2 Security Model
This chapter covers the following sections:
Terminology
This section defines Security Terms used.
Table 2-1 Security Terms
| Term | Definition |
|---|---|
|
Application Administrator |
A customer application admin user who can perform application configurations via SIOCS admin screen. |
|
Application Implementer |
System implementer is user who implements the application. |
|
Customer Cloud Administrator |
A delegated customer cloud user for customer cloud management tasks, for example create customer security admin user, and other users. |
|
Customer Security Admin |
A customer security admin user who can create customer users and assign application roles. Please note that sometimes this may not be setup as a separate user than application administrator. |
|
IDCS or OCI IAM Application Role |
IDCS or OCI IAM application roles are specific user entitlements that are created at the time of provisioning EICS application on IDCS or OCI IAM. Each IDCS or OCI IAM application role creates a security group. |
|
Retail Home User |
A user who can access SIOCS tile reports on Retail Home and navigate to related operational views in SIOCS from there. |
|
Security Group |
A collection of users and groups. These groups are created automatically at the time of provisioning EICS application on IDCS or OCI IAM for each IDCS or OCI IAM application role. These groups are known to the Java EE server container. |
|
SIOCS Application Role |
SIOCS application role is a collection of users and other application roles. SIOCS Application roles are defined in the applications and they are not necessarily known to a Java Container. |
|
Store Manager |
A user who performs store manager role. |
|
Store User |
A user who performs store operations with assigned role permissions. |
|
System Operator |
Will be used by Oracle cloud team for debug. |
|
User |
A user is an end-user accessing a service or application. |
In addition to application users, integration users need to be setup based on integrated applications.
User Access to Functionality
Users of SIOCS have roles through which they gain access to functions and data.
Security implementation involves the management of:
-
User creations
-
Assigning IDCS or OCI IAM Application Roles to corporate operational users
-
Assigning IDCS or OCI IAM Groups to corporate operational users
-
Assigning SIOCS Application Roles to store users
IDCS or OCI IAM Application Roles
SIOCS comes with nine IDCS or OCI IAM application roles used for special purpose access. These IDCS or OCI IAM application roles are defined inside EICS application on IDCS or OCI IAM.
All
The IDCS or OCI IAM application role all_users is required to access SIOCS.
This app role should be assigned to all users.
Admin
The IDCS or OCI IAM application role admin_users is required for access to administration tasks, such as managing configuration settings or translations.
This IDCS or OCI IAM application role should only be assigned to system operators and administrators.
Batch
This IDCS or OCI IAM application role should only be assigned to system operators and batch administrators.
The IDCS or OCI IAM application role batch_users is required for access to batch related tasks, such as job management or scheduling.
Full Permission
The IDCS or OCI IAM application role full_permission_users allows the user to gain access to all available permissions without any database role assignment.
This IDCS or OCI IAM application role should only be assigned to system operator and initial customer admin user.
Note:
This full permissions IDCS or OCI IAM application role does not provide full data permission access. For performing administration operations, user should be assigned ADMINISTRATOR SIOCS application role in SIOCS application.
Global Store User
The IDCS or OCI IAM application role global_store_users grants the user access to all store locations.
This IDCS or OCI IAM application role should only be assigned to system operators, and administrators or special users requiring access to all store locations.
Integration
The IDCS or OCI IAM application role integration_users is required for accessing integration resources, such as web services.
This IDCS or OCI IAM application role should only be assigned to users designated for application integration, not those requiring access to the application UI.
Users that are only integrating with SIOCS are considered integration users, for example, the RIB injection user is a typical case of an integration user.
These users do not require access to the SIOCS client applications, and therefore do not require store assignments or role assignments (permissions).
MPS
The IDCS or OCI IAM application role mps_users is required for access to MPS (message processing service) related tasks, such as staged message maintenance or work type management.
This IDCS or OCI IAM application role should only be assigned to system operators and MPS administrators.
Security
The IDCS or OCI IAM application role security_users is required for access to security management tasks, such as role maintenance and user role/store assignments.
This IDCS or OCI IAM application role should only be assigned to system operators and security administrators.
Users accessing application UI features that are restricted by group access must also be granted the relevant permissions through role and store assignments.
