4 Oracle Key Vault Installation and Configuration
Installing Oracle Key Vault entails ensuring that the environment meets the necessary requirements before you begin the installation and configuration.
- About Oracle Key Vault Installation and Configuration
Oracle Key Vault is a software appliance that is delivered as an ISO image. - Oracle Key Vault Installation Requirements
The Oracle Key Vault installation requirements cover system requirements such as CPU, memory, disk space, network interfaces, and supported endpoint platforms. - Installing and Configuring Oracle Key Vault
You must download the Oracle Key Vault application software, and then you can perform the installation. - Logging In to the Oracle Key Vault Management Console
To use Oracle Key Vault, you can log in to the Oracle Key Vault management console. - Upgrading a Standalone or Primary-Standby Oracle Key Vault Server
This upgrade includes the Oracle Key Vault server software and utilities that control the associated endpoint software. - Upgrading Oracle Key Vault in a Multi-Master Cluster Environment
Similar to a standalone or primary-standby upgrade, this type of upgrade includes the Oracle Key Vault server software and endpoint software-related utilities. - Overview of the Oracle Key Vault Management Console
The Oracle Key Vault management console provides a graphical user interface for Oracle Key Vault users. - Performing Actions and Searches
The Oracle Key Vault management console enables you to perform standard actions and search operations, as well as get help information.
4.1 About Oracle Key Vault Installation and Configuration
Oracle Key Vault is a software appliance that is delivered as an ISO image.
The software appliance consists of a pre-configured operating system, an Oracle database, and the Oracle Key Vault application. You can install Oracle Key Vault onto its own dedicated server, as a VM guest into your virtualization platform, or as a compute instance in your OCI tenancy. See the Oracle Cloud Marketplace at https://cloudmarketplace.oracle.com/marketplace/app/OracleKeyVault.
Before you begin the installation or upgrade process for Oracle Key Vault, check the Oracle Key Vault Release Notes for any known issues that you should be aware of.
Parent topic: Oracle Key Vault Installation and Configuration
4.2 Oracle Key Vault Installation Requirements
The Oracle Key Vault installation requirements cover system requirements such as CPU, memory, disk space, network interfaces, and supported endpoint platforms.
- System Requirements
System requirements include CPU, memory, disk, network interface, hardware compatibility, and RESTful services client. - Network Port Requirements
Network port requirements includes requirements for SSH/SCP, SNMP, HTTPS, listeners, KMIP, and TCP ports. - Supported Endpoint Platforms
Oracle Key Vault supports both UNIX and Windows endpoint platforms. - Endpoint Database Requirements
Administrators can use online master keys and the Oracle DatabaseCOMPATIBLEinitialization parameter to manage Oracle Database endpoints.
Parent topic: Oracle Key Vault Installation and Configuration
4.2.1 System Requirements
System requirements include CPU, memory, disk, network interface, hardware compatibility, and RESTful services client.
The Oracle Key Vault installation removes existing software on a server.
Deployment on virtual machines is not recommended for production systems. However, virtual machines are useful for testing and proof of concept purposes.
The minimum hardware requirements for deploying the Oracle Key Vault software appliance are:
-
CPU: Minimum: x86-64 16 cores. Recommended: 24-48 cores with cryptographic acceleration support (Intel AESNI).
-
Memory: Minimum 16 GB of RAM. Recommended: 32–64 GB.
-
Disk: Both BIOS and UEFI boot mode. For a system with a boot disk size greater than 2 TB, Oracle Key Vault supports booting in UEFI mode only.
-
Network interface: One network interface.
-
Hardware Compatibility: Any Intel x86 64-bit hardware platform supported by Oracle Key Vault's embedded operating system. Oracle Key Vault uses Oracle Linux release 7 with the Unbreakable Enterprise Kernel (UEK) version 5. For a list of compatible hardware, refer to Hardware Certification List for Oracle Linux and Oracle VM in the Related Topics. This list contains the minimum version of Oracle Linux certified with the selected hardware. All Oracle Linux updates starting with Oracle Linux release 7 as the minimum are also certified unless otherwise noted. Refer to Oracle Linux documentation for more information on the operating system platform.
Note:
You can find the supported hardware from the hardware certification list for Oracle Linux and Oracle VM. Filter the results by selecting All Operating Systems and choosing Oracle Linux 7.9. However, be aware that Oracle Key Vault does not support the QLogic QL4* family of network cards.Oracle Key Vault supports both Legacy BIOS and UEFI BIOS boot modes. The support for UEFI BIOS mode allows the installation of Oracle Key Vault on servers that exclusively support UEFI BIOS only, such as Oracle X7-2 Server. Oracle Key Vault can be installed on Oracle X7–2 servers as a standalone server, a primary-standby configuration, or a multi-master cluster configuration.
-
RESTful Services Client: If RESTful Services are enabled, then each endpoint that connects to the Oracle Key Vault management console must have at least Java 1.7.0.21 installed.
Note:
For deployment with a large number of endpoints, the hardware requirement may need to scale to meet the workload.Related Topics
Parent topic: Oracle Key Vault Installation Requirements
4.2.2 Network Port Requirements
Network port requirements includes requirements for SSH/SCP, SNMP, HTTPS, listeners, KMIP, and TCP ports.
