Configure AWS Key Management Service (KMS) to store TDE Master Encryption Key for Exadata Database Service on Dedicated Infrastructure on Oracle Database@AWS
Introduction
This guide explains how to integrate AWS Key Management Service (KMS) with Oracle Exadata Database Service on Dedicated Infrastructure, part of Oracle Database@AWS. With this integration, organizations can centrally manage Transparent Data Encryption (TDE) master keys using AWS KMS.
Key benefits
- Centralized Key Management: Use AWS KMS to centrally manage encryption keys across Oracle Database workloads.
- Organization-Specific Security Policies: Flexibly adhere to enterprise key management and compliance requirements.
- Seamless Integration: Support for TDE-protected data with transparent transition from Oracle Wallet to AWS Customer Managed Keys.
- Audit and Lifecycle Management: Benefit from AWS KMS auditing, and key control features.
- Granular Access Control: Leverage AWS IAM and Oracle IAM policies for secure and controlled key access.
Objectives
- Enable and configure AWS KMS as the key management solution for Exadata Database Service on Dedicated Infrastructure on Oracle Database@AWS.
Prerequisites
- Oracle Database@AWS environment with necessary administrative access to both AWS and Oracle Cloud Infrastructure (OCI) consoles.
- AWS KMS and IAM privileges for creating and managing keys and roles.
- Exadata VM Cluster provisioned.
- OCI IAM Policy to allow Exadata VM Clusters to access AWS KMS keys:
allow any-user to read oracle-db-aws-keys in compartment id <your-compartment-OCID> where all { request.principal.type = 'cloudvmcluster'} - Oracle Database 19c or later.
Task 1: Verify and Configure OCI Identity Domain
-
In the AWS Console, select Settings in Oracle Database@AWS page. Confirm the OCI Identity Domain Status is Available.
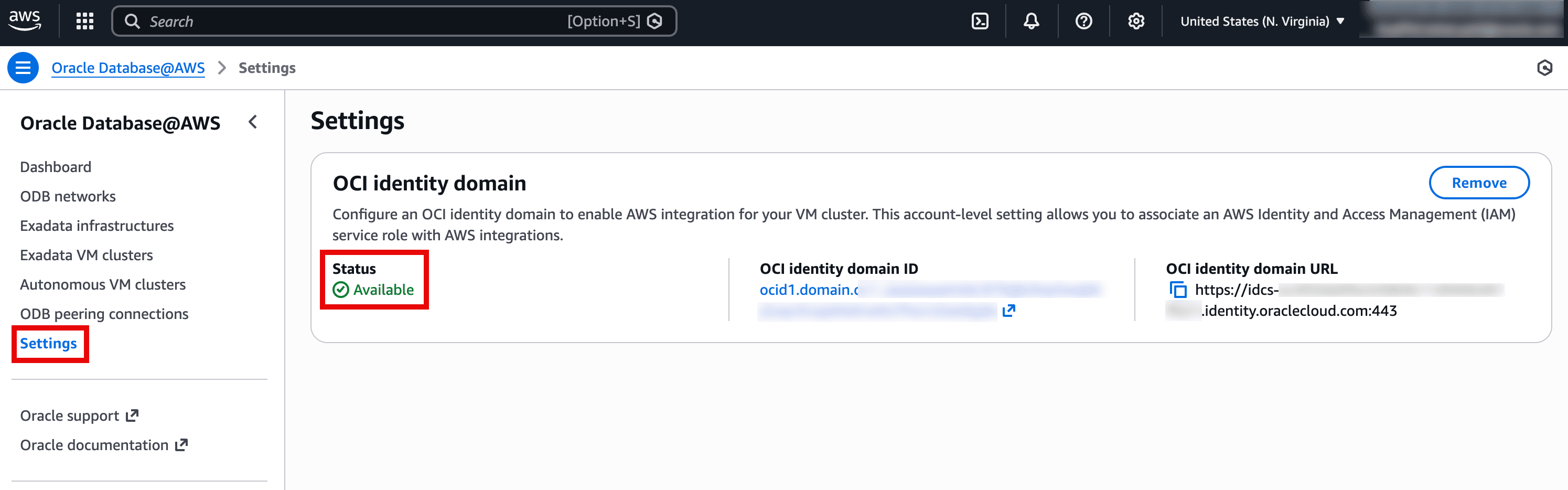
Description of the illustration verify-oci-identity-domain.png
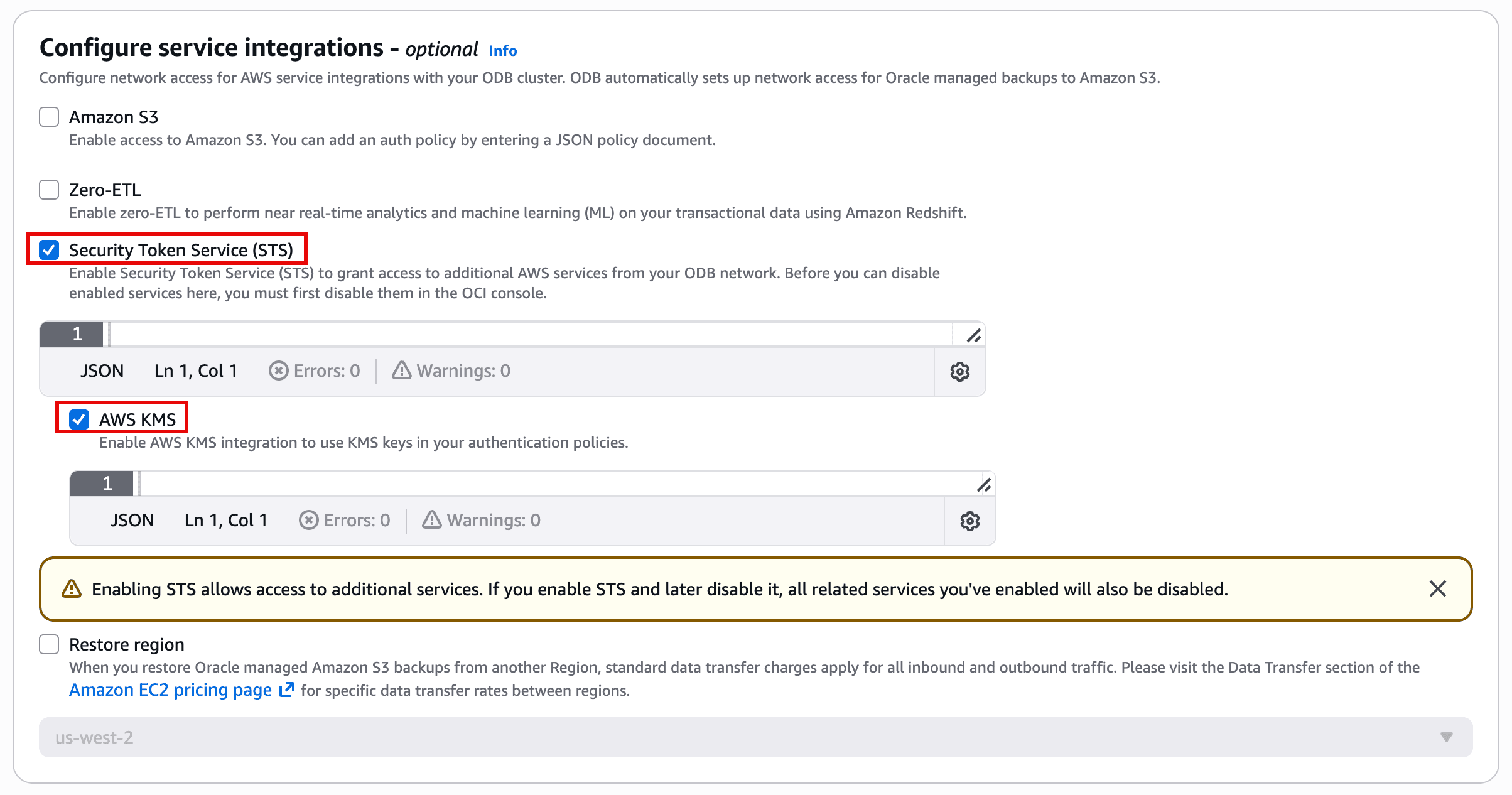
Task 2: Enable Security Token Service and AWS KMS in ODB Network
-
In the AWS Console, select ODB Networks in Oracle Database@AWS page. Either modify an existing ODB Network or create a new one.
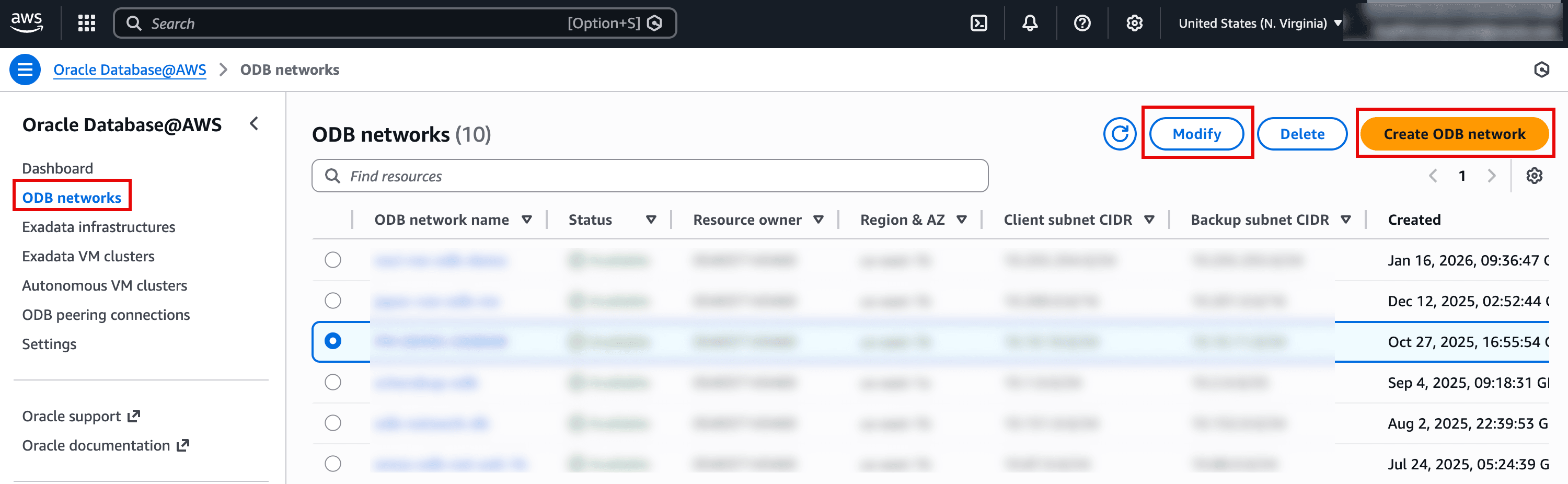
-
Under Configure service integrations, enable Security Token Service (STS) and AWS KMS options to allow the VM cluster to communicate securely with AWS KMS.
