12 DBA Operations in an Oracle Database Vault Environment
Database administrators can perform operations in an Oracle Database Vault environment, such as using Database Vault with products such as Oracle Data Pump.
- Handling Role Grants in Oracle Database Vault
Oracle Database Vault protects default roles such asRESOURCE,DBA,AUDIT_ADMIN, andPDB_DBA, which are created when you install Oracle Database. This feature protects the system and object privileges that are granted to these roles - Performing DDL Operations in Oracle Database Vault
Data Definition Language (DDL) operations in Oracle Database Vault can be affected by situations such as schema ownership and patch upgrades. - Using Oracle Database Vault with Oracle Enterprise Manager
Oracle Database Vault administrators can perform tasks in Oracle Enterprise Manager Cloud Control such as propagating polices to other databases. - Using Oracle Data Pump with Oracle Database Vault
Database administrators can authorize Oracle Data Pump users to work in a Database Vault environment. - Using Oracle Scheduler with Oracle Database Vault
Users who are responsible for scheduling database jobs must have Oracle Database Vault-specific authorization. - Using Information Lifecycle Management with Oracle Database Vault
Users who perform Information Lifecycle Management operations on an Oracle Database Vault-enabled database must be granted authorization to perform these operations. - Using Oracle Database Replay with Oracle Database Vault
Database administrators can authorize Oracle Database Replay users to work in a Database Vault environment. - Running Preprocessor Programs with Oracle Database Vault
Users who run preprocessor programs through external tables must have Oracle Database Vault-specific authorization. - Using Database Vault Operations Control to Restrict Multitenant Common User Access to Local PDB Data
You can control PDB access by CDB root common users, such as infrastructure database administrators. - Preventing Multitenant Local Users from Blocking Common Operations
You can prevent multitenant local users from blocking common operations when they attempt to create Oracle Database Vault protections on common user objects. - Oracle Recovery Manager and Oracle Database Vault
You can use Recovery Manager (RMAN) in an Oracle Database Vault environment. - Privileges for Using XStream with Oracle Database Vault
If you want to use XStream in an Oracle Database Vault environment, then you must have the appropriate privileges. - Privileges for Using Oracle GoldenGate with Oracle Database Vault
If you want to use Oracle GoldenGate in an Oracle Database Vault environment, then you must have the appropriate privileges. - Using Data Masking in an Oracle Database Vault Environment
You must have the correct authorization to perform data masking in an Oracle Database Vault environment. - Converting a Standalone Oracle Database to a PDB and Plugging It into a CDB
You can convert a standalone Oracle Database database from release 12c through 19c to a PDB, and then plug this PDB into a CDB. - Using the ORADEBUG Utility with Oracle Database Vault
TheORADEBUGutility is used primarily by Oracle Support to diagnose problems that may arise with an Oracle database. - Performing Patch Operations in an Oracle Database Vault Environment
UserSYSmust have theDV_PATCH_ADMINrole to perform a patch operations on an Oracle Database Vault-enabled database.
12.1 Handling Role Grants in Oracle Database Vault
Oracle Database Vault protects default roles such as RESOURCE, DBA, AUDIT_ADMIN, and PDB_DBA, which are created when you install Oracle Database. This feature protects the system and object privileges that are granted to these roles
- Identifying Roles That Are Protected by a Realm
As a user who has been granted theDV_OWNERorDV_ADMINrole, you can identify which roles are protected by which realm. - Identifying Roles That Are Not Protected by a Realm
As a user who has been granted theDV_OWNERorDV_ADMINrole, you can identify which roles are not protected by realms. - Handling Protected Role Grants for Named Users
If you are using named accounts, which Oracle recommends, and you must grant a protected role to another user, then you must authorize each named account by adding it to the appropriate realm as a realm owner. - Identifying Realms and Roles Protected by a Realm to Which SYS Has Authorization
As a user who has been granted theDV_OWNERorDV_ADMINrole, you can identify the Oracle Database Vault realms and roles that are protected by a realm to whichSYShas authorization.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.1.1 Identifying Roles That Are Protected by a Realm
As a user who has been granted the DV_OWNER or DV_ADMIN role, you can identify which roles are protected by which realm.
Perform the following query:
COLUMN "ROLE PROTECTED BY A DV REALM" FORMAT A35
SELECT REALM_NAME, OBJECT_NAME
AS "ROLE PROTECTED BY A DV REALM"
FROM DBA_DV_REALM_OBJECT
WHERE OBJECT_TYPE = 'ROLE'
ORDER BY 1, 2;Parent topic: Handling Role Grants in Oracle Database Vault
12.1.2 Identifying Roles That Are Not Protected by a Realm
As a user who has been granted the DV_OWNER or DV_ADMIN role, you can identify which roles are not protected by realms.
Perform the following query:
COLUMN "ROLE NOT PROTECTED BY A DV REALM" FORMAT A40
SELECT ROLE AS "ROLE NOT PROTECTED BY A DV REALM"
FROM DBA_ROLES
WHERE ROLE NOT IN (SELECT OBJECT_NAME FROM DBA_DV_REALM_OBJECT WHERE OBJECT_TYPE = 'ROLE')
ORDER BY 1;Parent topic: Handling Role Grants in Oracle Database Vault
12.1.3 Handling Protected Role Grants for Named Users
If you are using named accounts, which Oracle recommends, and you must grant a protected role to another user, then you must authorize each named account by adding it to the appropriate realm as a realm owner.
For example, if dba_debra wants to grant the PDB_DBA role to dba_harvey, then the following error will occur if the realm authorizations are not in place for dba_debra:
GRANT PDB_DBA TO DBA_HARVEY;
ERROR at line 1: ORA-47410: Insufficient realm privileges to GRANT on PDB_DBA. As a user with the DV_OWNER or DV_ADMIN role, identify the Database Vault realm that is protecting the PDB_DBA role by performing the following query. This example uses the PDB_DBA role in its query.
SELECT REALM_NAME FROM DBA_DV_REALM_OBJECT
WHERE OBJECT_NAME = 'PDB_DBA' AND OBJECT_TYPE = 'ROLE';Output similar to the following appears:
REALM_NAME
--------------------------------------------------
Oracle System Privilege and Role Management RealmAs that same user, add dba_debra to the Oracle System Privilege and Role Management Realm as an owner.
BEGIN
DBMS_MACADM.ADD_AUTH_TO_REALM (
REALM_NAME => 'Oracle System Privilege and Role Management Realm',
GRANTEE => 'DBA_DEBRA',
RULE_SET_NAME => NULL,
AUTH_OPTIONS => DBMS_MACUTL.G_REALM_AUTH_OWNER);
END;
/ Now, when dba_debra attempts to grant the PDB_DBA role to another user, the role grant will succeed:
GRANT PDB_DBA TO DBA_HARVEY;
Grant succeeded.To revoke the authorization from dba_debra:
BEGIN
DBMS_MACADM.DELETE_AUTH_FROM_REALM (
REALM_NAME => 'Oracle System Privilege and Role Management Realm',
GRANTEE => 'DBA_DEBRA');
END;
/ Note that SYS has been granted owner authorization on many of the default Database Vault realms. You can use SYS to perform the GRANT commands. Oracle recommends that you create named accounts (for example, pfitch, cabramowitz) for each user instead of relying on shared accounts such as SYS or SYSTEM. Named users will also make it easier to identify who performed an action in the Oracle database.
