2 Configuring HSM
The HSM can be configured to protect keys, work in a classic primary-standby setup, or in a Multi-Master Cluster.
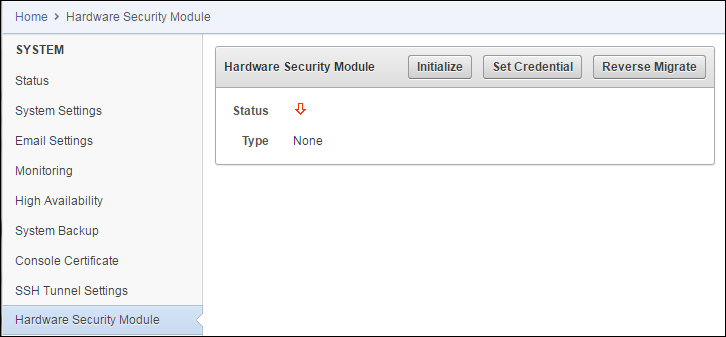
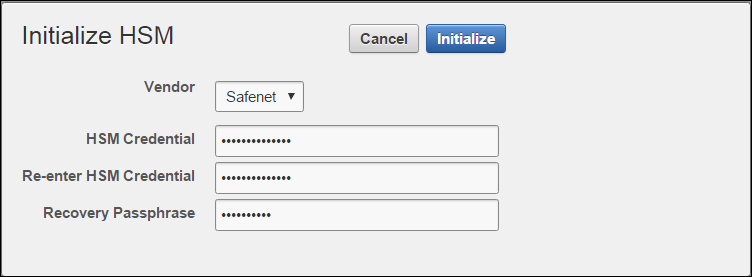
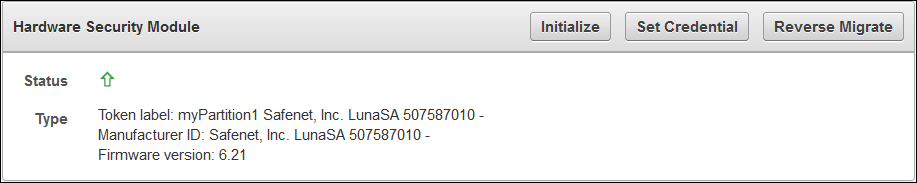
2.1 Protect the Oracle Key Vault TDE Master Key with the HSM
Note:
If you change the HSM credential on the HSM after initialization, you must also update the HSM credential on the Oracle Key Vault server using the Set Credential command.Parent topic: Configuring HSM
2.2 Enable HSM in a Primary-Standby Oracle Key Vault Installation
In a primary-standby Oracle Key Vault installation you must enable HSM separately on the servers you mean to designate as primary and standby before pairing them in a primary-standby configuration.
If you are enabling primary-standby using a nCipher HSM, see Vendor Specific Notes - nCipher for more instructions.
To enable HSM in a primary-standby deployment, do the following:
Parent topic: Configuring HSM
2.3 HSM in a Multi-Master Cluster
In an Oracle Key Vault installation with HSM enabled, the HSM stores a top-level encryption key, thereby acting as a Root of Trust (RoT) that protects encryption keys used by OKV. HSMs are built with specialized tamper-resistant hardware which is harder to access than normal servers. This protects the RoT and makes it difficult to extract, lowering the risk of compromise. In addition HSMs can be used in FIPS 140-2 Level 3 mode which can help meet certain compliance requirements.
Note:
An existing Oracle Key Vault deployment cannot be migrated to use an HSM as a Root of Trust.In a Multi-Master OKV installation, any OKV node in the cluster can use any HSM. The nodes in the Multi-Master cluster may use different TDE wallet passwords, Root of Trust keys, and HSM credentials.
Note:
To ensure complete security, all OKV nodes within the cluster must be HSM-enabled.- Set up HSM for a Multi-Master Cluster with a Single Node
- Set up HSM for a Multi-Master Cluster with Multiple Nodes
Parent topic: Configuring HSM
2.3.1 Set up HSM for a Multi-Master Cluster with a Single Node
If you want to use a HSM with a Multi-Master Cluster, it is strongly recommended that you start with a single HSM-enabled node and add additional HSM-enabled nodes, as described in this section.
The following are the recommended steps to set up HSM for a Multi-Master cluster with a single node:
- Configure the first node of the cluster.
- Configure HSM on the first node before adding any new nodes. If there is already more than one node in the cluster, follow the steps described below.
- HSM-enable the Oracle Key Vault servers that are going to be added to the cluster.
- Add the HSM-enabled nodes to the cluster. If any node in the cluster is already HSM-enabled, you cannot add a new node that is not HSM-enabled.
Parent topic: HSM in a Multi-Master Cluster
2.3.2 Set up HSM for a Multi-Master Cluster with Multiple Nodes
Please note that Set up HSM for a Multi-Master Cluster with a Single Node is the recommended method for setting up HSM for a Multi-Master Cluster.
