and an Identity Domain
- Get the JWK signing certificates from the identity domain of Oracle Integration.
- Get the REST API of the identity domain endpoint that gives
you the signing certificate endpoint. For
example:
/admin/v1/SigningCert/jwkSee All REST Endpoints in REST API for Oracle Identity Cloud Service.
- Copy the endpoint.
- Get the identity domain URL from the Oracle Cloud Infrastructure Console or from the Oracle Integration About menu.
- Add that URL to the front of the signing certificate and use
a tool (for example,
postman) to invoke the REST APIs. For example:https://identity_domain_URL.identity.oraclecloud.com/admin/v1/SigningCert/jwk - Perform a GET call to retrieve the payloads of the
certificates. There are two sections in the payload:
- Identity domain certificate
- Certificate authority (CA) certificate
Examples of the type of response you receive are provided. See Retrieve the Tenant's Signing Certificate in JWK Format.
- Copy both certificate sections into separate files. Note
that the headers and footers in the files must be in the following exact
format to be successfully uploaded to Oracle Fusion
Applications:
-----BEGIN CERTIFICATE----- content_of_certificate . . . . . . -----END CERTIFICATE-----You can validate the certificate. For example:openssl x509 -in IDCS.cert -noout -text
- Get the REST API of the identity domain endpoint that gives
you the signing certificate endpoint. For
example:
- File a service request (SR) with Oracle Fusion Applications Support
that includes the following details:
- SR Summary: Set Up Trust Between Oracle Fusion Applications and OCI Identity Domain
- Category: Login, Logout and SSO
Attach your certificates for upload. You cannot upload the certificates yourself.
- Create a resource application in an Oracle Integration identity domain to represent the Oracle Fusion Applications
resource.
- Log in to the identity domain as the domain administrator.
- In the navigation pane, click Identity & Security.
- Click Domains.
- Select your compartment.
- Click the identity domain.
- In the navigation pane, click Integrated applications.
- Click Add application.
- Select Confidential Application, then click Launch workflow.
- On the Details page, provide a name (for example,
FA Resource), and click Next. - On the Client page, click Next without making changes.
- On the Resources page, click Configure this application as a resource server now.
- Optionally update the value in the Access Token Expiration field.
- Select Is Refresh Token Allowed.
- In the Primary Audience field, add
the Oracle Fusion Applications URL and port. This is the primary
recipient where the token is
processed.
https://FA_URL:443 - In the Scopes section, click Add.
- In the Scope field, enter
/. - In the Description field, enter All.
- Select Requires Consent.
- Click Add, then click Next.
- On the Web Tier Policy and Authorization pages, click Next without making any changes.
- Click Finish to complete resource application creation.
- Click Activate to activate your client application. The resource server representing the resource is now active.
(Optional) Create a Local User
Note:
The following step is required if the Oracle Fusion Applications user is not federated with an identity domain or whichever identity provider you are using.- Create an identity domain local user. Carefully review the
following table to see if you already have a local user.
Scenario Do I Need to Create a Local User? You have an Oracle Fusion Applications user federated with the identity domain that is protecting Oracle Integration. No. You do not need to create the local identity domain Oracle Fusion Applications user. This is because identity domain already has Oracle Fusion Applications users in its repository.
You do not have federation between Oracle Fusion Applications and the identity domain that is protecting Oracle Integration. Yes. You must create the local identity domain Oracle Fusion Applications user that you plan to use with the OAuth setup in Oracle Integration.
The identity domain administrator must create a nonfederated local username in the identity domain that matches the user in Oracle Fusion Applications. If you have already used and invoked Oracle Fusion Applications REST endpoints, you likely already created a user with the necessary roles and accesses to invoke the REST endpoints of Oracle Fusion Applications. This user must be created in the identity domain and have a local user password.
Create the Confidential Client Application for Oracle Integration
- Sign in as the identity domain administrator to the Oracle Cloud Infrastructure Console.
- In the navigation pane, click Identity & Security.
- Click Domains.
- Select your compartment.
- Click the identity domain.
- In the navigation pane, click Integrated applications.
- Click Add application.
- Select Confidential Application, then click Launch workflow.
- Enter a name. The remaining fields on this page are optional and can be ignored.
- Click Next.
- In the Client configuration box, select Configure this application as a client now.
- For authorization code, select Refresh token and Authorization code in the Allowed grant types section.
- In the Redirect URL field, enter the
redirect URL of the client application. After user login, this URL is redirected
to with the authorization code. You can specify multiple redirect URLs. This is
useful for development environments in which you have multiple instances, but
only one client application due to licensing issues. For example:
Note:
If you don't know the following information, check with your administrator:
- If your instance is new or upgraded from Oracle Integration Generation 2 Generation 2 to Oracle Integration Generation 2.
- The complete instance URL with the region included (required for new instances).
For Connections… Include the Region as Part of the Redirect URL? Example of Redirect URL to Specify… Created on new Oracle Integration Generation 2 instances Yes. https://OIC_instance_URL.region.ocp.oraclecloud.com/icsapis/agent/oauth/callbackCreated on instances upgraded from Oracle Integration Generation 2 Generation 2 to Oracle Integration Generation 2
No. This applies to both:
- New connections created after the upgrade
- Existing connections that were part of the upgrade
https://OIC_instance_URL.ocp.oraclecloud.com/icsapis/agent/oauth/callbackFor the OAuth authorization code to work, the redirect URI must be set properly.
- Under Resources, click Add
Scope to add appropriate scopes.