Oracle Key Vault and its endpoints use a set of specific ports for communication. Network administrators must ensure that these ports are open in the network firewall.
The following table lists the required network ports for Oracle Key Vault:
Table 4-1 Ports Required for Oracle Key Vault
| Port Number | Protocol | Descriptions |
|---|---|---|
|
|
SSH/SCP port |
Used by Oracle Key Vault administrators and support personnel to remotely administer Oracle Key Vault |
|
|
SNMP port |
Used by monitoring software to poll Oracle Key Vault for system information |
|
|
HTTPS port |
Used by web clients such as browsers and RESTful Administrative commands to communicate with Oracle Key Vault |
|
|
HTTPS port |
Used by RESTful Key Management commands to communicate with Oracle Key Vault |
|
|
Database TCPS listener ports |
In a primary-standby configuration, listener ports used by Oracle Data Guard to communicate between the primary and standby server. In a cluster configuration, listener ports used to communicate between read-write peer nodes. |
|
|
HTTPS port |
Listener port used in a primary-standby configuration to run OS commands like synchronizing wallets and configuration files through HTTPS. This port is also used when you add a new node to a cluster. |
|
|
KMIP port |
Used by Oracle Key Vault endpoints and third party KMIP clients to communicate with the Oracle Key Vault KMIP Server |
|
|
TCP port |
Used by Oracle GoldenGate for transmitting data in a Multi-Master Cluster configuration. |
Parent topic: Oracle Key Vault Installation Requirements
4.2.3 Supported Endpoint Platforms
Oracle Key Vault supports both UNIX and Windows endpoint platforms.
Oracle supports 64-bit Linux endpoints, and only 64-bit endpoints are supported for Oracle databases that use the online master key. The operating systems on which the endpoint runs must be compatible with Transport Layer Security (TLS) 1.2, either directly or with appropriate patches.
The supported endpoint platforms in this release are as follows:
-
Oracle Linux (6 and 7)
-
Oracle Solaris x86 (10 and 11)
-
Oracle Solaris SPARC (10 and 11)
-
RHEL 6 and 7
-
IBM AIX (6.1, 7.1, and 7.2)
If you used AIX 5.3 in the release that you are upgrading from, then you must move your endpoints off that platform, because it is no longer supported starting with Oracle Key Vault release 21.1.
-
HP-UX (IA) (11.31)
-
Windows Server 2012
Parent topic: Oracle Key Vault Installation Requirements
4.2.4 Endpoint Database Requirements
Administrators can use online master keys and the Oracle Database COMPATIBLE initialization parameter to manage Oracle Database endpoints.
Administrators can use the online master key to manage TDE master encryption keys for endpoints that are Oracle Database 11.2 or later. Administrators who want to use Oracle Key Vault for wallet management only or who are migrating existing wallets deployments to Oracle Key Vault can use the okvutil upload command to upload Oracle wallets to Oracle Key Vault.
Administrators who manage endpoints that are Oracle Database may need to set the COMPATIBLE initialization parameter.
For an endpoint that is Oracle Database release 11.2 or later, set the COMPATIBLE initialization parameter to 11.2.0.0 or later. A COMPATIBLE setting of 11.2 or later enables Transparent Data Encryption to work with Oracle Key Vault. For example:
SQL> ALTER SYSTEM SET COMPATIBLE = '11.2.0.0' SCOPE=SPFILE;
This applies to an Oracle Database endpoint that use the online master key to manage TDE master encryption keys. This compatibility mode setting is not required for Oracle wallet upload or download operations.
Also note that after setting the COMPATIBLE parameter to 11.2.0.0, you cannot set it to a lower value such as 10.2. After you set the COMPATIBLE parameter, you must restart the database.
Parent topic: Oracle Key Vault Installation Requirements
4.3 Installing and Configuring Oracle Key Vault
You must download the Oracle Key Vault application software, and then you can perform the installation.
- Downloading the Oracle Key Vault Appliance Software
You can download executable files for both a fresh Oracle Key Vault installation or an upgrade. - Installing the Oracle Key Vault Appliance Software
The Oracle Key Vault installation process installs all the required software components onto a dedicated server or virtual machine. - Performing Post-Installation Tasks
After you install Oracle Key Vault, you must complete a set of post-installation tasks.
Parent topic: Oracle Key Vault Installation and Configuration
4.3.1 Downloading the Oracle Key Vault Appliance Software
You can download executable files for both a fresh Oracle Key Vault installation or an upgrade.
For a fresh installation, you can download the Oracle Key Vault appliance software from Software Delivery Cloud. You cannot use this package to upgrade Oracle Key Vault. For an upgrade, you can download the Oracle Key Vault upgrade software from the My Oracle Support website.
