9 Configuring Secure Application Roles for Oracle Database Vault
Secure application roles enable you to control how much access users have to an application.
- What Are Secure Application Roles in Oracle Database Vault?
In Oracle Database Vault, you can create a secure application role that you enable with an Oracle Database Vault rule set. - Creating an Oracle Database Vault Secure Application Role
You can create a Database Vault secure application role in Database Vault Administrator. - Enabling Oracle Database Secure Application Roles to Work with Oracle Database Vault
You can modify an existing secure application role only if it has been created in Oracle Database Vault. - Security for Oracle Database Vault Secure Application Roles
Users who have database administrative privileges may try to use theDROP ROLEstatement to delete Oracle Database Vault secure application roles. - Deleting an Oracle Database Vault Secure Application Role
You can delete Oracle Database Vault secure application roles in Oracle Database Vault Administrator. - How Oracle Database Vault Secure Application Roles Work
The process flow for an Oracle Database Vault secure application role begins after you create and set the secure application role. - Tutorial: Granting Access with Database Vault Secure Application Roles
This tutorial demonstrates how to create a secure application role to control user access to theOE.ORDERStable during work hours. - How Secure Application Roles Affect Performance
You can check system performance by Oracle Enterprise Manager Cloud Control. - Secure Application Role Related Reports and Data Dictionary View
Oracle Database Vault provides reports and a data dictionary view that you can use to analyze Oracle Database Vault secure application roles.
9.1 What Are Secure Application Roles in Oracle Database Vault?
In Oracle Database Vault, you can create a secure application role that you enable with an Oracle Database Vault rule set.
Regular Oracle Database secure application roles are enabled by custom PL/SQL procedures. You use secure application roles to prevent users from accessing data from outside an application. This forces users to work within the framework of the application privileges that have been granted to the role.
In a multitenant environment, you only can create a secure application role in a PDB, not in the CDB root or the application root.
The advantage of basing database access for a role on a rule set is that you can store database security policies in one central place, as opposed to storing them in all your applications. Basing the role on a rule set provides a consistent and flexible method to enforce the security policies that the role provides. In this way, if you must update the security policy for the application role, you do it in one place, the rule set. Furthermore, no matter how the user connects to the database, the result is the same, because the rule set is bound to the role. All you need to do is to create the role and then associate it with a rule set. The associated rule set validates the user who is trying to enable the role.
Related Topics
9.2 Creating an Oracle Database Vault Secure Application Role
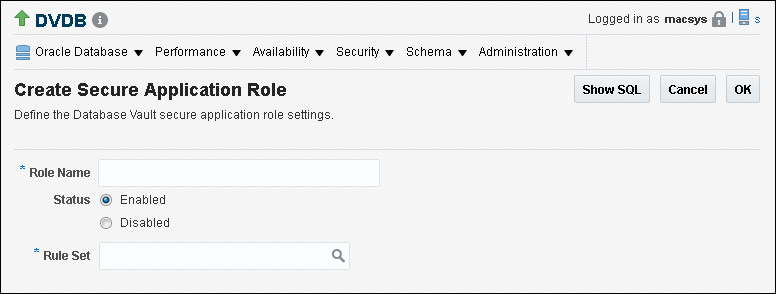
You can create a Database Vault secure application role in Database Vault Administrator.
9.3 Enabling Oracle Database Secure Application Roles to Work with Oracle Database Vault
You can modify an existing secure application role only if it has been created in Oracle Database Vault.
Related Topics
9.4 Security for Oracle Database Vault Secure Application Roles
Users who have database administrative privileges may try to use the DROP ROLE statement to delete Oracle Database Vault secure application roles.
Whenever an Oracle Database Vault secure application role has been created, Database Vault adds the secure application role to the Oracle Database Vault realm. This prevents database administrator from deleting the secure application role using the DROP ROLE statement.
9.5 Deleting an Oracle Database Vault Secure Application Role
You can delete Oracle Database Vault secure application roles in Oracle Database Vault Administrator.
- Log in to Oracle Database Vault Administrator from Cloud Control as a user who has been granted the
DV_OWNERorDV_ADMINrole and theSELECT ANY DICTIONARYprivilege. Logging into Oracle Database Vault explains how to log in. - If necessary, locate the various references to the secure application roles by querying the role-related Oracle Database Vault views.
- Check and modify any applications that may be using the secure application role that you want to delete.