Parent topic: Handling Role Grants in Oracle Database Vault
12.1.4 Identifying Realms and Roles Protected by a Realm to Which SYS Has Authorization
As a user who has been granted the DV_OWNER or DV_ADMIN role, you can identify the Oracle Database Vault realms and roles that are protected by a realm to which SYS has authorization.
Perform the following query:
SELECT REALM_NAME, OBJECT_NAME
FROM DBA_DV_REALM_OBJECT
WHERE OBJECT_TYPE = 'ROLE' AND REALM_NAME IN (SELECT REALM_NAME FROM DBA_DV_REALM_AUTH WHERE GRANTEE = 'SYS')
ORDER BY 1,2;To identify only the realms, you can perform a query similar to the following:
SELECT DISTINCT REALM_NAME
FROM DBA_DV_REALM_OBJECT
WHERE OBJECT_TYPE = 'ROLE' AND REALM_NAME IN (SELECT REALM_NAME FROM DBA_DV_REALM_AUTH WHERE GRANTEE = 'SYS')
ORDER BY 1;To identify the realms in that SYS does not have authorization for, you can perfrom a query similar to the following:
SELECT DISTINCT REALM_NAME
FROM DBA_DV_REALM_OBJECT
WHERE OBJECT_TYPE = 'ROLE' AND REALM_NAME NOT IN (SELECT REALM_NAME FROM DBA_DV_REALM_AUTH WHERE GRANTEE = 'SYS')
ORDER BY 1;Parent topic: Handling Role Grants in Oracle Database Vault
12.2 Performing DDL Operations in Oracle Database Vault
Data Definition Language (DDL) operations in Oracle Database Vault can be affected by situations such as schema ownership and patch upgrades.
- Restrictions on Performing DDL Operations in Oracle Database Vault
Depending on the Oracle Database Vault configuration, DDL operations may be restricted and require DDL authorizations in an Oracle Database Vault environment. - Impact of the DV_PATCH_ADMIN Role on DDL Operations
Object owners and users who have been granted theDV_PATCH_ADMINrole are exempt from the DDL authorization requirement. - Impact of Upgrades from Releases 21c and Earlier on DDL Operations
If you upgrade Oracle Database Vault from release 21c or earlier, you may need to change the DDL authorizations. - Impact of the Removal of the DDL Default Authorization of ('%', '%')
The DDL default authorization of ('%', '%') enables a user to perform DDL operations on any schema without explicit DDL authorizations.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.2.1 Restrictions on Performing DDL Operations in Oracle Database Vault
Depending on the Oracle Database Vault configuration, DDL operations may be restricted and require DDL authorizations in an Oracle Database Vault environment.
Specifically, a user is required to have DDL authorization to perform DDL operations on a schema that has any of the following characteristics:
- The schema is an owner of objects that are protected by enabled realms.
- The schema is authorized to any enabled realm directly or through roles.
- The schema is granted object privileges directly or through roles on objects that are protected by enabled realms.
- The schema is granted any Oracle Database Vault roles directly or through roles.
Object owners and users who have granted the DV_PATCH_ADMIN role are exempt from the DDL authorization requirement. You can authorize a user to perform DDL operations on a specific schema by using the DBMS_MACADM.AUTHORIZE_DDL procedure. Note, however, that DDL authorization does not enable the grantee to perform DDL operations on a realm protected object or schema. To enable such operations, you must authorize the user to the realm. To find information about users who have been granted this authorization, query the DBA_DV_DDL_AUTH data dictionary view.
If Oracle Database Vault is upgraded from a previous release older than Oracle Database 21c, then the default DDL authorization of (%, %) may exist, and it would enable users to perform DDL operations on any schema without explicit DDL authorizations. For better security, Oracle recommends that you remove the default DDL authorization by running DBMS_MACADM.UNAUTHORIZE_DDL('%', '%') and grant required DDL authorizations only to users who need to perform DDL operations.
Related Topics
Parent topic: Performing DDL Operations in Oracle Database Vault
12.2.2 Impact of the DV_PATCH_ADMIN Role on DDL Operations
Object owners and users who have been granted the DV_PATCH_ADMIN role are exempt from the DDL authorization requirement.
You can authorize a user to perform DDL operations on a specific schema by using the DBMS_MACADM.AUTHORIZE_DDL procedure. Note, however, that DDL authorization does not allow the grantee to perform DDL operations on a realm-protected object or schema. To allow such operations, you must authorize the user for the realm. To find information about users who have been granted this authorization, query the DBA_DV_DDL_AUTH data dictionary view.
Related Topics
Parent topic: Performing DDL Operations in Oracle Database Vault
12.2.3 Impact of Upgrades from Releases 21c and Earlier on DDL Operations
If you upgrade Oracle Database Vault from release 21c or earlier, you may need to change the DDL authorizations.
The default DDL authorization of ('%', '%') may exist, which enables users to perform DDL operations on any schema without explicit DDL authorizations. For better security, Oracle recommends that you remove the default DDL authorization by running DBMS_MACADM.UNAUTHORIZE_DDL('%', '%') and then grant required DDL authorizations only to users who need to perform DDL operations.
Related Topics
Parent topic: Performing DDL Operations in Oracle Database Vault
12.2.4 Impact of the Removal of the DDL Default Authorization of ('%', '%')
The DDL default authorization of ('%', '%') enables a user to perform DDL operations on any schema without explicit DDL authorizations.
This default DDL authorization, which has been in place since DDL authorization was introduced in Oracle Database release 12.1, was to prevent any undesirable disruption due to unexpected DDL failures in the Oracle Database Vault environment. From Database Vault release 21c, however, there is no default DDL authorization, and the existing default DDL authorization of ('%', '%') is removed when Database Vault is upgraded to 21c or later. To prevent any problems, you need to identify and authorize trusted database users for DDL operations or optionally re-authorize ('%', '%') so that every user is allowed to perform DDL operations without explicit authorization. For better security, Oracle recommends that only trusted users are authorized for DDL operations.
Related Topics
Parent topic: Performing DDL Operations in Oracle Database Vault
12.3 Using Oracle Database Vault with Oracle Enterprise Manager
Oracle Database Vault administrators can perform tasks in Oracle Enterprise Manager Cloud Control such as propagating polices to other databases.
- Propagating Oracle Database Vault Configurations to Other Databases
You can propagate Database Vault configurations (such as a realm configuration) to other Database Vault-protected databases. - Enterprise Manager Cloud Control Alerts for Oracle Database Vault Policies
To view Oracle Database Vault alerts, you must be granted theDV_OWNER,DV_ADMIN, orDV_SECANALYSTrole. - Oracle Database Vault-Specific Reports in Enterprise Manager Cloud Control
From the Database Vault home page, you can find information about violations.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.3.1 Propagating Oracle Database Vault Configurations to Other Databases
You can propagate Database Vault configurations (such as a realm configuration) to other Database Vault-protected databases.