Parent topic: Installing and Configuring Oracle Key Vault
4.3.2 Installing the Oracle Key Vault Appliance Software
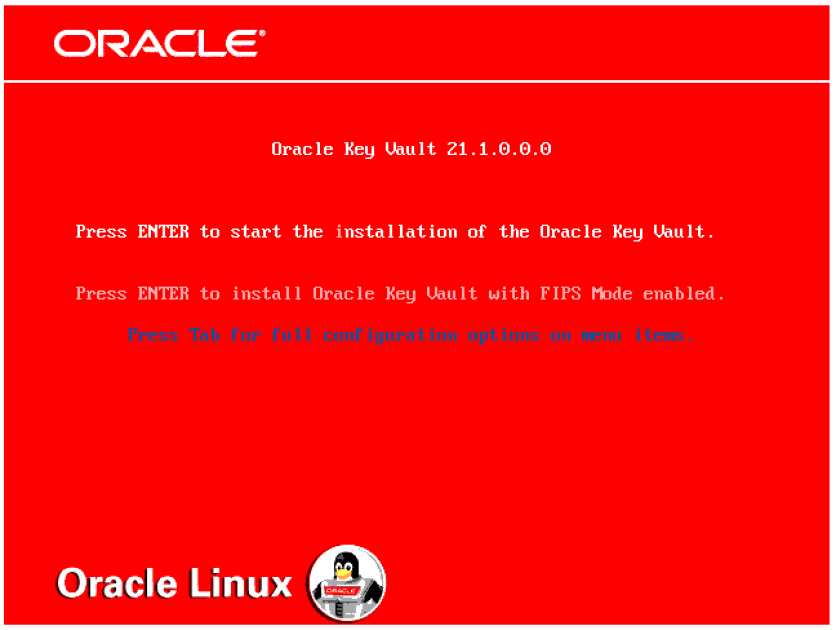
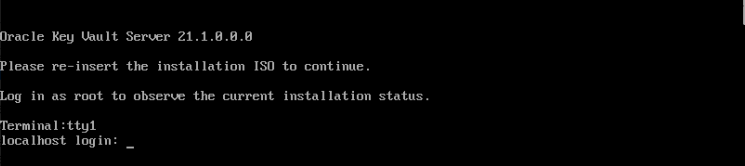
The Oracle Key Vault installation process installs all the required software components onto a dedicated server or virtual machine.
If you are installing Oracle Key Vault on VMware, then set the VMX configuration parameter disk.EnableUUID to TRUE. In addition, you must set your virtual machine to use EFI boot. In some versions of VMware this is done by selecting the VM Options tab, then expanding Boot Options, and then setting the firmware to EFI. You must disable secure boot. Without this setting, the Oracle Key Vault installation on VMware will fail.
Caution:
The Oracle Key Vault installation wipes the server, repartitions the disk, and installs a hardened Oracle Linux 7 Update 9. The installation erases existing software and data on the server.
-
