Topics:
Get Started with Oracle WebCenter Portal 14c (14.1.2) on Marketplace
Create and View Oracle WebCenter Portal 14c (14.1.2) on Marketplace Instances
Get Started with Oracle WebCenter Portal 14c (14.1.2) on Marketplace
Here’s information about Oracle WebCenter Portal on Marketplace that will help you get started:
About Oracle WebCenter Portal on Marketplace
Oracle WebCenter Portal on Marketplace is provided as a VM-based solution on Oracle Cloud Infrastructure.
Oracle WebCenter Portal on Marketplace is available in two types of Marketplace offerings: Paid and BYOL. See About the License for Oracle WebCenter Portal on Marketplace.
Oracle WebCenter Portal on Marketplace helps customers to provision/set up the environment in few clicks and enables to deliver Portal solutions on cloud.
About the License for Oracle WebCenter Portal on Marketplace
Oracle WebCenter Portal on Marketplace is based on Oracle WebCenter Portal 14c (14.1.2). Oracle WebCenter Portal on Marketplace is available in two types of Marketplace offerings:
Paid: Use the following Oracle WebCenter Portal (Paid) listing to use Universal Credits pricing:
Oracle WebCenter Portal 14c (Paid)
BYOL: Use the Oracle WebCenter Portal (BYOL) listing to Bring Your Own License using your existing Oracle WebCenter Portal 14c (14.1.2) on-premises license, or you can purchase a new license for Oracle WebCenter Portal 14c (14.1.2).
When you activate Oracle WebCenter Portal on Marketplace using the BYOL listing, you are charged only for the Oracle Cloud Infrastructure resources consumed. You must have sufficient supported on-premises licenses as required and specified in the Service Description for Oracle PaaS.
For the processor conversion ratios and license requirements for the BYOL offering, go to the Cloud Service Descriptions page and go to the Cloud Service Description PDF. In particular, note the following conversion ratios for BYOL:
For each supported Processor license, you may activate up to 2 OCPUs of the BYOL Cloud Service.
For every 10 supported Named User Plus licenses, you may activate 1 OCPU of the BYOL Cloud Service.
About Roles and User Accounts
Oracle WebCenter Portal on Marketplace uses roles to control access to tasks and resources. A role assigned to a user gives certain privileges to the user.
Access to Oracle WebCenter Portal on Marketplace is based on the roles and users set up for the Oracle Cloud Infrastructure console. You need OCI Administrator role to provision WebCenter Portal.
For information about how to add user accounts in Oracle Cloud, see:
Add Users to a Cloud Account with Identity Cloud Service in Getting Started with Oracle Cloud.
Managing Oracle Identity Cloud Service Users and Groups in the Oracle Cloud Infrastructure Console in the Oracle Cloud Infrastructure documentation.
Create and View Oracle WebCenter Portal 14c (14.1.2) on Marketplace Instances
The information in this chapter will help you create and view Oracle WebCenter Portal on Marketplace instances.
Before You Begin
Before you begin, you would need to complete the following tasks and prerequisites.
Sign in to Oracle Cloud Infrastructure Console
Complete the following steps to sign in to the Oracle Cloud Infrastructure console.
Go to http://cloud.oracle.com.
Enter your cloud account name and click Next.
Sign in to the Oracle Cloud Infrastructure console:
If your cloud account uses identity domains, sign in to the Oracle Cloud Infrastructure console as a user configured in Oracle Cloud Infrastructure Identity and Access Management (IAM).
Select the domain you normally use to log in to the OCI console.
If your cloud account does not use identity domains, sign in to the Oracle Cloud Infrastructure console as a user federated through Oracle Identity Cloud Service.
Under Single Sign-On (SSO) options, note the identity provider selected in the Identity Provider field and click Continue.
Enter the user name and password provided in the welcome email, and click Sign In. The Oracle Cloud Infrastructure console is shown.
Prerequisites
You'll need to complete the following prerequisites before provisioning the WebCenter Portal stack.
System Requirements [Required]
Generate SSH key pair [Required]
Create a Compartment [Required]
Create Vault and Master Key [Required]
Create Database [Required] - This is not required when the “Quick Start” option is selected.
Create IDCS Application [Required] - This is required only when the ‘Enable Authentication Using Identity Cloud Service’ or ‘Quick Start’ option is selected.
Create the Object Storage Bucket and API Key [Optional] - This is required only for the “Object Storage” is selected for “Content Storage Strategy”.
Configure Dynamic Groups and Policies for Non-Admin Delegated Users [Optional] - This is required only when non-admin user needs to provision the stack.
Setup DNS resolver to resolve Database domain [Optional] - This is required only when VCNs used for Database and WebCenter Stack pre-exist and are different.
After completing the above prerequisites, you can proceed to provision the WebCenter Portal stack.
Note: WebCenter Content is installed when you provision the WebCenter Portal stack.
System Requirements
You require access to the following services to use Oracle WebCenter Portal on OCI.
Identity and Access Management (IAM)
Compute, Network, Block Storage, Block Volume
Vault, Key, Secret
Resource Manager
Database
Load Balancer
Tagging
Make sure you have the following minimum limits for the services in your Oracle Cloud Infrastructure tenancy, and if necessary, request for an increase of a service limit.
| Service | Minimum Limit |
|---|---|
| Identity and Access Management (IAM) Policy | 3 |
| Compute Shape VM.Standard.E4.Flex or VM.Standard.E5.Flex | 4 |
| Virtual Cloud Network | 1 |
| Block Storage | 1 TB |
| Block Volume | 200 GB |
| Vault & Key | 1 |
| Secrets | 5 |
| Load Balancer | Flexible Load Balancer |
In Oracle Cloud Infrastructure Vault (formerly known as Key Management), a standard vault is hosted on a hardware security module (HSM) partition with multiple tenants, and it uses a more cost-efficient, key-based metric for billing purposes. A virtual private vault provides greater isolation and performance by allocating a dedicated partition on HSM. Each type of vault has a separate service limit in your Oracle Cloud Infrastructure tenancy. The limit for secrets spans all the vaults.
See Service Limits in the Oracle Cloud Infrastructure documentation.
Generate SSH key pair
See Generate an SSH Key Pair for WebCenter for generating an SSH key pair.
This SSH key pair will be used for connecting to Bastion and Compute instances after stack execution.
Note: This will be used to create DB and WebCenter Portal nodes.
Create a Compartment
If your tenancy does not already include a compartment for your Oracle WebCenter Portal on Marketplace instances, you can create a new one.
Note: To create a compartment, your administrator must first add the following policy for your group: allow group groupName to manage compartments in tenancy
To create a compartment in Oracle Cloud Infrastructure:
Open the navigation menu and click Identity & Security. Under Identity, click Compartments. A list of the existing compartments in your tenancy is displayed.
Click Create Compartment.
Enter the following:
Name: Specify a name. For example, wcp-compartment. Restrictions for compartment names are: Maximum 100 characters, including letters, numbers, periods, hyphens, and underscores. The name must be unique across all the compartments in your tenancy.
Description: A friendly description.
Parent Compartment: Select the parent compartment where you want the new compartment to be created. When the parent compartment is not selected, the new compartment is created under the root compartment.
Click Create Compartment.
Once the compartment is created, if you are not an administrator, ask your administrator to complete the following steps to grant you the permissions needed to perform the required tasks in the compartment:
Note: You can use any name (wcp-admins, wcp-compartment, and wcp-policy are examples).
Create an IAM group with the user that will do the Marketplace install.
Navigate to Identity & Security, and then Domains.
If not already selected, select the compartment where you’ll install the Marketplace product.
Click the domain where you’ll create the group.
Click Groups.