Task 3: Configure AWS Identity Provider (OIDC) and IAM Role
-
In the AWS Console, select Exadata VM clusters in Oracle Database@AWS page. Select the Exadata VM Cluster for which you want to enable AWS KMS Key Management.
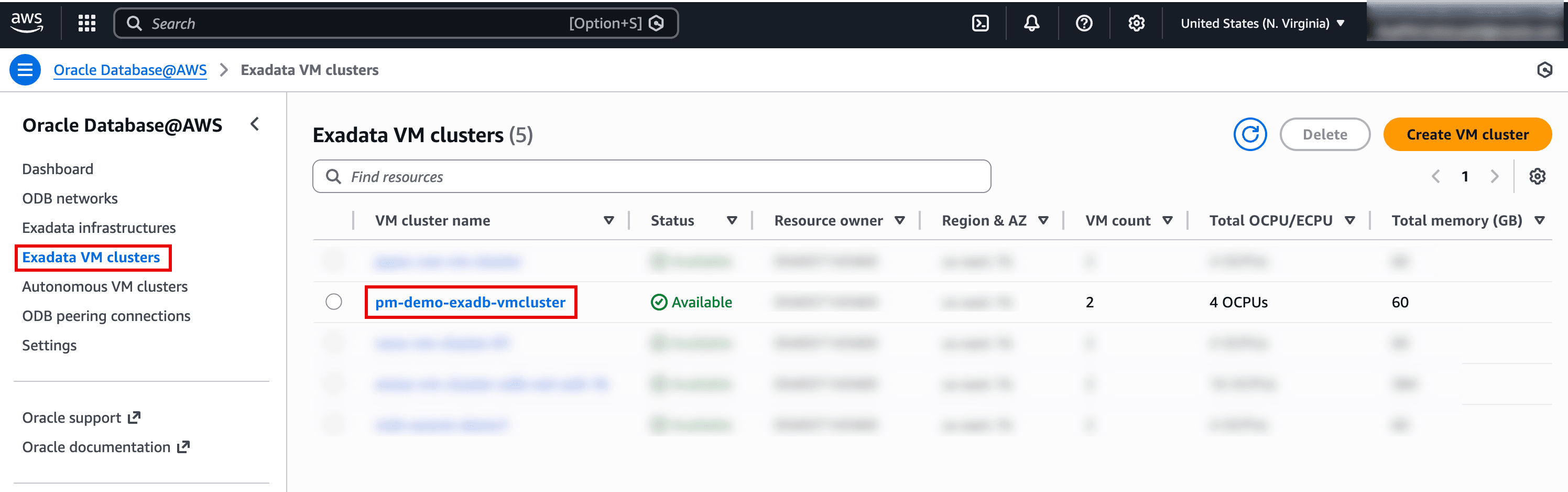
Description of the illustration Select-Exadata-VM-Cluster.png
-
From the Exadata VM Cluster’s details page, go to the IAM service roles tab and select the CloudFormation link to open the AWS Quick Create Stack page.
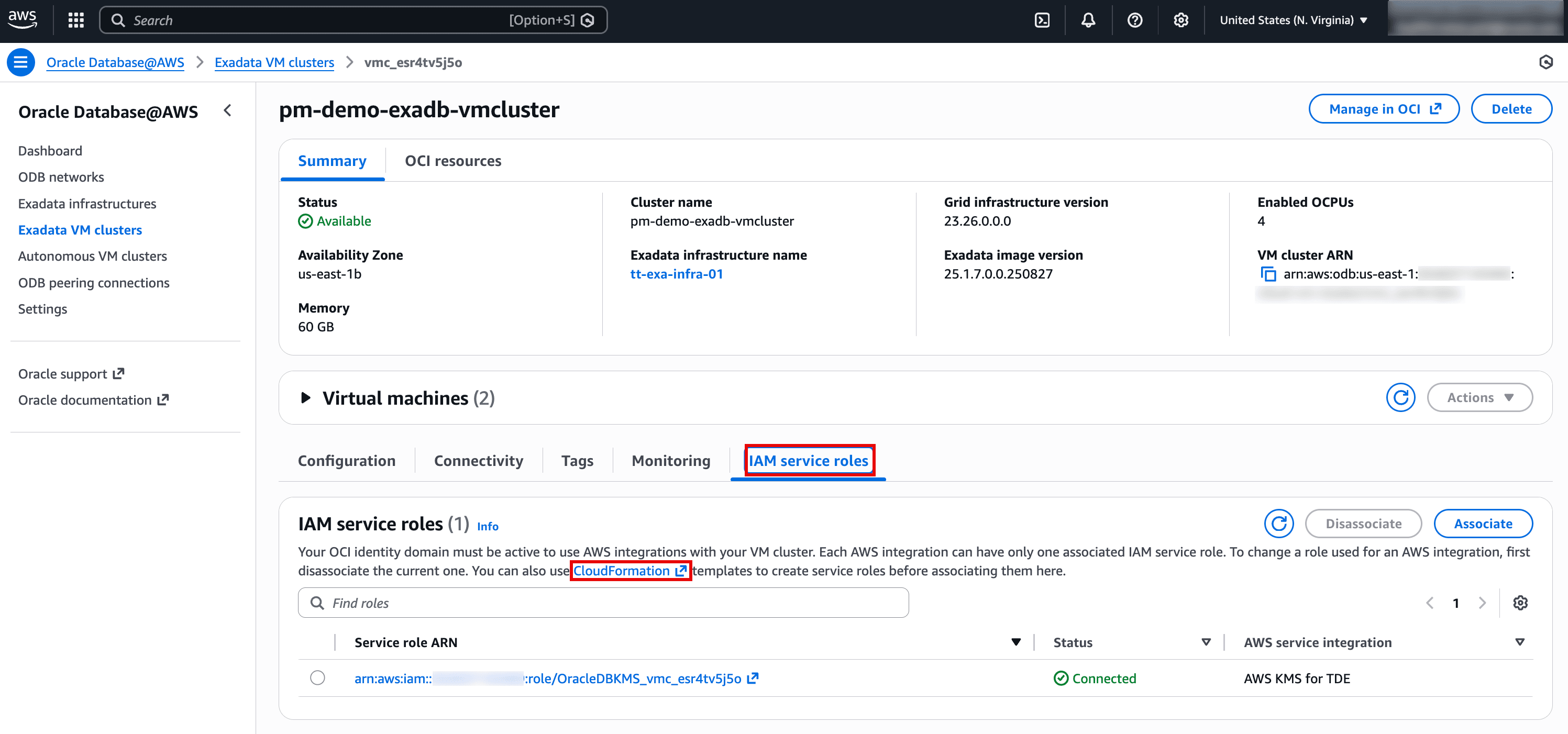
Description of the illustration Click-CloudFormation-link.png
-
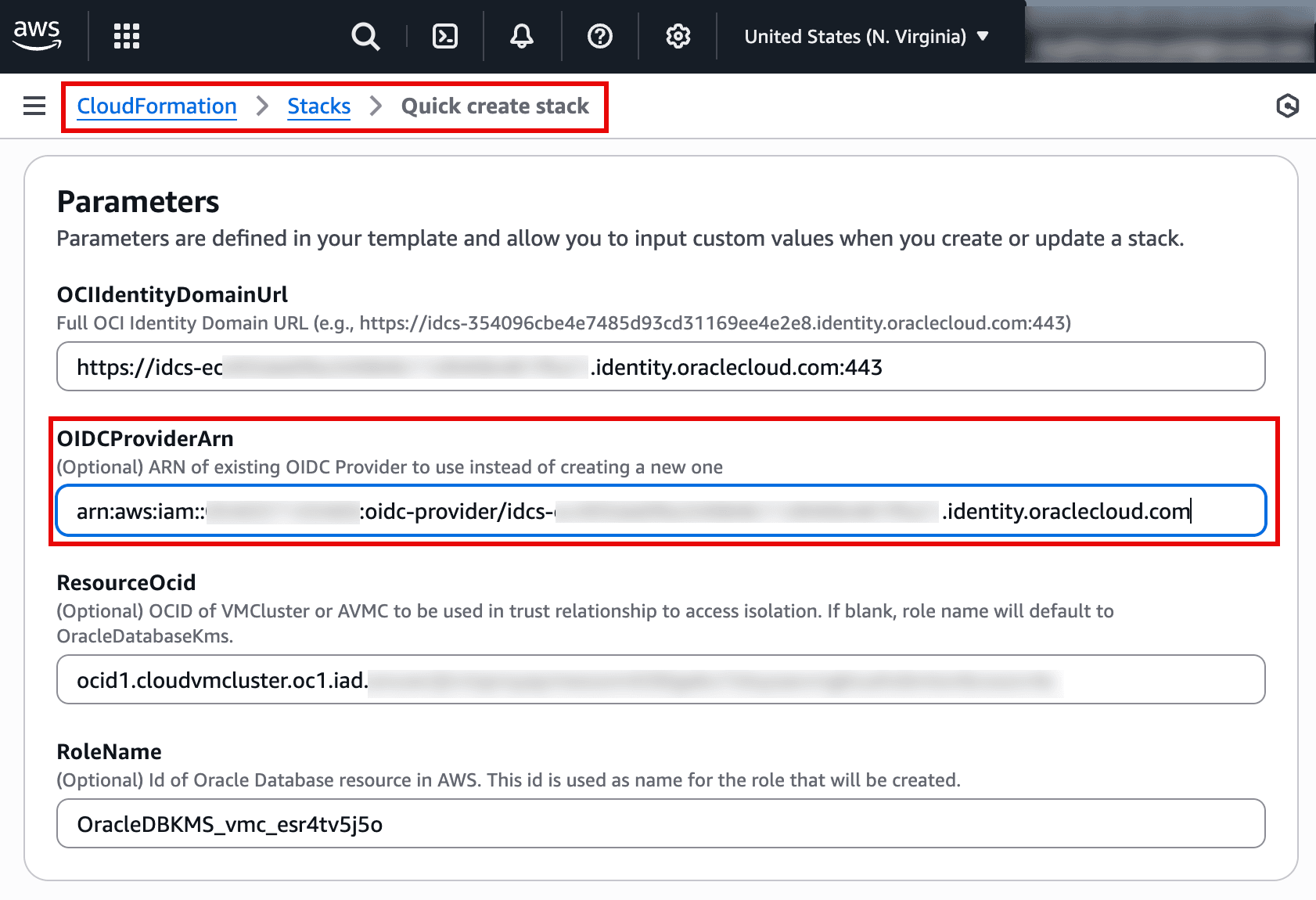
If this is the first time you are creating OpenID Connect Provider then leave OIDCProviderArn blank to create a new OIDC provider. For subsequent executions, provide the existing OIDCProviderArn. Existing OpenID Connect provider details including ARN can be found by going to IAM page and then click Identity providers.