Ensure that the server meets the recommended requirements.
-
Request a fixed IP address, network mask, and gateway address from your network administrator. You will need this information to configure the network.
To install the Oracle Key Vault appliance:
Related Topics
Parent topic: Installing and Configuring Oracle Key Vault
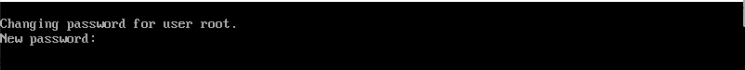
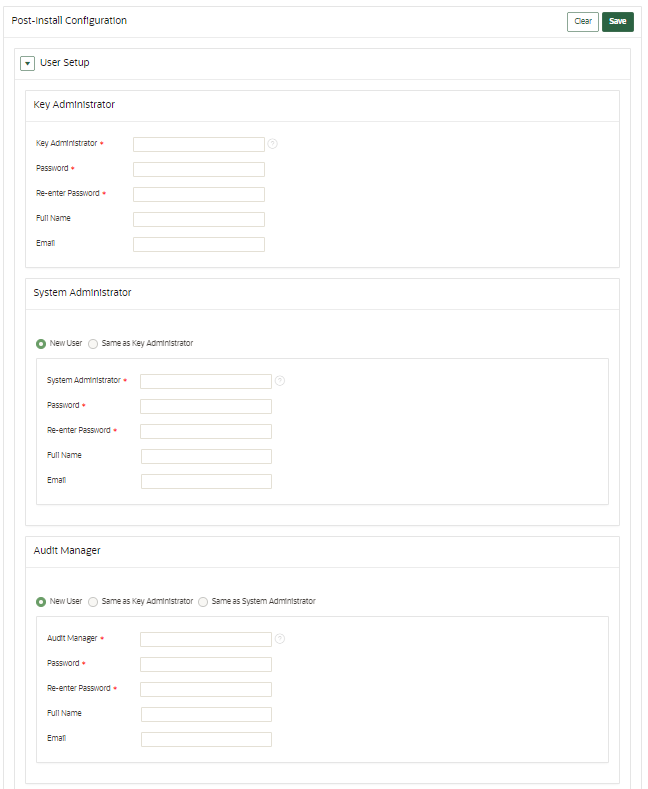
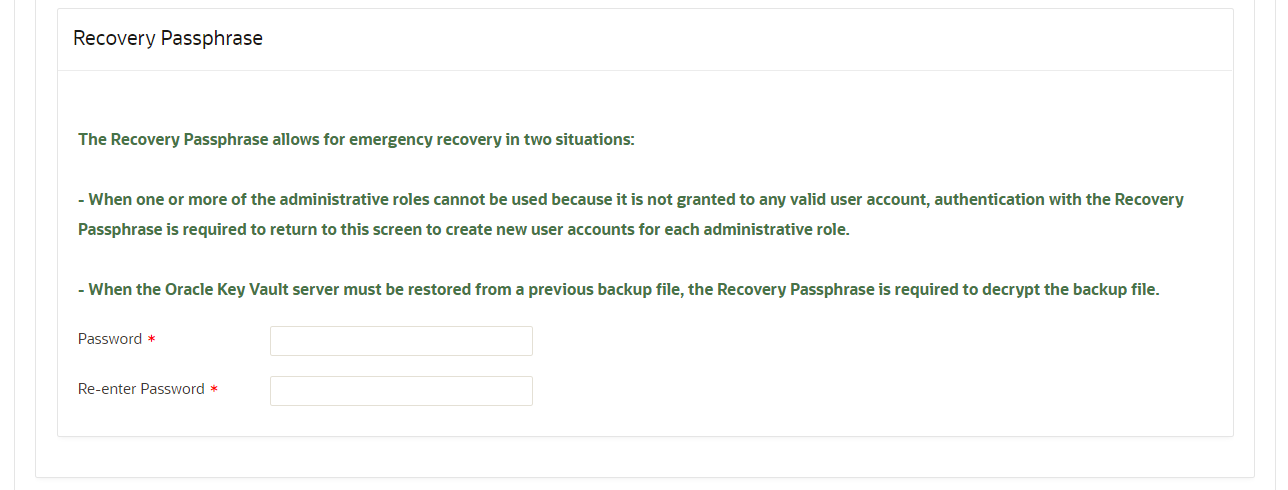
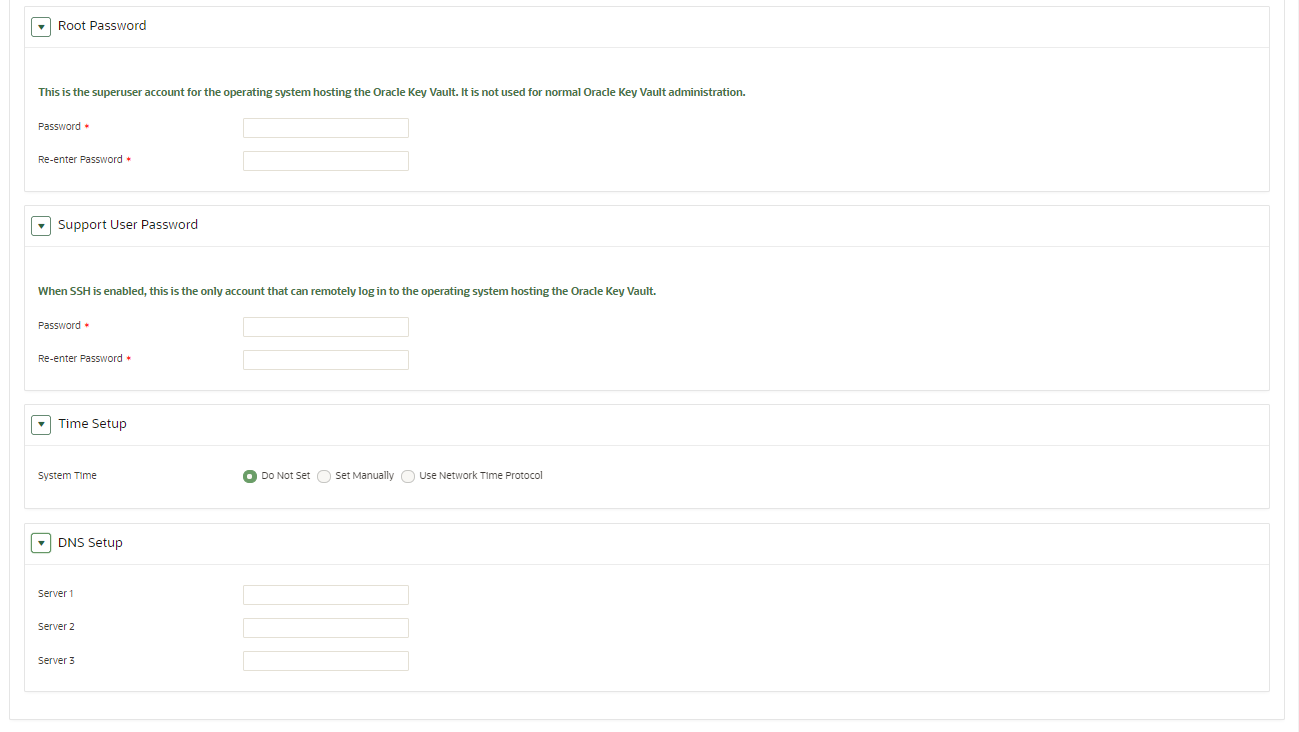
4.3.3 Performing Post-Installation Tasks
After you install Oracle Key Vault, you must complete a set of post-installation tasks.
These tasks include configuring the administrative user accounts and passwords for recovery, and operating system accounts and passwords for root and support.
Related Topics
Parent topic: Installing and Configuring Oracle Key Vault
4.4 Logging In to the Oracle Key Vault Management Console
To use Oracle Key Vault, you can log in to the Oracle Key Vault management console.