If the first node to be HSM-enabled is in a cluster that already has multiple nodes, information has to be manually copied from that HSM-enabled OKV to all of the other OKVs in the cluster before HSM-enabling any other nodes.
If the first node to be HSM-enabled has a downstream peer, the downstream peer will not be able to decrypt the information from the HSM-enabled node until the bundle is copied and applied successfully to the downstream peer.
The following are the recommended steps to set up HSM for a Multi-Master cluster with multiple nodes:
-
Configure HSM on a node of the cluster.
-
On the HSM-enabled node, click Create Bundle on the HSM page.
-
Log in to the HSM node through SSH as user
support.ssh support@hsm_enabled_node <Enter password when prompted> - Switch to the
rootuser.su root <Enter password when prompted> -
To copy the bundle to the
/usr/local/okv/hsmlocation on each of the other nodes using the IP address:scp /usr/local/okv/hsm/hsmbundle support@ip_address:/tmp -
Log in to each node in the cluster using the IP address (except the original HSM-enabled node):
ssh support@ip_address <Enter password when prompted> - Switch to the
rootuser.su root <Enter password when prompted> -
Perform the following steps on each node:
cp /tmp/hsmbundle /usr/local/okv/hsm/ chown oracle:oinstall /usr/local/okv/hsm/hsmbundle -
On each node except the original HSM-enabled node, click Apply Bundle on the HSM page. The bundle must be applied immediately on all nodes before reverse migrating this node. Proceed to HSM-enable each of these nodes in the same way that the first node was HSM-enabled. After all of the nodes have been HSM-enabled and replication between all nodes has been verified, remove the
hsmbundlefiles from all of the nodes.
Parent topic: HSM in a Multi-Master Cluster
2.4 Backup and Restore in HSM Mode
You can backup and restore Oracle Key Vault with HSM mode enabled.
Parent topic: Configuring HSM
2.4.1 Backup in HSM Mode
Parent topic: Backup and Restore in HSM Mode
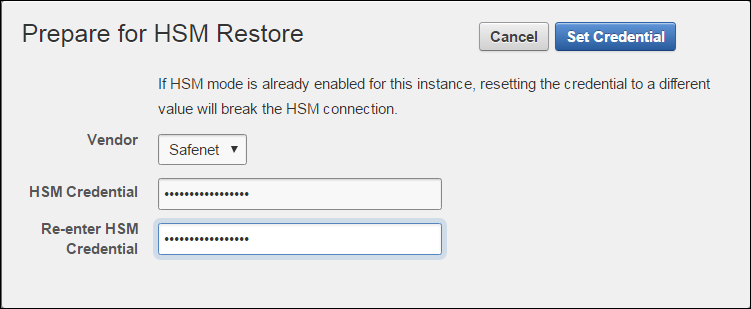
2.4.2 Restore in HSM Mode
-
HSM
-
Root of Trust used to take the backup
Parent topic: Backup and Restore in HSM Mode
2.5 Reverse Migrating to Local Wallet
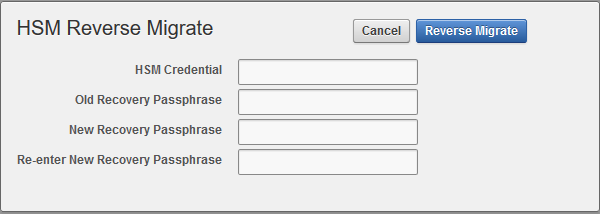
The HSM reverse migrate procedure allows you to disable the HSM and go back to a local wallet protected by the Recovery Passphrase. The purpose of reverse migrate is to revert back to a local wallet protected by the Recovery Passphrase. This will be necessary if an HSM currently protecting Oracle Key Vault needs to be decommissioned.
- Reverse Migrating a Standalone Deployment
- Reverse Migrating a Primary-Standby Deployment
- Reverse Migrating a Multi-Master Cluster
Parent topic: Configuring HSM
2.5.1 Reverse Migrating a Standalone Deployment
Parent topic: Reverse Migrating to Local Wallet
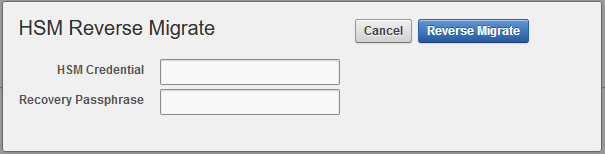
2.5.2 Reverse Migrating a Primary-Standby Deployment
Perform the following procedure to reverse migrate a primary-standby deployment (Oracle Key Vault 12.2.0.6.0 and later).
To reverse migrate a primary-standby deployment (Oracle Key Vault 12.2.0.6.0 and later), do the following:Parent topic: Reverse Migrating to Local Wallet
2.5.3 Reverse Migrating a Multi-Master Cluster
Parent topic: Reverse Migrating to Local Wallet