3 Getting Started with Oracle Database Vault
Before you can start using Oracle Database Vault, you must configure and enable it with the Oracle database.
- About Configuring and Enabling Oracle Database Vault in Oracle Database
Oracle Database includes Database Vault when you choose to include a default database in the installation process, but you must configure and enable it before you can use it. - Configuring and Enabling Oracle Database Vault
You can configure and enable Oracle Database Vault based on several scenarios. - Verifying That Database Vault Is Configured and Enabled
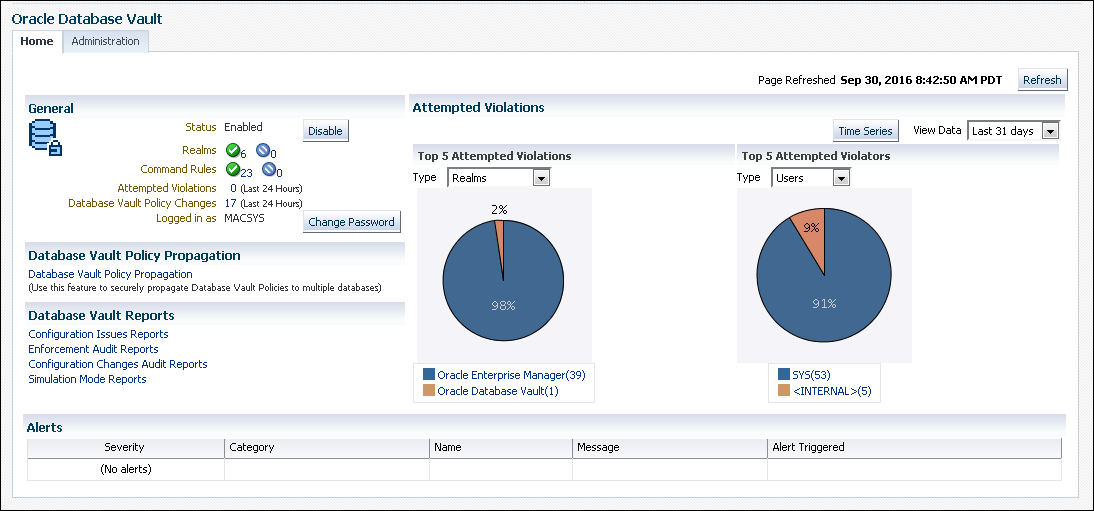
TheDBA_DV_STATUS,CDB_DV_STATUS, andDBA_OLS_STATUSdata dictionary views verify if Oracle Database is configured and enabled. - Logging in to Oracle Database Vault from Oracle Enterprise Cloud Control
Oracle Enterprise Manager Cloud Control (Cloud Control) provides pages for managing Oracle Database Vault. - Quick Start Tutorial: Securing a Schema from DBA Access
This tutorial shows how to create a realm around theHRschema.
3.1 About Configuring and Enabling Oracle Database Vault in Oracle Database
Oracle Database includes Database Vault when you choose to include a default database in the installation process, but you must configure and enable it before you can use it.
Oracle Database includes Database Vault when you choose to include a default database in the installation process, but you must configure and enable it before you can use it. The configuration and enablement process enables Oracle Label Security if it is not already enabled. Oracle Label Security is required for Oracle Database Vault but it does not require a separate license unless you begin using Oracle Label Security separately and create Oracle Label Security policies.
Oracle Database includes Database Vault when you choose to include a default database in the installation process, but you must configure and enable it before you can use it. If you create a custom database, then you can use DBCA to install and enable Database Vault for it. The registration process enables Oracle Label Security if it is not already enabled. Oracle Label Security is required for Oracle Database Vault but it does not require a separate license unless you begin using Oracle Label Security separately and create Oracle Label Security policies. This procedure applies to the CDB root, application root, and the current pluggable database (PDB), as well as to both single-instance and Oracle Real Application Clusters (Oracle RAC) installations. In a multitenant database, Database Vault must be configured with the CDB root before any of the PDBs can configure Database Vault.
As part of the configuration process, you created the Database Vault administrative accounts. These are accounts that hold the Database Vault roles DV_OWNER and DV_ACCTMGR. Use these accounts initially to provision the roles to named users with administrative privileges. Maintaining a backup account will allow you to recover from the named user losing or somehow misplacing their credentials because SYS will not be able to reset these passwords for users with these roles.
Note:
If you upgraded from a release earlier than Oracle Database 12c, then you disabled Oracle Database Vault to perform the upgrade. After the upgrade process is complete, then you must configure and enable Oracle Database Vault again.If you are migrating a non-Database Vault-enabled Oracle database from a release earlier than release 12c, then you must perform a manual installation of Database Vault.