Parent topic: Oracle Key Vault Installation and Configuration
4.5 Upgrading a Standalone or Primary-Standby Oracle Key Vault Server
This upgrade includes the Oracle Key Vault server software and utilities that control the associated endpoint software.
- About Upgrading the Oracle Key Vault Server Software
When you upgrade the Oracle Key Vault server software appliance, also upgrade the endpoint software to get access to the latest enhancements. - Step 1: Back Up the Server Before You Upgrade
Before you upgrade the Oracle Key Vault server, perform a one-time backup to a remote destination so that you can recover data in case the upgrade fails. - Step 2: Perform Pre-Upgrade Tasks
To ensure a smooth upgrade to Oracle Key Vault, you should prepare the server you are upgrading. - Step 3: Add Disk Space to Extend the vg_root for the Release 21.1 Upgrade
Before upgrading to Oracle Key Vault release 21.1, you will need to extend thevg_rootto increase disk space. - Step 4: Upgrade the Oracle Key Vault Server or Primary-Standby Pair
You can upgrade a standalone Oracle Key Vault server or a pair of Oracle Key Vault servers in a primary-standby deployment. - Step 5: Upgrade the Endpoint Software
As part of the upgrade, you must reenroll endpoints created in earlier releases of Oracle Key Vault, or update the endpoint software. - Step 6: If Necessary, Add Disk Space to Extend Swap Space
If necessary, extend the swap space. Oracle Key Vault release 21.1 requires a hard disk size greater than or equal to 1 TB in size with approximately 64 GB of swap space. - Step 7: If Necessary, Remove Old Kernels
Oracle recommends that you clean up the older kernels that were left behind after the upgrade. - Step 8: If Necessary, Remove SSH-Related DSA Keys
You should remove SSH-related DSA keys left behind after the upgrade, because they can cause problems with some code analysis tools. - Step 9: Back Up the Upgraded Oracle Key Vault Server
You must perform server backup and user password tasks after completing a successful upgrade.
Parent topic: Oracle Key Vault Installation and Configuration
4.5.1 About Upgrading the Oracle Key Vault Server Software
When you upgrade the Oracle Key Vault server software appliance, also upgrade the endpoint software to get access to the latest enhancements.
However, the endpoint software downloaded from the previous Oracle Key Vault release will continue to function with the upgraded Oracle Key Vault server. Be aware that while the old endpoint software will continue to work with the upgraded Oracle Key Vault server, the new endpoint functionality may not work.
You must upgrade in the order shown: first perform a full backup of Oracle Key Vault, upgrade the Oracle Key Vault server or server pair in the case of a primary-standby deployment, the endpoint software, and last, perform another full backup of the upgraded server. Note that upgrading requires a restart of the Oracle Key Vault server.
The Oracle Key Vault server is not available to endpoints for a limited duration during the upgrade. You can enable the persistent cache feature to enable endpoints to continue operation during the upgrade process.
Before you begin the upgrade, refer to Oracle Key Vault Release Notes for additional information about performing upgrades.
4.5.2 Step 1: Back Up the Server Before You Upgrade
Before you upgrade the Oracle Key Vault server, perform a one-time backup to a remote destination so that you can recover data in case the upgrade fails.
Caution:
Do not bypass this step. Back up the server before you perform the upgrade so that your data is safe and recoverable.
Related Topics
4.5.3 Step 2: Perform Pre-Upgrade Tasks
To ensure a smooth upgrade to Oracle Key Vault, you should prepare the server you are upgrading.
Related Topics
4.5.4 Step 3: Add Disk Space to Extend the vg_root for the Release 21.1 Upgrade
Before upgrading to Oracle Key Vault release 21.1, you will need to extend the vg_root to increase disk space.
Related Topics
4.5.5 Step 4: Upgrade the Oracle Key Vault Server or Primary-Standby Pair
You can upgrade a standalone Oracle Key Vault server or a pair of Oracle Key Vault servers in a primary-standby deployment.
- About Upgrading an Oracle Key Vault Server or Primary-Standby Pair
In a standalone deployment you must upgrade a single Oracle Key Vault server, but in a primary-standby deployment you must upgrade both primary and standby Oracle Key Vault servers. - Upgrading a Standalone Oracle Key Vault Server
A single Oracle Key Vault server in a standalone deployment is the most typical deployment in test and development environments. - Upgrading a Pair of Oracle Key Vault Servers in a Primary-Standby Deployment
You should allocate several hours to upgrade the primary server after upgrading the standby.
4.5.5.1 About Upgrading an Oracle Key Vault Server or Primary-Standby Pair
In a standalone deployment you must upgrade a single Oracle Key Vault server, but in a primary-standby deployment you must upgrade both primary and standby Oracle Key Vault servers.
Note that persistent caching enables endpoints to continue to be operational during the upgrade process.
Note:
If you are upgrading from a system with 4 GB memory, first add an additional 12 GB memory to the system before upgrading.Related Topics
4.5.5.2 Upgrading a Standalone Oracle Key Vault Server
A single Oracle Key Vault server in a standalone deployment is the most typical deployment in test and development environments.
4.5.5.3 Upgrading a Pair of Oracle Key Vault Servers in a Primary-Standby Deployment
You should allocate several hours to upgrade the primary server after upgrading the standby.
