About User and Role Management
Overview of user authentication, roles, and groups in Oracle Fusion Cloud Enterprise Performance Management and Oracle Fusion Cloud Enterprise Data Management.
The environment is protected by multiple layers of security. Oracle implements and manages infrastructure security components to create highly secure Cloud EPM and Cloud EDM environments. Access is restricted to authorized users through various mechanisms, including:
- Single Sign-On (SSO)
- Role-based access to environments
Both SSO and role-based security are governed by Oracle Identity Management, which establishes a security domain for each environment. After a successful signin, access to the service is determined by the role assigned to the user.
Cloud Account Name
The Cloud Account Name is the Oracle account that manages your subscription. In OCI (Gen2), Identity Domain Administrators use IAM Interface in Oracle Cloud Console to set up and manage users and security.
The Account Administrator grants the Identity Domain Administrator role to one or more users to delegate security setup responsibilities. By default, each customer is allocated two environments: one for testing and other for production. Multiple services may be activated under one cloud account.
Users
Each user who needs to access an environment must have an account in the identity domain associated with the environment. The application roles assigned to the user determine what the user can do within an environment.
Application Cloud EPM Roles
Roles link users to the business activities that they are permitted to perform within an environment and the data that they can access. Users must be assigned to application roles that grant them access to business functions and associated data. Application roles are described in Understanding Application Roles. Identity Domain Administrator is not an application role.
Groups
There are three types of groups:
- PREDEFINED: These groups are automatically created for each application role. All users are assigned to a PREDEFINED group based on their application role (for example, Power User). You can view them in Access Control.
- EPM: These are the groups that you create in Access Control. They cannot be created in Oracle Cloud Console.
- IDCS: In OCI (Gen2), multiple users can be assigned to groups, which can then be assigned application roles. This eliminates the need to assign application roles to individual users, simplifying role administration. Since Oracle Identity groups can be synced with identity provider (IdP) groups (such as Microsoft Entra ID), you can add individual users to IdP groups and assign application roles to these groups in the IAM Interface of Oracle Cloud Console. These groups can also be synchronized with identity providers like Okta or Microsoft Entra ID. Although they will appear in Access Control, they cannot be created directly through this interface.
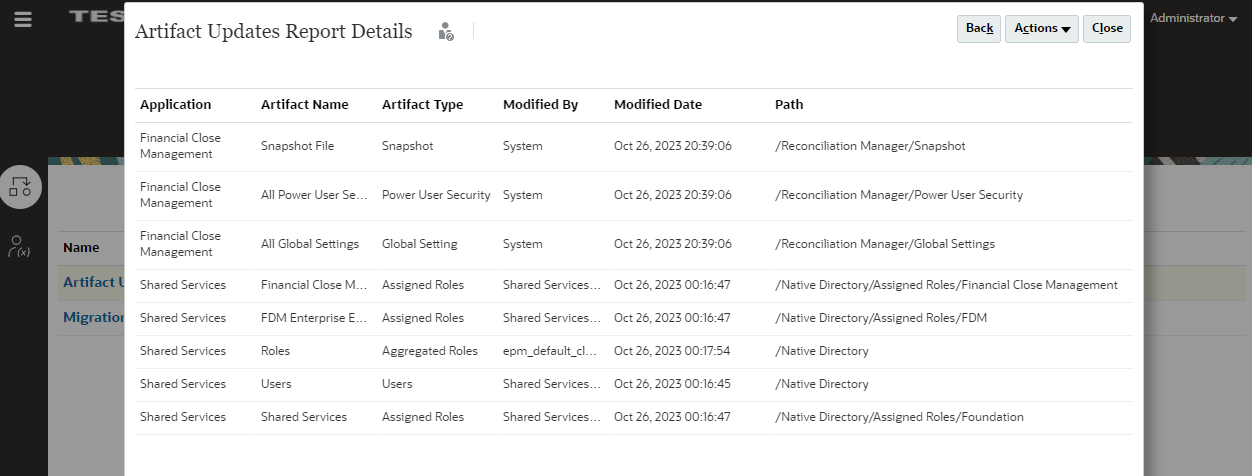
Use of SYSTEM as a Username
The environment shows the user name as SYSTEM if there are changes done internally or it is not recorded who made the change. There is no real user on the environment with this name. For example, for the following Account Reconciliation artifacts, there may be many Modified By users or the Modified By user is not always recorded. In such cases, SYSTEM is identified as the Modified By user:
- Snapshot
- Aging Profile
- Currency Bucket
- Global Settings
- Power User Security
- Rate Type
Related Tutorial
This tutorial describes the layers of security in business processes and shows you how to manage security using Access Control and access permissions. The sections build on each other and should be completed sequentially. See Setting Up Security in Cloud EPM Business Processes.