3.2 Configuring and Enabling Oracle Database Vault
You can configure and enable Oracle Database Vault based on several scenarios.
- About Configuring and Enabling Database Vault
You must configure and enable Oracle Database Vault in the CDB root before you can perform the same action in any of the associated PDBs. - Configuring and Enabling Database Vault in the CDB Root
You can configure and enable Oracle Database Vault with common users who will use the Database Vault-enforced roles in the CDB root. - Configuring and Enabling Database Vault Common Users to Manage Specific PDBs
You must configure and enable Oracle Database Vault in the root first, then in the PDBs afterward. - Configuring and Enabling Database Vault Local Users to Manage Specific PDBs
You must configure and enable Oracle Database Vault in the root first, and then in the PDBs afterward. - Configuring and Enabling Oracle Database Vault in an Oracle Real Application Clusters Environment
You can configure Oracle Database Vault for an Oracle Real Application Clusters (Oracle RAC) environment, including each Oracle RAC node. - Creating a Profile to Protect the DV_OWNER and DV_ACCTMGR Users
A profile provides additional protection for users who have been granted theDV_OWNERandDV_ACCTMGRroles. - Manually Installing Oracle Database Vault
Under certain conditions, you must manually install Oracle Database Vault.
Parent topic: Getting Started with Oracle Database Vault
3.2.1 About Configuring and Enabling Database Vault
You must configure and enable Oracle Database Vault in the CDB root before you can perform the same action in any of the associated PDBs.
The common users who have been assigned the DV_OWNER and DV_ACCTMGR roles in the CDB root can also have the same role in the PDBs. PDBs can have Database Vault configured and enabled using the same common users or use separate PDB local users. The DV_ACCTMGR role is granted commonly to the common user in the CDB root. You can grant DV_OWNER locally or commonly to the CDB root common user when you configure and enablement Database Vault with the CDB root. Granting DV_OWNER locally to the common user prevents the common DV_OWNER user from using this role in any PDB.
Parent topic: Configuring and Enabling Oracle Database Vault
3.2.2 Configuring and Enabling Database Vault in the CDB Root
You can configure and enable Oracle Database Vault with common users who will use the Database Vault-enforced roles in the CDB root.
UTL_RECOMP PL/SQL package to check the validity of objects. See Oracle Database PL/SQL
Packages and Types Reference.
Related Topics
- Verifying That Database Vault Is Configured and Enabled
- Oracle Database Vault Roles
- Logging in to Oracle Database Vault from Oracle Enterprise Cloud Control
- DV_PATCH_ADMIN Database Vault Database Patch Role
- CONFIGURE_DV General System Maintenance Procedure
- Configuring and Enabling Oracle Database Vault in an Oracle Real Application Clusters Environment
- Resetting Oracle Database Vault Account Passwords
Parent topic: Configuring and Enabling Oracle Database Vault
3.2.3 Configuring and Enabling Database Vault Common Users to Manage Specific PDBs
You must configure and enable Oracle Database Vault in the root first, then in the PDBs afterward.
ORA-47503: Database Vault is not enabled on CDB$ROOT error appears.
Related Topics
- Verifying That Database Vault Is Configured and Enabled
- Oracle Database Vault Roles
- Logging in to Oracle Database Vault from Oracle Enterprise Cloud Control
- DV_PATCH_ADMIN Database Vault Database Patch Role
- CONFIGURE_DV General System Maintenance Procedure
- Configuring and Enabling Database Vault in the CDB Root
- Resetting Oracle Database Vault Account Passwords
Parent topic: Configuring and Enabling Oracle Database Vault
3.2.4 Configuring and Enabling Database Vault Local Users to Manage Specific PDBs
You must configure and enable Oracle Database Vault in the root first, and then in the PDBs afterward.
ORA-47503: Database Vault is not enabled on CDB$ROOT error appears.
3.2.5 Configuring and Enabling Oracle Database Vault in an Oracle Real Application Clusters Environment
You can configure Oracle Database Vault for an Oracle Real Application Clusters (Oracle RAC) environment, including each Oracle RAC node.
Related Topics
Parent topic: Configuring and Enabling Oracle Database Vault
3.2.6 Creating a Profile to Protect the DV_OWNER and DV_ACCTMGR Users
A profile provides additional protection for users who have been granted the DV_OWNER and DV_ACCTMGR roles.
DV_OWNER or DV_ACCTMGR roles are considered critical, privileged, accounts. Typically, these accounts should be considered service accounts and exempt from password lockout requirements. Oracle recommends that you create a custom profile that prevents the account from being locked. In addition, you should audit failed login attempts for these Database Vault-related accounts.