Related Topics
4.5.6 Step 5: Upgrade the Endpoint Software
As part of the upgrade, you must reenroll endpoints created in earlier releases of Oracle Key Vault, or update the endpoint software.
Related Topics
4.5.7 Step 6: If Necessary, Add Disk Space to Extend Swap Space
If necessary, extend the swap space. Oracle Key Vault release 21.1 requires a hard disk size greater than or equal to 1 TB in size with approximately 64 GB of swap space.
swapon -s command. By default, Oracle Key Vault releases earlier than release 18.1 were installed with approximately 4 GB of swap space. After you complete the upgrade to release 18.1 or later, Oracle recommends that you increase the swap space allocation for the server on which you upgraded Oracle Key Vault. A new Oracle Key Vault installation is automatically configured with sufficient swap space. However, if you upgraded from a previous release, and your system does not have the desired amount of swap space configured, then you must manually add disk space to extend the swap space, particularly if the intention is to convert the upgraded server into the first node of a multi-master cluster.
4.5.8 Step 7: If Necessary, Remove Old Kernels
Oracle recommends that you clean up the older kernels that were left behind after the upgrade.
4.5.9 Step 8: If Necessary, Remove SSH-Related DSA Keys
You should remove SSH-related DSA keys left behind after the upgrade, because they can cause problems with some code analysis tools.
4.6 Upgrading Oracle Key Vault in a Multi-Master Cluster Environment
Similar to a standalone or primary-standby upgrade, this type of upgrade includes the Oracle Key Vault server software and endpoint software-related utilities.
- About Upgrading Oracle Key Vault in a Multi-Master Cluster Environment
To perform this upgrade, you must upgrade each multi-master cluster node. - Step 1: Perform Pre-Upgrade Tasks
Similar to a standalone or primary-standby environment, you must prepare the Oracle Key Vault server for the pre-upgrade multi-master cluster process. - Step 2: Add Disk Space to Extend the vg_root for Upgrade to Oracle Key Vault Release 21.1
To upgrade to Oracle Key Vault release 21.1, you will need additional disk space by adding an additional disk to be able to extend thevg_root. - Step 3: Upgrade Multi-Master Clusters
Depending on your multi-master cluster configuration, you must follow the steps that are specific to your deployment. - Step 4: Check the Node Version and the Cluster Version
After you complete the upgrade of at least one node, you can log into any of the upgraded nodes to check the node and cluster versions. - Step 5: If Necessary, Change the Network Interface for Upgraded Nodes
Nodes that were created in Oracle Key Vault releases earlier than release 21.1 use Classic mode, in which only one network interface was used.
Parent topic: Oracle Key Vault Installation and Configuration
4.6.1 About Upgrading Oracle Key Vault in a Multi-Master Cluster Environment
To perform this upgrade, you must upgrade each multi-master cluster node.
There are different steps for upgrading the multi-master cluster depending on your deployment. A 2-node cluster, running Oracle Key Vault release 18.5 or earlier, configured as a single read-write pair would involve running a pre-upgrade script which no other deployment requires. Multi-master cluster nodes deployed in a read-write configuration must follow different upgrade steps than those deployed as read-only nodes.
Oracle does not support direct upgrades from Oracle Key Vault release 18.1 or earlier. You must upgrade to Oracle Key Vault release 18.2 or later before upgrading to release 21.1.
The upgrade process involves performing the upgrade on each multi-master cluster node. After you have begun a cluster upgrade, ensure that you upgrade all the nodes in the cluster one after the other, without too much intervening time between upgrades of two nodes.
Upgrading an Oracle Key Vault multi-master cluster includes upgrading each cluster node to the new later version. You must upgrade all nodes to the same Oracle Key Vault version. You should first upgrade the read-only nodes of the cluster, and then upgrade the read-write pairs. As each cluster node is upgraded, its node version is updated to the new version of the Oracle Key Vault. After you complete the upgrade of all cluster nodes, the cluster version is updated to the new version of the Oracle Key Vault. You can check node version or the cluster version by selecting the Cluster tab, then in the left navigation bar, selecting Management. Oracle Key Vault multi-master cluster upgrade is considered complete when node version and cluster version at each cluster node is updated to the latest version of Oracle Key Vault.
Before you perform the upgrade, note the following:
- Perform the entire upgrade process on all multi-master cluster nodes, without interruption. That is, after you have started the cluster upgrade process, ensure that you try and upgrade all nodes, individually one after the other or in read-write pairs. Do not perform any critical operations or make configurational changes to Oracle Key Vault until you have completed upgrading all the nodes in your environment.
- Be aware that you cannot use any new features that were introduced in this release until you have completed upgrading all of the multi-master cluster nodes. An error is returned when such features are used from the node that has been upgraded. Oracle recommends that you plan the upgrade of all cluster nodes close to each other to ensure availability of the new features sooner.
4.6.2 Step 1: Perform Pre-Upgrade Tasks
Similar to a standalone or primary-standby environment, you must prepare the Oracle Key Vault server for the pre-upgrade multi-master cluster process.
- Back up the server so that you can recover data in case the upgrade fails.