If the Oracle Fusion Applications instance is federated with the identity domain, the Oracle Integration cloud service application is listed among the resources for selection. This enables the client application to access Oracle Integration.
- Search for the Oracle Fusion Applications resource application created in Set Up Trust Between Oracle Fusion Applications and an Identity Domain.
- Select the resource and click >.
- Select the scope, then click Add.
- Click Next without making changes on the Resource and Web Tier Policy pages.
- On the Authorization page, click Finish.
The Application Added dialog shows the client ID and client secret values.
- Copy and save these values. You need this information when creating
a connection for the OAuth Authorization Code Credentials security policy on the
Connections page.
Note the following details for successfully authenticating your account on the Connections page.
If The... Then... Identity domain safeguarding Oracle Integration and the Oracle Fusion Applications resource application are the same. Log in to Oracle Integration using the local Oracle Fusion Applications user created earlier. You must create a connection and click Provide Consent on the Connections page for authentication to succeed. Identity domain safeguarding Oracle Integration and the Oracle Fusion Applications resource application are different. Log in to Oracle Integration using a general Oracle Integration developer account, create a connection, and click Provide Consent on the Connections page. You need to log in to the Oracle Fusion Applications resource identity domain application using the local Oracle Fusion Applications user account created earlier. - Activate the application.
Avoid Potential Errors When Testing Your Connection with a Nonfederated User Account
After you configure the OAuth Authorization Code Credentials security policy on the Connections page, you must test your connection.
If you are logged in to Oracle Integration with an Oracle Integration
user account and click Provide Consent to test the OAuth
flow, consent is successful. However, when you test the connection, it fails with an
Unauthorized 401 error.
- Log out of Oracle Integration and log back in with a user account that exists in Oracle Fusion Applications.
- Return to the Connections page and retest the connection.
The connection is successful this time.
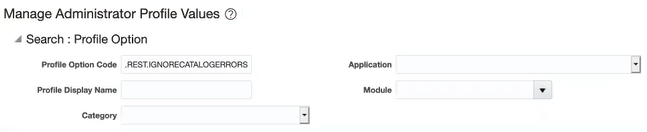
Access the REST Catalog Through the Oracle ERP Cloud Adapter
You must perform the following steps to access the REST catalog through the Oracle ERP Cloud Adapter. This enables you to browse for REST resources on the Operations page of the Adapter Endpoint Configuration Wizard. This also enables Oracle ERP Cloud to skip REST resources when an error is encountered while generating the metadata. Without this, Oracle ERP Cloud generates a partial catalog that results in missing business resources on the Operations page.
Note:
After saving your profile value changes, it takes approximately 30 minutes for the REST resources to be available for selection in the Adapter Endpoint Configuration Wizard.Create Custom Business Events
You can create custom business events in Application Composer that are visible for selection when configuring the Oracle ERP Cloud Adapter as a trigger connection in the Adapter Endpoint Configuration Wizard. You must access Application Composer through the Oracle Fusion Applications user interface. Select ERP and SCM Cloud from the Applications list in Application Composer to create the custom objects and promote them as custom events to be consumed by the Oracle ERP Cloud Adapter.
Note:
Custom business events are supported only for Oracle ERP Cloud custom business objects.See technical note 2535444.1 at My Oracle Support for instructions.
Obtain the Oracle ERP Cloud Service Catalog Service WSDL, Event Catalog URL, or Interface Catalog URL (For Connections Created Prior to 2/18/20)
The steps in this section are only required for existing connections created prior to the initial release of the simplified connections page on 2/18/20. For existing connections, you are prompted to specify a service catalog service WSDL (for accessing and configuring the inbound and outbound adapter to use either business objects or business services) in the ERP Services Catalog WSDL URL field and optionally an event catalog URL (for accessing and configuring the inbound adapter to use event subscriptions) in the ERP Events Catalog URL field and interface catalog URL (for accessing and configuring the outbound endpoint using REST business resources) in the Interface Catalog URL field.
Note:
For new connections created with the initial release of the simplified connections page on 2/18/20, the preconfiguration details described in this section are not required. All WSDLs and URLs are automatically identified for you based on the Oracle ERP Cloud host name that you specify in the ERP Cloud Host field on the Connections page.The following sections describe how to obtain the service catalog service WSDL and event catalog URL:
For Fusion Applications Releases 13 and Later
Obtain the Oracle Fusion Applications Release 13 and later service catalog service WSDLs and event catalog URLs through the following methods.
Obtain the Service Catalog Service WSDL
To obtain the physical endpoint of your instance, perform the following steps:
-
Log in to the Fusion Applications home page. For example:
https://acme.fa.us6.oraclecloud.com/fscmUI/faces/FuseWelcomeWhere
acmeis the system name andus6is the data center. -
Copy
https://acme.fa.us6.oraclecloud.com/and append it withfscmService/ServiceCatalogService?WSDL. For example:https://acme.fs.us2.oraclecloud.com/fscmService/ServiceCatalogService?WSDL
Obtain the Event Catalog URL
Starting in Release 13, you access all Fusion Applications URLs using a consolidated endpoint. You must switch to the new consolidated endpoint that conforms to the following naming pattern:
https://systemName.fa.dcsn.oraclecloud.com/...fa domain, the URL looks as follows:
-
Copy the following URL:
https://acme.fa.us6.oraclecloud.com/ -
Append
soa-infrato the end of the URL:https://acme.fa.us6.oraclecloud.com/soa-infra