-
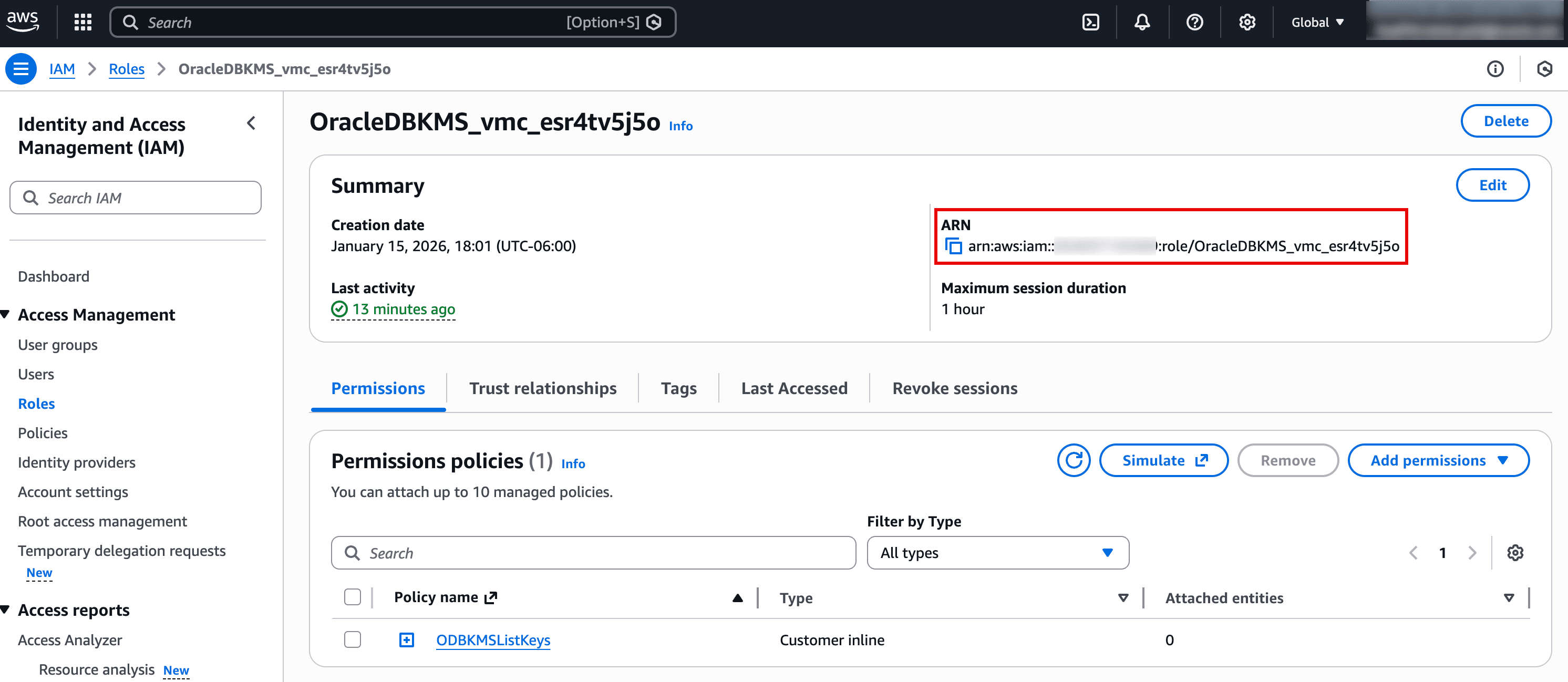
Proceed to create the stack. Once completed, find the details of resources created such as OIDC provider and IAM role. Click on the link under Physical ID for WebIdentityRole resource.
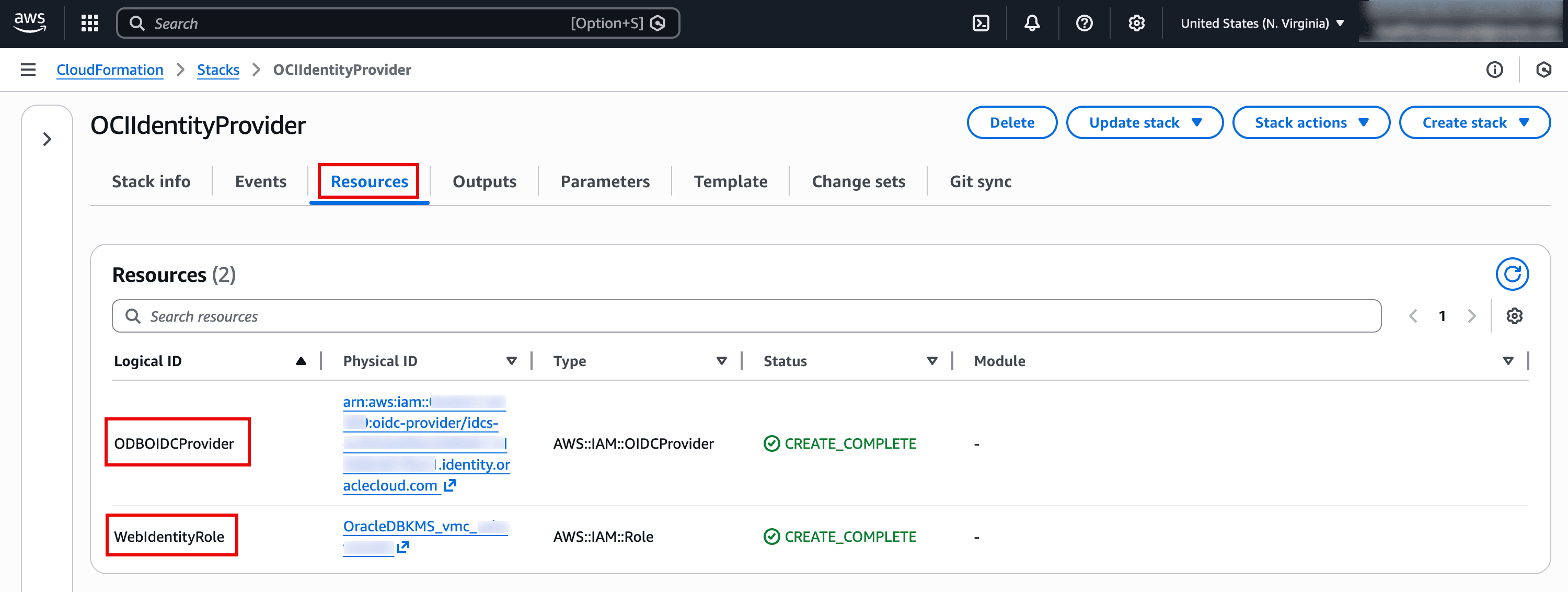
Description of the illustration CloudFormation-Resources.png
-
Copy the ARN of the created IAM role for next step.
Task 4: Associate IAM Role to Exadata VM Cluster
-
In the AWS Console, navigate to Oracle Database@AWS page and click on Exadata VM clusters. Select your Exadata VM Cluster to open its details page. Go to the IAM service roles tab and click Associate. Paste the ARN of IAM service role copied in previous step and click Associate.