On the Create group page, provide the following information:
- Name: wcp-admins
- Description: Webcenter Portal Administrators
- Users: Add the user that will do the Marketplace installation.
Click Create.
Create a policy with the permissions to perform the required tasks in the compartment.
Navigate to Identity & Security, and then Policies.
Click Create Policy and provide a name (for example, wcp-policy).
Create a policy with the following statements.
allow group wcp-admins to manage instance-family in compartment wcp-compartment
allow group wcp-admins to manage virtual-network-family in compartment wcp-compartment
allow group wcp-admins to manage volume-family in compartment wcp-compartment
allow group wcp-admins to manage load-balancers in compartment wcp-compartment
allow group wcp-admins to manage orm-family in compartment wcp-compartment
where
wcp-adminsis the group name andwcp-compartmentis the compartment name.
Create Vault and Master Key
Create a Vault
Sign in to the Oracle Cloud Infrastructure Console and search for Vault.
Click Create Vault.
Provide a name and click Create Vault.
Create a Master Key
You'll need to create a master key for the vault.
Open the navigation menu and click Identity & Security and then Vault.
Change the necessary compartment.
Click the already created vault name.
On the left side, click Master Encryption keys and then click Create Key.
Complete the following:
Create In Compartment : Name of the selected compartment
Protection Mode: Software
Name: Specify a name.
For remaining fields, retain the default values.
Click Create Key.
Wait for the status to show green.
Create Database
You can follow the below steps to create a new Oracle Database instance (or you can use an existing database too).
Note: Currently, Autonomous Database Serverless - Transaction Processing, Autonomous Database on Dedicated Exadata Infrastructure, Exadata Database Service on Dedicated Infrastructure, and Base Database are supported. For any additional questions, contact the Oracle Support team.
Note: Oracle WebCenter Portal 14c requires Oracle Database 19c (19.23) or higher. For the latest list of certified databases, refer to the Supported System Configurations information on the Oracle Technology Network.
Complete the following to create a new DB service instance:
Create VCN
Log in to OCI Console, navigate to Networking, then to Virtual Cloud Networks.
Click Create VCN via Wizard.
Click Start VCN Wizard.
VCN name: Provide a name.
Compartment: Specify the compartment in which the VCN needs to be created.
VCN IPv4 CIDR block: Specify IPv4 CIDR block (for example, 10.0.0.0/16).
Select the Use DNS hostnames in this VCN check box.
In the Configure public subnet and Configure private subnet sections, specify the correct CIDR blocks and click Next.
Make sure to create the necessary gateways such as Internet gateway, NAT gateway, and Service gateway.
Click Create. The VCN is created.
Create a New Database
Follow the below OCI documentation links for creating OCI Database resources based on the preferred service.
Base Database (Single Node or RAC) : See Provision a Base Database Service for more information.
Note: The base database should be created with minimum 2 cores/OCPUs.
Autonomous Database Serverless (Transaction Processing) : See Provision an Autonomous Database Service for more information.
Autonomous Database on Dedicated Exadata Infrastructure : See Provision an Autonomous Database on Dedicated Exadata Infrastructure for more information.
Exadata Database Service on Dedicated Infrastructure: See Provision an Exadata Database Service on Dedicated Infrastructure for more information.
Create IDCS Application
An IDCS confidential application is needed to configure the IDCS security provider in Weblogic domain during provisioning.
If you are creating the stack as a private service (Checking Enable Private Service option), then the Identity Domain needs to be homed in the same region where the stack is going to be provisioned. Please ensure this before creating the application.
| Note |
|---|
| There is an alternate option to auto-create the application along with stack creation. If you prefer to choose that, then the provisioning user needs to be granted Identity Domain Administrator role in the domain’s security settings (see Adding Identity Domain Administrators) and the same user needs to create the stack. If you prefer that option, you can skip this requirement and choose Auto-Create Domain App option during stack provisioning. |
Follow the below instructions based on whether OCI Tenancy IAM is with Identity Domains or not.
For OCI accounts where IAM is with Identity Domains (tenancy with IAM domains), complete the following:
Log in to OCI console.
Navigate to Identity & Security, and then Domains.
Select the domain which needs to be used for SSO log-in.
Go to Integrated Applications and click Add application.
Choose Confidential Application and launch the workflow.
On the Add Application Details page, fill the Name and Description fields, and then click Next.
On the Configure OAuth page, select the Configure this application as a client now option under Client configuration section.
In the Authorization section, select the Client credentials check box for the Allowed Grant Types field.
Scroll down and select the Add app roles check box. In the App roles section, add the Identity Domain Administrator role.
Click Next. Leave the default settings for the next page as is and click Finish.
Make a note of the client ID and client secret. These values will be needed when you run the script.
Activate the application.
For OCI accounts where IDCS is not yet migrated to IAM Domains (tenancy without IAM domains), complete the following:
Log in to the IDCS administration console of the federated IDCS.
For example,
https://idcs-abcde.identity.oraclecloud.com/ui/v1/adminconsole.Navigate to Applications. Click + to add an application. Choose Confidential Application in the wizard:
Add a name and a description on the App details page.
Click Next. Select the Configure this application as a client now option.
In the Authorization section, select the Client credentials check box for the Allowed Grant Types field.
In the Grant the client access to Identity Cloud Service Admin APIs section, click Add to add the application roles. You need to add the Identity Domain Administrator role.
Click Next. Leave the default settings for the next pages as is and click Finish.
Make a note of the client ID and client secret. These values will be needed when you run the script.
Activate the application.
Create the Object Storage Bucket and API Key
Create the Object Storage Bucket in OCI
Click the navigation menu in the upper left corner of the page and click Storage.
Click Buckets.
Confirm that you're in the correct compartment and the correct region.
Click Create Bucket on the "Buckets in <compartment name> Compartment" page.
Provide a value for Bucket Name.
Leave the Default Storage Tier set to Standard.
Leave the Encryption set to Encrypt using Oracle managed keys.
Click Create.
See Object Storage Buckets for more information.
Create a New User API Key
Click on your avatar in the upper-right corner of the page.
Click My profile.
In the Resources menu on the left side of the page, click API Keys.
Click Add API Key.
Download the private key by clicking Download private key. The private key will be added to the vault's secret later.
Click Add.
Click Copy to copy the content of the configuration file which has user OCID and fingerprint as this will be required later. Close the dialog.
Create Vault Secrets
Click the vault app created earlier. Create a master encryption key by specifying the compartment, protection mode, name, algorithm, length, and so on in the Create Key section.
Click Secrets on the left side and start adding secrets by specifying the compartment, name, key, secret type template, secret contents, and so on in the Create Secret section.