A regular store user should not require this assignment for accessing the application UI.
System Operator
The IDCS or OCI IAM application role sysop_users is required for access to restricted areas of the application, such as certain system configuration settings.
This IDCS or OCI IAM application role should only be assigned to system operators, which are typically the cloud operator.
Note:
The sysop_users IDCS or OCI IAM application role is for internal use by Oracle team only and should not be assigned to customer users.
These IDCS or OCI IAM application roles are scoped to the EICS application on IDCS or OCI IAM. Since a new EICS application will be provisioned on IDCS or OCI IAM for each deployment type, there won't be any overlap in IDCS or OCI IAM application roles between different deployment types. This allows a Customer Security Admin to assign an IDCS or OCI IAM application role to a user on one deployment and not on others.
IDCS or OCI IAM application roles are assigned to users through IDCS or OCI IAM.
Each IDCS or OCI IAM application role creates one security group. These security groups are not visible on IDCS or OCI IAM but the access can be managed via the associated IDCS or OCI IAM application role.
For example, assigning admin_users IDCS or OCI IAM application role to a user will automatically assign the associated security group, thus providing access to administration tasks to the user.
This table identifies IDCS or OCI IAM application roles:
Table 2-2 IDCS or OCI IAM Application Roles
| Cloud Service or Options | IDCS or OCI IAM Application Roles |
|---|---|
|
Admin Service |
admin_users |
|
Authenticated |
all_users |
|
Batch Service |
batch_users |
|
Initial user setup to login to EICS application |
full_permission_users |
|
All store locations |
global_store_users |
|
Integration Service |
integration_users |
|
Message Processing Service |
mps_users |
|
Security Service |
security_users |
|
Perform application system configurations (both non-restricted and restricted) |
sysop_users |
IDCS or OCI IAM Groups
SIOCS comes with three IDCS or OCI IAM groups used for special purpose access. These groups can be found under Groups section on the IDCS or OCI IAM admin console.
PSRAF Users
The IDCS or OCI IAM group psraf_users is required to access platform features, for example, Favorites.
This group should be assigned to all users.
The naming convention for the group is <EICS_IDCS_APP_DISPLAY_NAME>.psraf_users where EICS_IDCS_APP_DISPLAY_NAME is the display name of EICS app on IDCS or OCI IAM.
PSRAF Admin Users
The IDCS or OCI IAM group psraf_admin_users is required to access platform admin features to users logging in via Retail Home, for example, Notification types.
This group should be assigned to all Retail Home users that need access to .platform admin features.
The naming convention for the group is <EICS_IDCS_APP_DISPLAY_NAME>.psraf_admin_users where EICS_IDCS_APP_DISPLAY_NAME is the display name of EICS app on IDCS or OCI IAM.
Retail Home
The IDCS or OCI IAM group retail_home_users is required for Retail Home application users to access SIOCS tile APIs.
This group should be assigned to all Retail Home users that need access to SIOCS tiles.
The naming convention for the group is <EICS_IDCS_APP_DISPLAY_NAME>.retail_home_users where EICS_IDCS_APP_DISPLAY_NAME is the display name of EICS app on IDCS.
Note:
The naming convention for the group is <EICS_IDCS_APP_DISPLAY_NAME>.<GROUP_NAME> where EICS_IDCS_APP_DISPLAY_NAME is the display name of EICS app on IDCS or OCI IAM and GROUP_NAME is the name of the group.
For example, RGBU_SIOCS_PRD_EICS.psraf_users and RGBU_SIOCS_PRD_EICS.retail_home_users.
These IDCS or OCI IAM groups are scoped globally so in order to differentiate between deployment types, the group names are prefixed by the app name that they belong to. This allows a Customer Security Admin to assign an IDCS or OCI IAM group to a user on one deployment and not on others.
IDCS or OCI IAM groups are assigned to users through IDCS or OCI IAM.
SIOCS Application Roles
SIOCS application roles are a collection of permissions that are assigned to users for specific or all of their assigned stores. These permissions are used to control access to application functionality and data. Roles are created, managed, and assigned to users through the SIOCS security admin UI.