-
Log in to Oracle Database Vault Administrator from Cloud Control as a user who has been granted the
DV_OWNERorDV_ADMINrole and theSELECT ANY DICTIONARYprivilege. Logging in to Oracle Database Vault from Oracle Enterprise Cloud Control explains how to log in. -
In the Database Vault home page, under Database Vault Policy Propagation, select Database Vault Policy Propagation.
The Available Policies area in the Policy Propagation subpage lists a summary of the Oracle Database Vault configurations that were created for the current database: that is, configurations that were created for realms, command rules, rule sets, and secure application roles. It does not list the Oracle Database Vault policies that were introduced in Oracle Database release 12c (12.2). From here, you can propagate these configurations to another database.
-
Under Available Policies, select each configuration that you want to propagate to another database.
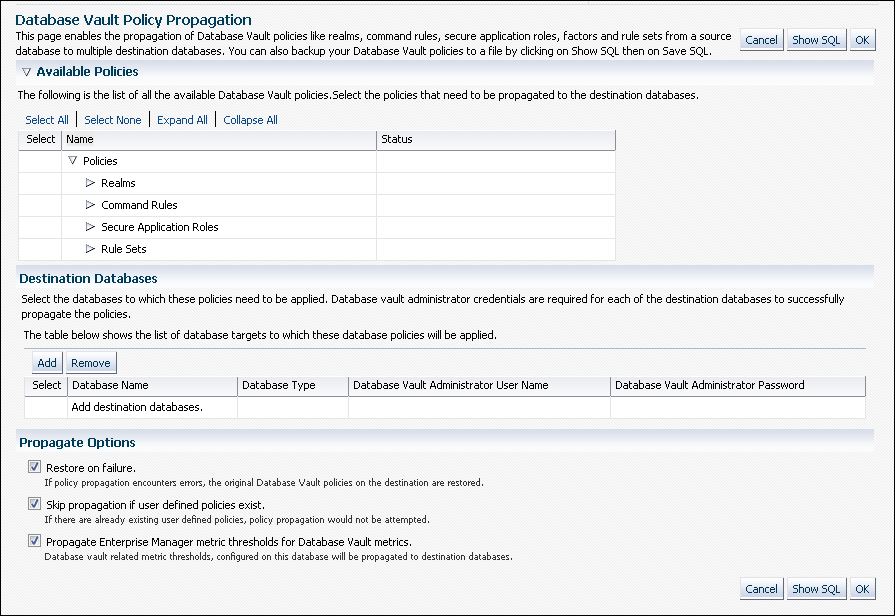
Description of the illustration policy_propagation122.png -
Under Destination Databases, click the Add button.
-
Under Search and Select: Database Vault Enabled Destination Databases, search for the destination databases, and then select each database to which you want to propagate the configurations. Then click the Select button.
-
Under Destination Databases, do the following:
-
Under Apply credentials across destination database(s), enter the user name and password of the administrator of the Database Vault database that contains the configurations you want to propagate.
This feature applies the Database Vault administrator's user name and password to all of the selected destination databases.
-
Select each database to which you want to propagate the configurations.
-
Enter the Database Vault administrator user name and password for each database.
-
Click the Apply button.
-
-
In the Propagate Options page, select from the following options.
Any changes made to the seeded realms, command rules, rule sets, and so on will not be propagated to the destination databases. Only custom-created data are propagated.
-
Restore on failure: If the propagation operations encounters errors, then the propagation is rolled back. That is, the original policies on the destination database are restored. If you do not select this option, then the policy propagation on the destination database continues and ignores any errors.
-
Skip propagation if user defined policies exist: If the destination databases already have the user-defined configurations, then the propagation operation is not attempted. If you do not select this option, then regardless of whether user-defined policies exist on the destination database, all the existing configurations are cleared, and the configurations from the source database are applied to the destination database.
-
Propagate Enterprise Manager metric thresholds for database vault metrics: If the source database has Oracle Database Vault metric thresholds set, then these thresholds are also propagated to the destination databases. If you do not select this option, then only configurations are propagated and not the Oracle Database Vault thresholds.
-
-
Click the OK button.
-
In the Confirmation window, click OK.
A message indicating success or failure appears. If the propagation succeeds, then the configurations are active right away in their destination databases.
12.3.2 Enterprise Manager Cloud Control Alerts for Oracle Database Vault Policies
To view Oracle Database Vault alerts, you must be granted the DV_OWNER, DV_ADMIN, or DV_SECANALYST role.
The alerts are as follows:
-
Database Vault Attempted Realm Violations. This alert helps the Oracle Database Vault security analyst (
DV_SECANALYSTrole) to monitor violation attempts on the Database Vault database. This user can select the realms to be affected by the alert and filter these realms based on the different types of attempts by using error codes. You can enable this metric from the Metrics and Policy Settings page. By default, the attempted realm violations are collected every 24 hours. -
Database Vault Attempted Command Rule Violations. The functionality for this alert is the same as for Database Vault Attempted Realm Violations, except that it focuses on violations on command rules.
-
Database Vault Realm Configuration Issues. This metric tracks and raises an alert if users misconfigure realms. This metric is enabled when you install Oracle Database vault, and by default it collects data every one hour.
-
Database Vault Command Rule Configuration Issues. This functionality for this alert is that same as Database Vault Realm Configuration Issues, except that it focuses on configuration changes to command rules.
-
Database Vault Policy Changes. This metric raises an alert on any change to any Database Vault policy, such as policies for realms and command rules. It provides a detailed policy changes report.
12.3.3 Oracle Database Vault-Specific Reports in Enterprise Manager Cloud Control
From the Database Vault home page, you can find information about violations.
These violations are as follows:
-
Top five attempted violations on realm and command rule
-
Top five attempted violations by database users and client host
-
Time series-based graphical reports on attempted violations for more detailed analysis
To have full access to the Database Vault reports, you must log into Database Vault Administrator as a user who has been granted the DV_OWNER, DV_ADMIN, or DV_SECANALYST role.
Related Topics
12.4 Using Oracle Data Pump with Oracle Database Vault
Database administrators can authorize Oracle Data Pump users to work in a Database Vault environment.
- About Using Oracle Data Pump with Oracle Database Vault
Oracle Data Pump is used to unload data and metadata into a set of operating system files and dump files. Oracle Database Vault enables you to control which privileged users are authorized to perform Data Pump imports or exports. - Authorizing Users or Roles for Data Pump Regular Export and Import Operations
You can use different authorization types for administrators who perform Oracle Data Pump export and import operations in a Database Vault environment. - Authorizing Users or Roles for Data Pump Transportable Export and Import Operations
You can grant authorization levels for users who must perform Oracle Data Pump transportable operations, either directly or through a role. - Guidelines for Exporting or Importing Data in a Database Vault Environment
After you grant the Oracle Data Pump database administrator the proper authorization, this user can perform any export or import operations that are necessary.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.4.1 About Using Oracle Data Pump with Oracle Database Vault
Oracle Data Pump is used to unload data and metadata into a set of operating system files and dump files. Oracle Database Vault enables you to control which privileged users are authorized to perform Data Pump imports or exports.