Required secrets
| Secret Name | Secret Description | Comment |
|---|---|---|
| wcp-admin-password | Secret for WebCenter Portal Admin Password | The Secret Contents field should be populated with the Weblogic password value. The password needs to meet the following password policy: • The password must be of at least 8 characters and maximum 12 characters length. •The password must contain at least one number. •The password must contain at least one small case letter. •The password must contain at least one uppercase letter. •The password must contain at least one special character. •The password should not have more than 3 consecutive character. •The password should not have more than 4 repeated characters. |
| wcp-schema-password | Secret for WebCenter Portal schema password. | The password needs to meet the following password policy: •The password must start with a letter. •The password must contain at least two digits. •The password must contain at least two uppercase letters. •The password must contain at least two lowercase letters. •The password must contain at least two special characters from the set [$#_]. •The password must be of at least 15 characters and maximum 30 characters in length. Example: OCI#db#456789123 |
Database System (Required)
Note: Required only when “Database System” is selected for “Database Strategy”.
| Secret Name | Secret Description | Comment |
|---|---|---|
| db-system-sys-password | Secret for DB System SYS Password | SYS user password of DB created in the Create a New Database section should be used in the Secret Contents field. Required only if chosen database service is Base Database. |
| db-system-ssh-private-key | Secret for DB System SSH private key | The Secret Contents field should be populated with the passphrase of private key value that was used to create DB in the Create a New Database section. Required only if chosen database service is Base Database. |
| db-system-ssh-private-key-passphrase | Secret for DB System SSH private key’s passphrase | The Secret Contents field should be populated with the private key’s passphrase value that was used to create DB in the Create a New Database section. Required only if chosen database service is Base Database and Key is passphrase protected. |
Exadata Database (Optional)
Note: Required only when “Exadata Database” is selected for “Database Strategy”
| Secret Name | Secret Description | Comment |
|---|---|---|
| exadata-db-sys-password | Secret for Exadata Database SYS Password | SYS user password of Exadata database created in the Create a New Database section should be used in the Secret Contents field. Required only if chosen database service is Exadata Database Service on Dedicated Infrastructure. |
| exadata-db-ssh-private-key | Secret for Exadata Database SSH private key | The Secret Contents field should be populated with the private key value that was used to create DB in the Create a New Database section. Required only if chosen database service is Exadata Database Service on Dedicated Infrastructure. |
| exadata-db-ssh-private-key-passphrase | Secret for Exadata Database SSH private key’s passphrase | The Secret Contents field should be populated with the private key’s passphrase value that was used to create DB in the Create a New Database section. Required only if chosen database service is Exadata Database Service on Dedicated Infrastructure and Key is passphrase protected. |
Autonomous Transaction Processing Database (Optional)
Note: Required only when “Autonomous Transaction Processing Database” is selected for “Database Strategy”.
| Secret Name | Secret Description | Comment |
|---|---|---|
| atp-db-password | Secret for Autonomous Database Admin Password | Admin user password of Autonomous database created in the Create a New Database section should be used in the Secret Contents field. Required only if chosen database service is Autonomous Database Serverless or Autonomous Database on Dedicated Exadata Infrastructure. |
IDCS secrets (Optional)
Note: Required only when “Enable Authentication Using Identity Cloud Service” option is selected.
| Secret Name | Secret Description | Comment |
|---|---|---|
| idcs-client-secret | Secret for IDCS Client secret | The Secret Contents field should be populated with the Client Secret value that was noted when the IDCS Confidential App was created in the IDCS section. |
Object Storage (Optional)
Note: This is required only when “object storage” is selected for the “Content Storage Strategy”.
| Secret Name | Secret Description | Comment |
|---|---|---|
| oci-user-private-key | Secret for user API private key | The Secret Contents field should be populated with the private key value downloaded earlier in the Create a New User API Key section. |
Provision WebCenter Portal Stack
You can provision Oracle WebCenter Portal on a Marketplace instance in a selected compartment in Oracle Cloud Infrastructure.
| Note |
|---|
| In the Stack Configuration section, you can select the Quick Start check box to quickly provision a WebCenter environment using default values. See Quick Start for WebCenter for more information. |
To provision Oracle WebCenter Portal on a Marketplace instance:
Navigate to the WebCenter Portal listing on Marketplace by direct URL or by browsing in Oracle Cloud Infrastructure.
Using direct URL:
In your browser, enter https://cloudmarketplace.oracle.com/marketplace/en_US/homePage.jspx?tag=WebCenter+Portal.
The Marketplace listings for WebCenter Portal are displayed.
Click the title of the listing you want to use. The landing page of that listing is displayed.
Click Get App.
Select your Oracle Cloud Infrastructure region and click Sign In.
By browsing:
Open the navigation menu and click Marketplace. Under Marketplace, click All Applications.
In the Marketplace search field, enter WebCenter Portal. The Marketplace listings for WebCenter Portal are displayed.
Click the title of the listing you want to use and review the information on the Overview page.
Accept the terms and restrictions, and then click Launch Stack. The Create Stack wizard is displayed.
Provide information about the stack for the instance.
Stack information:
Enter name and description.
Create in Compartment: Select the compartment.
Terraform version: Specify the Terraform version and click Next.
Configure variables:
Stack Configuration
Resource Name Prefix: Enter a prefix (for example, WCP). The name of all compute and network resources will begin with this prefix. It must begin with a letter and it can contain only letters or numbers.
SSH Public key: Provide the SSH public key (created in Generate SSH key pair).
Quick Start: Select this check box to quickly provision a WebCenter Portal environment using default values. See Quick Start for WebCenter for more information.
OCI Policies: Select this check box if you need the stack to create policies to provision WebCenter Portal resources, configure Database Network, and read Vault Secrets. Deselecting this option is for Advanced users only. See Configure Dynamic Groups and Policies for Non-Admin Delegated Users for more information.
Enable Authentication Using Identity Cloud Service: Select this check box if you need to use Identity Cloud Service (IDCS) as the security provider in WebCenter Content. If not selected, the local Weblogic identity store will be used.
Enable Private Service: Select this check box if you need to provision service in private subnet for Fast Connect usage.
Secrets Key Management
OCI Vault compartment: Select the compartment for OCI vault.
Use pre-created OCI Vault Secrets: Select this check box if you need to use pre-created KMS Secrets. If not selected, a new KMS secret and KMS encryption key will be created in the given OCI vault. If selected, you need to pre-create vault secrets as mentioned in Create Vault Secrets.
OCI Vault to store secrets: Select the OCI vault to store new KMS secret. This option is visible when the Use pre-created OCI Vault Secrets check box is not selected.
OCI Vault to fetch secrets: Select the OCI vault to fetch pre-created KMS secrets. This option is visible when the Use pre-created OCI Vault Secrets check box is selected.
Virtual Cloud Network
If you're using an existing VCN, complete the following:
Network Compartment: Select the compartment you created earlier.
Existing WebCenter Portal Virtual Cloud Network: Select the VCN provisioned for WebCenter Portal.
If you need to use a new VCN, then select the Create the Virtual Cloud Network check box and complete the following:
Network Compartment: Select the compartment you created earlier.
Virtual Cloud Network Name: Specify a name for the new VCN to be created for this service.
Virtual Cloud Network CIDR: Specify a CIDR to assign to the new VCN.
Content Storage
Content Storage Strategy: Select a content storage strategy from the drop-down list. The available options are Database, File System, and Object Storage.
If you selected Object Storage as the content storage strategy, complete the following:
Object Storage Compartment: Select the compartment where the bucket was created.
Bucket Name: Specify the bucket name which you created earlier.
User OCID: This will be pre-populated with the current user's OCID. If you are using a different user for creating the API key, specify the user OCID of that user.
Public Key Fingerprint: Specify the fingerprint from the configuration file (that you copied when you created the user API key as part of the prerequisites).
OCI User Private Key: Upload the user API private key. This is applicable only if the Use pre-created OCI Vault Secrets check box is not selected.
Secret for OCI User Private Key: Select the secret for the user API private key. This is applicable only if the Use pre-created OCI Vault Secrets check box is selected.
Database
Database Strategy: Select the type of database to use for provisioning. The supported databases are: Database System, Autonomous Transaction Processing Database, and Exadata Database.
If you selected Autonomous Transaction Processing Database as the Database Strategy, then complete the following that are displayed:
Select the value for Autonomous Database compartment.
Select the value for Autonomous Database.
Autonomous Database Admin Password Secret Compartment: Choose the compartment that holds the secret for the Autonomous Database Admin Password.
Secret for Autonomous Database Admin Password: Select the secret for Autonomous Database Admin Password.
If you selected Database System as the Database Strategy, then complete the following that are displayed:
Select the value for DB System compartment.
Select the value for DB System Instance Name.
PDB name: Provide the PDB name of the DB system.