SIOCS has the following predefined application roles.
Table 2-3 Predefined Application Roles
| Operations | SIOCS Application Role |
|---|---|
|
Admin permission role |
ADMINISTRATOR |
|
Store Manager permission role |
MANAGER |
|
Retail Home permission role |
RETAIL HOME |
Role Permissions Configuration
There are 350+ configuration settings that decide how users access functionality. For details, see the Oracle Retail Enterprise Inventory Cloud Service Administration Guide - Configuration chapter.
User Types
Table 2-4 User Types with IDCS or OCI IAM Application Roles, IDCS or OCI IAM Group, and SIOCS Application Roles
| Application User Type | Job Duties | SIOCS Application Roles Assigned (User Role Assignment is via SIOCS Security Admin Screen) | IDCS or OCI IAM Application Role Assigned(Role Assignment is via IDCS or OCI IAM) | IDCS or OCI IAM Group Assigned(Group Assignment is via IDCS or OCI IAM) |
|---|---|---|---|---|
|
Initial Application Admin User |
To access SIOCS application and create other application admin and store users. |
N/A |
all_users admin_users batch_users full_permission_users global_store_users mps_users security_users |
psraf_users |
|
Application Admin User |
Perform all administration activities, setup other customer application store users and perform application configuration. |
ADMINISTRATOR |
all_users admin_users batch_users global_store_users mps_users security_users |
psraf_users |
|
Store Users |
Perform store operations in store using Mobile client. |
Custom Defined Role with selected role permissions. |
all_users |
psraf_users |
|
Integration Users |
External system invokes EICS provided Integration Services. See Integration Implementation sections for additional details. |
N/A |
integration_users |
|
|
Retail Home User |
Access SIOCS tiles on retail home and navigate to related operational views in SIOCS. |
RETAIL HOME |
all_users |
psraf_users retail_home_users |
User Provisioning
Before users can access the Oracle Retail Stores Inventory and Operations Cloud Service applications, it is necessary to provision each user access to the system, and assign IDCS or OCI IAM application roles, stores, and SIOCS application roles to each user to control what functionality will be available to them. The access provisioning is done using Oracle Identity Cloud Service (IDCS) or Oracle Cloud Infrastructure Identity and Access Management (OCI IAM) for initial customer admin user. This user can create or manage other user provisioning via IDCS or OCI IAM and the SIOCS security admin UI.
IDCS or OCI IAM application roles assignments are typically used for special purpose access such as integration or various administration tasks. IDCS or OCI IAM application roles are assigned to users through IDCS or OCI IAM.
The application client uses store based sessions for performing business operations. Store assignments control the stores available for a user to login to. Users can be assigned access to specific stores through the SIOCS security admin UI.
SIOCS application roles are a collection of permissions that are assigned to users for specific or all of their assigned stores. These permissions are used to control access to application functionality and data. Roles are created, managed, and assigned to users through the SIOCS security admin UI.
Figure 2-1 EICS Security Model
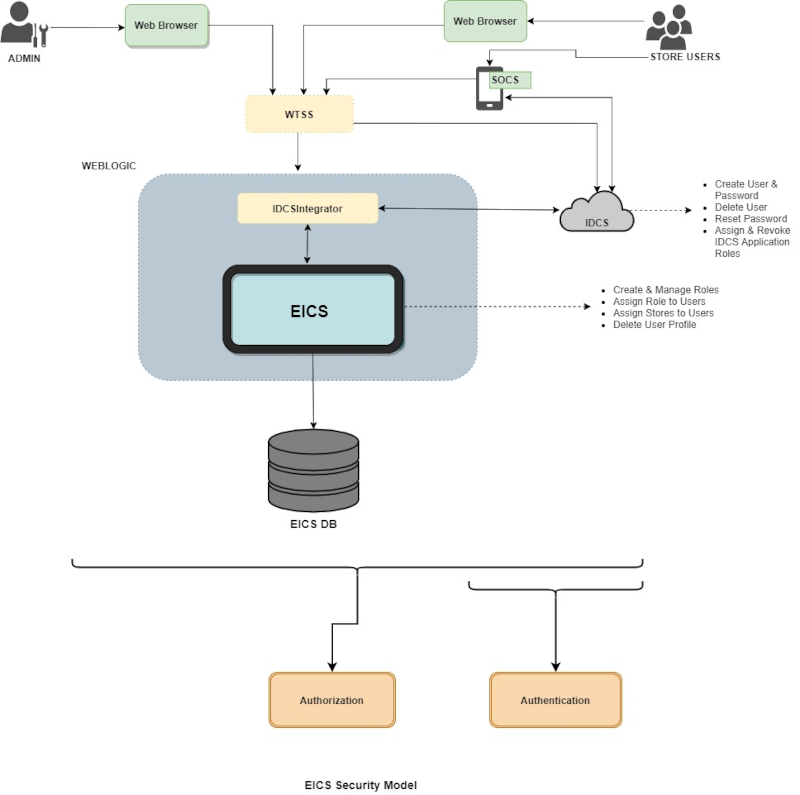
User Access
It is recommended that users are granted the least level of access they require to perform their duties.
