9Security
Security
Data Confidentiality
Taleo strongly recommends the enforcement of "Full SSL" as the supported communications protocol. The SSL communications protocol properties can be configured with the SmartOrg Communications Protocol Editor by a user with an Integrator role. When "Full SSL" mode is enforced, the Taleo-hosted environments only accept HTTPS requests. This communication protocol configuration ensures that only secure connections are accepted and that all data transmitted is properly encrypted. All Integration points created with TCC should conform to this protocol at the handshake. TCC supports TLS 1.2.
To support organizations with limited HTTPS capabilities, TCC allows HTTP based communications. When this protocol is selected, the data is not encrypted during transmission between TCC and the Taleo-hosted environments. HTTP communication should only be used when the organization’s network does not support HTTPS communications.
User Authentication
TCC supports basic user name and password authentication as well as certificate based authentication.
Web Services Security (WS-S)
Oracle Taleo announced the deprecation of support for Username Token Profile 1.1 using the PasswordDigest scheme in release 14B. Any customers using this method for authenticating with the Oracle Taleo Enterprise Edition 14B and above zones, will be required to make modifications and replace Password Digest with Basic Authentication. Configuration that were using this scheme will now automatically default to basic authentication.
Basic Authentication
When using the basic authentication, TCC provides user credentials in the form of a user name and password, as HTTP headers.
Certificate Based Authentication
TCC supports the signing of communication between TCC and the Taleo zone. The authentication is used to sign the requests and responses between Connect Client and Taleo. This is in addition to basic authentication.
Stored Passwords
Taleo Connect Client (TCC) communicates to Taleo hosted products using an authenticated user and password. In addition, if proxy servers are installed within the environment additional user credentials can be required by TCC.
Integration User password
TCC maintains the Integration User password locally to establish a connection with a Taleo hosted product. Passwords can be stored in the following locations:
Default configuration board file: default.board.xml
Environment file: *.properties
Configuration files: *_cfg.xml
The Integration User password is encrypted by an AES algorithm with a key size of 128 bits. It is stored in an XML file:
EncryptedPassword=Base64 (AES:128 (password))
Encryption Key Server (EKS)
With release 14A, an encryption key server is delivered with Taleo Connect Client (TCC) which can be used to augment existing password management services. The EKS can be used to generate a key that encrypts passwords within the TCC application.
Encryption Key Server Installation
Step 1. Copy the encryptionkey-server.jar file from the server folder under the TCC installation folder, to a location on the network. It is recommended that this be a different location than the TCC installation. The encryptionkey-server.jar file is the default EKS delivered for enhancing password management.
Step 2. By default, the EKS runs using a local host IP address and port 1126. To use another address or port, a folder and file must be created at the server root location. (A server restart is required following any modification.)
Folder and file name:
conf/EncryptionKeyServer.conf File content:
HOST_PORT=YOUR_SERVER_PORT
HOST_ADDRESS=YOUR_SERVER_ADDRESS
Step 3. The encryption server can now be started, call your_java_location –jar encryptionkey-server.jar.
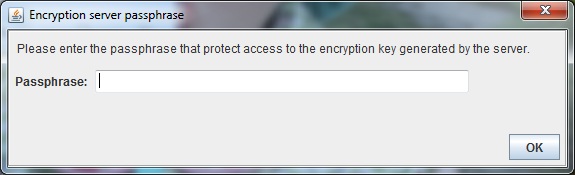
a. On Windows platform - the following screen prompts is displayed to the user. The user should enter a passphrase value. This value is masked with *.
b. On platform - command line will prompt user for passphrase entry.
On starting the EKS for the first time, an AES symmetric encryption key is generated. This will be automatically saved into the conf/ClientKey.key file. The user entered passphrase is used to protect access to the encryption key value stored in this file. Each new installation of the EKS will generate a different & unique encryption key. Due to this, it is strongly recommended that a backup of the key file is made and saved in a secured location. In doing so, it is possible to recover encrypted data if there is a failure with the original implementation. Using the same passphrase would unlock the encryption key needed to decrypt the data. At all subsequent EKS startups, the entered passphrase will be used to unlock the encryption key needed to decrypt any encrypted data.