DB System PDB User: Leave the value 'sys' as is. Do not change this user name.
If you have not selected Use pre-created OCI Vault Secrets, then complete the following that are displayed.
DB System Password: Provide the value of DB System password.
DB System SSH Private key: Upload the DB System SSH Private key which is created without passphrase.
Passphrase needed for DB System SSH Private key: Check if the private key is passphrase protected.
Passphrase for DB System SSH Private key: Provide the value for DB System SSH key passphrase.
If you selected Use pre-created OCI Vault Secrets, then complete the following that are displayed.
Secret for DB System Password: Select the secret for DB system password. When defining the secret key, you must have specified a user-friendly name for each secret. Use the same name here so that it is easy.
Secret for DB System SSH Private key: Select the secret for DB System SSH private key.
Passphrase needed for DB System SSH Private key: Check if the private key is passphrase protected.
Secret for DB System SSH Private key passphrase: Select the secret for DB System SSH private key’s passphrase.
If you selected Exadata Database as the Database Strategy, then complete the following that are displayed:
Select the value for Exadata Database compartment.
Exadata DB Home OCID: Provide the OCID of Exadata DB Home.
Select the value for Exadata Database.
Exadata Database PDB name: Provide the PDB name of the Exadata database.
Exadata Database PDB User: Leave the value 'sys' as is. Do not change this user name.
If you have not selected Use pre-created OCI Vault Secrets, then complete the following that are displayed.
Exadata Database Password: Provide the value of the PDB user password for the Exadata database.
Exadata Database SSH Private key: Upload the Exadata database SSH Private key created without passphrase.
Passphrase needed for Exadata Database SSH Private key: Check if the private key is passphrase protected.
Passphrase for Exadata Database SSH Private key: Provide the value for Exadata Database SSH key passphrase.
If you selected Use pre-created OCI Vault Secrets, then complete the following that are displayed.
Exadata Database Password Secret Compartment: Choose the compartment that holds the secret for the Exadata database password.
Secret for Exadata Database Password: Select the secret for Exadata database password. When defining the secret key, you must have specified a user-friendly name for each secret. Use the same name here so that it is easy.
Exadata Database SSH Private key Secret Compartment: Choose the compartment that holds the secret for the Exadata Database SSH private key.
Secret for Exadata Database SSH Private key: Select the secret for Exadata Database SSH private key.
Passphrase needed for Exadata Database SSH Private key: Check if the private key is passphrase protected.
Secret for Exadata Database SSH Private key passphrase: Select the secret for Exadata Database SSH private key’s passphrase.
Database Schema Strategy: Select the database schema strategy to use for provisioning. The supported schema strategies are: Create New Database Schemas and Use existing Database Schemas. The option Create New Database Schemas will create new database schemas with the given schema prefix. The option Use existing Database Schemas will try to find and use existing database schemas with the given schema prefix and provisioning will fail if database schemas matching the given schema prefix don’t pre-exist.
Database Schema Prefix for WebCenter Content: Provide a value for database schema prefix. It should not be longer than 12 characters and should start with a letter followed by uppercase alphabets and numeric characters.
Database Schema Prefix for WebCenter Portal: Provide a value for database schema prefix. It should not be longer than 12 characters and should start with a letter followed by uppercase alphabets and numeric characters.
Bastion Instance:
If you're using an existing VCN, complete the following:
Bastion Strategy: Select a bastion strategy from the drop-down list. The available options are Create New Bastion Instance, and Use Existing Bastion Instance.
If you selected Create New Bastion Instance as the Bastion Strategy, then complete the following that are displayed:
Existing Subnet for Bastion Host: Select an existing public subnet to use for a Bastion compute instance.
Bastion Host Shape: Select the appropriate Bastion host shape (keep the default value).
If you selected Use Existing Bastion Instance as the Bastion Strategy, then complete the following that are displayed:
Public IP of Bastion Instance: Provide the public IP of existing Bastion and make sure it is reachable for new WebCenter compute instances.
SSH Private Key Bastion Instance: Select the appropriate SSH Private key to access the bastion instance. This private key should not contain passphrase.
WebCenter Portal Compute Instance:
Compute Shape: Select the appropriate compute shape.
OCPU count: Select the OCPU count. The default value is 2.
If you're using an existing VCN, complete the following:
Existing Subnet for WebCenter Portal Compute Instances: Select an existing subnet to use for WebCenter Portal compute instances.
Node Count: Specify the node count. The default value is 2.
WebCenter Content Compute Instance:
- Compute Shape: Select the appropriate compute shape.
File System:
Use Existing File System: Select this check box to use an existing File System and Mount Target.
If selected, you will need to select the compartment and availability domain of the existing File System and provide the File System OCID and Mount Target OCID. The Mount Target must have security rules configured to allow traffic to the chosen VCN CIDR. See Configuring VCN Security Rules for File Storage.
File System Compartment: Choose the compartment where the WebCenter Content stack will be created.
File System Availability Domain: Select the Availability Domain.
Existing Subnet for Mount Target: Select an existing subnet to use for mount target.
Load Balancer:
If you're using an existing VCN, complete the following:
Existing Subnet for Load Balancer: Select an existing subnet to use for the load balancer.
Provide the value for Minimum Bandwidth for Flexible Load Balancer.
Provide the value for Maximum Bandwidth for Flexible Load Balancer.
Identity Domain:
Auto-Create Identity Domain App: If this option is selected, then a new IDCS App will be created during stack provisioning. It requires the provisioning user to be granted Identity Domain Administrator role in the selected domain. If this is not feasible and IDCS application is already created as part of pre-requisites, this option can be deselected.
If you are creating the stack as a private service (Checking Enable Private Service option), then the Identity Domain needs to be homed in the same region where the stack is going to be provisioned.
If you selected Auto-Create Identity Domain App option, then complete the following that are displayed:
Identity Domain Compartment: Select the compartment of identity domain.
Identity Domain Name: Provide the name of identity domain.
Identity Domain Username: Provide the value for IDCS username who will be configured as the product administrator.
If you deselected Auto-Create Identity Domain App option, then complete the following that are displayed:
Identity Domain URL: Provide the value for IDCS domain URL.
Identity Domain Username: Provide the value for IDCS username who will be configured as the product administrator.
Identity Client ID: Provide the value for IDCS Client ID created in Prerequisites.
Identity Client Secret: Provide the value for IDCS Client Secret. This is applicable only if the Use pre-created OCI Vault Secrets check box is not selected.
Secret for the Identity Client Secret: Select the secret for the IDCS client secret. This is applicable only if the Use pre-created OCI Vault Secrets check box is selected.
WebCenter Portal WebLogic Domain Configuration:
- WebCenter Portal Admin User Name: Leave the value 'weblogic' as is.
If you have not selected Use pre-created OCI Vault Secrets, then complete the following that are displayed.
WebCenter Portal Admin Password: Provide the value for WebCenter Portal Admin password.
WebCenter Portal Schema Password: Provide the value for WebCenter Portal Schema password.
If you have selected Use pre-created OCI Vault Secrets, then complete the following that are displayed.
WebCenter Portal Admin Secret Compartment: Choose the compartment that holds the secret for the WebCenter Portal Server administrator password.
Secret for WebCenter Portal Admin Password: Select the secret for WebCenter Portal administrator password.
WebCenter Portal Schema Password Secret Compartment: Choose the compartment that holds the secret for the WebCenter Portal schema password.
Secret for the WebCenter Portal Schema Password: Select the secret for the WebCenter Portal schema password.