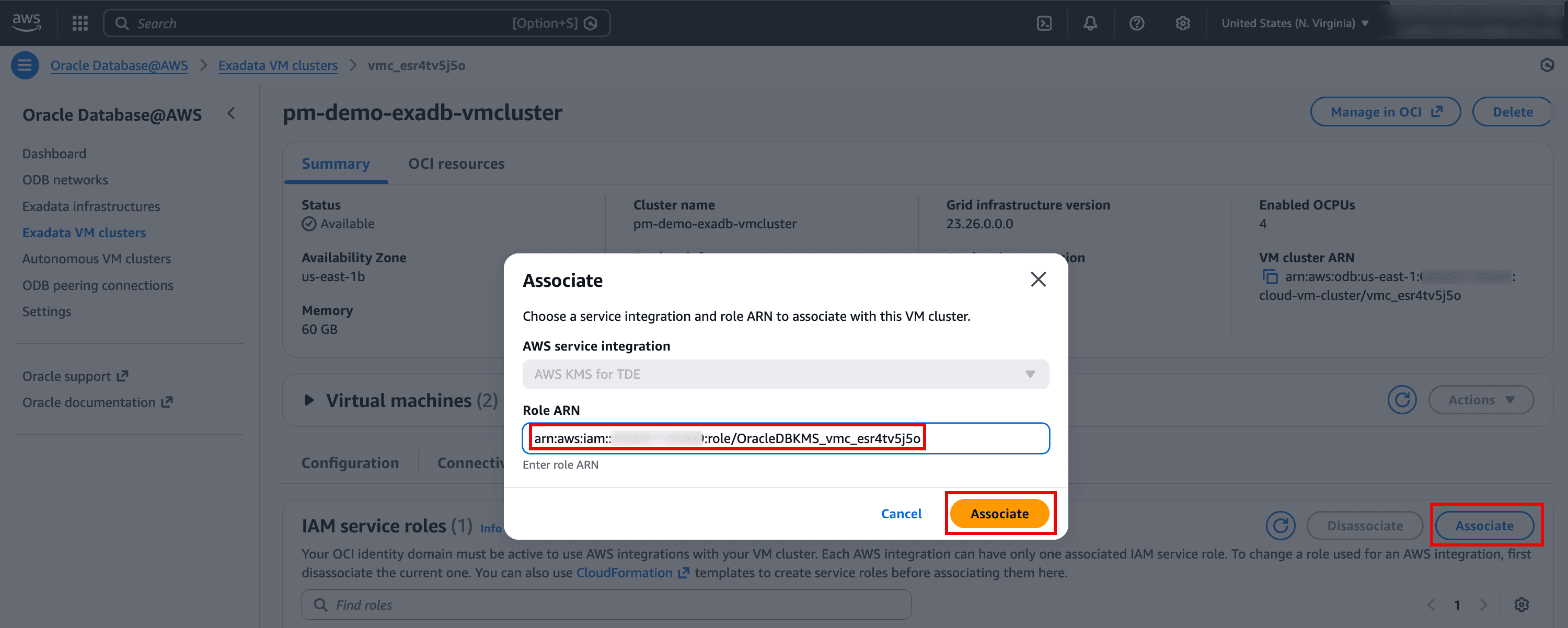
Description of the illustration Associate-IAM-Service-Role.png
-
Once IAM role is associated to the Exadata VM Cluster, it will show status as Connected.
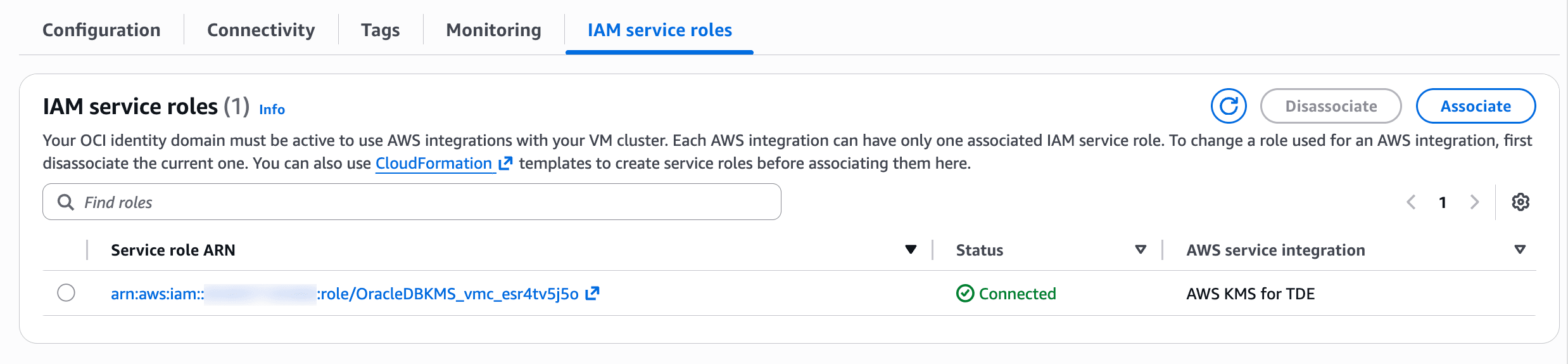
Description of the illustration Connected-IAM-Service-Role.png
Task 5: Create a Customer Managed Key in AWS KMS
-
In the AWS Console, go to Key Management Service (KMS) and then click Customer managed keys. Click Create key. Choose below options and click Next.
Key type: Symmetric
Key usage: Encrypt and decrypt
