Content Security Policy
Content Security Policy (CSP) is a feature that helps to prevent or minimize the risk of certain types of security threats. The primary use case for this is to control which resources, in particular JavaScript resources, a document is allowed to load. By enabling this response header, customers get the security benefits related to this.
Customers are expected to run tests to understand the external URLs they use in the application. Customers should fill in the Content Security Policy (CSP) Modification Request form with details and raise a Service Request to the Oracle Utilities Cloud Operations team to get them included in the CSP.
Note: Content Security Policy will be enabled by default in the 26.4 release, so if external URLs are not added to the CSP, it will result in a loss of functionality.
Testing Your Content Security Policy
To test your Content Security Policy, use the following procedure:
Note: Users must have F1-DEBUG privileges to be able to enable the csp reporting.
Note: The steps below are based on using Google Chrome.
1. Login into the application using your user ID and password.
2. Modify the URL to add the following parameter: ?cspReportOnly=true
Example: http://servername:portno/spl/cis.jsp?cspReportOnly=true
Example: http://servername:portno/spl/cis.jsp?cspReportOnly=true
3. Refresh your browser. In the browser refresh option choose the "Empty cache hard refresh" option. This will ensure that the cache is deleted and all the contents are freshly loaded.
4. Open the Settings menu (Alt + F in Google Chrome), select More Tools, and then select Developer Tools. Ensure you see the Content-Security-Policy-Report-Only response header for all of your different requests.
5. Navigate through CM modules and modules where there is a possibility to use or access other URLs. For example, in the image below we can see that the error is related to a URL missing in the script-src directory.
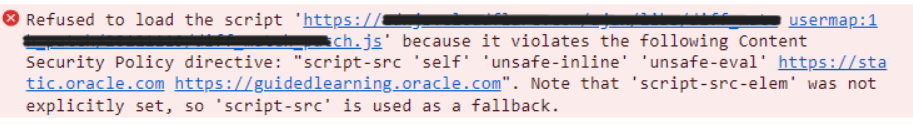
6. Go back to the Developer Tools panel and select the Console tab. Look for possible errors starting with [Report Only] similar to the image above. For example:
[Report Only] Refused to execute inline event handler because it violates the following Content Security Policy directive: …..)
7. Customers can look for the directory name(s) listed in the Content Security Policy Modification Request form. Examples include img-src, script-src, and so on. Collect these and document like the Sample Completed Content Security Policy Modification Request Form below.
8. Logout of the application.
9. In the browser refresh option, choose the "Empty cache hard refresh‘" option. This will ensure that the cache is deleted and all the contents are freshly loaded. This will ensure to fresh download of the static files without the Content-Security-Policy-Report-Only response header.
Content Security Policy Modification Request Form
Below is the form customers should fill out.
Note: The "Cloud Operations Key" will provide the name of the substitution variable.
Environments names: (example: DEV, TEST, PROD)
Directory Name | Cloud Operations Key | URL That is Causing the Violation (For example, if the URL is https://customer-domain1.com/abc/abc.js, then specify https://customer-domain1.com without the path. Multiple URLs should be delimited by spaces.) |
|---|---|---|
img-src | CSP_URL_IMG_SRC | Used as a substitution variable to allow access to an image from an external source. |
script-src | CSP_URL_SCRIPT_SRC | Used as a substitution variable to allow access to a script from an external source. |
frame-src | CSP_URL_FRAME_SRC | Used as a substitution variable to allow access to a frame from an external source. |
style-src | CSP_STYLE_SRC | Used as a substitution variable to allow access to a style from an external source. |
connect-src | CSP_CONNECT_SRC | Used as a substitution variable to allow access to a network connection from an external source. |
font-src | CSP_FONT_SRC | Used as a substitution variable to allow access to a font from an external source. |
To override and or append the content security policy (CSP) to use external customer specific urls, images, fonts and so on with in your cloud service environment, substitution variables may be used but this requires a Service Request from the customer to set these parameters to the required external system.
Sample Completed Content Security Policy Modification Request Form
Here is an example of a completed form:
ENVIRONMENT: DEV01, TEST
Environments names: (example: DEV, TEST, PROD)
Directory Name | Cloud Operations Key | URL That is Causing the Violation (For example, if the URL is https://customer-domain1.com/abc/abc.js, then specify https://customer-domain1.com without the path. Multiple URLs should be delimited by spaces.) |
|---|---|---|
img-src | CSP_URL_IMG_SRC | https://customer-domain1.com |
script-src | CSP_URL_SCRIPT_SRC | https://customer-domain1.com |
frame-src | CSP_URL_FRAME_SRC | |
style-src | CSP_STYLE_SRC | https://customer-domain1.com https://customer-domain2.com |
connect-src | CSP_CONNECT_SRC | |
font-src | CSP_FONT_SRC |