Click Next. Review all the configuration variables and then select the Run apply check box under Run apply on the created stack section. Click Create. 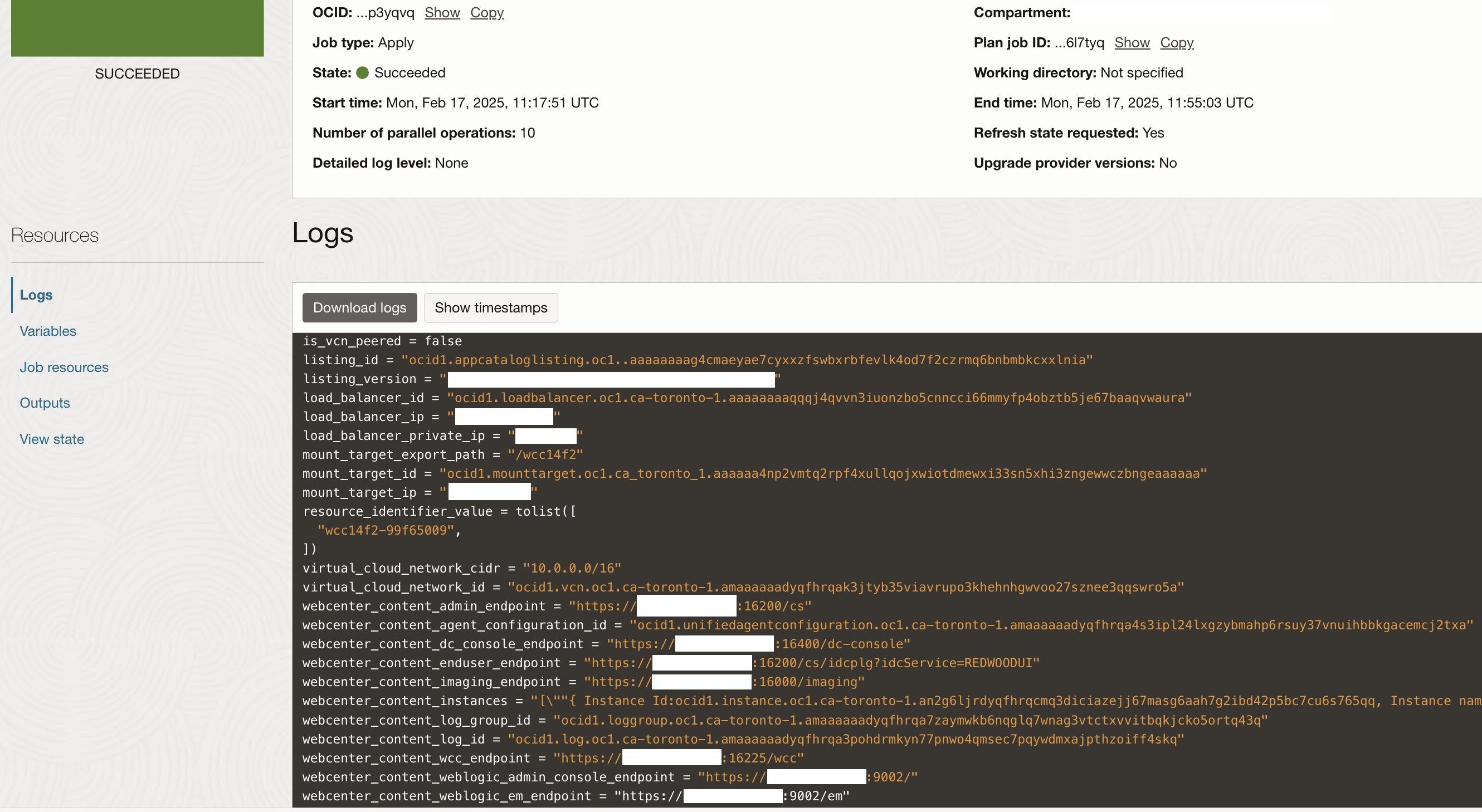
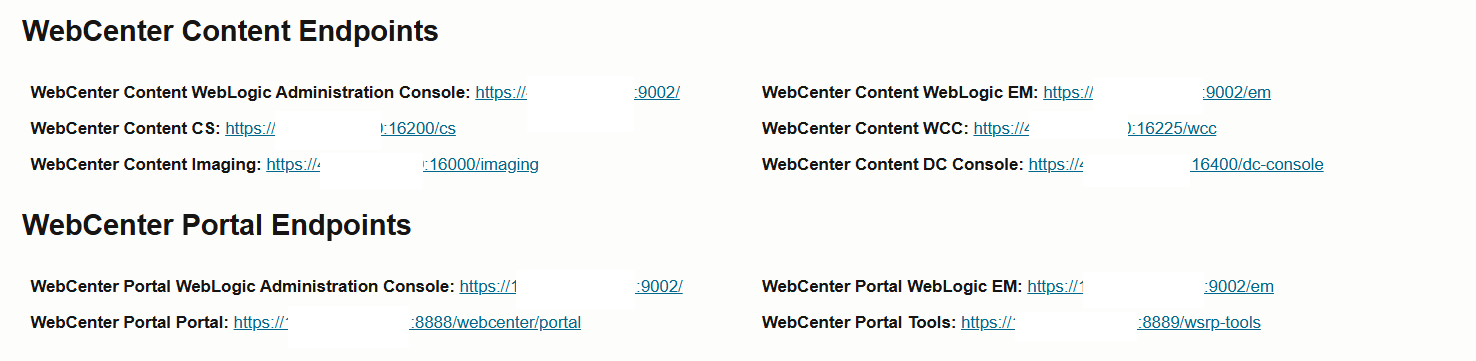
WebCenter Portal Endpoints
If everything goes as expected, then navigate to the WebCenter Portal stack and click the Application Information tab. You'll see all the provisioned end points for the services under sections WebCenter Content Endpoints and WebCenter Portal Endpoints:
WebCenter Content WebLogic Administration Console:
"https://<lb-host-IP>:9002/"WebCenter Content WebLogic EM:
"https://<lb-host-IP>:9002/em"WebCenter Content Admin Endpoint:
"https://<lb-host-IP>:16200/cs"WebCenter Content End User Endpoint:
"https://<lb-host-IP>:16200/cs/idcplg?idcService=REDWOODUI"WebCenter Content WCC:
"https://<lb-host-IP>:16225/wcc"WebCenter Content Imaging:
"https://<lb-host-IP>:16000/imaging"WebCenter Content DC Console:
"https://<lb-host-IP>:16400/dc-console"WebCenter Portal WebLogic Administration Console:
"https://<lb-host-IP>:9002/"WebCenter Portal WebLogic EM:
"https://<lb-host-IP>:9002/em"WebCenter Portal Portal:
"https://<lb-host-IP>:8888/webcenter/portal"WebCenter Portal Tools:
"https://<lb-host-IP>:8889/wsrp-tools"
To navigate to the WebCenter Portal stack:
In the side menu, select Developer Services, Resource Manager, and then Stacks.
Select your compartment and click the name of the WebCenter Portal stack you created.
If something goes wrong or if for any reason you want to do a clean-up of all the resources that were provisioned as part of the WebCenter Portal deployment, use Destroy Job to do the clean-up.
Additional Steps for Stack Provisioned with a Self-Signed Certificate
If you provisioned the WebCenter Portal stack with a self-signed certificate, then you might encounter issues when trying to upload documents from WebCenter Portal. The upload button might be in a frozen state and will not work, hence the pop-up screen will not be shown. To resolve this issue, complete the following steps.
In the browser, open Developer Tools using Ctrl + Shift + I (Windows) or Option + ⌘ + I (Mac) and click the Network tab to see the web traffic.
Note: For Safari browser, navigate to Settings, Advanced tab, and then to Show features for web developers (Enable) and then press Option + ⌘ + C to open Developer Tools and then switch to the Network tab.
