2 Shipboard Property Management System Security Overview
This chapter provides an overview of the Oracle Hospitality Cruise Shipboard Property Management System security and explains the general principles of application security.
Basic Security Considerations
The following principles are fundamental in order to use any application securely:
-
Keep software up to date. This includes the latest product release and any patches that apply to it.
-
Limit privileges as much as possible. You should be given only the access necessary to perform their work. User privileges should be reviewed periodically to determine relevance to current work requirements.
-
Monitor system activity. Establish who should access which system components, and how often, and monitor those components.
-
Install software securely. For example, use firewalls, secure protocols using Transport Layer Security (TLS), Secure Sockets Layer (SSL) and secure passwords. See Performing a Secure Shipboard Property Management System Installation for more information.
-
Use secure development practices. For example, take advantage of existing database security functionality instead of creating your own application security. See Security Considerations for Developers for more information.
-
Keep up to date on security information. Oracle regularly issues security-related patch updates and security alerts. You must install all security patches as soon as possible. See the “Critical Patch Updates and Security Alerts” website:http://www.oracle.com/technetwork/topics/security/alerts-086861.html
Overview of Shipboard Property Management Security
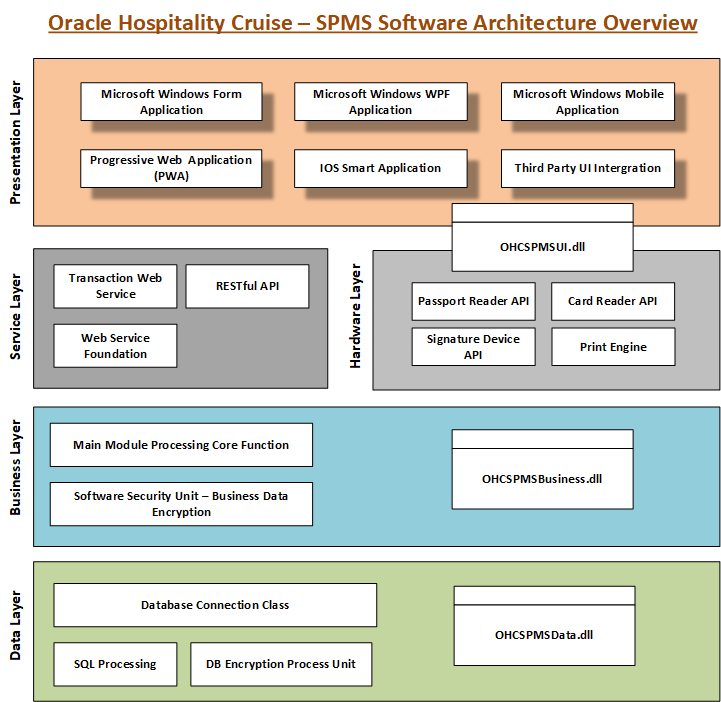
SPMS Architecture Overview
The SPMS uses an N-Tier/3-Tier Architecture style. Most of the application components are Microsoft Windows desktop applications, interfaces, RESTful API, Progressive Web application (WPA), and a few web services used for third party integration. It is scalable since clients/interfaces, databases, and web services can be distributed onto three or more machines and does not have to be deployed on a single machine.
Technology
Shipboard Property Management System Web Services uses industry standard Simple Object Access Protocol (SOAP)/JavaScript Object Notation (JSON) to work with internal and external applications. Typically, web services are deployed and exposed on the Microsoft Internet Information Services (IIS) Webserver, and IIS provides options to secure the communications using the Secure Sockets Layer (SSL). It also uses Transmission Control Protocol /Internet Protocol (TCP-IP) and File System for integration internally and externally. Every communication can be configured to use the Secure Sockets Layer (SSL) if required. It also uses strong encryption/hashing algorithms (Microsoft managed Rijndael, Microsoft Windows Data Protection Application Programming Interface (DPAPI), Password-Based Key Derivation Function 2 (PBKDF2)) to encrypt and store sensitive customer information, application user passwords, application configuration information, secrets, and passwords.
Figure 2-1 SPMS Network Architecture Diagram
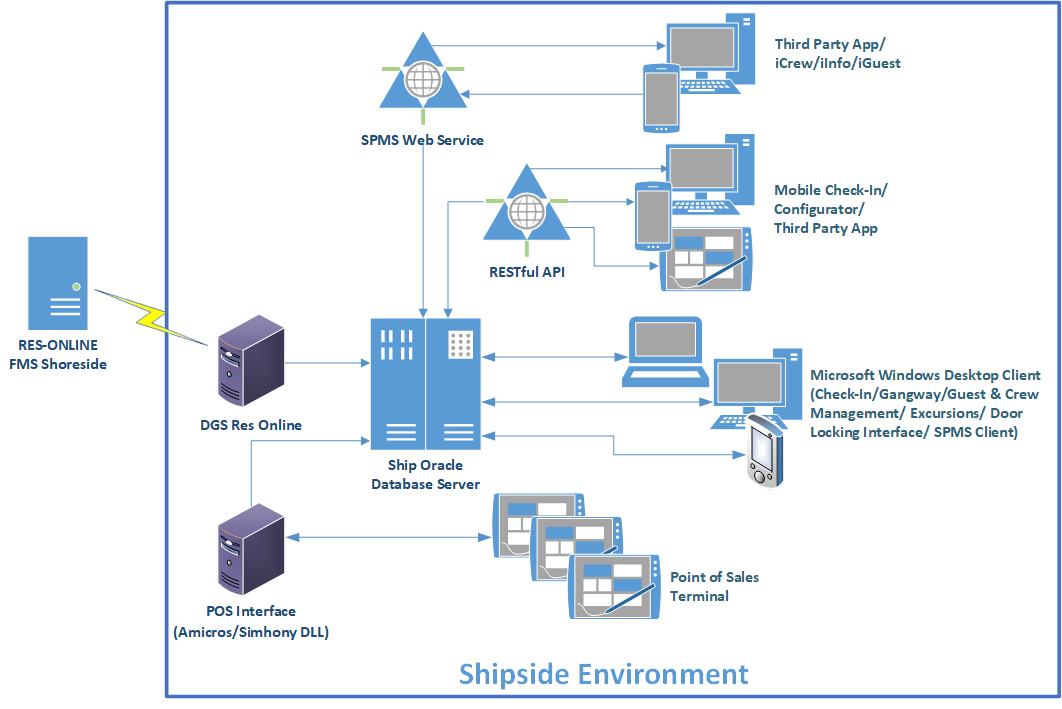
Figure 2-2 SPMS Software Architecture Diagram
User Authentication
Overview
Authentication is a process of ensuring that people are who they say they are.