(Optional) Key material origin: Choose KMS-recommended or AWS CloudHSM key store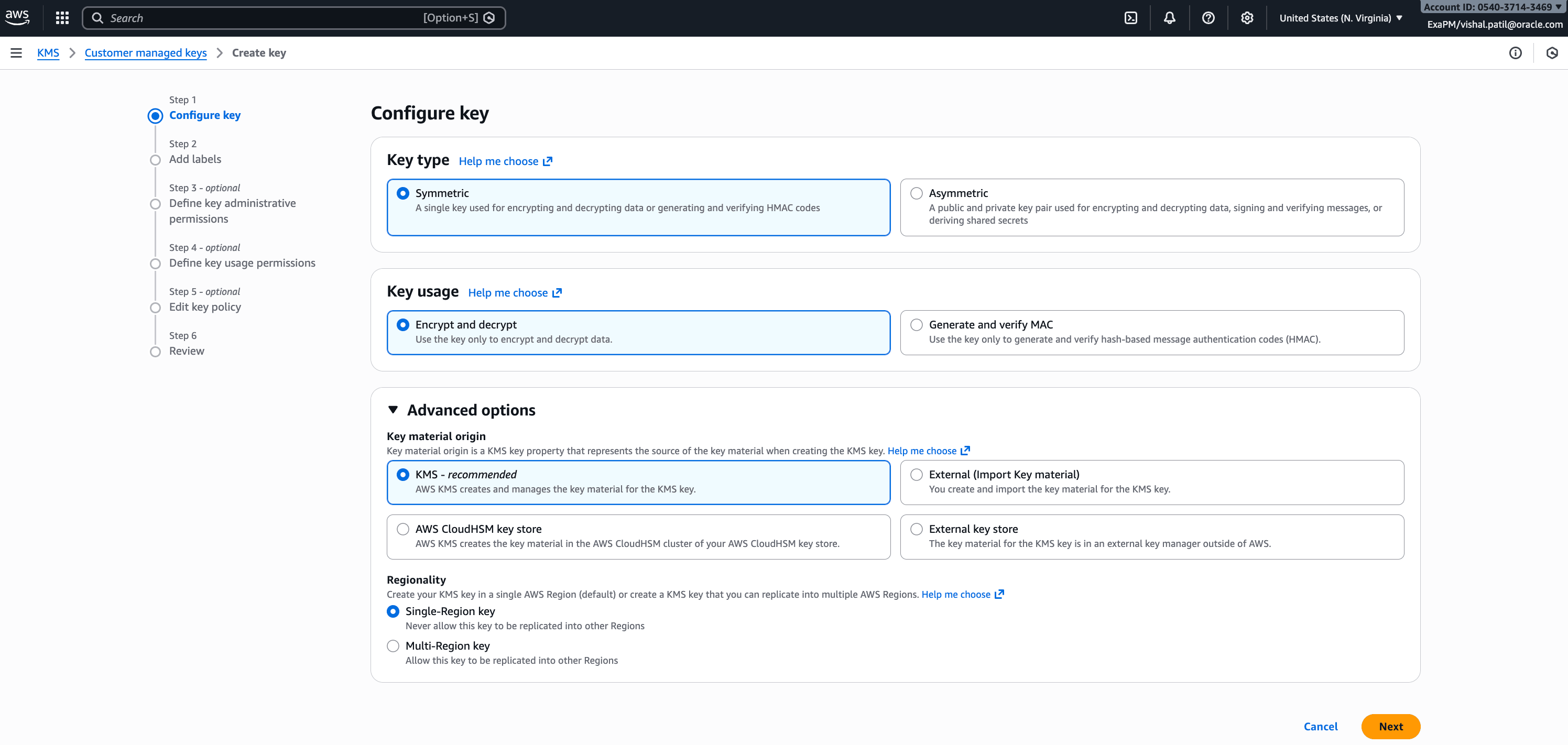
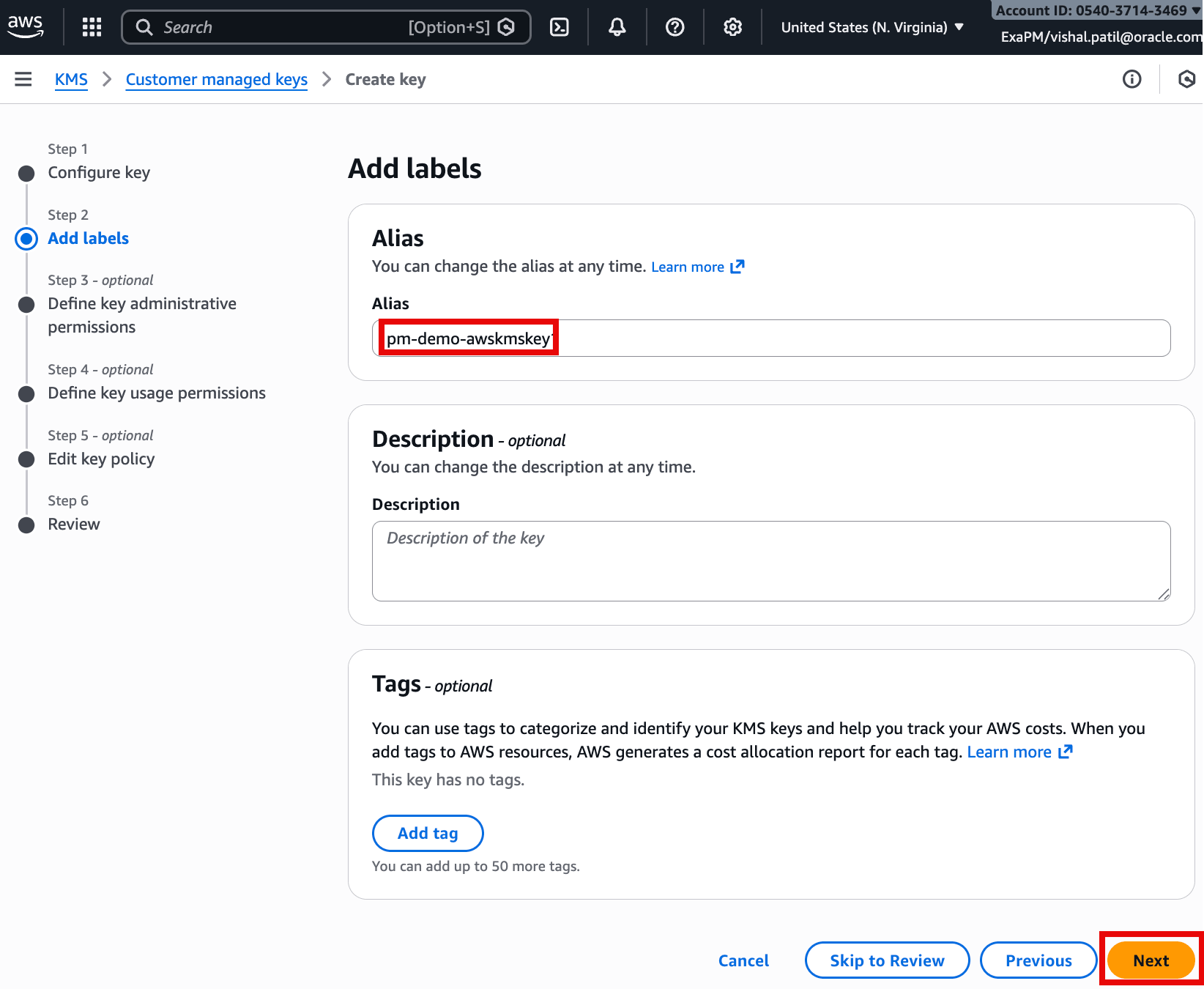
-
On the next screen add labels such as Alias, Description (optional), and Tags (optional). Then click Next.
-
Under Define key administrative permissions, select the IAM role created using CloudFormation in previous task. Then click Next.
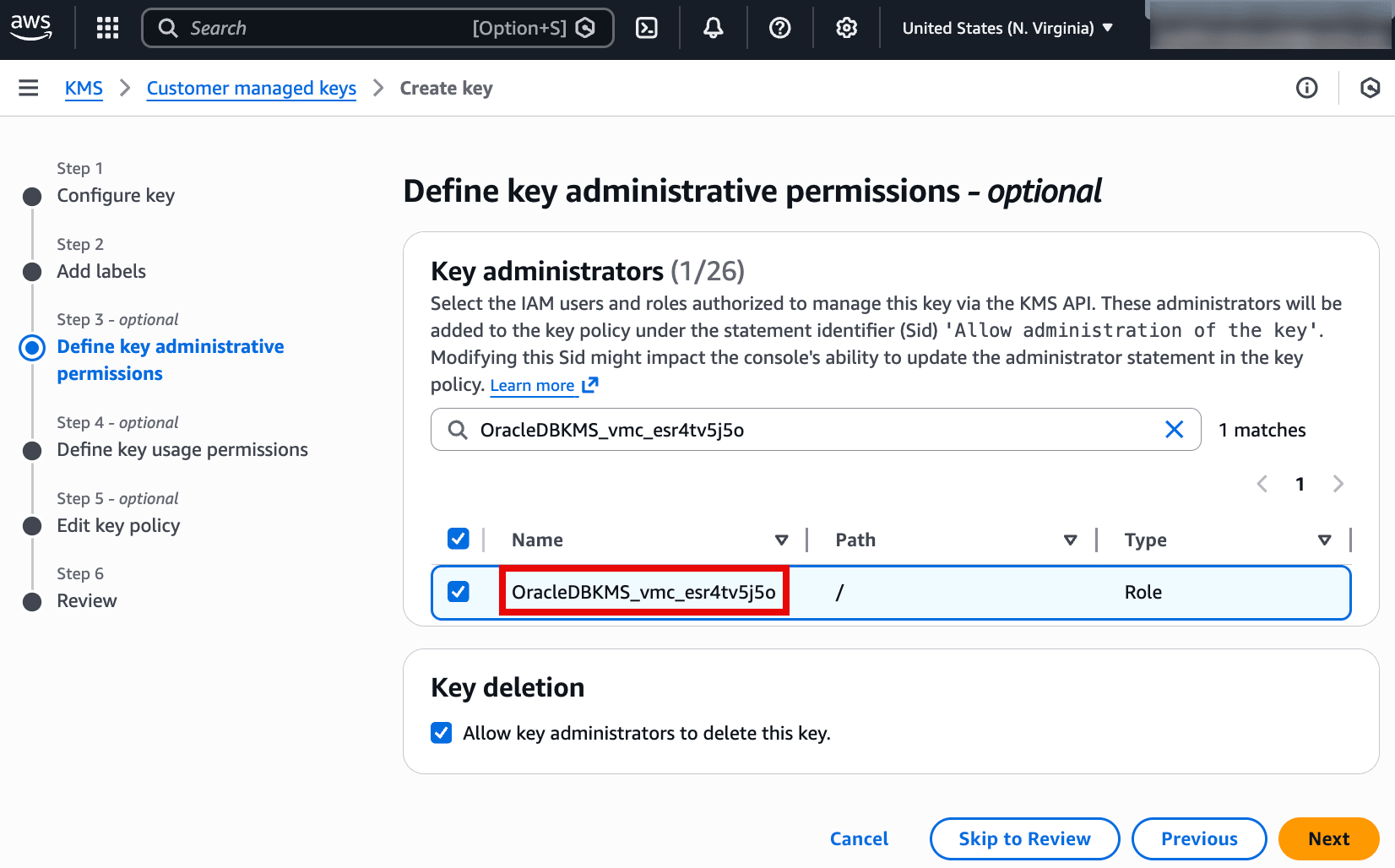
Description of the illustration Define-Key-Administrators.png
-
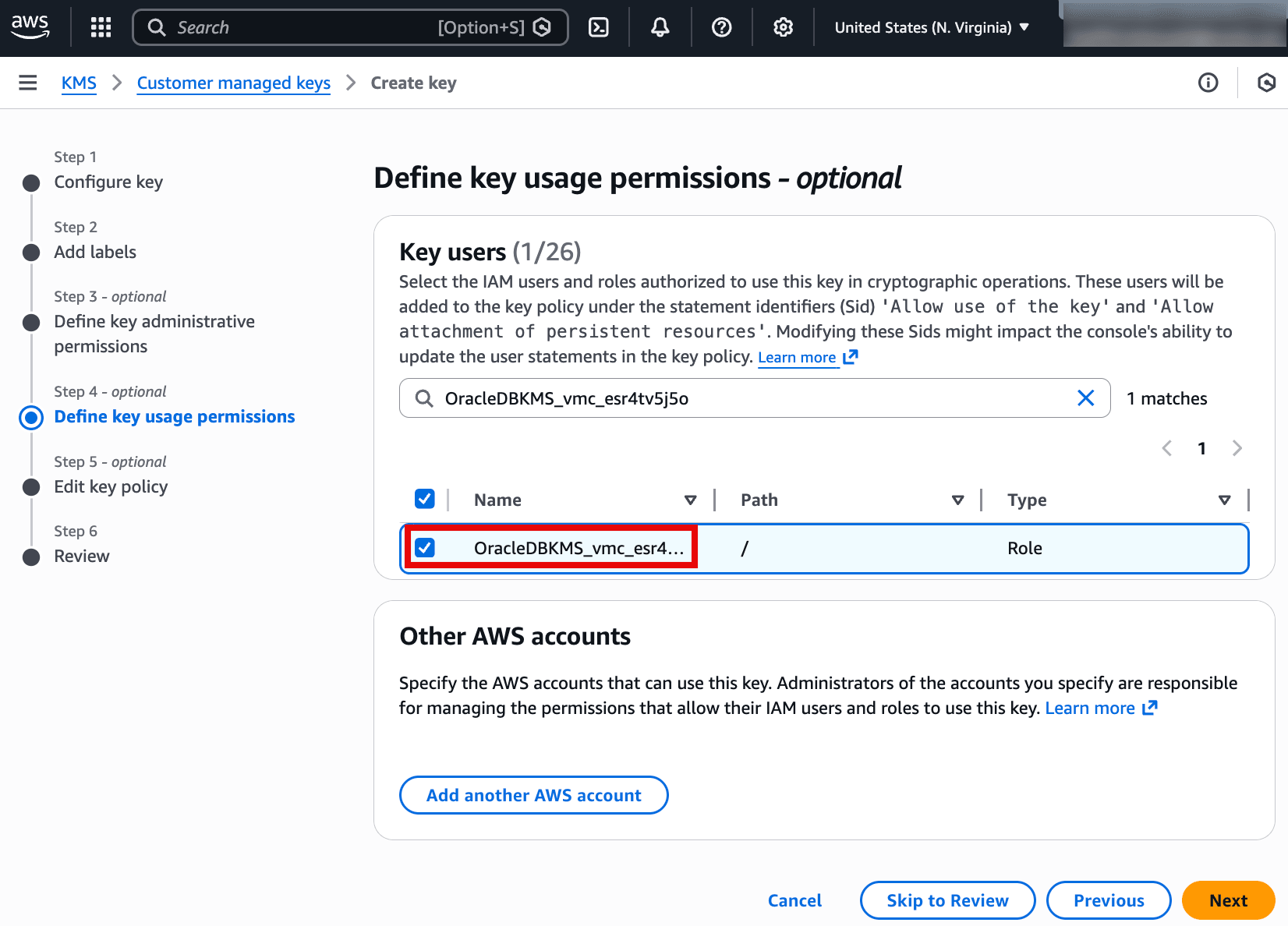
Under Define key usage permissions, select the relevant IAM roles. Then click Next.