Refresh the browser tab in which WebCenter Portal was accessed. Navigate to Home Portal and click the Documents page.
Press Ctrl + Shift + R (Windows) or ⌘ +Shift + R (Mac) to do a hard refresh. In the web traffic, look for a URL that is similar to
https://<WebCenter Content host>:16200/cs/idcplg?IdcService=GET_COAO_JSFor Safari browser, Option + ⌘ + R can be used to do a hard refresh.
Copy the URL for GET_COAO_JS IdcService and open it in a new browser tab. Accept the certificate risk to get the response.
Refresh the browser tab in which WebCenter Portal was accessed. Navigate to Home Portal, click the Documents page and click the Upload button to see a pop-up screen for Document Upload in the browser.
Note: The above steps need to be completed by all users (for each new browser one time) if users need to resolve the specified issue and upload files using WebCenter Portal Documents Upload UI.
Note: The specified issue with the upload button is not encountered when a CA signed certificate is used.
Weblogic Remote Console
In 14.1.2, Weblogic Administration Console will be accessible via Weblogic Remote Console. You need to install and setup Weblogic Remote Console Desktop Application.
Follow the Installation steps as described in Install Desktop WebLogic Remote Console
Create and connect to an Admin Server Provider Connection as described in Connect to an Administration Server
For Provider type you will need to select: Add Admin Server Connection Provider.
For the connection URL, use the WebCenter Portal/Content WebLogic Administration Console endpoint from the stack’s Application Information tab under the section WebCenter Portal Endpoints. See WebCenter Portal Endpoints
Troubleshoot
This chapter describes common problems that you might encounter and also provides information that can be helpful with the troubleshooting process.
Issue: Provisioning failed
Description
If you encountered a failure when trying to provision WebCenter Portal, do the following to see the logs which might help in troubleshooting:
Log in to bastion host.
From bastion host perform ssh to wls-1 VM. For example:
ssh -I <private key> opc@<IP Address of wls-1 VM>sudo su – oraclecd /u01/data/domains/logsvi provisioning.log
Issue: Documents tool is currently unavailable
Description
If you encounter a failure when trying to use the Documents tool in WebCenter Portal and see a message stating Documents tool is currently unavailable as there is no default content repository connection, then do the following to see the configuration which might help in troubleshooting:
Log in to bastion host.
From the bastion host, perform ssh to wcp-wls-1 VM. For example:
ssh -I <private key> opc@<IP Address of wls-1 VM of WebCenter Portal>sudo su – oracleRun the wlst.sh script and connect to the Admin server using the command below (after updating the command)
$ORACLE_HOME/oracle_common/common/bin/wlst.sh connect('weblogic server user name', '<weblogic server password>', 't3s://<VM's private IP>:9002')Once connected, run the below commands to verify the content server connection information.
listContentServerConnections(appName='webcenter', verbose=true, server='WC_Portal_server1') listContentServerProperties(appName='webcenter', server='WC_Portal_server1')After running the above commands, if you see a text in the output stating Please check whether the content server properties have been set or not. Invalid RIDC connection. Drop and recreate the content server connection wccConnection, then, run the below command in the same WLST session.
setContentServerProperties(appName='webcenter', portalServerIdentifier='/webcenterPortal1', securityGroup='webcenterPortal1', adminUserName='sysadmin', server='WC_Portal_server1')Restart all the WebCenter Portal managed servers in a sequential manner using the Oracle WebLogic Server administration console.
Issue: Document upload from WebCenter Portal or WCC UI is not working
Description
If you encountered a failure when trying to upload a document from WebCenter Portal or using WebCenter Content UI, do the following to see the configuration (which might help in troubleshooting):
Log in to WebCenter Content as an administrator.
Navigate to Administration and then to Configuration for wcc****.
Check if Search Engine, Index Engine Name, and Active Index show as:
Search Engine: ORACLETEXTSEARCHIndex Engine Name: ORACLETEXTSEARCHActive Index: ots1If Search Engine, Index Engine Name, and Active Index do not show the values specified above, see Provision WebCenter Portal Stack section to configure the full-text search engine.
Navigate to Administration and then to Admin Actions.
Check the state and status for Automatic Update Cycle and Collection Rebuild Cycle. If it does not show the state as Idle and status as Finished, then:
- Click cancel and wait for sometime.
- Then, click start and wait till you see Progress Message: Finished indexing.
If you have further issues, raise a support ticket in My Oracle Support and attach logs. You can collect logs using the package logs tool described in Package Logs for Troubleshooting.
Appendix
Configure Elastic Search in Oracle WebCenter Portal
Learn how you can configure Elastic Search to index and search objects in the Marketplace WebCenter Portal instance.
Create a crawl user
Log in to the Oracle WebLogic Server Administration Remote Console.
Click on Security Tree button.
Expand Realms → myrealm → Authentication Providers → DefaultAuthenticator
Click on User and Right Pane click on + New button.
Add a user by providing a name (for example, wccrawladmin) and a password. Note down the name and password for future use.
Note For 14.1.2 release use a password meeting below requirements -
Must contain at least 1 lowercase character
Must contain at least 1 uppercase character
Must contain at least 1 numeric character
Must contain at least 1 special character
Does not contain spaces
Must contain at least 8 characters and Maximum 12 characters
Install Elasticsearch
Elasticsearch can be installed as either a single server set-up or a cluster set-up (with a minimum of three servers).
To install a single server set-up, complete the following steps:
Log in to the WebCenter Portal machine as an Oracle user and run the following commands:
sudo su - oracle export JAVA_HOME=/u01/jdk/ export ES_JAVA_HOME="/u01/jdk" export PATH=$JAVA_HOME/bin:$PATH export ORACLE_HOME=/u01/app/oracle/middleware export ELASTIC_SEARCH_HOME=/u01/app/oracle/middleware/wcportal/es unset -f $(env | grep -oP "^BASH_FUNC_\K([^%]*)")Download and extract the Elasticsearch binary file.
cd $ELASTIC_SEARCH_HOME wget https://artifacts.elastic.co/downloads/elasticsearch/elasticsearch-7.17.28-linux-x86_64.tar.gz tar -zxvf elasticsearch-7.17.28-linux-x86_64.tar.gz cd elasticsearch-7.17.28/ mv * .. cd .. rm -rf elasticsearch-7.17.28 elasticsearch-7.17.28-linux-x86_64.tar.gzEdit secureES.properties and update the following properties:
vi $ORACLE_HOME/wcportal/es/secureES.propertiesSEARCH_APP_USER=wccrawladmin ELASTIC_SEARCH_NODE_NAME=<compute host name> ELASTIC_SEARCH_HOME=/u01/app/oracle/middleware/wcportal/es ELASTIC_SEARCH_PRIMARY_HOST=<fqdn compute host name obtained via hostname -f>Install the elastic search server using the following command:
$ORACLE_HOME/oracle_common/common/bin/wlst.sh $ORACLE_HOME/wcportal/es/secureESNode.py $ORACLE_HOME/wcportal/es/secureES.propertiesThe following is the sample output for the successful installation on Linux:
Initializing WebLogic Scripting Tool (WLST) ... Welcome to WebLogic Server Administration Scripting Shell Type help() for help on available commands Please provide a password for search application user [username = wccrawladmin]: Please provide a password for certificate 'node-certificate.p12': Generating node certificate for secured communication... Node certificate generated and password added to elasticsearch keystore successfully. Successfully updated the elasticseach.yml file Creating the user wccrawladmin in Elasticsearch server... Starting elastic search server % Total % Received % Xferd Average Speed Time Time Time Current Dload Upload Total Spent Left Speed 100 82 100 23 100 59 15 39 0:00:01 0:00:01 --:--:-- 39 Stopped elastic search server The user wccrawladmin is created successfully. Starting elastic search server Elasticsearch server security configuration is complete.After the successful installation, verify that Elasticsearch is configured properly.