Configuring TCC using an Encryption Key Server
It is necessary for TCC to be provided with the host address and port of the EKS that was setup and configured in the previous step. This can be added when a new instance of TCC is being installed via the setup dialog step illustrated below. This information is captured during the installation process of the new version of TCC and stored in the TaleoConnectClient.ini file.
If more convenient, the EKS can be installed at a later time, and the relevant host and port information can be added directly into the TaleoConnectClient.ini file as illustrated below:
-
-Dcom.taleo.integration.client.encryption.key.hostPort=Your_Server_Port
-
-Dcom.taleo.integration.client.encryption.key.hostAddress=Your_Server_Address
Please note that using a different encryption server will imply modifying the configuration files to use the new encryption key.
In TCC, no modifications are visible in the UI. When creating a new profile or configuration board entry, if both properties have been specified, the encryption from the server is used to encrypt the password. Otherwise, the default encryption mechanism is used.
Encrypt Password Tool
An additional tool is provided to encrypt individual string values. It is located in the menu.
Enter the string value to encrypt in the text box and click Encrypt. If the encryption server properties are defined, this will be used to encrypt the value. Otherwise, the default encryption mechanism will be used. The encrypted result is displayed at the bottom of the page. Click Copy to save to clipboard. Click Close to close the window.
Proxy Password Management Using EKS
TCC uses a System Properties file to authenticate itself against proxy servers needed to access the internet. The required System properties are:
-Dhttp.proxyHost=myproxyhostname
-Dhttp.proxyPort=portnumber
-Dhttp.proxyUser=username
-Dhttp.proxyPassword=hello123
-Dhttps.proxyPassword=securedHello123
The two following properties must be added to use the Encryption Key Server:
-Dcom.taleo.integration.client.encryption.key.hostAddress=your_server_address
-Dcom.taleo.integration.client.encryption.key.hostPort=your_server_port
There are two different ways to set up System properties, depending on the way TCC is launched.
-
On windows via the GUI:
When running TCC through the Windows GUI, all System properties must be defined in the TaleoConnectClient.ini file located at the root of the installation folder.
-
Launching TCC through the Command Line interface:
When running TCC in a Command Line interface, the System properties must be included in the TaleoConnectClient.bat (Windows) or TaleoConnectClient.sh (Linux) files.
To be able to run TCC from command line without any issue it is recommended to use the following Java options (don't forget to replace the variables with the values that are best for the type of operations that are done).
JAVA_OPTS=" -ms${JAVA_MIN_MEM}M -mx${JAVA_MAX_MEM}M -XX:NewSize=${NEWGEN}m -XX:MaxNewSize=${MAXNEWGEN}m -XX:PermSize=${PERMGEN}m -XX:MaxPermSize=${MAXPERMGEN}m
EKS Logging Service
A logging service is available for operations related to the encryption key server. Logging is written in file log/ EncryptionServerLog.log. Default level is INFO. It is possible to change the logging level using a property at startup. Here are the possibilities:
-
-Dlog.file.level=LEVEL_TO_USE
-
-Djava.util.logging.config.file=YOUR_LOGGING_PROPERTIES_FILE_PATH
Here is an example of logging properties file content: com.taleo.integration.client.encryption.key.level=FINE
Specifying Integration Password
Specifying Integration user password as ENCRYPTED_PASSWORD symbol when using the command line to invoke TCC.
Using ENCRYPTED_PASSWORD symbol improves security since the integration passwords do not have to be unveiled to TCC script developers.
Override ENCRYPTED_PASSWORD
To pass the password at the command line, add the following system property when invoking the TCC application:
clear text password
-Dcom.taleo.client.symbol.ENCRYPTED_PASSWORD=TheSecretPasswordencrypted password
-Dcom.taleo.client.symbol.ENCRYPTED_PASSWORD=[DECRYPT(\"xH/JD4X3xuVTMz7pO1fdxcFUBUlFWGrZqTfNDw/DLpo=\")]
HTTP Proxy
In certain corporate networks, IT policies enforce the use of a proxy to funnel all external HTTP requests. This is an important part of the overall network security.