-
On the next screen review key policy. Click Next.
-
Click Finish to create the key, noting the alias and key details.
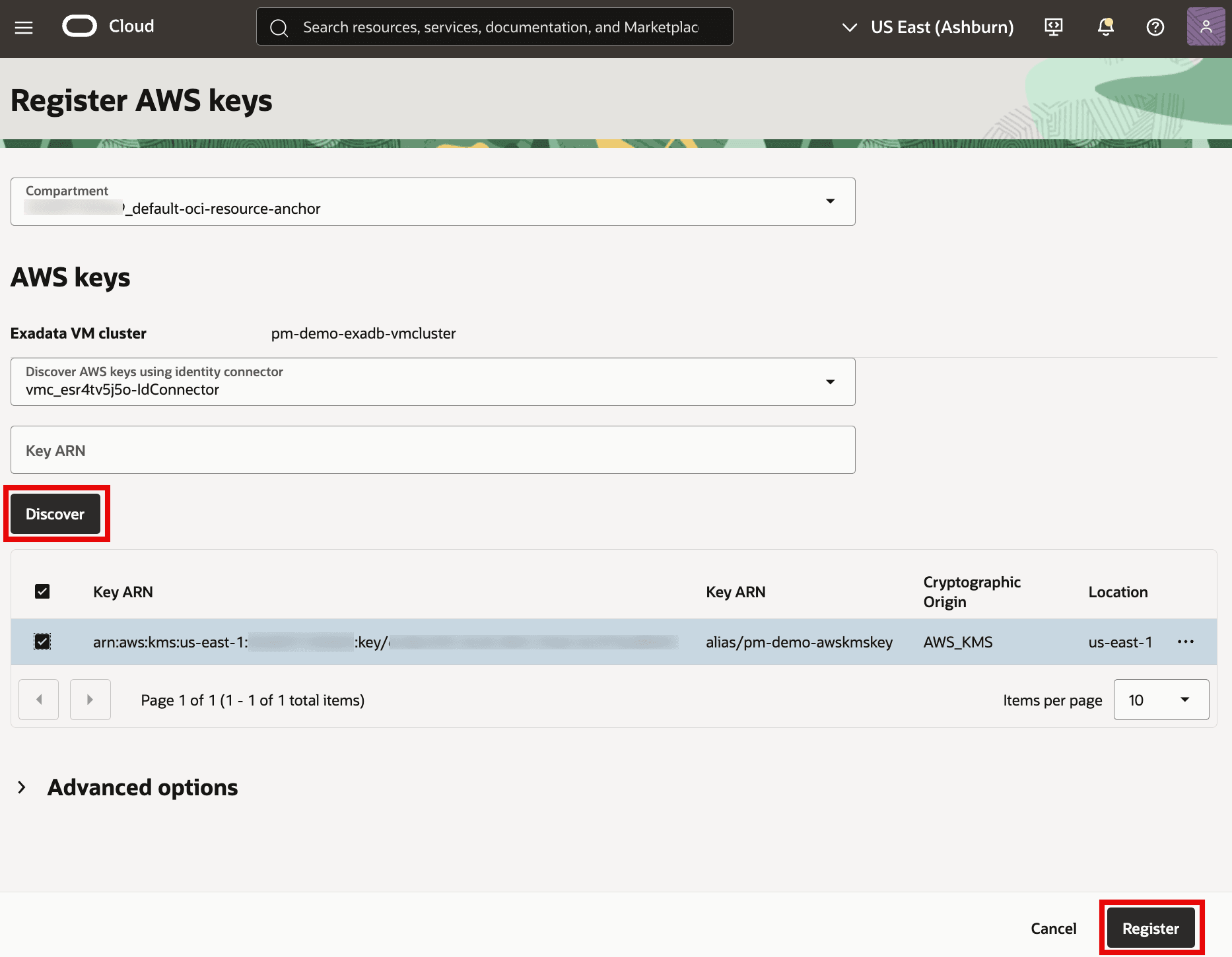
Task 6: Register AWS KMS key in OCI
-
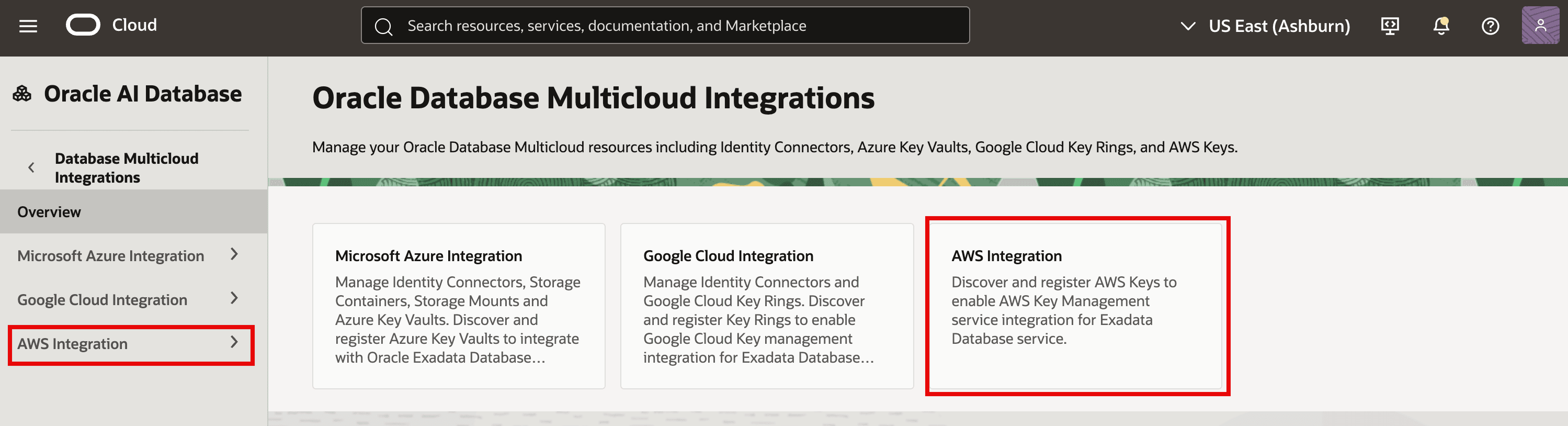
In the OCI Console, from menu navigate to Oracle AI Database and then click Database Multicloud Integrations. Click on AWS Integration.
-
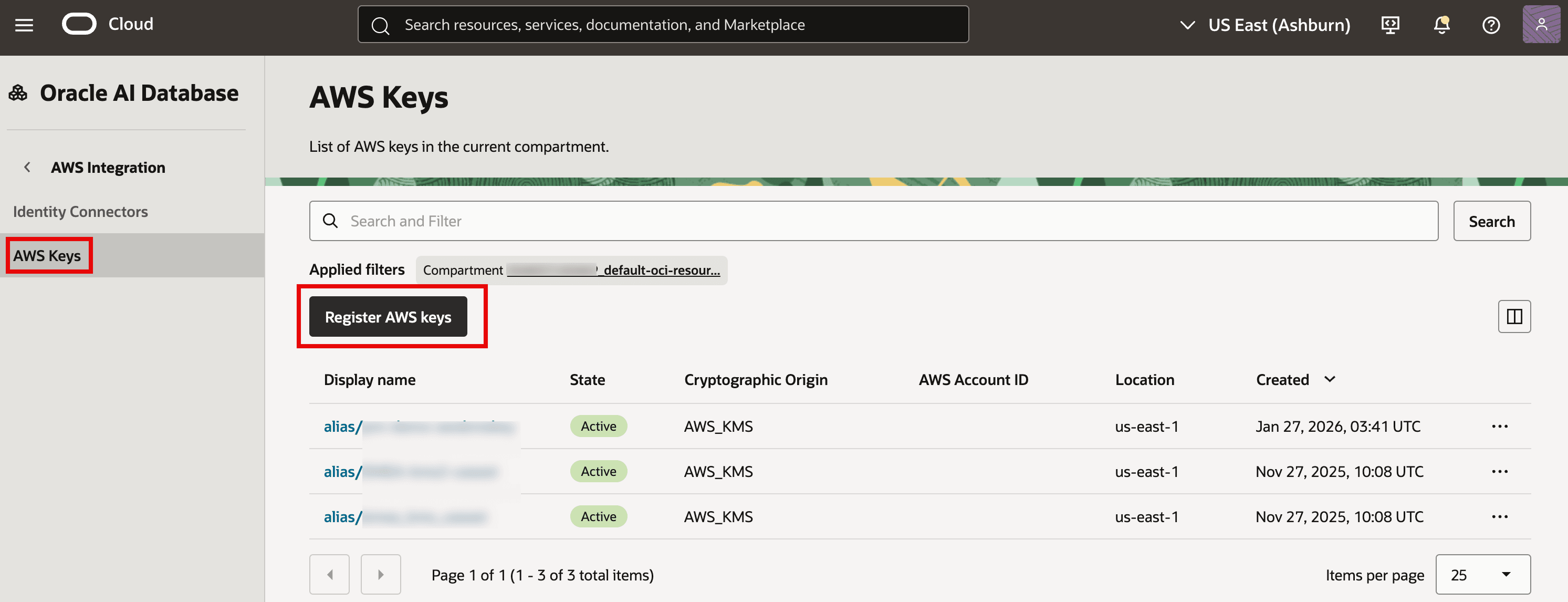
Click AWS Keys and then click on Register AWS keys.