curl -v -u 'wccrawladmin:<wccrawladmin-password>' 0.0.0.0:9200 Sample output curl -v -u 'wccrawladmin:Dummypass#12' 0.0.0.0:9200 < HTTP/1.1 200 OK < X-elastic-product: Elasticsearch < content-type: application/json; charset=UTF-8 < content-length: 591 < { "name" : "dev-wcp-wls-1", "cluster_name" : "dev-wcp-wls-1.wccsubnet1642po.wccvcn.oraclevcn.com", "cluster_uuid" : "noLcCjSDT5mG1HV9OVXTpA", "version" : { "number" : "7.17.28", "build_flavor" : "default", "build_type" : "tar", "build_hash" : "139cb5a961d8de68b8e02c45cc47f5289a3623af", "build_date" : "2025-02-20T09:05:31.349013687Z", "build_snapshot" : false, "lucene_version" : "8.11.3", "minimum_wire_compatibility_version" : "6.8.0", "minimum_index_compatibility_version" : "6.0.0-beta1" }, "tagline" : "You Know, for Search" }
Managing Elasticsearch
You can start/stop Elasticsearch with the following commands:
export ELASTIC_SEARCH_HOME=/u01/app/oracle/middleware/wcportal/es cd $ELASTIC_SEARCH_HOME/bin; ./elasticsearch -d -p pidLog messages can be found in the $ELASTIC_SEARCH_HOME/logs/ directory.
To shut down Elasticsearch, kill the process
ps -ef| grep elasticsearch kill -9 <pid-from-previous-command>
Configure WebCenter Portal for Elasticsearch
To configure WebCenter Portal for search, you need to configure the connection between WebCenter Portal and Elasticsearch.
Navigate to your Oracle home directory and invoke the WLST script to run the following command for creating a search connection.
export ORACLE_HOME=/u01/app/oracle/middleware $ORACLE_HOME/oracle_common/common/bin/wlst.sh connect('weblogic', '<weblogic-password>', 't3s://<vm's private ip>:9002') createSearchConnection(appName='webcenter',name='webcenter-es', url='http://<wcp-es-machine-ip>:9200', indexAliasName='webcenter_portal', appUser='wccrawladmin', appPassword='<wcccrawladmin's password>', server='WC_Portal_server1') Example:- $ORACLE_HOME/oracle_common/common/bin/wlst.sh connect('weblogic', 'Welcome1#123', 't3s://dev-wcp-wls-1:9002') createSearchConnection(appName='webcenter',name='webcenter-es', url='http://dev-wcp-wls-1:9200', indexAliasName='webcenter_portal', appUser='wccrawladmin', appPassword='Dummypass#12', server='WC_Portal_server1')Note: where wcp-es-machine-ip is the IP address of the host where elastic search server is installed.
Restart all the Webcenter Portal managed servers.
To rebuild and update the search index in Oracle WebCenter Content:
- Log in to Oracle WebCenter Content server as a system administrator.
- On the Oracle WebCenter Content home page, expand Administration and select Admin Applets.
- On the Administration Applets page, click Repository Manager.
- On the Repository Manager page, click the Indexer tab.
- Under Collection Rebuild cycle section, click Start. In the dialog, deselect the Use fast rebuild option and then click OK to proceed.
For other optional advanced configurations, see this documentation.
Create a Portal Crawl Source
To create a crawl source to crawl objects such as lists, page metadata, page content (contents of HTML, text, and styled text components), portals, and profiles:
On the Settings page in WebCenter Portal, click Tools and Services or enter the following URL in your browser to navigate directly to the Tools and Services pages: http://host:port/webcenter/portal/admin/settings/tools
Click the icon for Search to open the Search Settings page.
On the Scheduler tab, select the Portal crawl source and click Edit.
On the Edit Portal Crawl Source page, modify the following source parameters as needed:
Maximum number of connection attempts: Maximum number of connection attempts to access the configuration URL. Choose a number from 2 to 10.
Configuration URL: URL of the RSS crawl servlet. For example: http://<WebCenter Portal host>:<port>/rsscrawl or http://<WebCenter Portal-VM-IP>:<port>/rsscrawl.
Note: In case of HTTPS-based URL for WebCenter Portal, it should be a valid domain host with updated DNS entry and CA-signed certificate.
Enter the credentials for the WebCenter Portal crawl administrator.
Click Test to test the connection.
Click Save and Close to save the changes.
Configure OCI Search Service with OpenSearch in Oracle WebCenter Portal
Learn how you can configure OCI Search Service with OpenSearch to index and search objects in the Marketplace WebCenter Portal instance.
Prerequisites
Ensure the following requirements:
Get the OCI tenancy details.
Create the required service policies in the OCI Console, tailoring them to your needs. For example, provide the compartment OCID.
Note: For new stack creation, the following working policies will be added automatically if the OCI Policies check box is selected.
The working policies are:
Allow service opensearch to manage vcns in compartment id <stack-compartment-ocid> Allow service opensearch to manage vnics in compartment id <stack-compartment-ocid> Allow service opensearch to use subnets in compartment id <stack-compartment-ocid> Allow service opensearch to use network-security-groups in compartment id <stack-compartment-ocid>
Create Open Search Cluster
Open the OCI Console navigation menu. Click Databases, OpenSearch, and then click Clusters. Then, choose the stack compartment where you want to create the cluster and click Create cluster.
Provide <stack-name>-cluster as the name.
On the Configure security page, enter a user name (for example, wccrawladmin) and password (for example, Dummypass#12).
Note For 14.1.2 release use a password meeting below requirements -
Must contain at least 1 lowercase character
Must contain at least 1 uppercase character
Must contain at least 1 numeric character
Must contain at least 1 special character
Does not contain spaces
Must contain at least 8 characters and Maximum 12 charactersNote down the name and password for future use. Click Next.
Choose the cluster sizing, and then click Next.
In the Configure Networking wizard, select the stack VCN you created and then select the Private WebCenter Portal subnet.
Click Next. After the cluster creation, in the Cluster details page, note the API endpoints and the IP addresses which you can alternatively use.
Note: If WebCenter Portal deployment is configured with IDCS SAML SSO, then same search cluster user (for example, wccrawladmin) needs to be created in the IDCS domain used for the stack. For more information about how you can create an IDCS user, see Create IDCS Users.
Update VCN Security Lists
- Open the OCI Console navigation menu. Click Networking and then Virtual Cloud Networks.
- Change the compartment as your stack compartment and click on your stack-related VCN.
- Click on the private subnet for the WebCenter compute node typically named as <stack-name>-wcp-subnet.
- On the left pane, click Security Lists and add the below rule to the security list for this subnet.
- Stateless: Leave this deselected.
- Source Type: CIDR
- Source CIDR: <stack-vcn-cidr>
- IP Protocol : TCP
- Source Port Range: Leave this empty which indicates All
- Destination Port Range: 9200
- Description: Ingress rule for open search port
Configure WebCenter Portal for Search
To configure WebCenter Portal for search, complete the following steps:
Log in to bastion host.
From bastion host, perform ssh to WebCenter Portal wls-1 VM.
For example:
ssh -I <private key> opc@<IP Address of wcp-wls-1 VM>sudo su - oracleNavigate to lcm scripts directory.
cd /u01/scripts/lcm/shRun the below command.
sh configure_open_search_wcp.sh -u <open-search-cluster-username> -p <open-search-cluster-user-password> -o <open-search-api-endpoint>The following example shows how to run the script.
sh configure_open_search_wcp.sh -u wccrawladmin -p Dummypass#12 -o https://amaaaaaadyqfhrqamqmjwmyixdirchld2luer7vtp6xiqg6gzse6w2vn5g5a.opensearch.ca-toronto-1.oci.oraclecloud.com:9200To rebuild and update the search index in Oracle WebCenter Content:
- Log in to Oracle WebCenter Content server as a system administrator.