This type of user must have Database Vault privileges in addition to the standard Oracle Data Pump privileges. If these users want to perform Oracle Data Pump transportable tablespace operations, then they must have special authorization. You can check a user's authorizations for using Data Pump in an Oracle Database Vault environment by querying the DBA_DV_DATAPUMP_AUTH data dictionary view. You can grant this authorization to either individual users or to database roles.
Parent topic: Using Oracle Data Pump with Oracle Database Vault
12.4.2 Authorizing Users or Roles for Data Pump Regular Export and Import Operations
You can use different authorization types for administrators who perform Oracle Data Pump export and import operations in a Database Vault environment.
- About Authorizing Users or Roles for Oracle Data Pump Regular Operations
Users who have Oracle Data Pump authorization can perform regular Oracle Data Pump operations in a Database Vault environment. - Levels of Database Vault Authorization for Oracle Data Pump Regular Operations
Oracle Database Vault provides several levels of authorization required for Oracle Data Pump regular operations in a Database Vault environment. - Authorizing Users or Roles for Oracle Data Pump Regular Operations in Database Vault
You can authorize a database administrator or a role to use Data Pump for regular operations in an Oracle Database Vault environment. - Revoking Oracle Data Pump Authorization from Users or Roles
You can revoke authorization from the database administrator or role who is using Oracle Data Pump for regular operations.
Parent topic: Using Oracle Data Pump with Oracle Database Vault
12.4.2.1 About Authorizing Users or Roles for Oracle Data Pump Regular Operations
Users who have Oracle Data Pump authorization can perform regular Oracle Data Pump operations in a Database Vault environment.
You can perform the following types of Oracle Data Pump authorizations:
- Authorizing the user or role to be able to import protected schemas and objects
- Authorizing the user or role to be able to perform following activities that can take place during the import operation: the creation of users, the grant of Oracle Database Vault-protected roles and system privileges, the grant of specific Oracle Database roles, and the grant of Oracle Database system privileges
Note:
Full level Data Pump authorization enables these users to perform transportable export and import operations as well.12.4.2.2 Levels of Database Vault Authorization for Oracle Data Pump Regular Operations
Oracle Database Vault provides several levels of authorization required for Oracle Data Pump regular operations in a Database Vault environment.
Table 12-1 describes these levels.
Table 12-1 Levels of Authorization for Oracle Data Pump Regular Operations
| Scenario | Authorization Required |
|---|---|
|
A database administrator wants to import data into another schema. |
You must grant this user (or a role) the |
|
A database administrator wants to export or import data in a schema that has no Database Vault protection. |
You only need to grant this user (or a role) the standard Oracle Data Pump privileges, which are the |
|
A database administrator wants to export or import data in a protected schema. |
In addition to the If the user wants to import data, also grant this user the |
|
A database administrator wants to export or import the contents of an entire database. |
In addition to the |
Footnote 1
The BECOME USER privilege is part of the IMP_FULL_DATABASE role by default, but in an Oracle Database Vault environment, this privilege is revoked.
12.4.2.3 Authorizing Users or Roles for Oracle Data Pump Regular Operations in Database Vault
You can authorize a database administrator or a role to use Data Pump for regular operations in an Oracle Database Vault environment.
12.4.3 Authorizing Users or Roles for Data Pump Transportable Export and Import Operations
You can grant authorization levels for users who must perform Oracle Data Pump transportable operations, either directly or through a role.
- About Authorizing Users for Oracle Data Pump Transportable Operations
You can grant users (either directly or through a role) different levels of transportable operation authorization. - Levels of Database Vault Authorization for Data Pump Transportable Operations
Oracle Database Vault provides levels of authorization required for users who must perform export and import transportable operations in a Database Vault environment. - Authorizing Users or Roles for Data Pump Transportable Operations in Database Vault
You can authorize users or roles to perform Oracle Data Pump transportable export or import operations in a Database Vault environment. - Revoking Transportable Tablespace Authorization from Users or Roles
You can revoke authorization from the database administrator who is using Data Pump.
Parent topic: Using Oracle Data Pump with Oracle Database Vault
12.4.3.1 About Authorizing Users for Oracle Data Pump Transportable Operations
You can grant users (either directly or through a role) different levels of transportable operation authorization.
If you want users to only have the authorization to perform transportable export and import operations, then you must grant users or roles the correct authorization, based on their tasks.
12.4.3.2 Levels of Database Vault Authorization for Data Pump Transportable Operations
Oracle Database Vault provides levels of authorization required for users who must perform export and import transportable operations in a Database Vault environment.
Table 12-2 describes these levels.
Table 12-2 Levels of Authorization for Oracle Data Pump Transporatable Operations
| Scenario | Authorization Required |
|---|---|
|
A database administrator wants to transportable export a tablespace or table that has no Database Vault protection. |
You only need to grant this user (or a role) the standard Oracle Data Pump privileges, which are the |
|
A database administrator wants to transportable export a tablespace where there is Database Vault protection (for example, realm or command rule for a table object residing on that tablespace). |
In addition to the Remember that users who have been granted full database level Oracle Data Pump authorization (through the |
|
A database administrator wants to transportable export a table within a tablespace where there is Database Vault protection (for example, a realm or command rule for a table object residing on the tablespace that contains the table to be exported). |
In addition to the Remember that users who have been granted full database level Oracle Data Pump authorization (from the |
|
A database administrator wants to transportable export the contents of an entire database. |
In addition to the |
|
A database administrator wants to use a network link to transportable import a tablespace or a table that has no Database Vault protection. |
In addition to the |
|
A database administrator wants to use a network link to transportable import a tablespace where there is Database Vault protection (for example, realm or command rule for a table object residing on that tablespace) |
In addition to the Remember that users that have been granted Database Vault-specific full database level Oracle Data Pump authorization (through the |
|
A database administrator wants to use a network link to import a table within a transportable tablespace where there is Database Vault protection (for example, realm or command rule for a table object residing on the tablespace that contains the table to be exported) |
In addition to the Remember that users who have been granted Database Vault-specific full database level Oracle Data Pump authorization (through the |
|
A database administrator wants to use a network link to transportable import the contents of an entire database. |
In addition to the |
12.4.3.3 Authorizing Users or Roles for Data Pump Transportable Operations in Database Vault
You can authorize users or roles to perform Oracle Data Pump transportable export or import operations in a Database Vault environment.
12.4.4 Guidelines for Exporting or Importing Data in a Database Vault Environment
After you grant the Oracle Data Pump database administrator the proper authorization, this user can perform any export or import operations that are necessary.
Before this user begins work, they should follow these guidelines:
-
Create a full backup of the database datafiles. This way, if you or other users do not like the newly-imported data, then you easily can revert the database to its previous state. This guideline is especially useful if an intruder had managed to modify Oracle Data Pump exported data to use their own policies.