Thick/ Windows Desktop Client/ RESTful API/ PWA Authentication
All user credentials for the SPMS are stored in the database. Anyone who wishes to access the desktop client must provide a valid username and password. To ensure strict access control of Shipboard Management, always assign unique usernames and complex passwords to each user. The passwords must follow the Payment Card Industry-Data Security Standard (PCI-DSS) guidelines and must have at least 8 characters and a combination of letters and numbers.
Web Service Authentication
The Security Session ID Approach is used in the Web Services/Web Apps only. For the first request from a client, predefined credentials are passed to gain a session ID, and this session ID is used with subsequent requests throughout the session.
Database Users
The Shipboard Property Management System stores the database user password on a local machine in an encrypted format using Microsoft Windows DPAPI (Data Protection Application Programming Interface) starting from Microsoft Windows 2000 onwards.
Security Note
The Oracle database user password and Key Encryption Key (KEK) are hosted/stored on a SPMS Security Server (OHC Secure Login Web Service), deployed on the IIS web server. Clients need to connect to the Security Server once to fetch the Database user password and KEK, and store them locally in their configuration file in an encrypted form using the Microsoft Windows DPAPI method. The Client uses a password stored in the configuration file to connect to the Database. The Client will only connect to the SPMS Security Server again to fetch the password, if the Database user password is changed.
Understanding the SPMS Environment
-
Which resources need to be protected?
-
You need to protect customer data, such as credit-card numbers.
-
You need to protect internal data, such as proprietary source code.
-
You need to protect system components from being disabled by external attacks or intentional system overloads.
-
-
Who are you protecting data from?
Any of your subscriber’s data from other subscribers, but someone in your organization might need to access that data to manage it. You can analyze your workflow to determine who needs access to the data; for example, it is possible that a system administrator can manage your system components without needing to access the system data.
-
What will happen if protections on strategic resources fail?
In some cases, a fault in your security scheme is nothing more than an inconvenience. In other cases, a fault might cause great damage to you or your customers. Understanding the security ramifications of each resource will help you protect it properly.
Recommended Deployment Configurations
This section describes recommended deployment configurations for the SPMS.
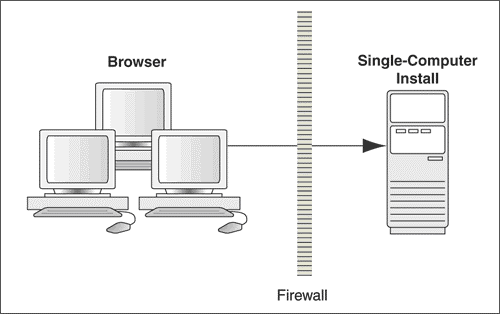
The SPMS can be deployed on a single server or in a cluster of servers. The simplest deployment architecture is the one shown in Figure 2-3.
This single-computer deployment may be cost effective for small organizations; however, it cannot provide high availability because all components are stored on the same computer. In a single server environment such as the typical installation, the server should be protected behind a firewall.
Figure 2-3 Simple Computer Deployment Architecture
The general architectural recommendation is to use the well-known and generally accepted Internet-Firewall-DMZ-Firewall-Intranet architecture as shown in the figure below.
Figure 2-4 Traditional DMZ View
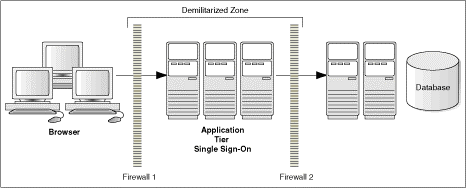
-
Blocking any traffic types that are known to be illegal.
-
Providing intrusion containment, should successful intrusions take over processes or processors.
See Appendix A - Shipboard Property Management System Ports Numbers for more information about the SPMS network port usage.
Component Security
Operating System Security
Before installing the SPMS, the operating system must be updated with the latest security updates.
Oracle Database Security
See Oracle Database Security Guide for more information about Oracle Database security.
Web Security
Use only HTTPS or Transport Layer Security (TLS) security obtained from a certification authority for the SPMS application.