-
To discover AWS Keys to register, select the compartment and identity connector, and (optionally) provide the Key ARN. Click Discover. Once discovered select the Key you want to register and then click Register to make the key available for database encryption in OCI.
Task 7: Enable AWS Key Management for the Exadata VM Cluster
-
In the OCI Console, from the menu, navigate to Oracle AI Database and then click on Oracle Exadata Database Service on Dedicated Infrastructure. In the Exadata VM Clusters page, click on your Exadata VM Cluster. On the VM Cluster information tab, click Enable next to AWS Key Management.
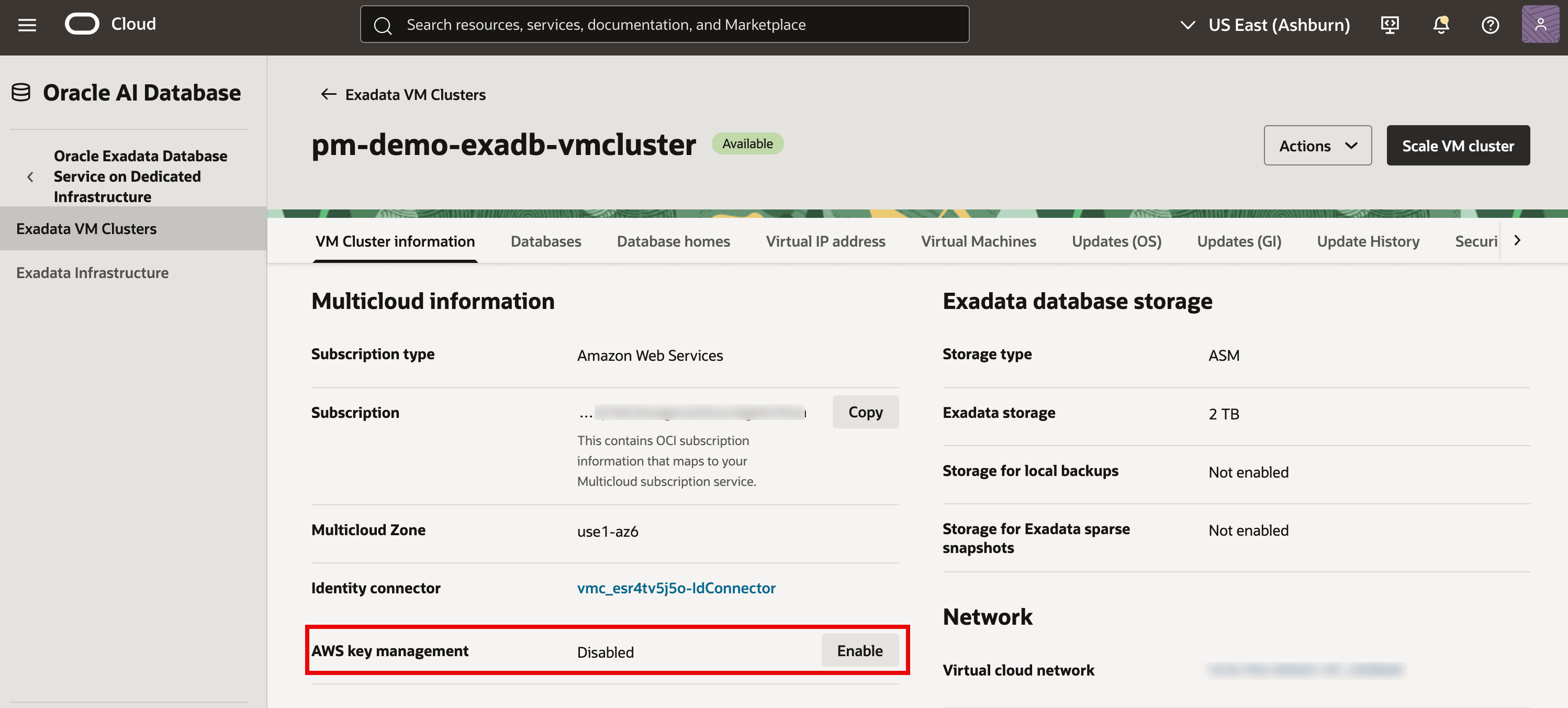
Description of the illustration OCI-Enable-AWS-KMS.png
Important: Once AWS KMS is enabled for the cluster, only Oracle Wallet or AWS KMS are supported options for Key Management during new database creation on that VM Cluster.
Task 8: Store TDE Master Encryption Key of your databases in AWS KMS
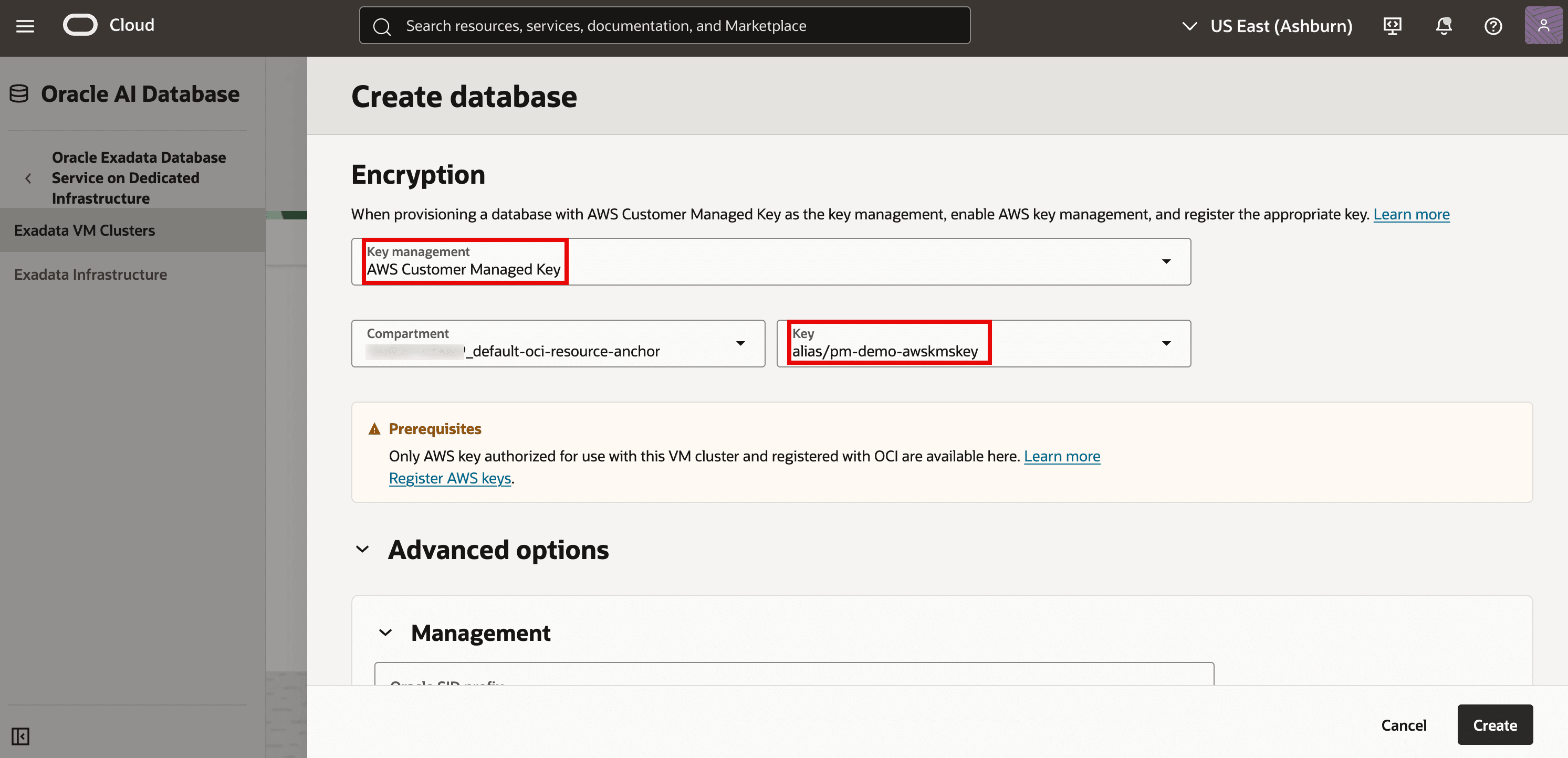
Option 1: Use AWS KMS to store TDE Master Encryption Key during New Database Creation
-
In the OCI Console, while creating a new database on Exadata VM Cluster where AWS Key Management is enabled, navigate to Encryption section. You will see both Oracle Wallet and AWS Customer Managed Key options in the drop-down for Key management, select AWS Customer Managed Key, select your compartment, and select the AWS KMS key alias registered in OCI.