-
Decide how to handle exporting and importing multiple schemas or tables. You cannot specify multiple schemas or tables in the
DBMS_MACADM.AUTHORIZE_DATAPUMP_USERprocedure, but you can use either of the following methods to accomplish this task:-
Run the
DBMS_MACADM.AUTHORIZE_DATAPUMP_USERprocedure for each schema or table, and then specify the list of these objects in theSCHEMASorTABLESparameter of theEXPDPandIMPDPutilities. -
Perform a full database export or import operation. If so, see the next guideline.
-
-
When performing an export or import operation for an entire database, set the EXPDP or IMPDP FULL option to Y. Remember that this setting will capture the
DVSYSschema, so ensure that the user or role has that you have authorized been granted theDV_OWNERrole.
Note the following:
-
You cannot use the legacy
EXPandIMPutilities with the direct path option (direct=y) if Oracle Database Vault is enabled. -
Users, either through a direct grant or a role grant, that have been granted Database Vault-specific Oracle Data Pump authorization through the
DBMS_MACADM.AUTHORIZE_DATAPUMP_USERprocedure or transportable tablespace authorization through theDBMS_MACADM.AUTHORIZE_TTS_USERprocedure can export and import database objects, but they cannot perform other activities, such asSELECTqueries on schema tables to which they normally do not have access. Similarly, users are not permitted to perform Data Pump operations on objects outside the designated data objects. -
You must grant the
DV_OWNERrole to users who must export or import an entire database, because a full database export requires access to theDVSYSschema, which stores the Oracle Database Vault policies. However, you cannot export theDVSYSschema itself. Data Pump only exports the protection definitions. The target database must have theDVSYSschema in it and Database Vault enabled before you can begin the import process.) Conversely, for a Data Pump import operation to apply the imported policies to the target database, it internally uses theDBMS_MACADMPL/SQL package, which in turn requires the Data Pump user to have theDV_OWNERrole.
Parent topic: Using Oracle Data Pump with Oracle Database Vault
12.5 Using Oracle Scheduler with Oracle Database Vault
Users who are responsible for scheduling database jobs must have Oracle Database Vault-specific authorization.
- About Using Oracle Scheduler with Oracle Database Vault
The level of authorization that you must grant depends on the schema in which the administrator wants to perform a task. - Granting a Job Scheduling Administrator Authorization for Database Vault
You can authorize a user to schedule database jobs in a Database Vault environment. - Revoking Authorization from Job Scheduling Administrators
You can revoke authorization from a user for scheduling database jobs.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.5.1 About Using Oracle Scheduler with Oracle Database Vault
The level of authorization that you must grant depends on the schema in which the administrator wants to perform a task.
Possible scenarios are as follows:
-
An administrator wants to schedule a job in their own schema. An administrator who has been granted privileges to schedule database jobs can continue to do so without any Oracle Database Vault-specific authorizations, unless this schema is protected by a realm. In that case, ensure that this user is authorized to access the realm.
-
An administrator wants to run a job in another schema, but this job does not access any Oracle Database Vault realm or command rule protected object. In this case, this user only needs job related system privileges, not the Oracle Database Vault privileges.
-
An administrator wants to run a job under the schema of another user, including any schema in the database or a remote database. If this job accesses an Oracle Database Vault realm or command rule protected object, then you must grant this user Database Vault-specific authorization by using the
DBMS_MACADM.AUTHORIZE_SCHEDULER_USERprocedure. This authorization applies to both background and foreground jobs. For background jobs, the authorization applies to the last user who created or modified the job. In addition, ensure that the schema owner (the protected schema in which the job is created) authorized to the realm.Later on, you can revoke this authorization by using the
DBMS_MACADM.UNAUTHORIZE_SCHEDULER_USERprocedure. If the schema is not protected by a realm, then you do not need to run theDBMS_MACADM.AUTHORIZE_SCHEDULER_USERprocedure for the user.
Before you can enable or disable an Oracle Scheduler job that is protected by a realm, you must be authorized for that realm (using DBMS_MACADM.ADD_AUTH_TO_REALM), or you should have Oracle Scheduler authorization for the job owner schema (using DBMS_MACADM.AUTHORIZE_SCHEDULER_USER).
Related Topics
Parent topic: Using Oracle Scheduler with Oracle Database Vault
12.5.2 Granting a Job Scheduling Administrator Authorization for Database Vault
You can authorize a user to schedule database jobs in a Database Vault environment.
Related Topics
Parent topic: Using Oracle Scheduler with Oracle Database Vault
12.5.3 Revoking Authorization from Job Scheduling Administrators
You can revoke authorization from a user for scheduling database jobs.
Related Topics
Parent topic: Using Oracle Scheduler with Oracle Database Vault
12.6 Using Information Lifecycle Management with Oracle Database Vault
Users who perform Information Lifecycle Management operations on an Oracle Database Vault-enabled database must be granted authorization to perform these operations.
- About Using Information Lifecycle Management with Oracle Database Vault
You can grant authorization to and from users who are responsible for performing Information Lifecycle Management (ILM) operations on Oracle Database Vault realm- and command rule-protected objects. - Authorizing Users for ILM Operations in Database Vault
You can authorize a user to perform Information Lifecycle Management (ILM) operations in an Oracle Database Vault environment. - Revoking Information Lifecycle Management Authorization from Users
You can revoke authorization from users so that they cannot perform Information Lifecycle Management (ILM) operations in an Oracle Database Vault environment.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.6.1 About Using Information Lifecycle Management with Oracle Database Vault
You can grant authorization to and from users who are responsible for performing Information Lifecycle Management (ILM) operations on Oracle Database Vault realm- and command rule-protected objects.
You must first authorize users before they can perform the following SQL statements for ILM operations in a Database Vault-enabled database:
-
ALTER TABLE-
ILM -
FLASHBACK ARCHIVE -
NO FLASHBACK ARCHIVE
-
-
ALTER TABLESPACE-
FLASHBACK MODE
-
12.6.2 Authorizing Users for ILM Operations in Database Vault
You can authorize a user to perform Information Lifecycle Management (ILM) operations in an Oracle Database Vault environment.
12.7 Using Oracle Database Replay with Oracle Database Vault
Database administrators can authorize Oracle Database Replay users to work in a Database Vault environment.
- About Using Database Replay with Oracle Database Vault
You can grant Oracle Database Vault authorizations for users to perform both workload capture and workload replay operations with Oracle Database Replay. - Authorizing Users for Database Replay Operations
You can authorize Oracle Database Replay users for both workload capture and workload replay operations. - Revoking Database Replay Authorization from Users
You can remove authorization for both Oracle Database Replay workload capture and workload replay operations.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.7.1 About Using Database Replay with Oracle Database Vault
You can grant Oracle Database Vault authorizations for users to perform both workload capture and workload replay operations with Oracle Database Replay.
Oracle Database Replay can capture a workload on the production system and replay it on a test system with the exact timing, concurrency, and transaction characteristics of the original workload. Because the workload may contain sensitive information, Oracle Database Vault enables you to control which privileged users can perform reply and capture operations.