- In the Administration page, under Database Vault Components, click Secure Application Roles.
- In the Secure Application Roles page, select the role that you want to remove.
- Click Delete.
- In the Confirmation window, click Yes.
Related Topics
9.6 How Oracle Database Vault Secure Application Roles Work
The process flow for an Oracle Database Vault secure application role begins after you create and set the secure application role.
-
Create or update the role either in Oracle Database Vault Administrator or by using the secure application role-specific functions in the
DBMS_MACADMpackage.See DBMS_MACADM Secure Application Role Procedures for more information.
-
Modify your application to call the role, by using the
DBMS_MACSEC_ROLES.SET_ROLEfunction.See SET_ROLE Procedure for more information.
-
Oracle Database Vault then evaluates the rule set associated with the secure application role.
If the rule set evaluates to true, then Oracle Database Vault enables the role for the current session. If the rule set evaluates to false, the role is not enabled. In either case, Oracle Database Vault processes the associated auditing and custom event handlers for the rule set associated with the secure application role.
9.7 Tutorial: Granting Access with Database Vault Secure Application Roles
This tutorial demonstrates how to create a secure application role to control user access to the OE.ORDERS table during work hours.
- About This Tutorial
In this tutorial, you restrict theSELECTstatement on theORDERStable in theOEschema to a specific set of users. - Step 1: Create Users for This Tutorial
First, you must create users for the tutorial. - Step 2: Enable the OE User Account
TheOEschema will be used for this tutorial. - Step 3: Create the Rule Set and Its Rules
The rule set and rules will restrict who can modify orders in theOE.ORDERStable. - Step 4: Create the Database Vault Secure Application Role
The Database Vault secure application role will be set when the rule set conditions are satisfied. - Step 5: Grant the SELECT Privilege to the Secure Application Role
The secure application role must be granted theSELECTprivilege. - Step 6: Test the Database Vault Secure Application Role
With all the components in place, you can test the Database Vault secure application role. - Step 7: Remove the Components for This Tutorial
You can remove the components that you created for this tutorial if you no longer need them.
9.7.1 About This Tutorial
In this tutorial, you restrict the SELECT statement on the ORDERS table in the OE schema to a specific set of users.
Furthermore, these users can only perform these statements on the OE.ORDERS table from within the office, not from a remote connection. To accomplish this, you create an Oracle Database Vault secure application role that is enabled for the user only if the user passes the checks enforced by the rule set that you associate with the secure application role.
9.7.4 Step 3: Create the Rule Set and Its Rules
The rule set and rules will restrict who can modify orders in the OE.ORDERS table.
9.7.5 Step 4: Create the Database Vault Secure Application Role
The Database Vault secure application role will be set when the rule set conditions are satisfied.
At this stage, the Database Vault secure application role and its associated rule set are created, though the role does not yet have any privileges.
9.7.6 Step 5: Grant the SELECT Privilege to the Secure Application Role
The secure application role must be granted the SELECT privilege.
9.7.7 Step 6: Test the Database Vault Secure Application Role
With all the components in place, you can test the Database Vault secure application role.
9.8 How Secure Application Roles Affect Performance
You can check system performance by Oracle Enterprise Manager Cloud Control.
Other tools that you can use are Automatic Workload Repository (AWR) and TKPROF.
See Also:
-
Oracle Database Performance Tuning Guide to learn how to monitor database performance
-
Oracle Database SQL Tuning Guide to monitor the performance of individual SQL and PL/SQL statements
9.9 Secure Application Role Related Reports and Data Dictionary View
Oracle Database Vault provides reports and a data dictionary view that you can use to analyze Oracle Database Vault secure application roles.
Table 9-1 lists the Oracle Database Vault reports. See Oracle Database Vault Reports for information about how to run these reports.
Table 9-1 Reports Related to Secure Application Roles
| Report | Description |
|---|---|
|
Lists audit records generated by the Oracle Database Vault secure application role-enabling operation. To generate this type of audit record, enable auditing for the rule set associated with the role. |
|
|
Lists secure application roles that have nonexistent database roles, or incomplete or disabled rule sets |
|
|
Lists rule sets that have no rules defined or enabled, which may affect the secure application roles that use them |
|
|
Provides information about powerful database accounts and roles |
You can use the DBA_DV_ROLE data dictionary view to find the Oracle Database Vault secure application roles used in privilege management. See DBA_DV_ROLE View for more information.