- Perform the pre-upgrade tasks that are described for standalone or primary-standby environments, which include tasks such as ensuring that the server meets the minimum disk space requirements by adding a new disk to extend
vg_root, ensuring that no full or incremental backup jobs are running, planning for any down time, and disabling STIG. (To disable STIG, asroot, execute the following command:/usr/local/dbfw/bin/stig --apply --disable) Adding a new disk to a multi-master cluster node requires that the node be disabled before it is shut down to add the new disk, and then enabled again after the disk has been successfully added. - Check the disk size before you begin the upgrade. If any of the nodes in question have a disk size that is greater than 2 TB, then you cannot upgrade that system to the new release. Oracle recommends that you remove the node from the cluster and if possible, replace it with a node whose disk is less than 2 TB in size.
- Increase the Maximum Disable Node Duration setting as appropriate so that any disabled cluster nodes have sufficient time to be upgraded then enabled back into the cluster. Note that increasing the Maximum Disable Node Duration setting also increases disk space usage.
Related Topics
4.6.3 Step 2: Add Disk Space to Extend the vg_root for Upgrade to Oracle Key Vault Release 21.1
To upgrade to Oracle Key Vault release 21.1, you will need additional disk space by adding an additional disk to be able to extend the vg_root.
Related Topics
4.6.4 Step 3: Upgrade Multi-Master Clusters
Depending on your multi-master cluster configuration, you must follow the steps that are specific to your deployment.
- About Upgrading Multi-Master Clusters
When upgrading a multi-master cluster, you may upgrade the read-only nodes one after the other and in the case of read-write pairs, you must upgrade both of the nodes simultaneously. - Upgrading Multi-Master Cluster Read-Only Nodes
Before upgrading multi-master cluster read-only nodes, ensure that you understand the requirements for performing this kind of upgrade. - Upgrading Multi-Master Cluster Read-Write Pairs
Before upgrading multi-master cluster read-write pairs, ensure that you understand the requirements for performing this kind of upgrade.
4.6.4.1 About Upgrading Multi-Master Clusters
When upgrading a multi-master cluster, you may upgrade the read-only nodes one after the other and in the case of read-write pairs, you must upgrade both of the nodes simultaneously.
To perform the upgrade, you must upgrade each multi-master cluster node. There are different steps for upgrading the multi-master cluster depending on your deployment. A two-node cluster, running Oracle Key Vault release 18.5 or earlier, configured as a single read-write pair would involve running a pre-upgrade script which no other deployment requires. For multi-master cluster nodes that were deployed in a read-write configuration, you must follow different upgrade steps than those that were deployed as read-only nodes.
This section describes the upgrade methods for the various deployments. Choose the method that is appropriate for your configuration. When upgrading read-write pairs, after disabling both the nodes, you can upgrade the nodes at the same time. However, Oracle recommends that you upgrade the cluster nodes one at a time. If you have a multi-master cluster with three or more nodes, then you can upgrade two nodes at the same time with no down time.
When upgrading read-write pairs, it is critically important that you perform the steps in the proper order on the two nodes.
If your cluster consists of only two nodes in a read-write configuration and if you are upgrading from Oracle Key Vault release 18.2 through 18.5, then you must execute a pre-upgrade script before performing the upgrade. The pre-upgrade script is not to be executed in any other multi-master cluster configuration.
Parent topic: Step 3: Upgrade Multi-Master Clusters
4.6.4.2 Upgrading Multi-Master Cluster Read-Only Nodes
Before upgrading multi-master cluster read-only nodes, ensure that you understand the requirements for performing this kind of upgrade.
Related Topics
- Step 1: Perform Pre-Upgrade Tasks
- Upgrading a Standalone Oracle Key Vault Server
- Step 2: Add Disk Space to Extend the vg_root for Upgrade to Oracle Key Vault Release 21.1
- Disabling a Cluster Node
- Step 4: Upgrade the Oracle Key Vault Server or Primary-Standby Pair
- Upgrading a Standalone or Primary-Standby Oracle Key Vault Server
- Enabling a Disabled Cluster Node
Parent topic: Step 3: Upgrade Multi-Master Clusters
4.6.4.3 Upgrading Multi-Master Cluster Read-Write Pairs
Before upgrading multi-master cluster read-write pairs, ensure that you understand the requirements for performing this kind of upgrade.
Do not perform any critical operations or make configuration changes to Oracle Key Vault until you have completed upgrading all multi-master cluster nodes.
You must perform these steps on both nodes of the cluster read-write pair in the order specified for all read-write pairs of your cluster. In order to perform the upgrade using this method, you must arbitrarily decide which of the read-write nodes of your pair will be Node A and which node will be Node B. The steps below will refer to Node A and Node B which correspond to your Node A and Node B.
Direct upgrades to Oracle Key Vault 21.2 from releases 18.1 or earlier are not supported. You must upgrade to Oracle Key Vault release 18.2 or later before upgrading to release 21.2. If you are upgrading a two-node cluster that runs Oracle Key Vault release 18.5 or earlier and is configured as a single read-write pair, then you must run the pre-upgrade script on each multi-master cluster node after mounting the ISO, but before performing the full upgrade.