Parent topic: Using Oracle Database Replay with Oracle Database Vault
12.7.2 Authorizing Users for Database Replay Operations
You can authorize Oracle Database Replay users for both workload capture and workload replay operations.
- Authorizing Users for Workload Capture Operations
You can authorize a user to perform Oracle Database Replay workload capture operations in an Oracle Database Vault environment. - Authorizing Users for Workload Replay Operations
You can authorize a user to perform Oracle Database Replay workload replay operations in an Oracle Database Vault environment.
Parent topic: Using Oracle Database Replay with Oracle Database Vault
12.7.2.1 Authorizing Users for Workload Capture Operations
You can authorize a user to perform Oracle Database Replay workload capture operations in an Oracle Database Vault environment.
Related Topics
Parent topic: Authorizing Users for Database Replay Operations
12.7.2.2 Authorizing Users for Workload Replay Operations
You can authorize a user to perform Oracle Database Replay workload replay operations in an Oracle Database Vault environment.
Related Topics
Parent topic: Authorizing Users for Database Replay Operations
12.7.3 Revoking Database Replay Authorization from Users
You can remove authorization for both Oracle Database Replay workload capture and workload replay operations.
- Revoking Workload Capture Privileges
You can revoke authorization from users so that they cannot perform Oracle Database Replay workload capture operations in an Oracle Database Vault environment. - Revoking Workload Replay Privileges
You can revoke authorization from users so that they cannot perform Oracle Database Replay workload replay operations in an Oracle Database Vault environment.
Parent topic: Using Oracle Database Replay with Oracle Database Vault
12.7.3.1 Revoking Workload Capture Privileges
You can revoke authorization from users so that they cannot perform Oracle Database Replay workload capture operations in an Oracle Database Vault environment.
Related Topics
Parent topic: Revoking Database Replay Authorization from Users
12.7.3.2 Revoking Workload Replay Privileges
You can revoke authorization from users so that they cannot perform Oracle Database Replay workload replay operations in an Oracle Database Vault environment.
Related Topics
Parent topic: Revoking Database Replay Authorization from Users
12.8 Running Preprocessor Programs with Oracle Database Vault
Users who run preprocessor programs through external tables must have Oracle Database Vault-specific authorization.
- About Running Preprocessor Programs with Oracle Database Vault
You can grant and revoke Database Vault authorizations for users to run preprocessor programs through external tables. - Authorizing Users to Run Preprocessor Programs
TheDBMS_MACADM.AUTHORIZE_PREPROCESSORprocedure grants users authorization to run preprocessor programs through external tables. - Revoking Authorization to Run Execute Preprocessor Programs from Users
TheDBMS_MACADM.UNAUTHORIZE_PREPROCESSORprocedure revokes authorization from users so that they cannot run preprocessor programs through external tables in an Oracle Database Vault environment.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.8.1 About Running Preprocessor Programs with Oracle Database Vault
You can grant and revoke Database Vault authorizations for users to run preprocessor programs through external tables.
Parent topic: Running Preprocessor Programs with Oracle Database Vault
12.8.2 Authorizing Users to Run Preprocessor Programs
The DBMS_MACADM.AUTHORIZE_PREPROCESSOR procedure grants users authorization to run preprocessor programs through external tables.
Parent topic: Running Preprocessor Programs with Oracle Database Vault
12.8.3 Revoking Authorization to Run Execute Preprocessor Programs from Users
The DBMS_MACADM.UNAUTHORIZE_PREPROCESSOR procedure revokes authorization from users so that they cannot run preprocessor programs through external tables in an Oracle Database Vault environment.
Parent topic: Running Preprocessor Programs with Oracle Database Vault
12.9 Using Database Vault Operations Control to Restrict Multitenant Common User Access to Local PDB Data
You can control PDB access by CDB root common users, such as infrastructure database administrators.
- About Using Database Vault Operations Control
You can automatically restrict common users from accessing pluggable database (PDB) local data in autonomous, regular Cloud, or on-premises environments. - How the Addition of Common Users and Packages to an Exception List Works
Before you add a common user or package to an exception list, they must fulfill special requirements. - Enabling Database Vault Operations Control
To enable Database Vault operations control, use theDBMS_MACADM.ENABLE_APP_PROTECTIONPL/SQL procedure. - Adding Common Users and Packages to an Exception List
Common users and applications that must access PDB local data can be added to an exception list. - Deleting Common Users and Packages from an Exception List
Users and applications that no longer need to access PDB local data can be removed from the exception list. - Disabling Database Vault Operations Control
To disable Database Vault operations control, use theDBMS_MACADM.DISABLE_APP_PROTECTIONPL/SQL procedure.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.9.1 About Using Database Vault Operations Control
You can automatically restrict common users from accessing pluggable database (PDB) local data in autonomous, regular Cloud, or on-premises environments.
To accomplish this, you can use Oracle Database Vault operations control, which applies to common users such as infrastructure database administrators and applications.
Database Vault operations control is useful for situations where a database administrator must log in to the CDB root as a highly privileged user, but still not be able to access PDB customer data. Database operations control does not block PDB database administrators. To block these users, enable Oracle Database Vault in the PDB and then use the Database Vault features such as realm control to block these users. (Note that when operations control is enabled, common users cannot proxy as local users into the PDB.)
You can create an exception list for Database Vault operations control of common users and packages for situations where a common user or application must perform tasks that must access local data on a PDB. An example of the type of common user that you would specify for the exception list is the CTXSYS application account, which is responsible for Oracle Text. Specifying a package in an exception list enables you to apply more fine-grained control instead of providing full access to a user in an exception list.
The general process for using Database Vault operations control is as follows:
- Enable Database Vault operations control and keep it enabled for the production environment.
- At this stage Database Vault operations control applies to all PDBs in the environment, regardless of whether the PDB has enabled Database Vault or not.
- To enable specific users and packages to have access to the local schemas of the PDBs, add them to an exception list. When the user or package no longer needs access, then you can remove them from the exception list. For example, if the database is using Oracle Text, then you can add the
CTXSYSadministrative user account and the package to the exception list.
12.9.2 How the Addition of Common Users and Packages to an Exception List Works
Before you add a common user or package to an exception list, they must fulfill special requirements.
You can add a user package to the exception list if the package is the only object in the user account that needs access to the PDB local data. This allows for fine grained control over what is put into the exception list. The kinds of common users and packages that you would add to the exception list are ones that are necessary for the functioning of the PDB. For example, if you are using Oracle Spatial, then you should add the MDSYS account to the exception list. MDSYS requires access to customer PDB data for Oracle Spatial functions.
A PL/SQL procedure on the Ops Control exception list can be run by any common user, as long as the common user has system or direct object privileges to run the PL/SQL procedure. (Only definer’s rights procedures can be added to the exception list, not invoker’s rights.)
Only users on the operations control exception list (user, % exception) can modify PL/SQL procedures on an exception list and only if they have the privileges to modify the PL/SQL procedures. For example, User X cannot modify their own User X PL/SQL procedure if the procedure is on the operations control exception list, but User X is not on the exception list. User Y can modify User X procedures if User Y is on the exception list (Y, %) and if User Y has privileges to modify User X procedures.