- Log into the database instance as a user who has the
CREATE PROFILEsystem privilege.- For common
DV_OWNERandDV_ACCTMGRusers: Log in to the root of the database instance. - For local
DV_OWNERandDV_ACCTMGRusers: Log in to the PDB in which you created the users.
- For common
- Create a profile similar to the following:
- For common
DV_OWNERandDV_ACCTMGRusers: In the root, create the profile similar to the following:CREATE PROFILE c##dv_profile limit FAILED_LOGIN_ATTEMPTS UNLIMITED PASSWORD_VERIFY_FUNCTION ORA12C_VERIFY_FUNCTION PASSWORD_LOCK_TIME UNLIMITED CONTAINER=ALL; - For local
DV_OWNERandDV_ACCTMGRusers: In the PDB, create the profile similar to the following:CREATE PROFILE dv_profile limit FAILED_LOGIN_ATTEMPTS UNLIMITED PASSWORD_VERIFY_FUNCTION ORA12C_VERIFY_FUNCTION PASSWORD_LOCK_TIME UNLIMITED CONTAINER=CURRENT;
- For common
- Update the
DV_OWNERandDV_ACCTMGRuser accounts to use this profile.- For common
DV_OWNERandDV_ACCTMGRusers:ALTER USER c##sec_admin_owen PROFILE c##dv_profile CONTAINER = ALL; ALTER USER c##dbv_owner_root_backup PROFILE c##dv_profile CONTAINER = ALL; ALTER USER c##accts_admin_ace PROFILE c##dv_profile CONTAINER = ALL; ALTER USER c##dbv_acctmgr_root_backup PROFILE c##dv_profile CONTAINER = ALL; - For local
DV_OWNERandDV_ACCTMGRusers:ALTER USER sec_admin_owen PROFILE dv_profile CONTAINER = CURRENT; ALTER USER dbv_owner_backup PROFILE dv_profile CONTAINER = CURRENT; ALTER USER accts_admin_ace PROFILE dv_profile CONTAINER = CURRENT; ALTER USER dbv_acctmgr_backup PROFILE dv_profile CONTAINER = CURRENT;
- For common
- Connect as a user who has been granted the
AUDIT_ADMINrole. - Create and enable a unified audit policy to track failed logins by any user who has been granted the
DV_OWNERorDV_ACCTMGRrole.- For common
DV_OWNERandDV_ACCTMGRusers: In the root, create a policy similar to the following:CREATE AUDIT POLICY c##dv_logins ACTIONS LOGON; AUDIT POLICY c##dv_logins BY USERS WITH GRANTED ROLES DV_OWNER, DV_ACCTMGR WHENEVER NOT SUCCESSFUL; - For local
DV_OWNERandDV_ACCTMGRusers: In the PDB, create a policy similar to the following:CREATE AUDIT POLICY dv_logins ACTIONS LOGON; AUDIT POLICY dv_logins BY USERS WITH GRANTED ROLES DV_OWNER, DV_ACCTMGR WHENEVER NOT SUCCESSFUL;
- For common
Parent topic: Configuring and Enabling Oracle Database Vault
3.2.7 Manually Installing Oracle Database Vault
Under certain conditions, you must manually install Oracle Database Vault.
Related Topics
Parent topic: Configuring and Enabling Oracle Database Vault
3.3 Verifying That Database Vault Is Configured and Enabled
The DBA_DV_STATUS, CDB_DV_STATUS, and DBA_OLS_STATUS data dictionary views verify if Oracle Database is configured and enabled.
SYS user and users who have been granted the DBA role can query these views.
-
For Database Vault:
-
If you want to find the Database Vault status for the root only or an individual PDB, then query
DBA_DV_STATUS. For example:SELECT * FROM DBA_DV_STATUS;Output similar to the following appears:
NAME STATUS -------------------- ----------- DV_APP_PROTECTION NOT CONFIGURED DV_CONFIGURE_STATUS TRUE DV_ENABLE_STATUS TRUEDV_APP_PROTECTIONrefers to operations control, which automatically restricts common users from accessing PDB local data in Oracle Database multitenant environments. -
If you want to find the Database Vault status of all PDBs in the multitenant environment, then as a common user with administrative privileges, query
CDB_DV_STATUS, which provides the addition of a container ID (CON_ID) field.
-
-
For Oracle Label Security, query the
DBA_OLS_STATUSdata dictionary view.
3.4 Logging in to Oracle Database Vault from Oracle Enterprise Cloud Control
Oracle Enterprise Manager Cloud Control (Cloud Control) provides pages for managing Oracle Database Vault.
3.5 Quick Start Tutorial: Securing a Schema from DBA Access
This tutorial shows how to create a realm around the HR schema.