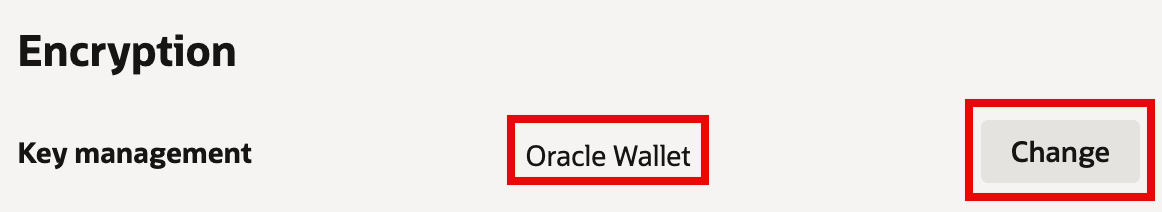
Option 2: Change TDE Master Encryption Key Management from Oracle Wallet to AWS KMS for existing databases
-
In the OCI Console, go to your Exadata VM Cluster where AWS Key Management is enabled. Then click on Databases tab. Select the database, and in the Database information tab verify Key management is set to Oracle Wallet under Encryption section. Click the Change button.
-
In the Key management drop-down, choose AWS Customer Managed Key, and select the appropriate Compartment and Key. Click Save changes to complete the transition.
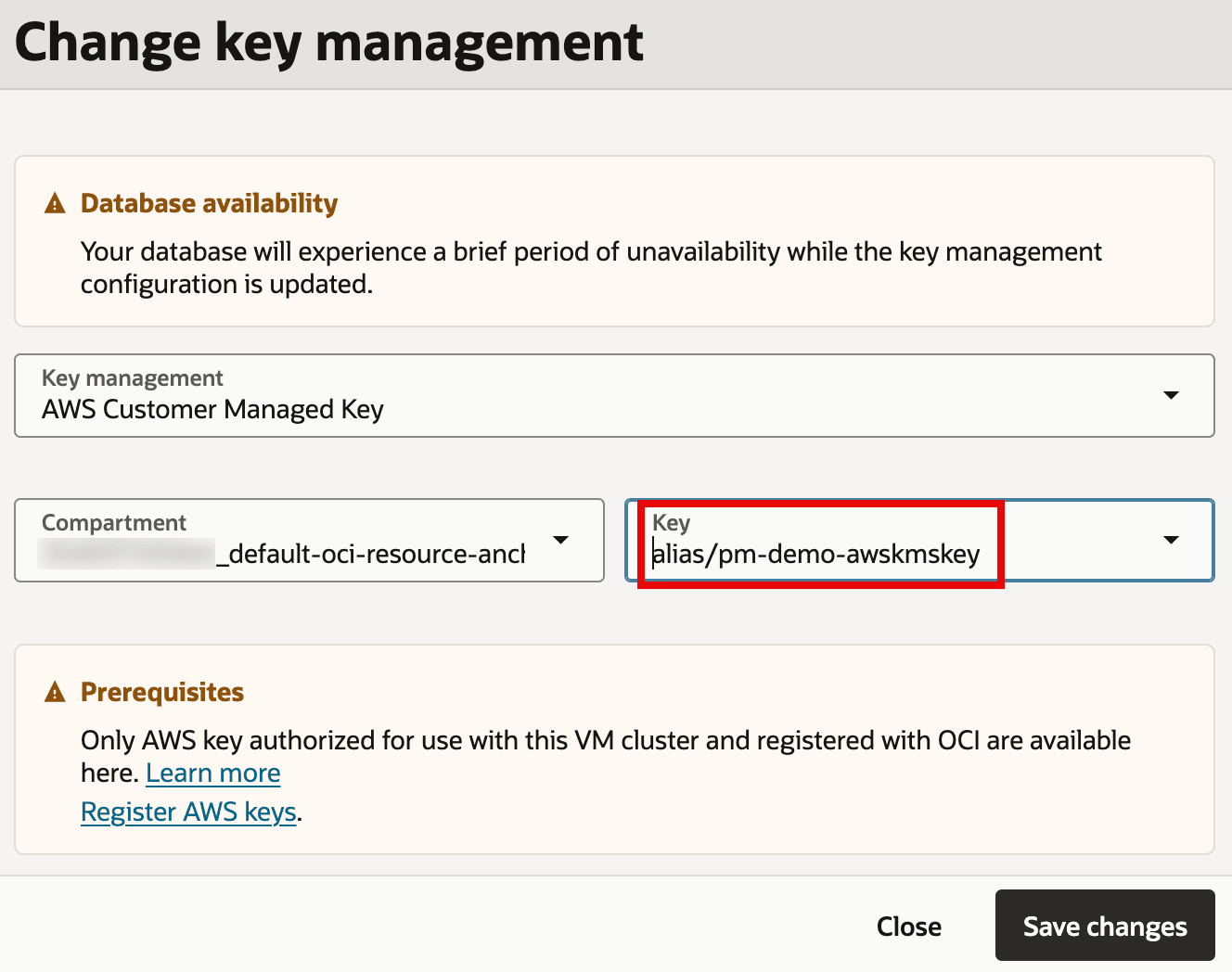
Description of the illustration AWS-KMS-Existing-DB-Select-Key.png
Additional Operational Task: Rotate the AWS KMS key of a Container Database (CDB)
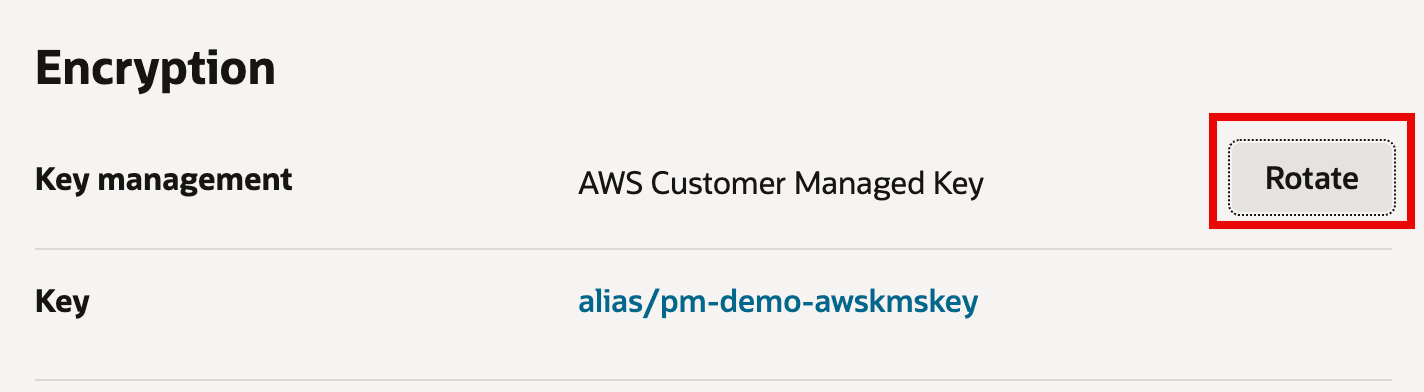
-
In the database details for container database, with Key Management set as AWS, click Rotate and confirm. Rotating the AWS KMS key generates a new encryption context for the same key.
Additional Operational Task: Rotate the AWS KMS key of a Pluggable Database (PDB)
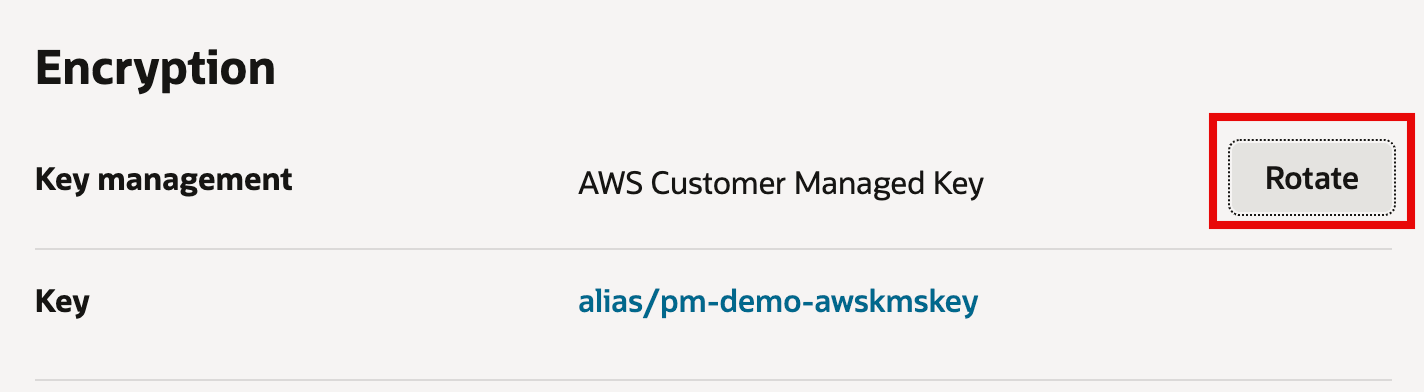
-
In the database details for pluggable database, with Key management set as AWS Customer Managed Key, click Rotate and confirm. Rotating the AWS KMS key generates a new encryption context for the same key.
Related Links
-
What’s New in Oracle Exadata Database Service on Dedicated Infrastructure
-
Exadata Database Service on Dedicated Infrastructure Documentation
-
Oracle Blog Announcing AWS KMS Integration with Oracle Database@AWS
Acknowledgments
- Authors - Leo Alvarado, Pravin Jha, and Vishal Patil (Product Management)
More Learning Resources
Explore other labs on docs.oracle.com/learn or access more free learning content on the Oracle Learning YouTube channel. Additionally, visit education.oracle.com/learning-explorer to become an Oracle Learning Explorer.
For product documentation, visit Oracle Help Center.
Configure AWS Key Management Service (KMS) to store TDE Master Encryption Key for Exadata Database Service on Dedicated Infrastructure on Oracle Database@AWS
G52189-01