To add a common user and a package to the Database Vault operations control exception list, you can use the DBMS_MACADM.ADD_APP_EXCEPTION PL/SQL procedure. To find existing exceptions, you can query the DBA_DV_APP_EXCEPTION data dictionary view.
12.9.3 Enabling Database Vault Operations Control
To enable Database Vault operations control, use the DBMS_MACADM.ENABLE_APP_PROTECTION PL/SQL procedure.
Oracle recommends that if you elect to use Database Vault operations control for your multitenant production server, then you should keep Database Vault operations control enabled full time.
In most cases, you will enable Database Operations control for the entire CDB, not just a specific PDB. If you need to disable it for a specific PDB (for example, for troubleshooting purposes), then you can run theDBMS_MACADM.DISABLE_APP_PROTECTION procedure on the PDB. When you are finished troubleshooting the PDB, re-enable it for Database Vault operations control, as shown in the example in this topic.
- Log in to the CDB root as a common user who has been granted the
DV_OWNERrole. - Run the
DBMS_MACADM.ENABLE_APP_PROTECTIONprocedure.- To enable Database Vault operations control for all PDBs in the CDB environment:
EXEC DBMS_MACADM.ENABLE_APP_PROTECTION; - The operations control for a specific PDB may have been disabled for troubleshooting reasons. To re-enable Database Vault operations control for a specific PBB (for example,
HRPDB):EXEC DBMS_MACADM.ENABLE_APP_PROTECTION ('HRPDB');
- To enable Database Vault operations control for all PDBs in the CDB environment:
SYS with the SYSDBA administrative privilege and then executing the SELECT * FROM DBA_DV_STATUS; query. If specific trusted common users or packages must have access to the local schemas of these PDBs to perform special operations, then you can use the DBMS_MACADM.ADD_APP_EXCEPTION procedure to add the user or package to an exception list for Database Vault operations control.
12.9.4 Adding Common Users and Packages to an Exception List
Common users and applications that must access PDB local data can be added to an exception list.
12.9.5 Deleting Common Users and Packages from an Exception List
Users and applications that no longer need to access PDB local data can be removed from the exception list.
DBMS_MACADM.DELETE_APP_PROTECTION PL/SQL procedure. To find existing exceptions, you can query the DBA_DV_APP_EXCEPTION data dictionary view.
12.9.6 Disabling Database Vault Operations Control
To disable Database Vault operations control, use the DBMS_MACADM.DISABLE_APP_PROTECTION PL/SQL procedure.
- Log in to the CDB root as a common user who has been granted the
DV_OWNERrole. - Run the
DBMS_MACADM.DISABLE_APP_PROTECTIONprocedure.- To disable Database Vault operations control for all PDBs in the CDB environment:
EXEC DBMS_MACADM.DISABLE_APP_PROTECTION; - To disable Database Vault operations control for a specific PBB (for example,
HRPDB):EXEC DBMS_MACADM.DISABLE_APP_PROTECTION ('HRPDB');
- To disable Database Vault operations control for all PDBs in the CDB environment:
12.10 Preventing Multitenant Local Users from Blocking Common Operations
You can prevent multitenant local users from blocking common operations when they attempt to create Oracle Database Vault protections on common user objects.
- About Preventing Multitenant Local Users from Blocking Common Operations
A user who has theDV_OWNERrole in the root can control whether local PDB users can create Oracle Database Vault controls on a common user's local objects. - Preventing Local Users from Blocking Common Operations
To prevent local users from blocking common operations, run theDBMS_MACADM.ALLOW_COMMON_OPERATIONprocedure in the root.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.10.1 About Preventing Multitenant Local Users from Blocking Common Operations
A user who has the DV_OWNER role in the root can control whether local PDB users can create Oracle Database Vault controls on a common user's local objects.
If a local user can apply Oracle Database Vault controls (such as realms or command rules) to a local object that is owned by a common user, or to an object owned by an application common user, then the common user or the application common user could be blocked from accessing local data in their own schema in the PDB. This may prevent them from running common operations necessary for the maintenance of the database or application. In addition, a local user could be able to create a CONNECT command rule on a common user that can prevent this common user from logging in to the PDB in which the common user's objects reside.
To prevent local users from being able to block common operations, a common user who has been granted the DV_OWNER role in the root can run the DBMS_MACADM.ALLOW_COMMON_OPERATION procedure in the root.
To find the current status of how DBMS_MACADM.ALLOW_COMMON_OPERATION has been set, a user with the DV_OWNER or DV_ADMIN role can query the DVSYS.DBA_DV_COMMON_OPERATION_STATUS data dictionary view.
Related Topics
12.10.2 Preventing Local Users from Blocking Common Operations
To prevent local users from blocking common operations, run the DBMS_MACADM.ALLOW_COMMON_OPERATION procedure in the root.
ALLOW COMMON OPERATION to TRUE, then local users are restricted from creating Oracle Database Vault controls on common user objects. This setting applies to existing local PDB Database Vault controls that were created on common user objects, so that they will not be enforced on common users.
12.11 Oracle Recovery Manager and Oracle Database Vault
You can use Recovery Manager (RMAN) in an Oracle Database Vault environment.
The functionality of RMAN with Oracle Database Vault is almost the same as its functionality in a standard Oracle Database environment. However, be aware that the RMAN recover table and table partitions features do not work with realm-protected tables when you attempt an export operation. To perform an export operation, you must perform a full table recovery and then have a Database Vault authorized user perform the export of the real-protected protected table.
Be aware that the RMAN recover table and table partitions features do not work with realm-protected tables when you attempt to recover the table. To recover the table, you must perform a full database recovery and then have a Database Vault authorized user perform the export of the realm-protected table to import into the existing database.
12.12 Privileges for Using XStream with Oracle Database Vault
If you want to use XStream in an Oracle Database Vault environment, then you must have the appropriate privileges.
These privileges are as follows:
-
You must be granted the
DV_XSTREAM_ADMINrole in order to configure the XStream. -
Before you can apply changes to any tables that are protected by a realm, you must be authorized to have access to that realm. For example:
EXEC DBMS_MACADM.ADD_AUTH_TO_REALM('realm_name','username'); - Before you can run the
DBMS_XSTREAM_AUTH.GRANT_ADMIN_PRIVILEGEprocedure, you must be granted theDV_ACCTMGRrole.
12.13 Privileges for Using Oracle GoldenGate with Oracle Database Vault
If you want to use Oracle GoldenGate in an Oracle Database Vault environment, then you must have the appropriate privileges.
These privileges are as follows:
-
The user must be granted the
DV_GOLDENGATE_ADMINrole in order to configure the Oracle GoldenGate. -
The user must be granted the
DV_GOLDENGATE_REDO_ACCESSrole if the user must use the Oracle GoldenGateTRANLOGOPTIONS DBLOGREADERmethod to access redo logs.For example, to grant the
DV_GOLDENGATE_ADMINandDV_GOLDENGATE_REDO_ACCESSroles to a user namedgg_admin:GRANT DV_GOLDENGATE_ADMIN, DV_GOLDENGATE_REDO_ACCESS TO gg_admin;
-
The user must be granted the
DV_ACCTMGRrole before this user can create users on the replicated side. -
The user must perform extract operations in triggerless mode before attempting to perform procedural replication.