- About This Tutorial
In this tutorial, you create a realm around for theHRsample database schema by using the Oracle Database Vault PL/SQL packages. - Step 1: Log On as SYSTEM to Access the HR Schema
You must enable theHRschema for this tutorial. - Step 2: Create a Realm
Realms can protect one or more schemas, individual schema objects, and database roles. - Step 3: Create the SEBASTIAN User Account
At this stage, there are no database accounts or roles authorized to access or otherwise manipulate the database objects the realm will protect. - Step 4: Have User SEBASTIAN Test the Realm
At this stage, userSEBASTIANcan test the realm by trying to query theHR.EMPLOYEEStable. - Step 5: Create an Authorization for the Realm
Next, userSEBASTIANmust be granted authorization to the HR Apps realm, so that they can access theHR.EMPLOYEEStable. - Step 6: Test the Realm
To test the realm, you must try to access theEMPLOYEEStable as a user other thanHR. - Step 9: Remove the Components for This Tutorial
You can remove the components that you created for this tutorial if you no longer need them.
Parent topic: Getting Started with Oracle Database Vault
3.5.1 About This Tutorial
In this tutorial, you create a realm around for the HR sample database schema by using the Oracle Database Vault PL/SQL packages.
In the HR schema, the EMPLOYEES table has information such as salaries that should be hidden from most employees in the company, including those with administrative access. To accomplish this, you add the HR schema to the secured objects of the protection zone, which in Oracle Database Vault is called a realm, inside the database. Then you grant limited authorizations to this realm. Afterward, you test the realm to make sure it has been properly secured.
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.2 Step 1: Log On as SYSTEM to Access the HR Schema
You must enable the HR schema for this tutorial.
HR sample schema is installed.
Related Topics
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.3 Step 2: Create a Realm
Realms can protect one or more schemas, individual schema objects, and database roles.
HR schema.
At this stage, you have created the realm but you have not assigned any authorizations to it. You will take care of that later on in this tutorial.
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.4 Step 3: Create the SEBASTIAN User Account
At this stage, there are no database accounts or roles authorized to access or otherwise manipulate the database objects the realm will protect.
So, the next step is to authorize database accounts or database roles so that they can have access to the schemas within the realm. You will create the SEBASTIAN user account.
Related Topics
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.5 Step 4: Have User SEBASTIAN Test the Realm
At this stage, user SEBASTIAN can test the realm by trying to query the HR.EMPLOYEES table.
SEBASTIAN has the READ ANY TABLE system privilege, they cannot query the HR.EMPLOYEES table, because the HR Apps realm takes precedence over the READ ANY TABLE system privilege.
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.6 Step 5: Create an Authorization for the Realm
Next, user SEBASTIAN must be granted authorization to the HR Apps realm, so that they can access the HR.EMPLOYEES table.
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.7 Step 6: Test the Realm
To test the realm, you must try to access the EMPLOYEES table as a user other than HR.
HR from accessing its own objects.)
The SYSTEM account normally has access to all objects in the HR schema because it has the SELECT ANY TABLE privilege, but now that you have safeguarded the EMPLOYEES table with Oracle Database Vault, this is no longer the case.
-
In SQL*Plus, connect to the PDB as
SYSTEM.CONNECT SYSTEM@pdb_name Enter password: password
-
Try querying any of the rows in the
EMPLOYEEStable again.For example:
SELECT FIRST_NAME, LAST_NAME, SALARY FROM HR.EMPLOYEES WHERE ROWNUM <10;
The following output should appear:
Error at line 1: ORA-01031: insufficient privileges
SYSTEMno longer has access to theEMPLOYEEStable. (In fact, even userSYSdoes not have any access to this table.) However, userSEBASTIANdoes have access to this information becauseSEBASTIANis an authorized participant in theHR Appsrealm. -
Connect as user
SEBASTIAN.CONNECT sebastian@pdb_name Enter password: password
-
Perform the following query:
SELECT FIRST_NAME, LAST_NAME, SALARY FROM HR.EMPLOYEES WHERE ROWNUM <10;
Output similar to the following appears:
FIRST_NAME LAST_NAME SALARY -------------------- ------------------------- ---------- Steven King 24000 Neena Kochhar 17000 Lex De Haan 17000 Alexander Hunold 9000 Bruce Ernst 6000 David Austin 4800 Valli Pataballa 4800 Diana Lorentz 4200 Nancy Greenberg 12008 9 rows selected.
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access
3.5.8 Step 9: Remove the Components for This Tutorial
You can remove the components that you created for this tutorial if you no longer need them.
Parent topic: Quick Start Tutorial: Securing a Schema from DBA Access