Generally, once your cluster nodes are disabled, they become unavailable for use. Therefore, in order to allow operational continuity when you upgrade a two-node cluster that is configured as a read-write pair, applying the pre-upgrade script on both nodes allows the node to remain available in a read-only mode, even when the node is disabled. After both the nodes are disabled, you can upgrade the nodes one at a time; the order is at your discretion. However, when you enable the nodes after they have been upgraded, you must enable them in the reverse order that they were disabled.
If your deployment required running the pre-upgrade script, then after you run the pre-upgrade script, proceed with the standard upgrade process as follows. Disable both nodes (the order of disabling matters) of the read-write pair, add the extra disk space as necessary and then perform the upgrade and reboot. When you run the upgrade and reboot commands, Oracle recommends running them on one node of the pair before running it on the other node to avoid down time.
Related Topics
Parent topic: Step 3: Upgrade Multi-Master Clusters
4.6.5 Step 4: Check the Node Version and the Cluster Version
After you complete the upgrade of at least one node, you can log into any of the upgraded nodes to check the node and cluster versions.
- Log in to the Oracle Key Vault management console as a user who has the System Administrator role.
- Select the Cluster tab.
- In the left navigation bar, select Management.
- Check the following areas:
- To find the node version, check the Cluster Details area.
- To find the cluster version, check the Cluster Information area.
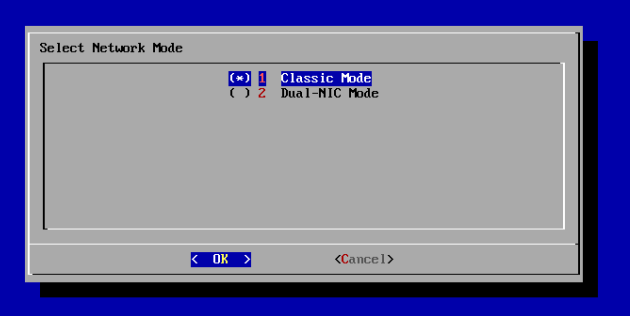
4.6.6 Step 5: If Necessary, Change the Network Interface for Upgraded Nodes
Nodes that were created in Oracle Key Vault releases earlier than release 21.1 use Classic mode, in which only one network interface was used.
If you prefer to use dual NIC network mode, which supports the use two network interfaces, then you can switch the node to use this mode, from the command line.
Related Topics
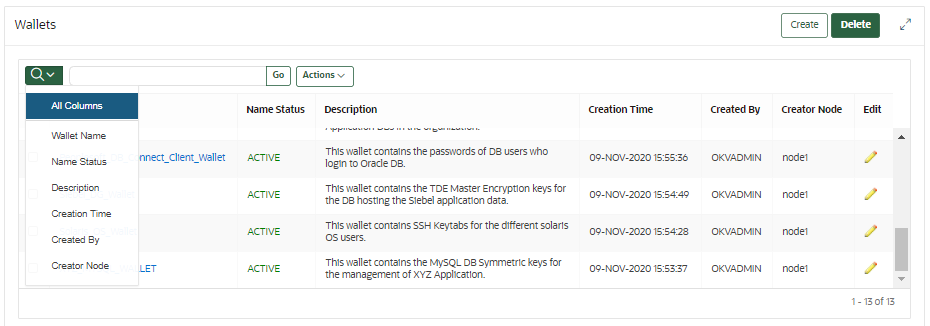
4.7 Overview of the Oracle Key Vault Management Console
The Oracle Key Vault management console provides a graphical user interface for Oracle Key Vault users.
The Oracle Key Vault management console is a browser-based console that connects to the server using the https secure communication channel. It provides the graphical user interface for Oracle Key Vault, where users can perform tasks such as the following:
-
Setting up and managing the cluster
-
Creating and managing users, endpoints, and their respective groups
-
Creating and managing virtual wallets and security objects
-
Setting system settings, like network and other services
-
Setting up primary-standby
-
Performing backups
Parent topic: Oracle Key Vault Installation and Configuration
4.8 Performing Actions and Searches
The Oracle Key Vault management console enables you to perform standard actions and search operations, as well as get help information.
Many of the tab and menu pages contain an Actions menu or Search bars that allow you to search and perform actions on lists and the results of searches. The Help selection of the Actions list provides detailed help for using these features.
- Actions Menus
The actions available from an Actions drop-down menu can vary but typically include a set of standard menu items. - Search Bars
Along with Actions menus, many tabs in the Oracle Key Vault management console contain search bars.
Parent topic: Oracle Key Vault Installation and Configuration
4.8.1 Actions Menus
The actions available from an Actions drop-down menu can vary but typically include a set of standard menu items.
These items are as follows:
-
Select Columns: Select which column should be displayed.
-
Filter: Filter by column or row and a user-defined expression.
-
Rows Per Page: Choose how many rows you want to view .
-
Format: Choose formatting such as Sort, Control Break, Highlight, Compute, Aggregate, Chart, and Group By.
-
Save Report: Save reports.
-
Reset: Reset the report settings, removing any customizations.
-
Help: Get information about these actions.
-
Download: Download the result set in CSV or HTML.
Parent topic: Performing Actions and Searches
4.8.2 Search Bars
Along with Actions menus, many tabs in the Oracle Key Vault management console contain search bars.
Parent topic: Performing Actions and Searches