-
Before users can apply changes to any tables that are protected by a realm, they must be authorized to have access to that realm. For example:
EXEC DBMS_MACADM.ADD_AUTH_TO_REALM('realm_name','username'); -
The
SYSuser must be authorized to perform Data Definition Language (DDL) operations in theSYSTEMschema, as follows:EXECUTE DVSYS.DBMS_MACADM.AUTHORIZE_DDL('SYS', 'SYSTEM'); -
The user must be granted authorization to the Oracle Default Component Protection Realm. For example, to grant this realm authorization to a user named
gg_admin:BEGIN DVSYS.DBMS_MACADM.ADD_AUTH_TO_REALM( REALM_NAME => 'Oracle Default Component Protection Realm', GRANTEE => 'gg_admin', AUTH_OPTIONS => 1); END; /
Note:
Oracle GoldenGate queries, updates, and manages objects in theSYS, SYSTEM and GoldenGate-related schemas. If any of the schemas are protected by an Oracle Database Vault realm, then the GoldenGate Extract operation can fail. Oracle Database Vault protects dictionary related objects with the Oracle Default Component Protection Realm and recommends that you do not protect default schemas, such as SYS and SYSTEM, with any custom Oracle Database Vault realms or custom Oracle Database Vault command rules.
12.14 Using Data Masking in an Oracle Database Vault Environment
You must have the correct authorization to perform data masking in an Oracle Database Vault environment.
- About Data Masking in an Oracle Database Vault Enabled Database
In an Oracle Database Vault-enabled database, only users who have Database Vault authorizations can mask data in Database Vault-protected database objects. - Adding Data Masking Users to the Data Dictionary Realm Authorizations
You can add data masking users to the Oracle Default Component Protection realm to give them data dictionary realm authorizations. - Giving Users Access to Tables or Schemas That They Want to Mask
To give users access to tables or schemas that they want to mask, you must authorize them for the appropriate realm. - Creating a Command Rule to Control Data Masking Privileges
You must have privileges to manage tables, packages, and triggers before you can use data masking in an Oracle Database Vault environment.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.14.1 About Data Masking in an Oracle Database Vault Enabled Database
In an Oracle Database Vault-enabled database, only users who have Database Vault authorizations can mask data in Database Vault-protected database objects.
In a non-Database Vault environment, users who have been granted the SELECT_CATALOG_ROLE and DBA roles can perform data masking. However, with Database Vault, users must have additional privileges. This section describes three ways that you can use to enable users to mask data in Database Vault-protected objects.
If users do not have the correct privileges, then the following errors can occur while creating the masking definition or when the job is executing:
ORA-47400: Command Rule violation for string on string ORA-47401: Realm violation for string on string. ORA-47408: Realm violation for the EXECUTE command ORA-47409: Command Rule violation for the EXECUTE command ORA-01301: insufficient privileges
12.14.2 Adding Data Masking Users to the Data Dictionary Realm Authorizations
You can add data masking users to the Oracle Default Component Protection realm to give them data dictionary realm authorizations.
The Oracle Data Dictionary controls access to the Oracle Database catalog schemas, such as SYS and SYSTEM. (See Default Realms for a full list of these schemas.) It also controls the ability to grant system privileges and database administrator roles. If you add users to the Oracle Default Component Protection realm, and assuming these users already have the privileges associated with the Oracle Data Dictionary, then these users will have these same privileges in a Database Vault environment. Therefore, if you do add a user to this realm, ensure that this user is a trusted user.
-
To add a user to the Oracle Default Component Protection realm, use the
DBMS_MACADM.ADD_AUTH_TO_REALMprocedure.
For example:
BEGIN DBMS_MACADM.ADD_AUTH_TO_REALM( realm_name => 'Oracle Default Component Protection Realm', grantee => 'DBA_JSMITH', auth_options => DBMS_MACUTL.G_REALM_AUTH_PARTICIPANT); END; /
12.14.3 Giving Users Access to Tables or Schemas That They Want to Mask
To give users access to tables or schemas that they want to mask, you must authorize them for the appropriate realm.
If the table or schema of a table that is to be data masked is in a realm, then you must add the user responsible for data masking to the realm authorization as a participant or owner. If the table or schema has dependent objects that are in other realm-protected tables, then you must grant the user participant or owner authorization for those realms as well.
-
To authorize users for data masking to a realm that protects the objects they want to data mask, use the
DBMS_MACADM.ADD_AUTH_TO_REALMprocedure.
The following example shows how to grant user DBA_JSMITH authorization for the HR.EMPLOYEES table, which is protected by a realm called Business Apps Realm:
BEGIN DBMS_MACADM.ADD_AUTH_TO_REALM( realm_name => 'Business Apps Realm', grantee => 'DBA_JSMITH', auth_options => DBMS_MACUTL.G_REALM_AUTH_PARTICIPANT; END; /
12.14.4 Creating a Command Rule to Control Data Masking Privileges
You must have privileges to manage tables, packages, and triggers before you can use data masking in an Oracle Database Vault environment.
For data masking, users must have the CREATE TABLE, SELECT TABLE, ALTER TABLE, and DROP TABLE privileges for the masking objects and if there are any dependent objects to be created, the user must have the appropriate privileges such as CREATE PACKAGE, CREATE TRIGGER, and so on.
You can create command rules to control data masking privileges at a granular level. To do so, create a command rule that can either prevent or allow the user access to objects that must have to be data masked. For example, you can create a command rule called Allow Data Masking that checks if the user is in a list of users who are responsible for data masking. If the user logging in is one of these users, then the command rule evaluates to true and the user is permitted to create the data mask for the protected object.
To create a command rule that controls data masking privileges:
12.15 Converting a Standalone Oracle Database to a PDB and Plugging It into a CDB
You can convert a standalone Oracle Database database from release 12c through 19c to a PDB, and then plug this PDB into a CDB.
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.16 Using the ORADEBUG Utility with Oracle Database Vault
The ORADEBUG utility is used primarily by Oracle Support to diagnose problems that may arise with an Oracle database.
ORADEBUG utility in an Oracle Database Vault-enabled environment. In a traditional auditing environment, you can audit the use of ORADEBUG by setting the AUDIT_SYS_OPERATIONS initialization parameter to TRUE. In a unified auditing environment, ORADBUG commands are mandatorily audited. This control does not apply to a privileged OS user, which is the OS user with the same OS user ID as the Oracle server process. This exception is made because such a user can completely control and examine the Oracle process using other means (for example, with a debugger).
Parent topic: DBA Operations in an Oracle Database Vault Environment
12.17 Performing Patch Operations in an Oracle Database Vault Environment
User SYS must have the DV_PATCH_ADMIN role to perform a patch operations on an Oracle Database Vault-enabled database.
DV_PATCH_ADMIN can also view data.
Parent topic: DBA Operations in an Oracle Database Vault Environment