Users should not be reused or shared by multiple people or for multiple purposes.
For example, users created for integration purposes should not be granted access required for application UI usage.
Oracle Identity Cloud Service Access Management
Oracle Identity Cloud Service (IDCS) provides a fully integrated service that delivers all the core identity and access management capabilities through a multi-tenant Cloud platform.
Figure 2-2 IDCS Access Management
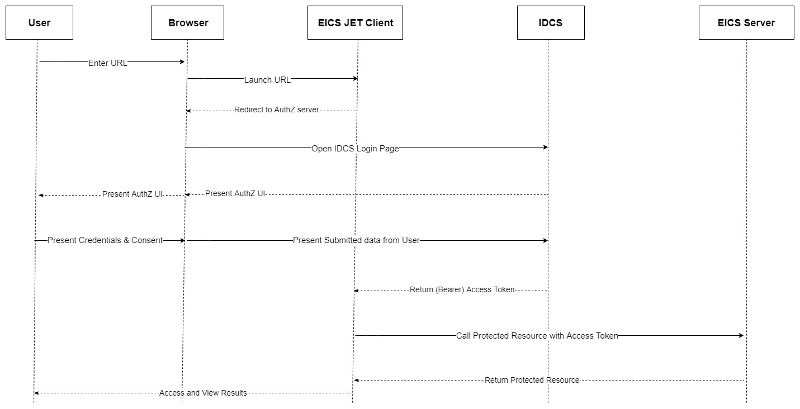
For instructions on managing users in IDCS, follow the Manage Users IDCS document at the following URL:
https://docs.oracle.com/en/cloud/paas/identity-cloud/index.html
IDCS Groups are used for special purpose access. A Customer Security Admin can assign IDCS groups to users on IDCS as follows:
-
Log into the IDCS console.
-
Select Groups from the Navigation Drawer.
-
Locate and click on the group.
-
Once inside group detail, select the users tab.
-
Click on the +Assign button to open Assign Users dialog.
-
Tick the users that you want to assign the group to.
-
Click the OK button to apply changes.
IDCS Application Roles are used for special purpose access. A Customer Security Admin can assign IDCS application roles to users on IDCS as follows:
-
Log into the IDCS console.
-
Select Oracle Cloud Services from the Navigation Drawer.
-
Locate and click on the EICS application for your deployment.
-
Navigate to the Application Roles tab.
-
Open the application role menu (
 ) for the role you want to assign and select Assign Users.
) for the role you want to assign and select Assign Users.
-
Select the users that you want to assign the IDCS application role to and click Assign.
You can also use the IDCS application role menu to revoke a role from a team member.
Assigning an IDCS application role will automatically assign the associated security group to the user. These security groups are not visible on the IDCS UI and are only maintained internally.
Oracle Cloud Infrastructure Identity and Access Management
Oracle Cloud Infrastructure Identity and Access Management (IAM) provides identity and access management features such as authentication, single sign-on (SSO), and identity lifecycle management for Oracle Cloud.
For instructions on managing users in OCI IAM, follow the Manage Users OCI IAM document at the following URL:
https://docs.oracle.com/en-us/iaas/Content/Identity/home.html