The Taleo Connect Client fully supports the use of an HTTP proxy both in the runtime execution script andthrough the design environment. The configuration of the HTTP proxy follows the Java standard documented at http://docs.oracle.com/javase/1.5.0/docs/guide/net/properties.html (these are the same specifications as for the 1.6 http://docs.oracle.com/javase/6/docs/technotes/guides/net/properties.html or 1.7 http://docs.oracle.com/javase/7/docs/technotes/guides/net/properties.htmlversion).
According to these specifications, the configuration of the HTTP proxy is done at the JRE level; that is the runtime environment in which the integration process is invoked. The connectivity information is passed as system properties in either the runtime execution script or the design environment initialization file.
Hence, assuming the corporate HTTP proxy is available at proxy.acme.net on port 3128, the TaleoConnectClient.bat script should be changed to add
%JAVA_HOME%\bin\java.exe
-Dhttp.proxyHost=proxy.acme.net
-Dhttp.proxyPort=3128
-Djava.endorsed.dirs=%IC_HOME%\lib\endorsed
Certain corporate HTTP proxy implementations require an explicit authentication. This information can be provided with two extra system properties as in the following example:
%JAVA_HOME%\bin\java.exe
-Dhttp.proxyHost=proxy.acme.net
-Dhttp.proxyPort=3128
-Dhttp.proxyUser=acmeuser
-Dhttp.proxyPassword=secret
-Djava.endorsed.dirs=%IC_HOME%\lib\endorsed
Please note that we also fully support the http.nonProxyHosts property as defined in the Java specifications.
If the use of an HTTP proxy is required also in the design environment, then the following lines should be added to the TaleoConnectClient.ini file:
vmargs
-Djava.endorsed.dirs=lib/endorsed
-Dorg.apache.commons.logging.Log=org.apache.commons.logging.impl.Log4JLogger
-Dhttp.proxyHost=proxy.acme.net
-Dhttp.proxyPort=3128
In previous versions, the configuration of the HTTP proxy was done in the client configuration file itself. This is no longer supported in favor of the standard way described above (see the section for more details).
Certain implementations support the https.proxyHost property although it is not part of the Java standard. The Taleo Connect Client only supports http.proxyHost, which is used for all HTTP requests (HTTP or HTTPS protocol).
Encrypting Proxy Password
Microsoft NTLM V1 Support
The Microsoft NTLM V1 proxy server authentication scheme is now supported. Clients with network security policies leveraging only this authentication method can now install TCC within their infrastructure in compliance with their internal policy.
Things to Consider
Technical limitations prevents password digest retrieval from the system.
The proxy password cannot be read from the network automatically; it must be manually entered in the batch file.
Users must keep the password in the batch file synchronized with the Windows domain password.
All proxy passwords MUST be encrypted.
Proxy System Properties Configuration
The Microsoft NTLM V1 proxy server authentication scheme must be configured in files located at the root of the TCC installation folder.
Launching TCC using the Windows user interface
When running TCC on Windows, all system properties must be defined in the TaleoConnectClient.ini file.
Launching TCC using the command line
When running TCC using the command line, all system properties must be passed using the command line. Insert the system properties in the TaleoConnectClient.bat file for Windows or in the TaleoConnectClient.sh file for Linux.
System Properties for NTLM Proxies
The following list contains system properties you can configure for the proxy:
-Dhttp.proxyHost=myproxyhostname-Dhttp.proxyPort=8080-Dhttp.proxyUser=username (Windows Domain User Name)-Dhttp.proxyPassword=encrypted password (Windows Domain Password)-Dhttp.proxyNTDomain=ACMEDOMAIN (Windows Domain Name)
Note: "http.proxyNTDomain" is only required for NTML proxy authentication.
Windows Vista
Although Microsoft Vista supports both the NTLM V1 and NTLM V2 proxy server authentication scheme, TCC currently supports only Microsoft NTLM V1.
Data at Rest
Standard TCC implementations have no data retention capabilities. Data-at-rest encryption capabilities are not required.