- On the Oracle WebCenter Content home page, expand Administration and select Admin Applets.
- On the Administration Applets page, click Repository Manager.
- On the Repository Manager page, click the Indexer tab.
- Under Collection Rebuild cycle section, click Start. In the dialog, deselect the Use fast rebuild option and then click OK to proceed.
For other optional advanced configurations, see this documentation.
Configure SAML2 IDCS Single Sign-On in WebCenter Portal
Learn to configure SAML2 IDCS Single Sign-On in WebCenter Portal.
Prerequisites
Complete the following before running the configuration script.
Create a WebCenter Portal Stack
A WebCenter Portal stack should have been created from OCI Marketplace on which SAML2 IDCS SSO configuration needs to be configured.
Create an OAuth Client for IDCS
Follow the below instructions based on whether OCI Tenancy IAM is with Identity Domains or not.
For OCI accounts where IAM is with Identity Domains (tenancy with IAM domains), complete the following:
Log in to OCI console.
Navigate to Identity & Security, and then Domains.
Select the domain which needs to be used for SSO log-in.
Go to Integrated Applications and click Add application.
Choose Confidential Application and launch the workflow.
On the Add Application Details page, fill the Name and Description fields, and then click Next.
On the Configure OAuth page, select the Configure this application as a client now option under Client configuration section.
In the Authorization section, select the Client credentials check box for the Allowed Grant Types field.
Scroll down and select the Add app roles check box. In the App roles section, add the Identity Domain Administrator role.
Click Next. Leave the default settings for the next page as is and click Finish.
Make a note of the client ID and client secret. These values will be needed when you run the script.
Activate the application.
For OCI accounts where IDCS is not yet migrated to IAM Domains (tenancy without IAM domains), complete the following:
Log in to the IDCS administration console of the federated IDCS.
For example, https://idcs-abcde.identity.oraclecloud.com/ui/v1/adminconsole.
Navigate to Applications. Click + to add an application. Choose Confidential Application in the wizard:
Add a name and a description on the App details page.
Click Next. Select the Configure this application as a client now option.
In the Authorization section, select the Client credentials check box for the Allowed Grant Types field.
In the Grant the client access to Identity Cloud Service Admin APIs section, click Add to add the application roles. You need to add the Identity Domain Administrator role.
Click Next. Leave the default settings for the next pages as is and click Finish.
Make a note of the client ID and client secret. These values will be needed when you run the script.
Activate the application.
Configuration in Stack
A configuration helper script will be available in every stack VM. It can be executed from Admin compute VM or VM-1 (*-wls-1) for WebCenter Portal and WebCenter Content domains.
The script expects the following inputs.
| Argument | Description |
|---|---|
| idcs_tenant | IDCS tenant name For example, if IDCS URL is idcs-abcde.identity.example.com, then IDCS tenant name would be idcs-abcde. |
| idcs_domain | IDCS domain For example, if IDCS URL is idcs-abcde.identity.example.com, then IDCS domain would be identity.example.com. |
| idcs_client | Client ID of the OAuth client created in prerequisites |
| idcs_client_secret | Client secret of the OAuth client created in prerequisites |
| service_host | Service host with DNS record mapped to load balancer IP For example, wcpstack1.xyz.com, wccstack1.xyz.com. If service host is not available, a load-balancer IP can be provided here for testing. |
| idcs_user_name | IDCS user who is configured as WebCenter product administrator user |
For WebCenter Portal Domain
Complete the following steps to execute the script:
Run the configure sso script for WebCenter Portal domain from VM having a name like <*>-wcp-wls-1 with service host value for WebCenter Portal load balancer DNS host or IP.
ssh -o ProxyCommand="ssh -W %h:%p -i <key> opc@<bastion-ip>" -i <key> opc@<wcp-vm-1-ip>
sudo su - oracle
cd /u01/scripts/sh
nohup sh configure_sso.sh --idcs_tenant <idcs-tenant> --idcs_domain identity.oraclecloud.com --idcs_client <idcs_client> --idcs_client_secret <idcs_client> --idcs_username <idcs_username> --service_host <wcp_service_host> &The script execution progress can be monitored from /u01/data/domains/logs/provisioning.log. Once the execution completes without any error, the configuration is completed in the stack environment.
Note: If the configuration was done with load-balancer IP, then the above script needs to be executed again with the service host once the DNS mapping to WebCenter Portal load-balancer IP is created.
For WebCenter Content Domain
Run the configure sso script for WebCenter Content domain from VM having a name like <*>-wcc-wls-1 with service host value for WebCenter Content load balancer DNS host or IP.
ssh -o ProxyCommand="ssh -W %h:%p -i <key> opc@<bastion-ip>" -i <key> opc@<wcc-vm-1-ip>
sudo su - oracle
cd /u01/scripts/sh
nohup sh configure_sso.sh --idcs_tenant <idcs-tenant> --idcs_domain identity.oraclecloud.com --idcs_client <idcs_client> --idcs_client_secret <idcs_client> --idcs_username <idcs_username> --service_host <wcc_service_host> &The script execution progress can be monitored from /u01/data/domains/logs/provisioning.log. Once the execution completes without any error, the configuration is completed in the stack environment.
Note: If the configuration was done with load-balancer IP, then the above script needs to be executed again with the service host once the DNS mapping to WebCenter Content load-balancer IP is created.
Configuration in your IDCS Tenant
Once the SAML configuration is completed on WebCenter Portal, SAML applications will be created under Integrated Applications in the IDCS domain. The WebCenter Portal/WebCenter Content role mapping groups (as described in the tables below) are also created.
| WebCenter Portal Group | Description |
|---|---|
| WebcenterGroup | The admin role is assigned to the system administrator. By default, this role has Admin permission to all security groups and all accounts, and has rights to all the administration tools. |
| WebCenter Content Groups | Description |
|---|---|
| admin | The admin role is assigned to the system administrator. By default, this role has Admin permission to all security groups and all accounts, and has rights to all the administration tools. |
| contributor | The contributor role has Read and Write permissions to the Public security group, which enables users to search for, view, check in, and check out content. |
| guest | The guest role has Read permission to the Public security group, which enables users to search for and view content. |
| sysmanager | The sysmanager role has privileges to access the Admin Server links from the Administration menu in the user interface. |
The Admin user is granted membership to the WebcenterGroup/admin group and can be used to access the service.
The SAML applications will be prefixed with the stack service name. Examples: wcp12_wcp_saml, wcp12_wcc_saml.
Add Users to Groups
To add a new user other than the administrator, you would need to add the user to the IDCS WebCenter Portal/WebCenter Content groups based on the permissions required for their usage.
Verification
After the configuration of SAML, verify the WebCenter Portal application URLs and validate that the IDCS SSO log-in is working.
Portal Server: https://<WebCenter Portal service_host|lb_ip>:8888/webcenter/portal
Content Server: https://<WebCenter Content service_host|lb_ip>:16200/cs
Web UI: https://<WebCenter Content service_host|lb_ip>:16225/wcc
Capture: https://<WebCenter Content service_host|lb_ip>:16400/dc-console
Imaging: https://<WebCenter Content service_host|lb_ip>:16000/imaging
Using Oracle WebCenter Portal 14c (14.1.2) on Marketplace in Oracle Cloud Infrastructure
G30112-02
Last updated: June 2025
Copyright © 2024, Oracle and/or its affiliates.
Primary Author: Oracle Corporation